Urgent Need for Comprehensive Post-Quantum Cryptography Solutions in Modern Network Security
Published on: 2026-04-01
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Why full-stack post-quantum cryptography cannot wait
1. BLUF (Bottom Line Up Front)
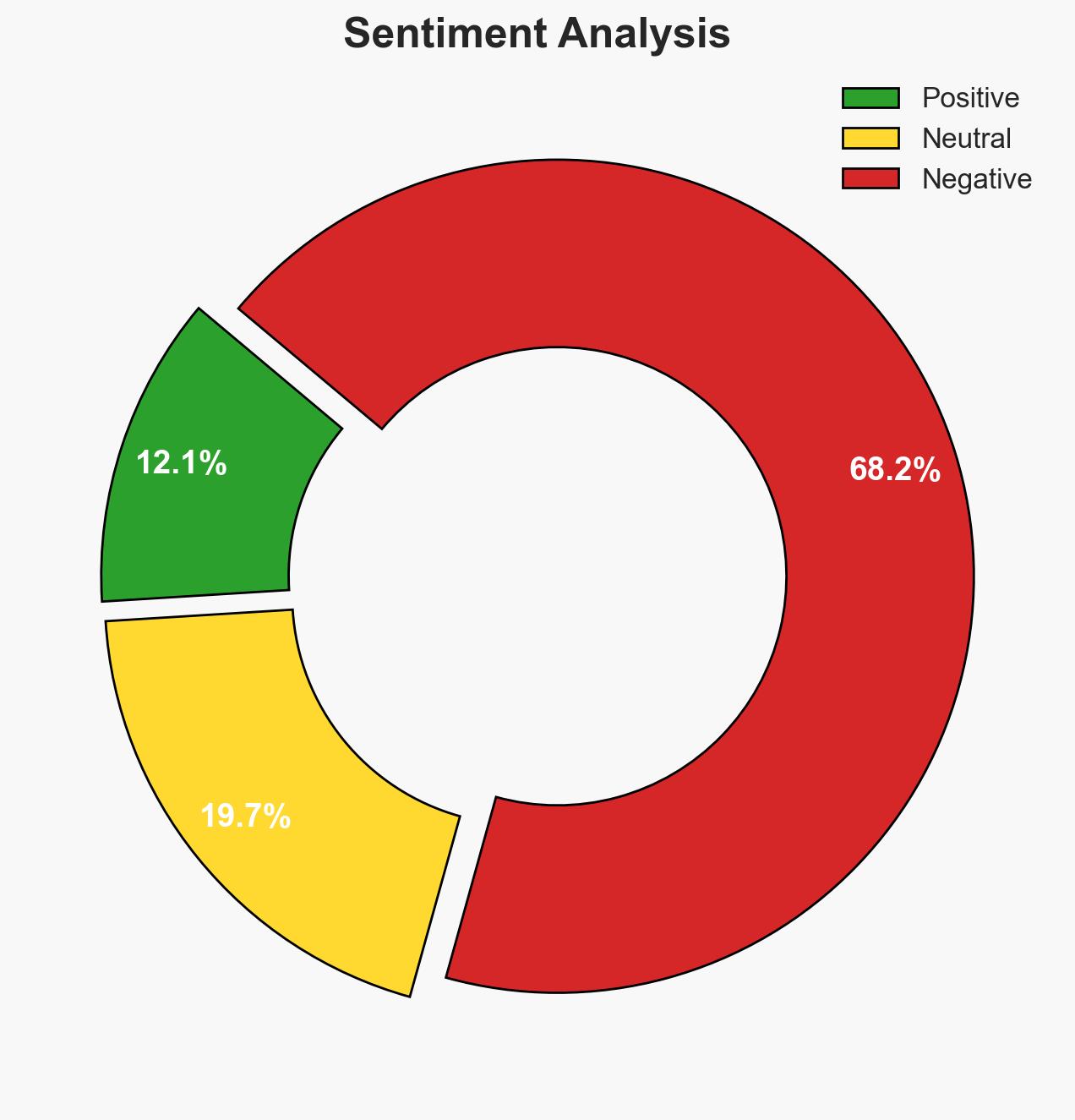
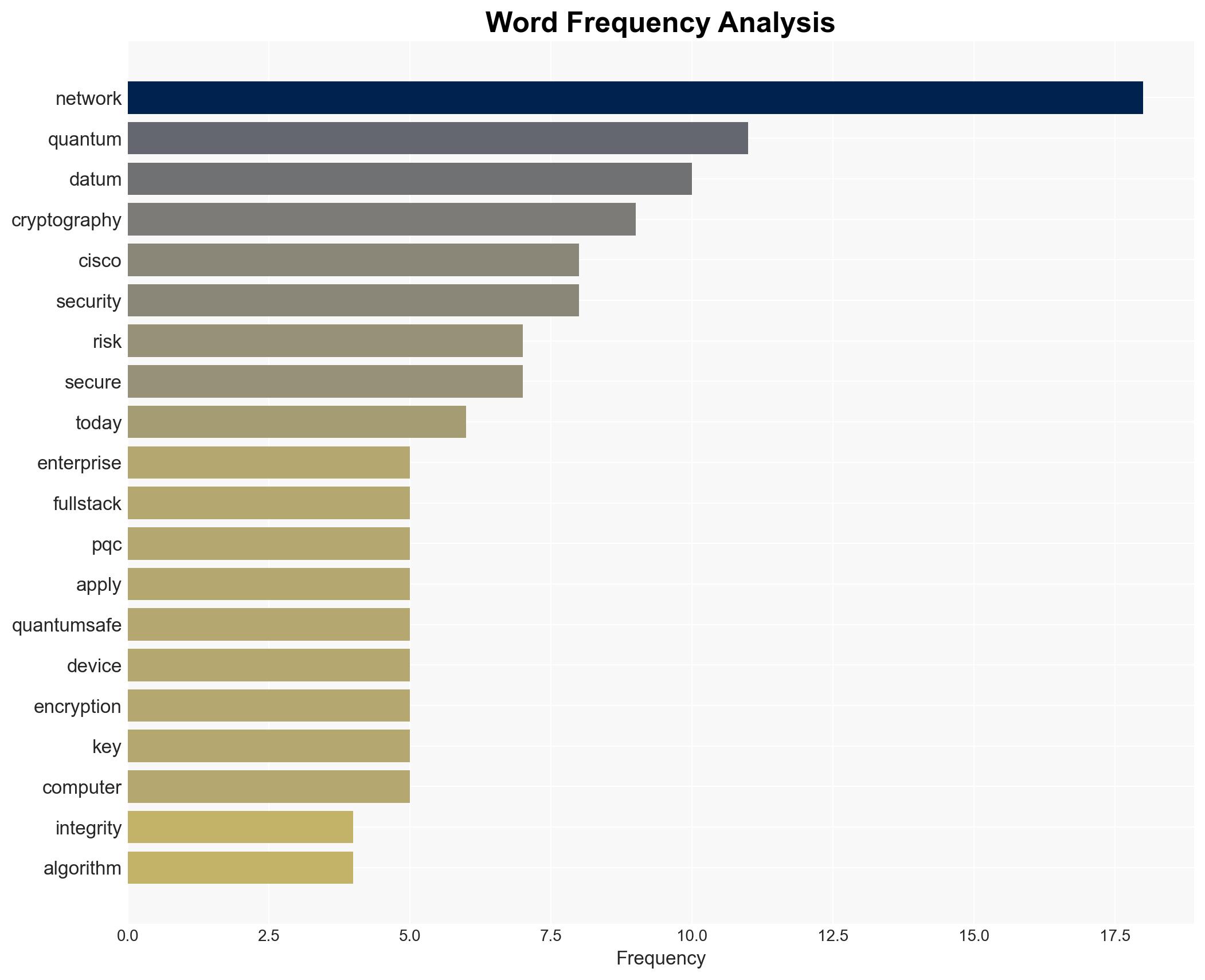
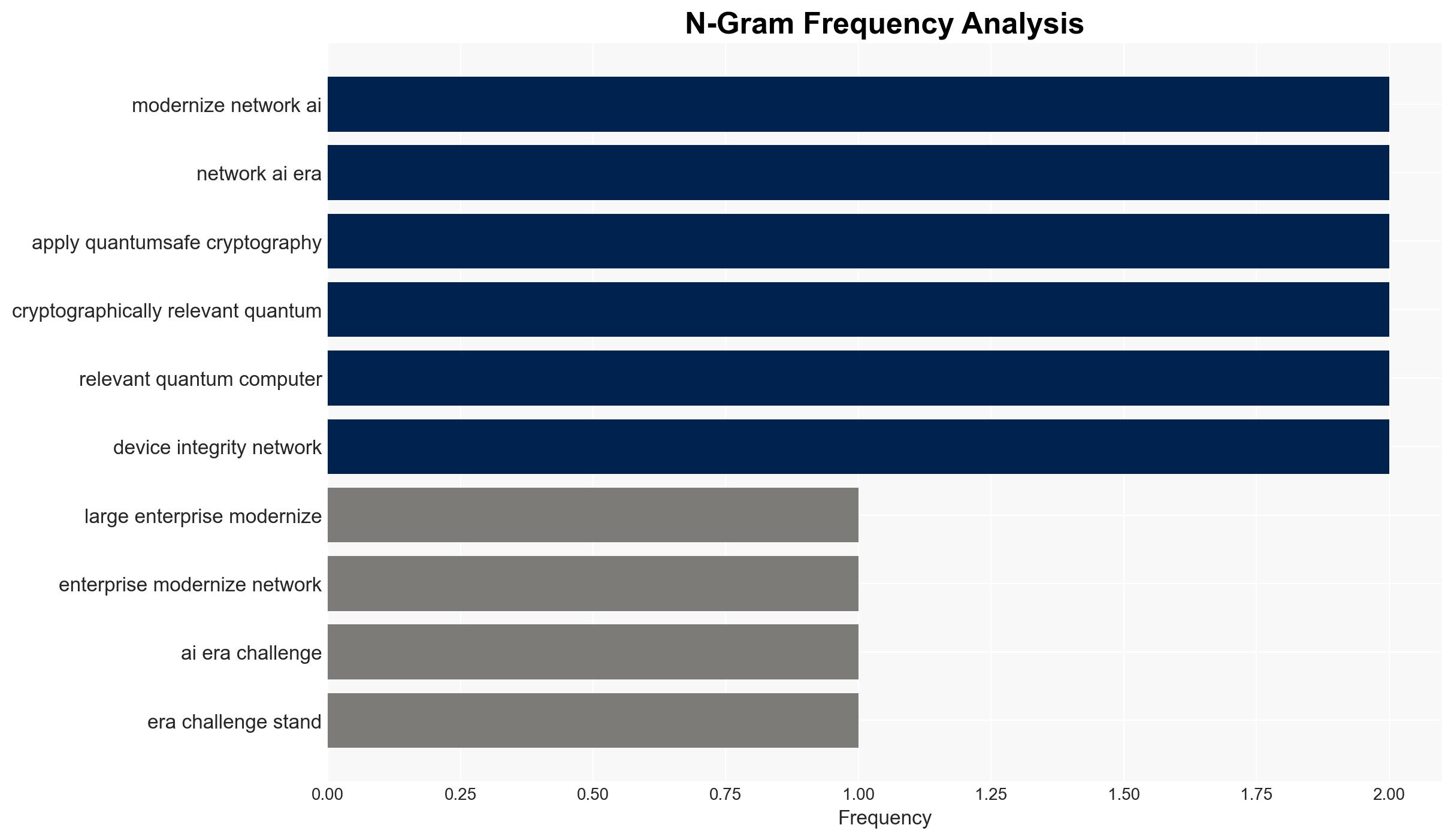
The emergence of quantum computing poses a significant threat to current cryptographic systems, necessitating the urgent adoption of post-quantum cryptography (PQC) solutions. Large enterprises, particularly those with extensive networks, are at risk of data breaches through quantum-based attacks. The introduction of full-stack PQC by Cisco represents a critical advancement in mitigating these risks. Overall confidence in this assessment is moderate, given the current pace of quantum computing development.
2. Competing Hypotheses
- Hypothesis A: Quantum computing will soon render current cryptographic systems obsolete, necessitating immediate adoption of PQC to protect data integrity. This is supported by the development of full-stack PQC solutions and the vulnerabilities in existing cryptographic mechanisms. However, the timeline for quantum computing breakthroughs remains uncertain.
- Hypothesis B: Quantum computing will not achieve the necessary capabilities to break current cryptographic systems in the near term, allowing more time for gradual adaptation to PQC. This hypothesis is less supported due to ongoing advancements in quantum research and the strategic risks of delayed action.
- Assessment: Hypothesis A is currently better supported due to the proactive measures being taken by industry leaders like Cisco and the potential for rapid advancements in quantum computing. Key indicators that could shift this judgment include breakthroughs in quantum computing capabilities or delays in PQC implementation.
3. Key Assumptions and Red Flags
- Assumptions: Quantum computing will advance to a point where it can break current cryptographic systems; PQC solutions will be effective against quantum threats; Enterprises will prioritize PQC adoption.
- Information Gaps: The exact timeline for quantum computing breakthroughs; the readiness and scalability of PQC solutions across different industries.
- Bias & Deception Risks: Over-reliance on industry reports and vendor claims; potential underestimation of quantum computing development timelines.
4. Implications and Strategic Risks
The transition to PQC is critical to maintaining data security as quantum computing evolves. Failure to adapt could lead to widespread data breaches and loss of trust in digital systems.
- Political / Geopolitical: Nations leading in quantum computing could gain strategic advantages, influencing global power dynamics.
- Security / Counter-Terrorism: Increased risk of cyber-attacks exploiting quantum vulnerabilities, potentially impacting national security.
- Cyber / Information Space: A shift in cyber defense strategies and increased focus on developing quantum-resistant algorithms.
- Economic / Social: Potential economic disruptions from data breaches; increased investment in PQC technologies.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive risk assessment of current cryptographic systems; initiate pilot projects for PQC implementation.
- Medium-Term Posture (1–12 months): Develop partnerships with technology leaders in PQC; invest in research and development of quantum-resistant technologies.
- Scenario Outlook:
- Best: Successful global adoption of PQC, mitigating quantum threats.
- Worst: Quantum computing breakthroughs outpace PQC adoption, leading to widespread data breaches.
- Most-Likely: Gradual adoption of PQC with ongoing advancements in quantum computing, requiring continuous adaptation.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
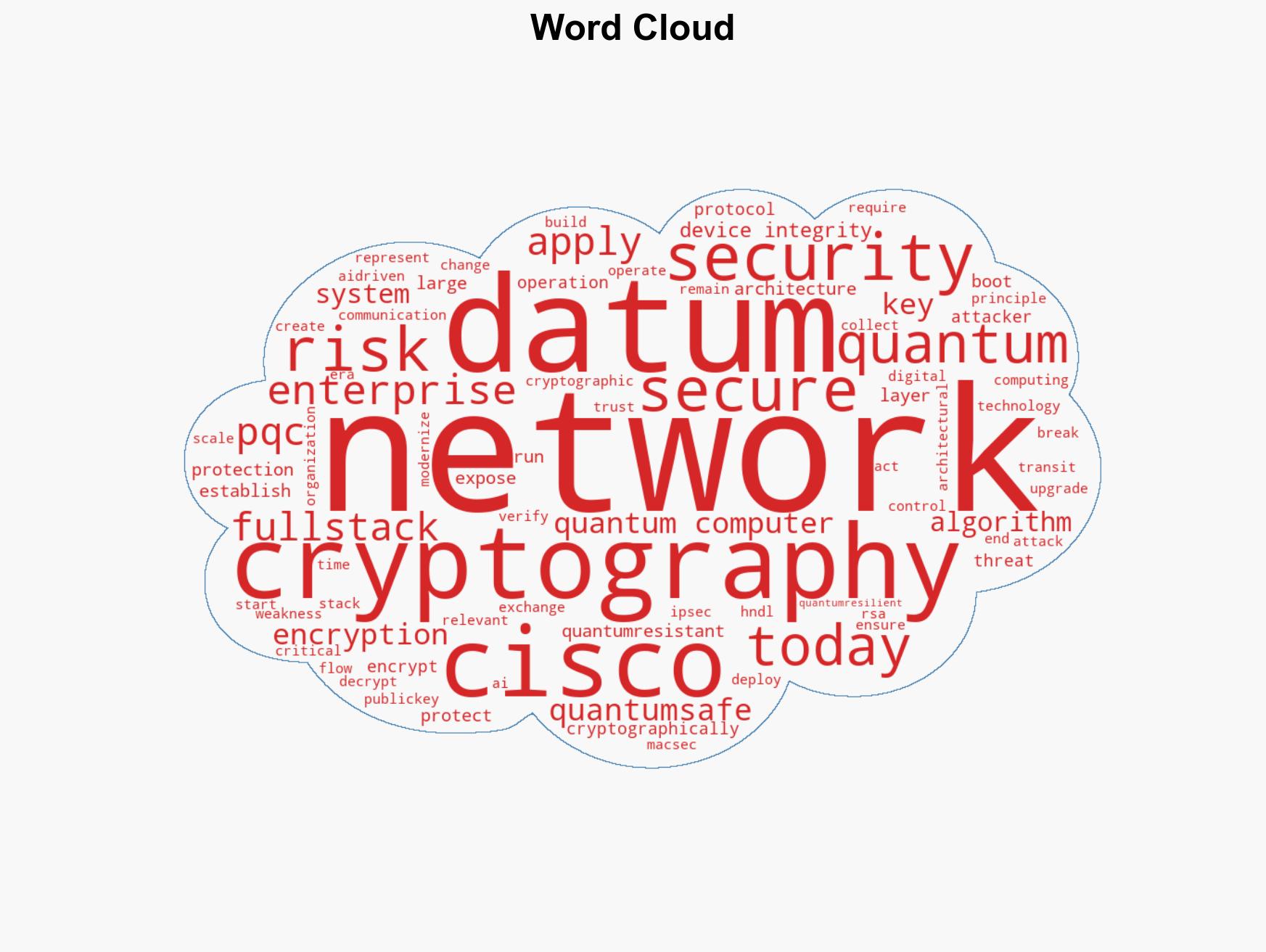
cybersecurity, quantum computing, post-quantum cryptography, data protection, enterprise security, cryptographic vulnerabilities, technology risk
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us