North Korean Hackers Target Popular JavaScript Library, Compromising Developer Security, Google Analysts Warn
Published on: 2026-03-31
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: North Korea-linked hackers suspected in Axios open-source hijack Google analysts say
1. BLUF (Bottom Line Up Front)
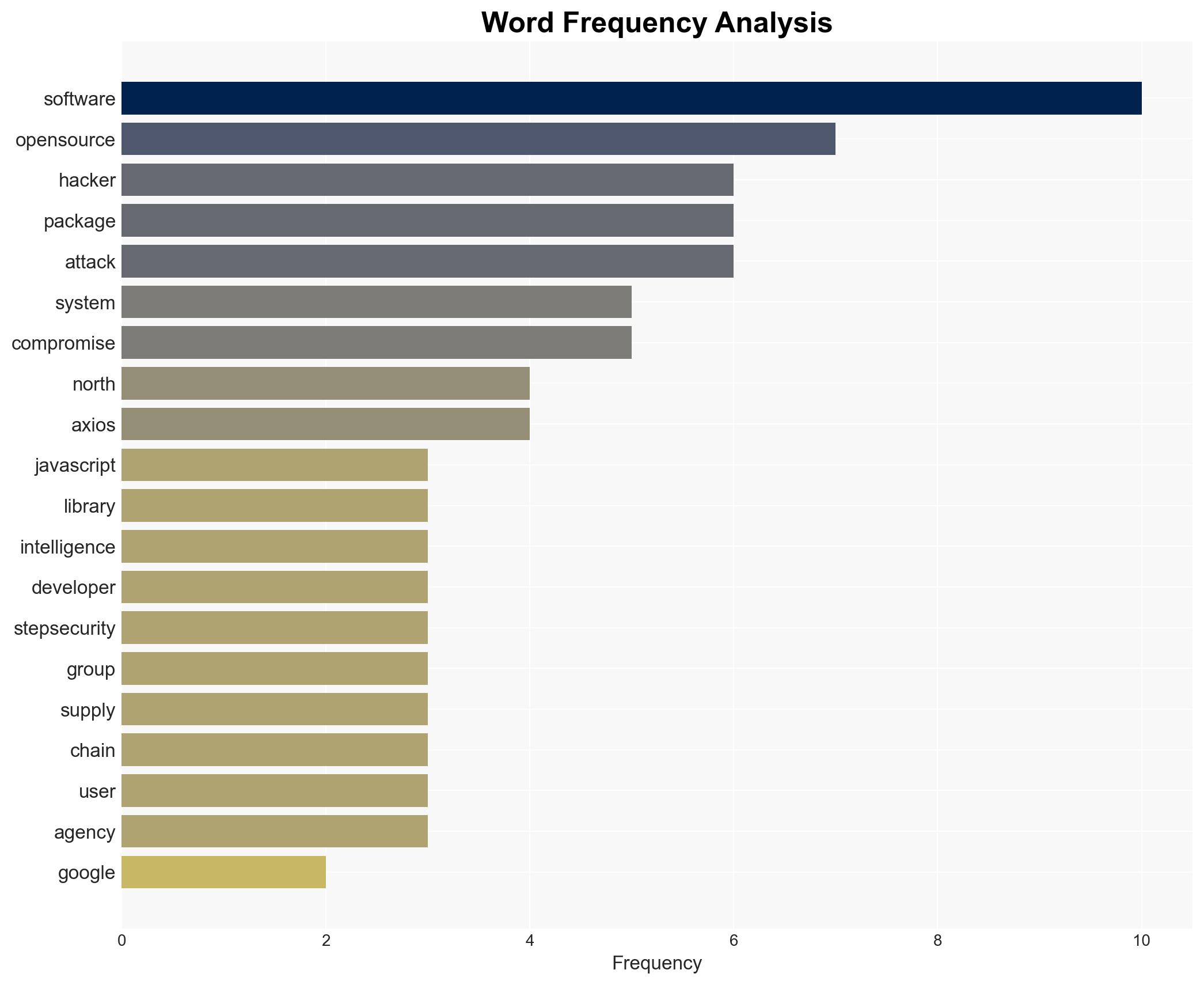
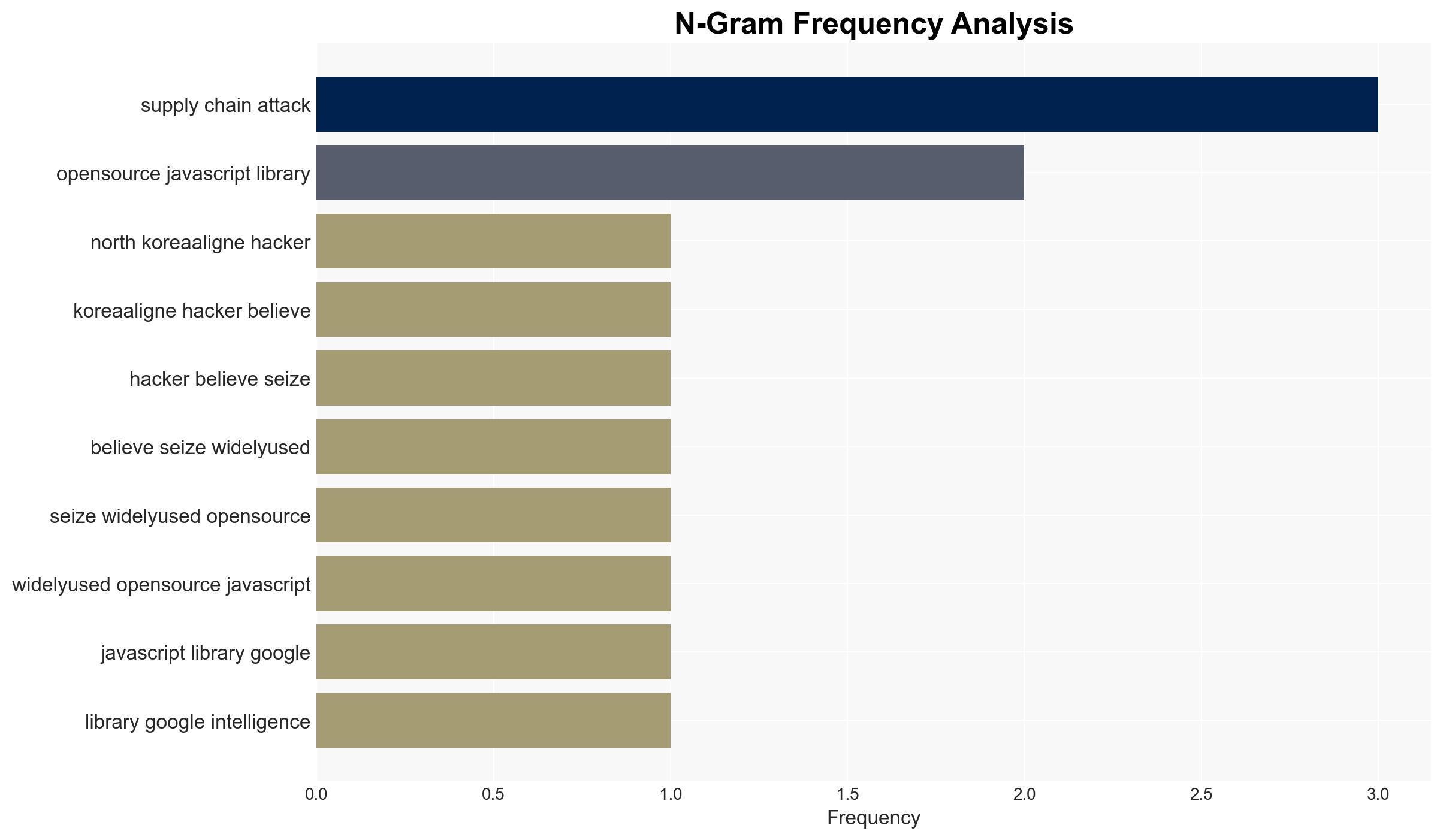
North Korean-affiliated hackers, identified as UNC1069, are suspected of compromising the Axios JavaScript library, posing a significant threat to software developers globally. The attack, characterized by its sophistication, could lead to widespread system compromises. This assessment is made with moderate confidence due to the ongoing investigation and limited public information.
2. Competing Hypotheses
- Hypothesis A: North Korean hackers executed the attack to gain unauthorized access to systems for espionage or financial gain. This is supported by the group’s history of supply chain attacks and the sophisticated nature of the malware. However, the full scope of the attack remains unclear.
- Hypothesis B: The attack was conducted by a non-state actor or another nation-state actor masquerading as North Korean hackers to mislead attribution. This is less supported due to the specific attribution by Google’s Threat Intelligence Group and the known tactics of UNC1069.
- Assessment: Hypothesis A is currently better supported given the attribution by credible sources and the alignment with known North Korean tactics. Indicators that could shift this judgment include new evidence of different attribution or motivations.
3. Key Assumptions and Red Flags
- Assumptions: The attribution to UNC1069 is accurate; the attack aimed to compromise systems for espionage or financial theft; the compromised library was widely used at the time of the attack.
- Information Gaps: The specific targets and impact of the attack; whether U.S. government systems were directly affected; the full capabilities of the deployed malware.
- Bias & Deception Risks: Potential bias in attribution due to reliance on specific intelligence sources; risk of deception if another actor is framing North Korea.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of open-source software security and heightened tensions in cyber diplomacy. The attack may prompt further investigation into supply chain vulnerabilities.
- Political / Geopolitical: Potential for increased diplomatic tensions between North Korea and affected nations.
- Security / Counter-Terrorism: Heightened threat environment for organizations relying on open-source software.
- Cyber / Information Space: Increased focus on securing software supply chains; potential for copycat attacks.
- Economic / Social: Possible economic impact on companies reliant on compromised software; increased demand for cybersecurity solutions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct audits of systems using the Axios library; enhance monitoring for suspicious activity; engage with cybersecurity firms for threat intelligence.
- Medium-Term Posture (1–12 months): Develop partnerships to improve open-source software security; invest in supply chain risk management capabilities.
- Scenario Outlook:
- Best Case: Rapid containment and patching of vulnerabilities, minimal impact.
- Worst Case: Widespread system compromises leading to significant data breaches and financial losses.
- Most-Likely: Moderate impact with increased cybersecurity measures and awareness.
6. Key Individuals and Entities
- UNC1069 (North Korean hacker group)
- John Hultquist (Chief Analyst, Google’s Threat Intelligence Group)
- StepSecurity (Security firm)
- Google’s Threat Intelligence Group
- Axios (JavaScript library)
- FBI
- Cybersecurity and Infrastructure Security Agency
7. Thematic Tags
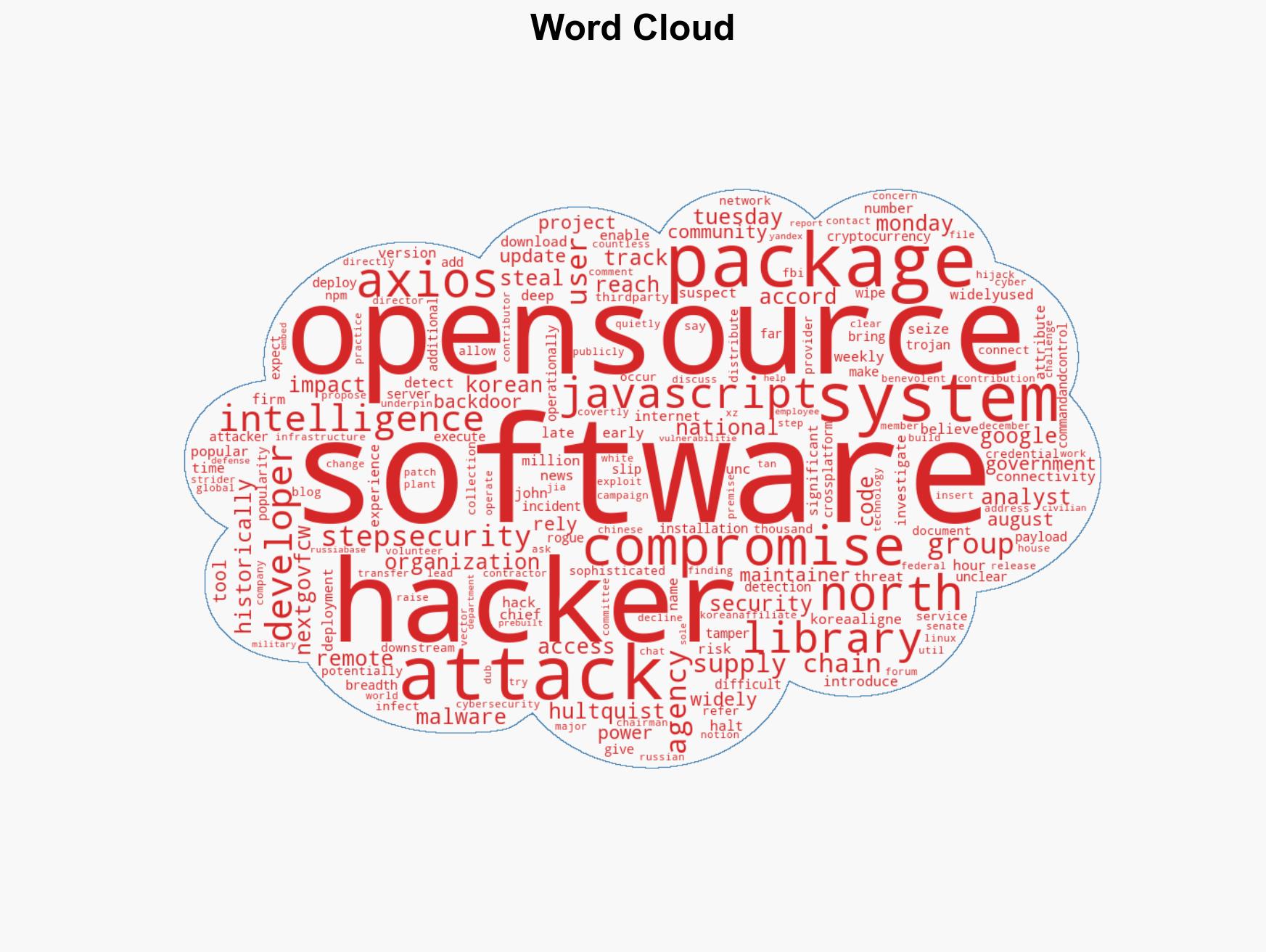
cybersecurity, supply chain attack, North Korea, open-source software, malware, espionage, cyber-espionage
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us