Maryland Man Faces Charges for $53 Million Theft from Uranium Finance Crypto Exchange
Published on: 2026-03-31
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
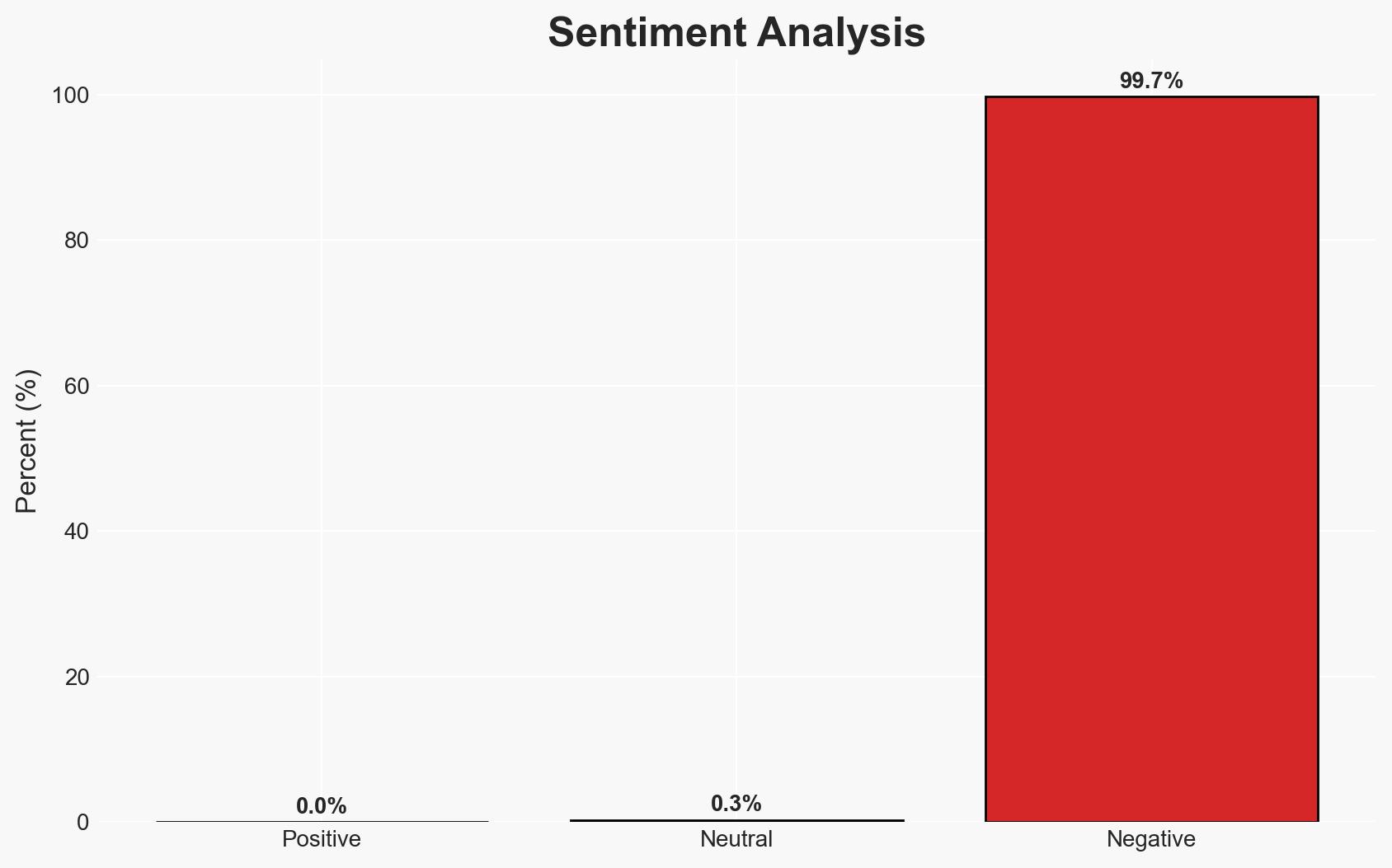
Intelligence Report: Hacker charged with stealing 53 million from Uranium crypto exchange
1. BLUF (Bottom Line Up Front)
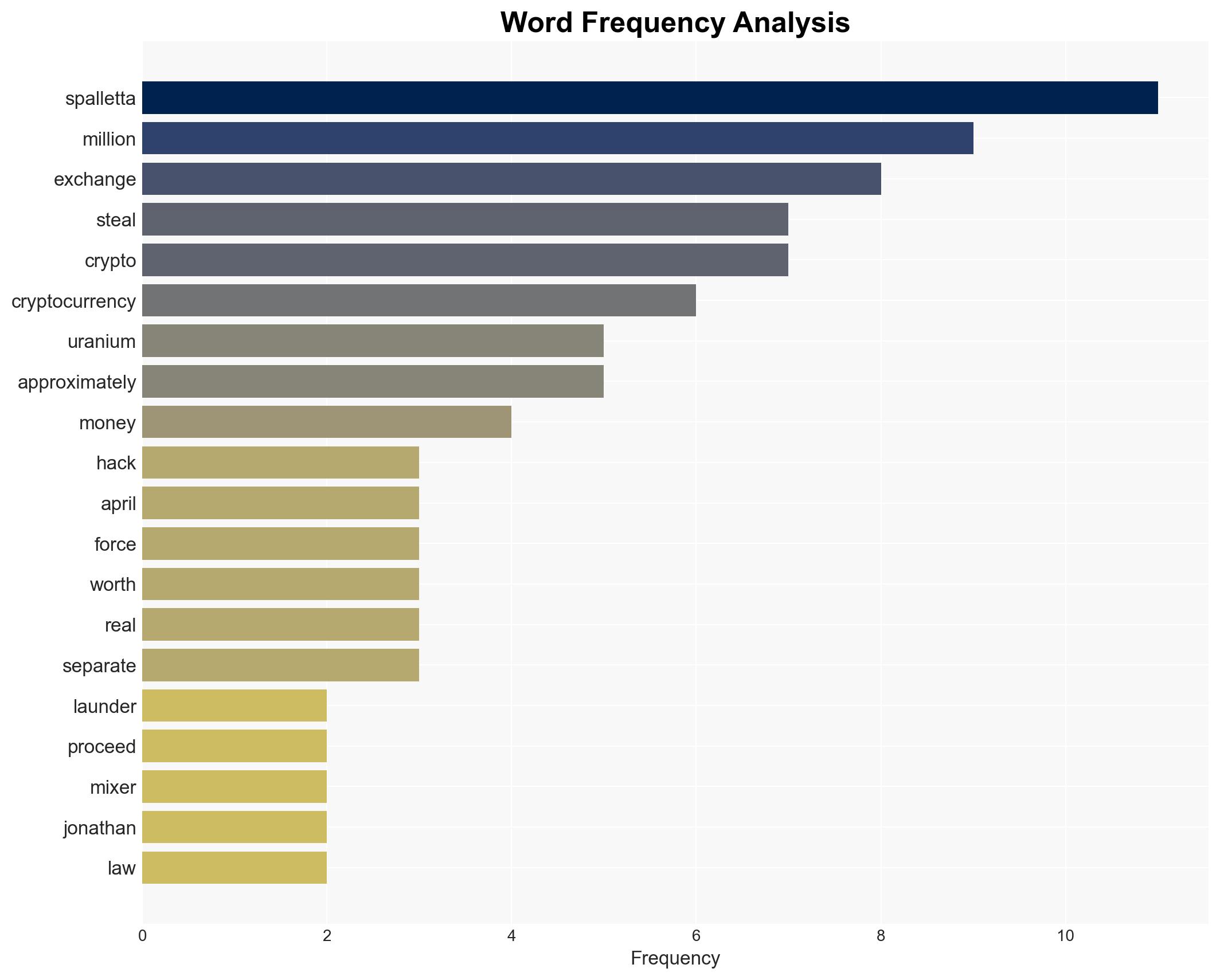
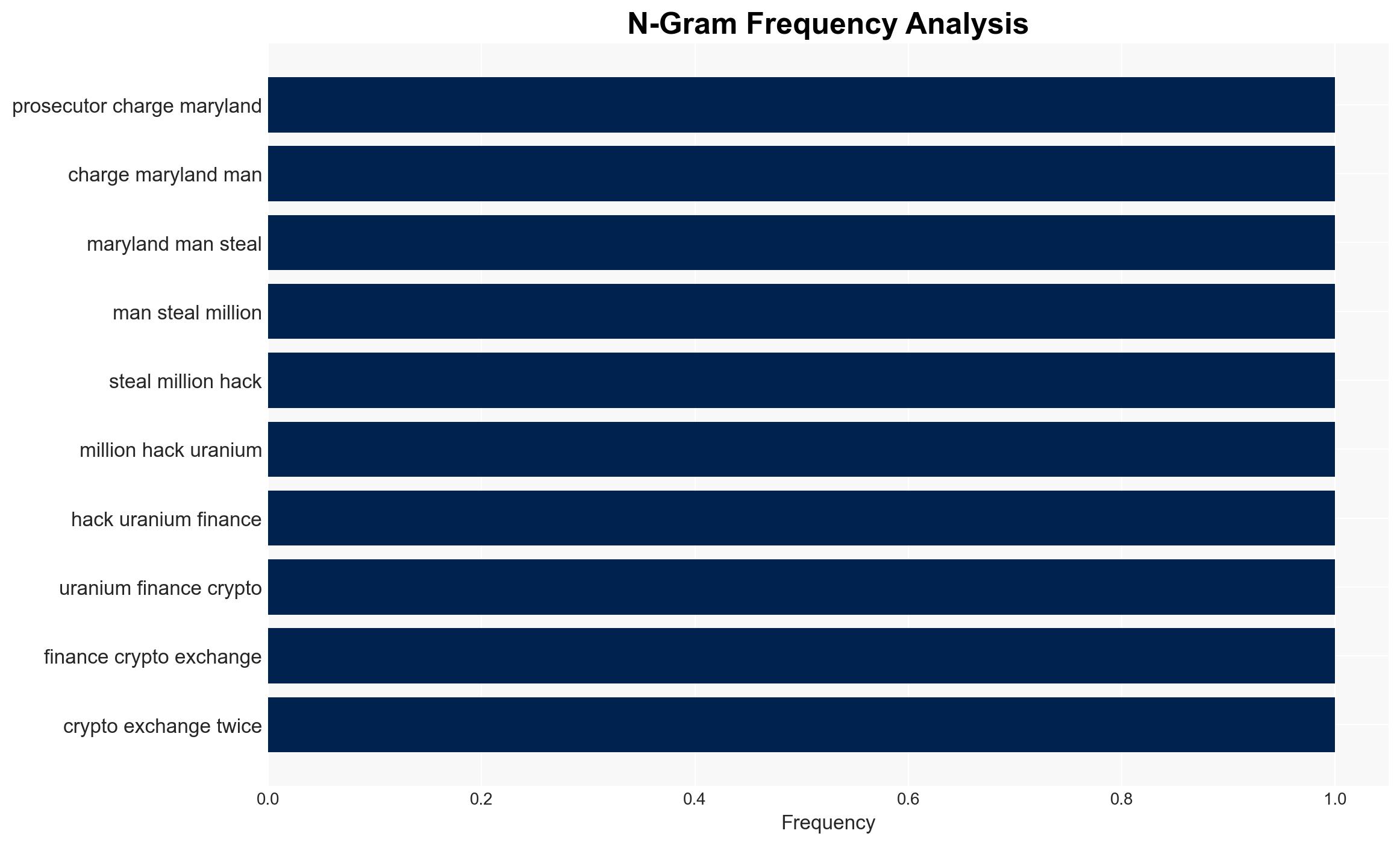
U.S. prosecutors have charged Jonathan Spalletta with stealing over $53 million from Uranium Finance, a decentralized crypto exchange, through two sophisticated hacks. The theft led to the exchange’s shutdown, affecting numerous stakeholders. The most likely hypothesis is that Spalletta acted independently for personal gain, exploiting vulnerabilities in smart contracts. This assessment is made with moderate confidence due to existing information gaps regarding potential accomplices and broader network involvement.
2. Competing Hypotheses
- Hypothesis A: Spalletta acted independently, motivated by personal financial gain, exploiting technical vulnerabilities in Uranium’s smart contracts. Supporting evidence includes his direct involvement in the hacks and subsequent laundering of funds through a cryptocurrency mixer. However, uncertainties remain about whether he had any accomplices or external support.
- Hypothesis B: Spalletta was part of a larger criminal network that orchestrated the attacks on Uranium Finance. This is supported by the complexity of the operations and the use of advanced laundering techniques. Contradicting evidence includes the lack of identified co-conspirators in the indictment.
- Assessment: Hypothesis A is currently better supported due to the direct evidence of Spalletta’s actions and lack of concrete links to a broader network. Indicators that could shift this judgment include the discovery of communications or transactions suggesting coordination with other individuals.
3. Key Assumptions and Red Flags
- Assumptions: Spalletta had the technical expertise to exploit smart contract vulnerabilities; the stolen funds were primarily used for personal purchases; Uranium Finance had inadequate security measures.
- Information Gaps: Details on potential accomplices or external support; comprehensive analysis of Spalletta’s financial transactions post-theft; Uranium Finance’s internal security protocols.
- Bias & Deception Risks: Potential bias in focusing solely on Spalletta without exploring broader network possibilities; risk of deception in Spalletta’s statements minimizing the seriousness of crypto theft.
4. Implications and Strategic Risks
This incident highlights vulnerabilities in decentralized finance platforms, potentially leading to increased regulatory scrutiny and security investments. The case may influence public perception of cryptocurrency security and trust.
- Political / Geopolitical: Potential for increased regulatory actions on cryptocurrency exchanges and mixers globally.
- Security / Counter-Terrorism: Heightened awareness of cyber threats in financial sectors, prompting enhanced security measures.
- Cyber / Information Space: Possible increase in cyber-attacks targeting similar vulnerabilities, necessitating improved cybersecurity frameworks.
- Economic / Social: Loss of investor confidence in decentralized finance platforms, potentially affecting market stability and innovation.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor for any signs of coordinated attacks on similar platforms; engage with cybersecurity experts to assess and mitigate vulnerabilities.
- Medium-Term Posture (1–12 months): Develop partnerships with regulatory bodies to establish clearer guidelines for crypto exchanges; invest in cybersecurity training and infrastructure.
- Scenario Outlook: Best case: Strengthened security and regulatory frameworks restore confidence. Worst case: Continued vulnerabilities lead to further major breaches. Most likely: Gradual improvement in security with intermittent regulatory challenges.
6. Key Individuals and Entities
- Jonathan Spalletta (a.k.a. “Cthulhon”, “Jspalletta”)
- Uranium Finance
- U.S. Attorney Jay Clayton
- Cryptocurrency mixer Tornado Cash
- Crypto fraud investigator ZachXBT
7. Thematic Tags
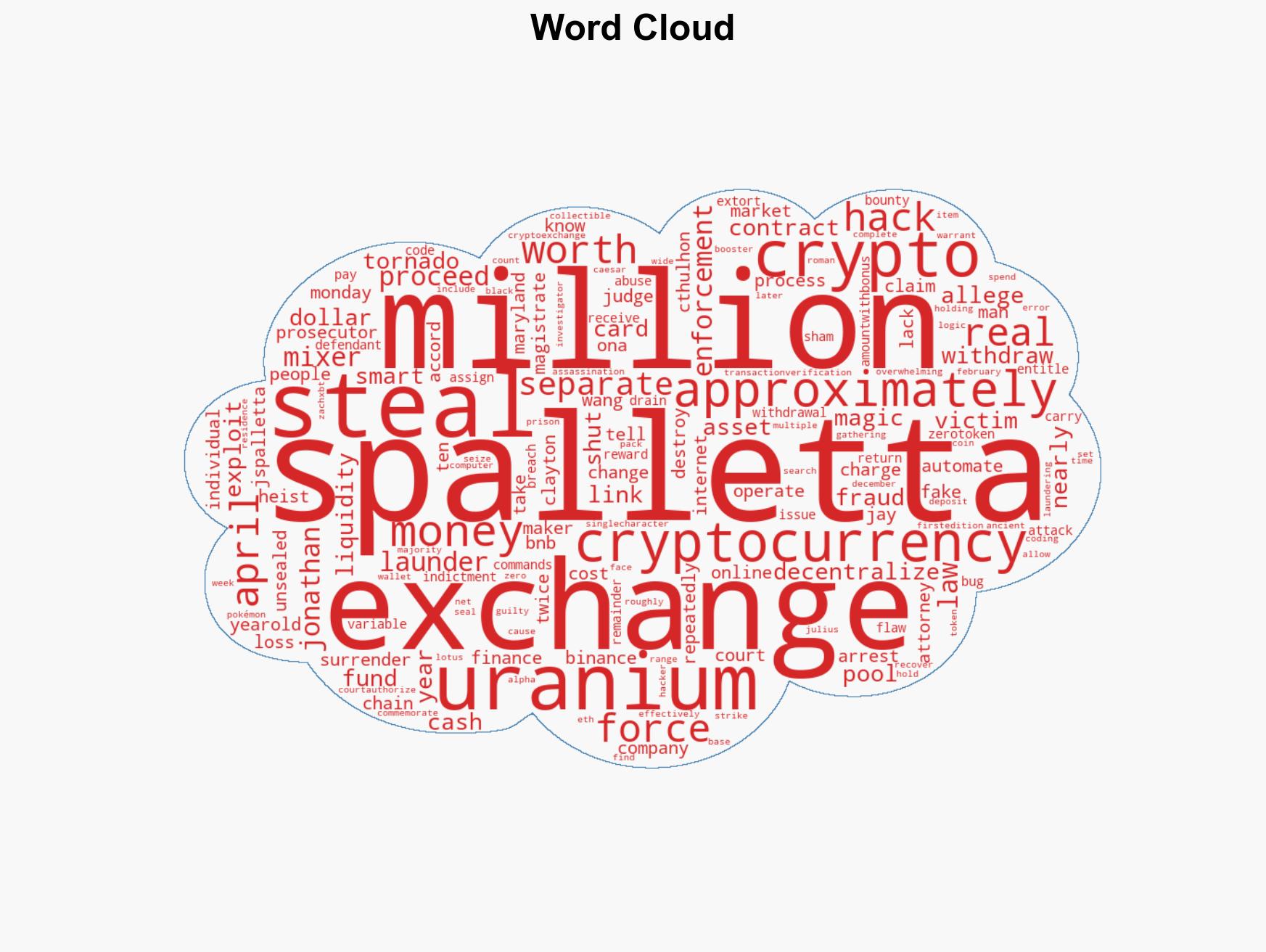
cybersecurity, cybercrime, cryptocurrency, financial security, regulatory scrutiny, decentralized finance, cyber vulnerabilities, money laundering
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us