Apple to Release Uncommon Security Updates for Older iOS Versions Amid DarkSword Hacking Threat
Published on: 2026-04-01
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Apple Will Push Out Rare Backported Patches to Protect iOS 18 Users From DarkSword Hacking Tool
1. BLUF (Bottom Line Up Front)
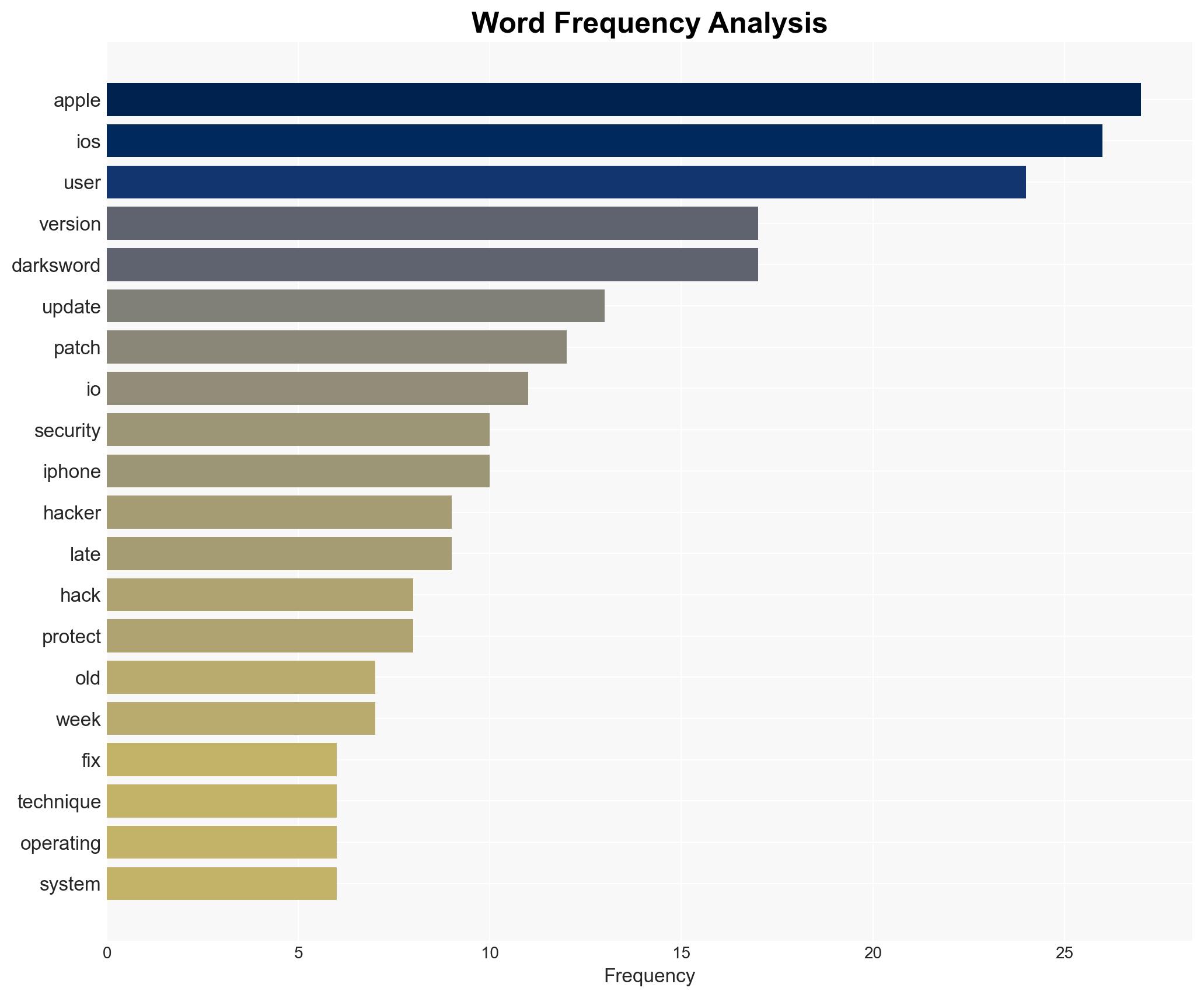
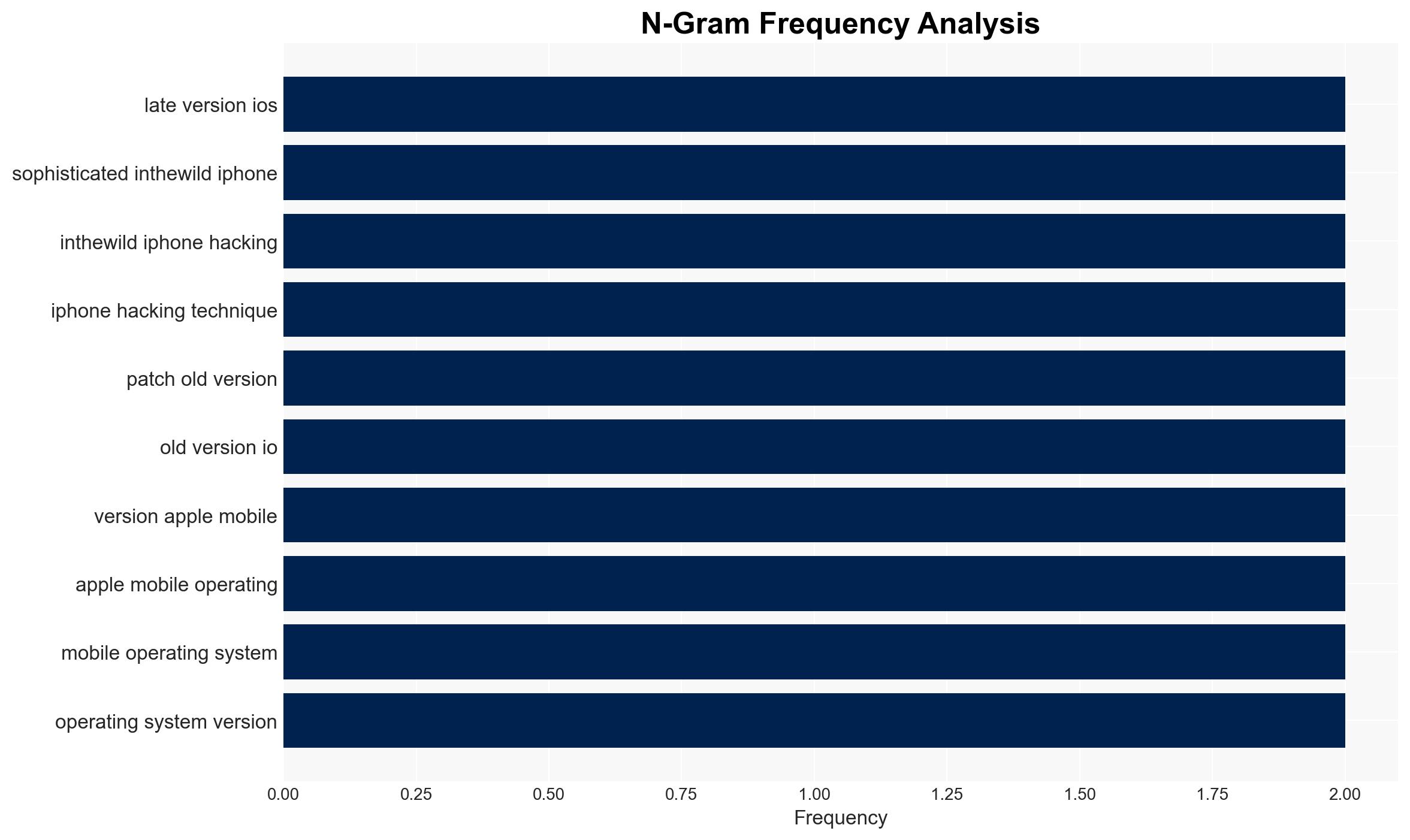
Apple’s decision to backport security patches for iOS 18 users in response to the DarkSword hacking tool represents a significant shift in its update policy, likely driven by user resistance to iOS 26. This move aims to protect a substantial portion of iPhone users who have not upgraded due to interface preferences. The overall confidence level in this assessment is moderate.
2. Competing Hypotheses
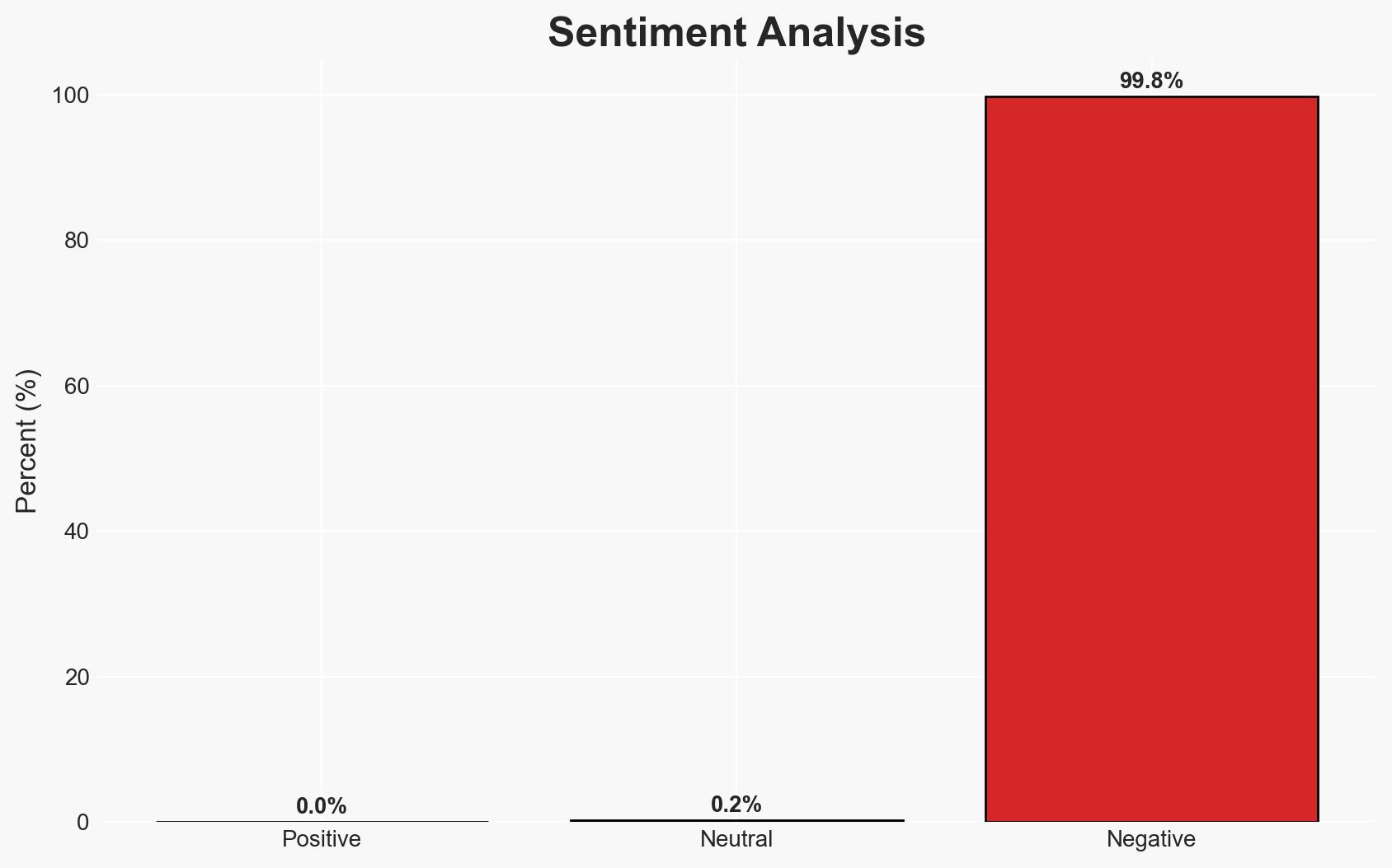
- Hypothesis A: Apple is backporting patches to protect users and maintain brand reputation, as the DarkSword tool poses a significant threat to iOS 18 users. Supporting evidence includes the widespread use of iOS 18 and the public disclosure of DarkSword. Contradicting evidence is limited but includes Apple’s historical reluctance to backport.
- Hypothesis B: Apple is primarily motivated by commercial interests, using security concerns as a pretext to encourage users to upgrade to iOS 26. Supporting evidence includes the company’s emphasis on the advanced protections of iOS 26. Contradicting evidence includes the immediate security threat posed by DarkSword.
- Assessment: Hypothesis A is currently better supported due to the immediate security risks posed by DarkSword and the potential reputational damage to Apple if users remain vulnerable. Indicators that could shift this judgment include further statements from Apple or evidence of increased marketing efforts for iOS 26.
3. Key Assumptions and Red Flags
- Assumptions: Apple has the technical capability to effectively backport patches; DarkSword poses a credible threat to iOS 18 users; user resistance to iOS 26 is significant.
- Information Gaps: Specific technical details of the DarkSword tool; Apple’s internal decision-making process regarding patching policies.
- Bias & Deception Risks: Potential bias in Apple’s public statements to downplay the severity of the threat; risk of underestimating user resistance to iOS 26.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of Apple’s security practices and influence user trust and brand loyalty. It may also set a precedent for future patching policies.
- Political / Geopolitical: Limited direct implications, but could influence global regulatory discussions on software security obligations.
- Security / Counter-Terrorism: Potentially reduces the attack surface for malicious actors exploiting iOS vulnerabilities.
- Cyber / Information Space: Highlights the importance of timely patching and may influence other tech companies’ policies.
- Economic / Social: Could impact Apple’s market share if users perceive a lack of security commitment; may affect user satisfaction and retention.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor the effectiveness of the backported patches; assess user response and update uptake rates.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms to enhance threat intelligence; consider policy adjustments for future patching strategies.
- Scenario Outlook:
- Best: Successful patch deployment with minimal disruption, enhancing user trust.
- Worst: Ineffective patches lead to widespread exploitation of iOS 18 vulnerabilities.
- Most-Likely: Gradual user migration to iOS 26 as security concerns outweigh interface preferences.
6. Key Individuals and Entities
- Apple Inc.
- iVerify
- Lookout
- DarkSword (hacking tool)
7. Thematic Tags
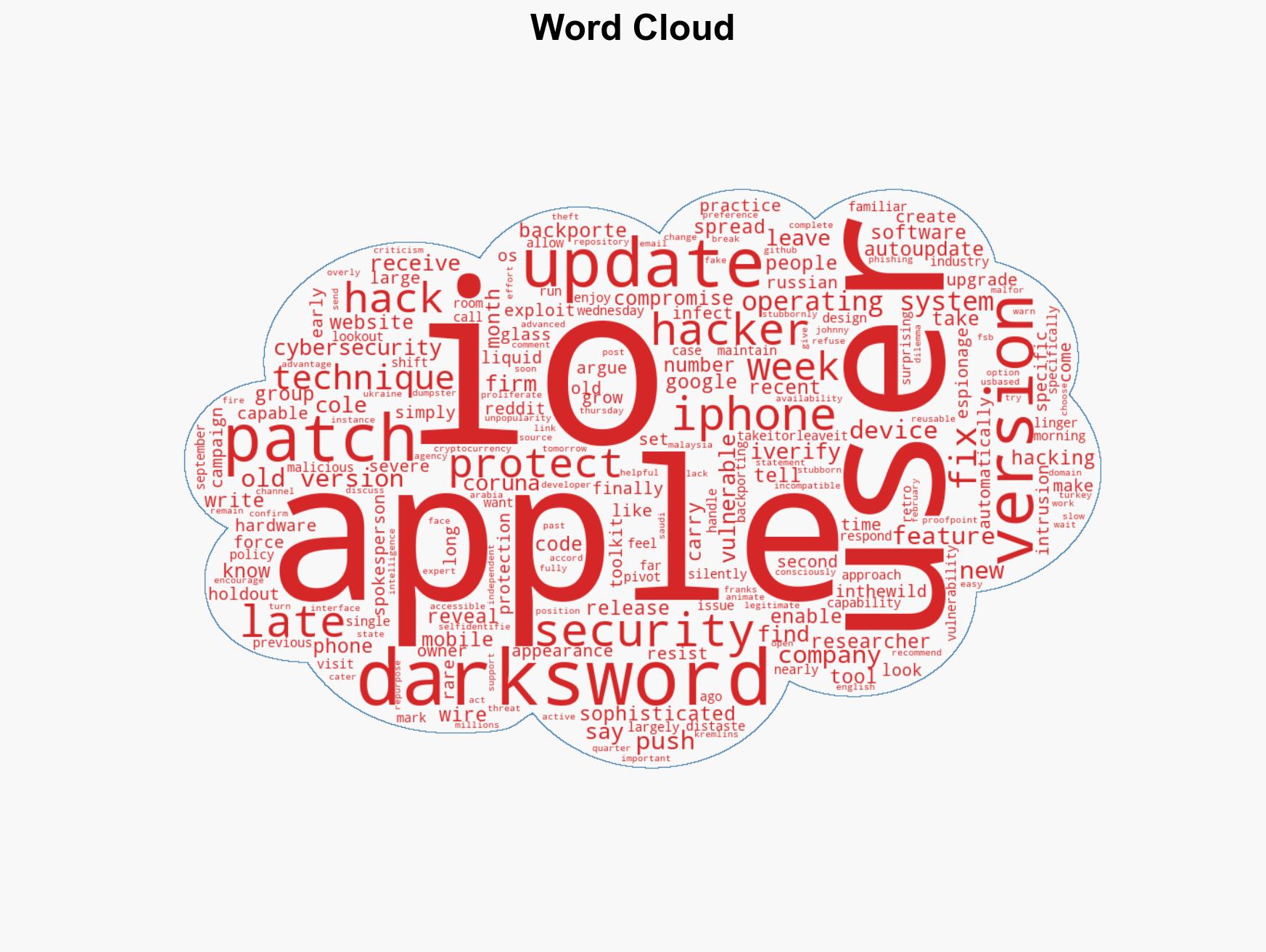
cybersecurity, software updates, mobile security, user behavior, corporate strategy, threat mitigation, digital trust
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us