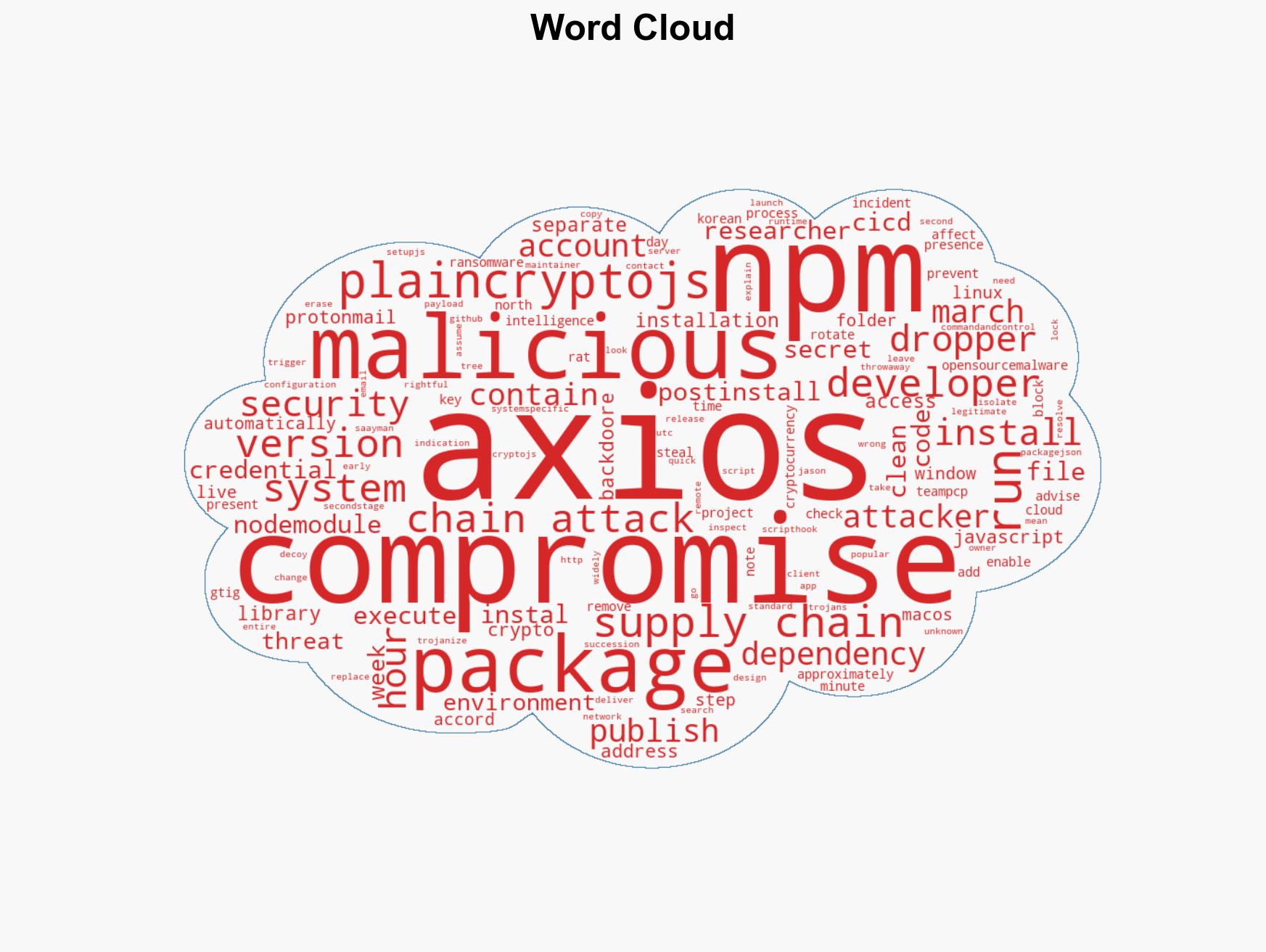
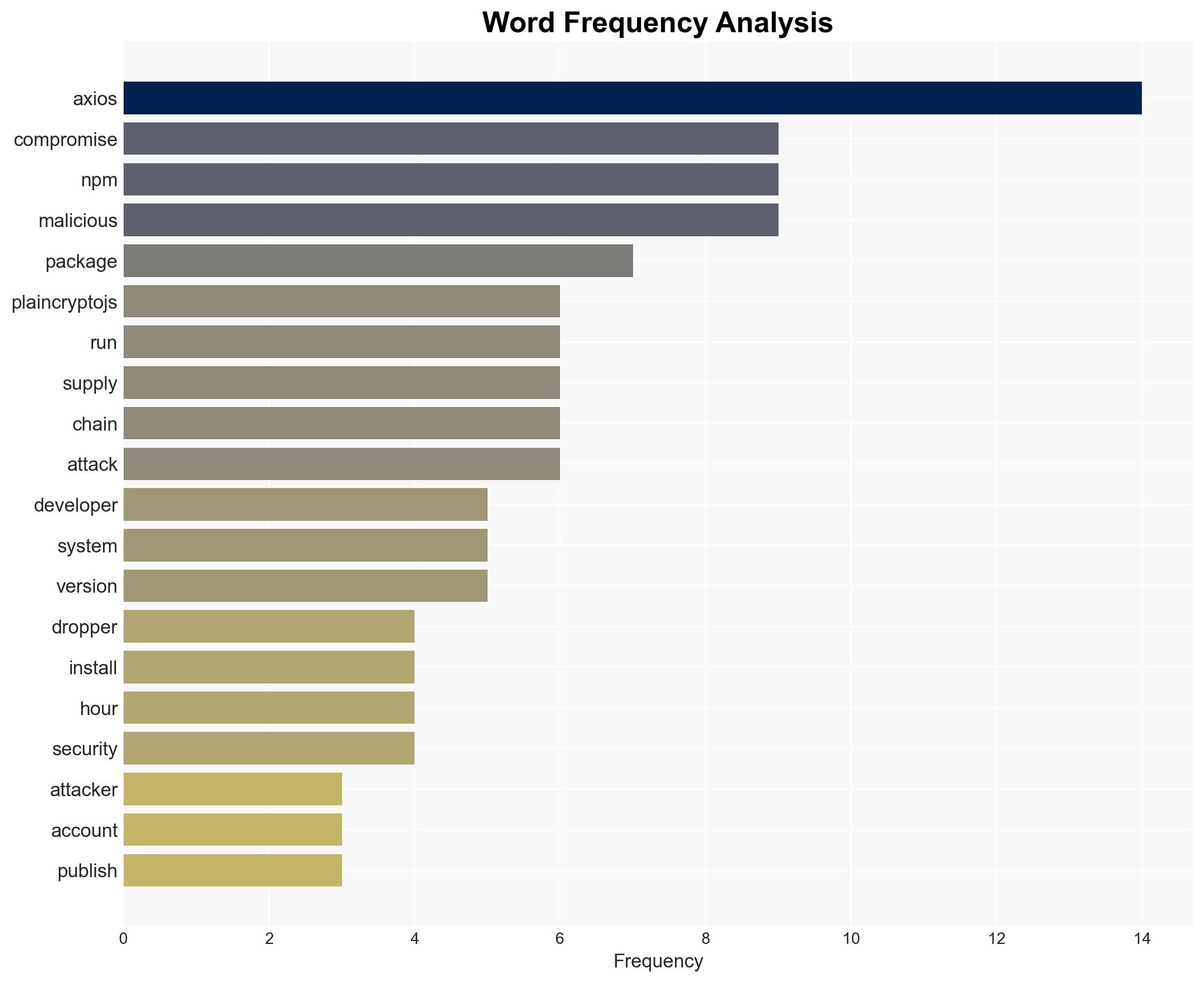
Axios npm packages compromised in supply chain breach, leading to malicious dependency installations.
Published on: 2026-03-31
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Axios npm packages backdoored in supply chain attack
1. BLUF (Bottom Line Up Front)
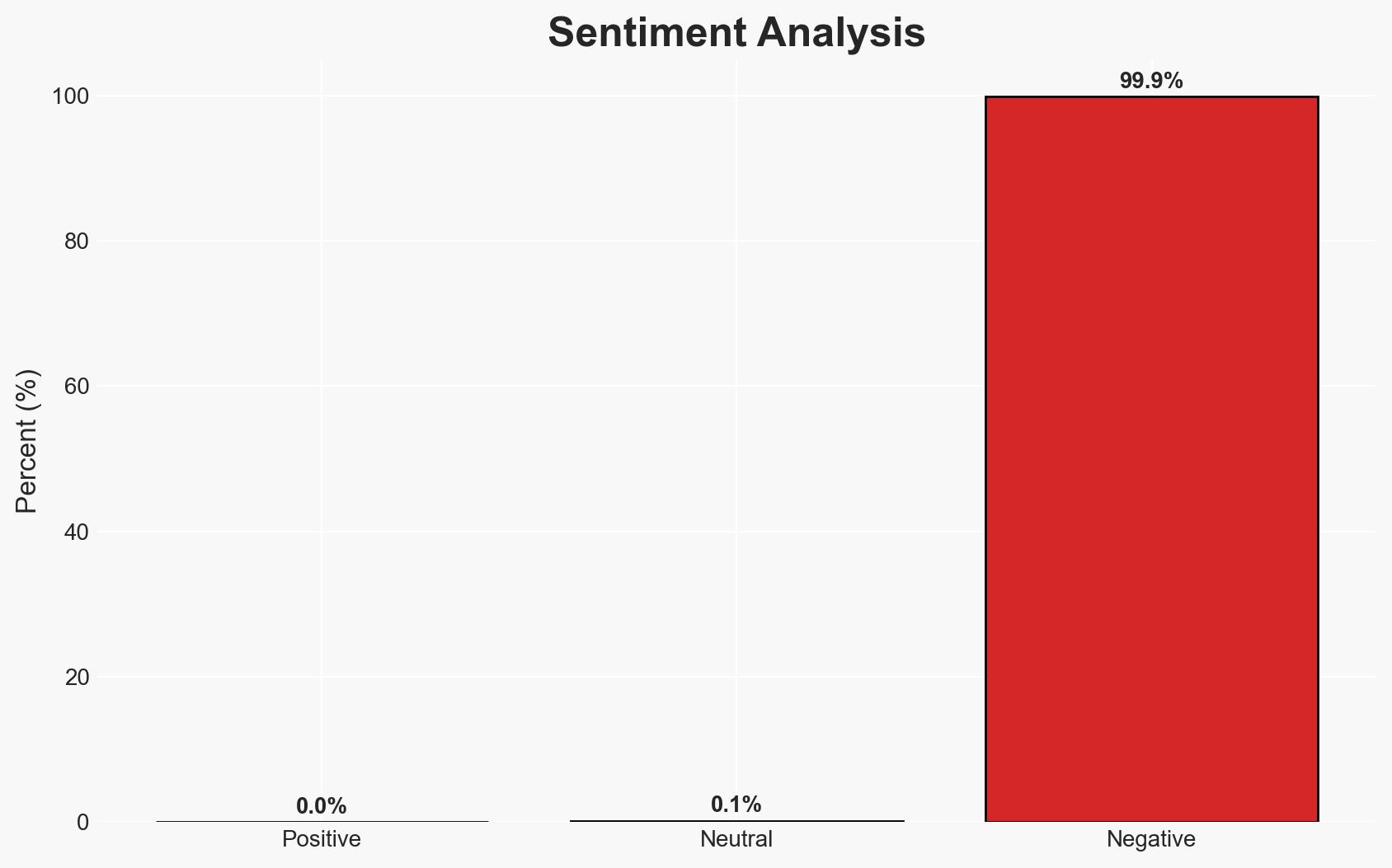
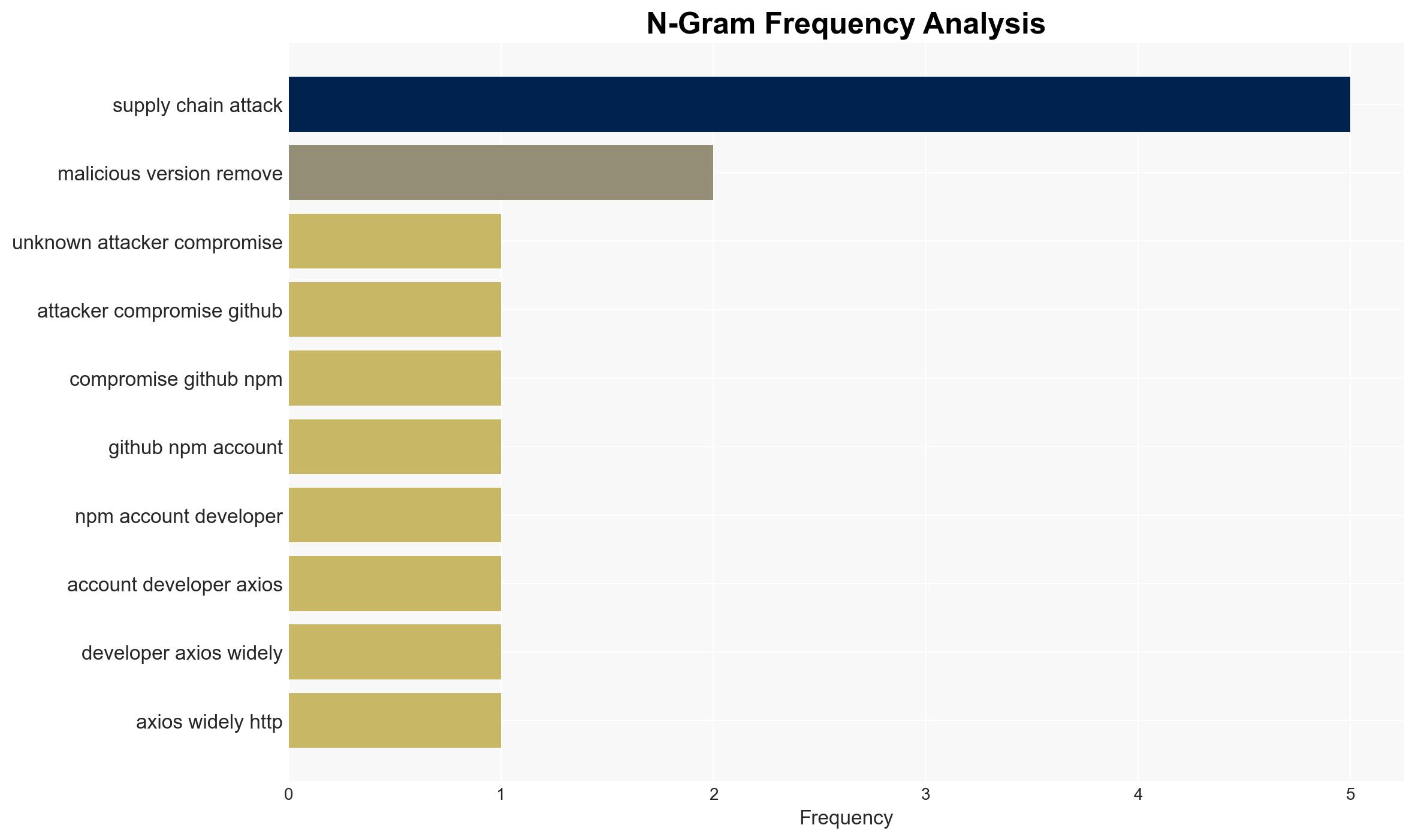
An unknown attacker has compromised npm packages associated with the Axios library, inserting backdoors that facilitate remote access and control of affected systems. This incident highlights significant vulnerabilities in software supply chains, affecting developers and potentially broader systems reliant on these libraries. The most likely hypothesis is that this attack was conducted by a sophisticated actor with specific objectives, given the complexity and precision of the operation. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The attack was orchestrated by a state-sponsored group aiming to infiltrate systems for intelligence gathering. This is supported by the sophisticated nature of the attack and the use of ProtonMail for anonymity. However, there is no direct evidence linking state actors.
- Hypothesis B: The attack was conducted by cybercriminals seeking financial gain through ransomware or data theft. The rapid deployment and obfuscation techniques align with criminal tactics, but the lack of immediate monetization attempts contradicts this.
- Assessment: Hypothesis A is currently better supported due to the strategic targeting and complexity of the attack, suggesting a higher level of resources and planning typical of state-sponsored operations. Indicators such as further intelligence linking the attack to known state actors could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The attacker has advanced technical capabilities; the use of ProtonMail indicates an attempt to obscure identity; the attack’s objective is broader than immediate financial gain.
- Information Gaps: The identity and motive of the attacker remain unknown; the full scope of affected systems is unclear; potential connections to known threat actors are not established.
- Bias & Deception Risks: Confirmation bias towards state-sponsored attribution; potential deception in the attack’s execution to mislead attribution efforts.
4. Implications and Strategic Risks
This development could lead to increased scrutiny and regulation of software supply chains, affecting open-source communities and software distribution practices.
- Political / Geopolitical: Potential for increased tensions if state-sponsored involvement is confirmed, leading to diplomatic confrontations.
- Security / Counter-Terrorism: Heightened alert for similar supply chain attacks, necessitating enhanced security protocols.
- Cyber / Information Space: Increased focus on securing open-source repositories and improving incident response capabilities.
- Economic / Social: Potential disruptions to businesses relying on compromised software, leading to economic losses and reduced trust in digital infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a thorough audit of affected systems, isolate compromised networks, and rotate credentials. Monitor for further malicious activity and engage with cybersecurity firms for incident response.
- Medium-Term Posture (1–12 months): Develop partnerships with open-source communities to enhance security practices, invest in supply chain security tools, and conduct regular security drills.
- Scenario Outlook:
- Best Case: Rapid identification and neutralization of the attacker, leading to minimal disruption.
- Worst Case: Prolonged exploitation of vulnerabilities, resulting in significant data breaches and economic impact.
- Most-Likely: Incremental improvements in supply chain security with ongoing vigilance against similar threats.
6. Key Individuals and Entities
- Jason Saayman (Axios maintainer, compromised account)
- Step Security (Research entity providing analysis)
- OpenSourceMalware (Entity providing threat intelligence)
- Not clearly identifiable from open sources in this snippet (attacker)
7. Thematic Tags
cybersecurity, supply chain attack, cyber security, npm, open-source vulnerabilities, state-sponsored threats, software development, remote access trojans
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us