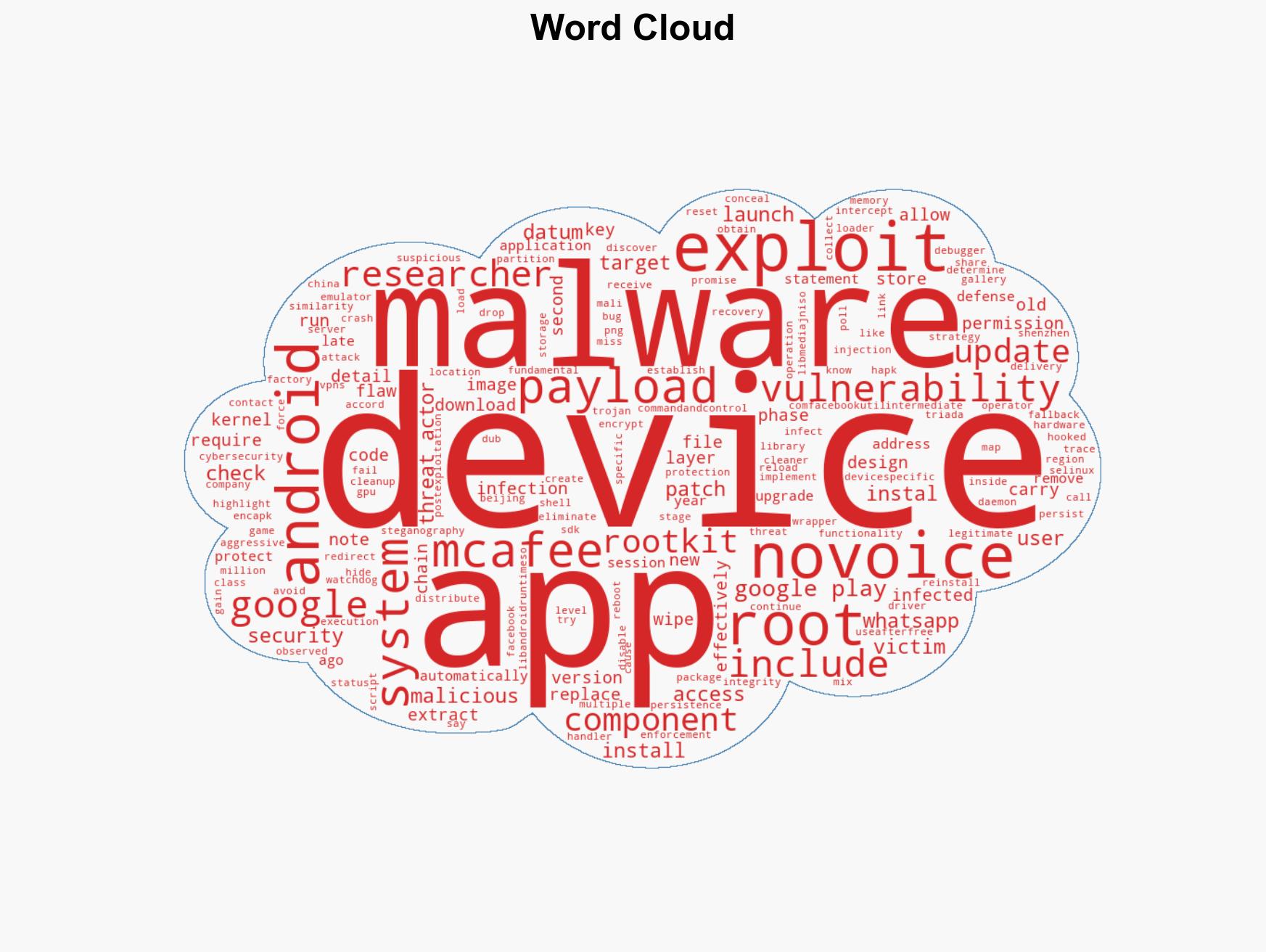
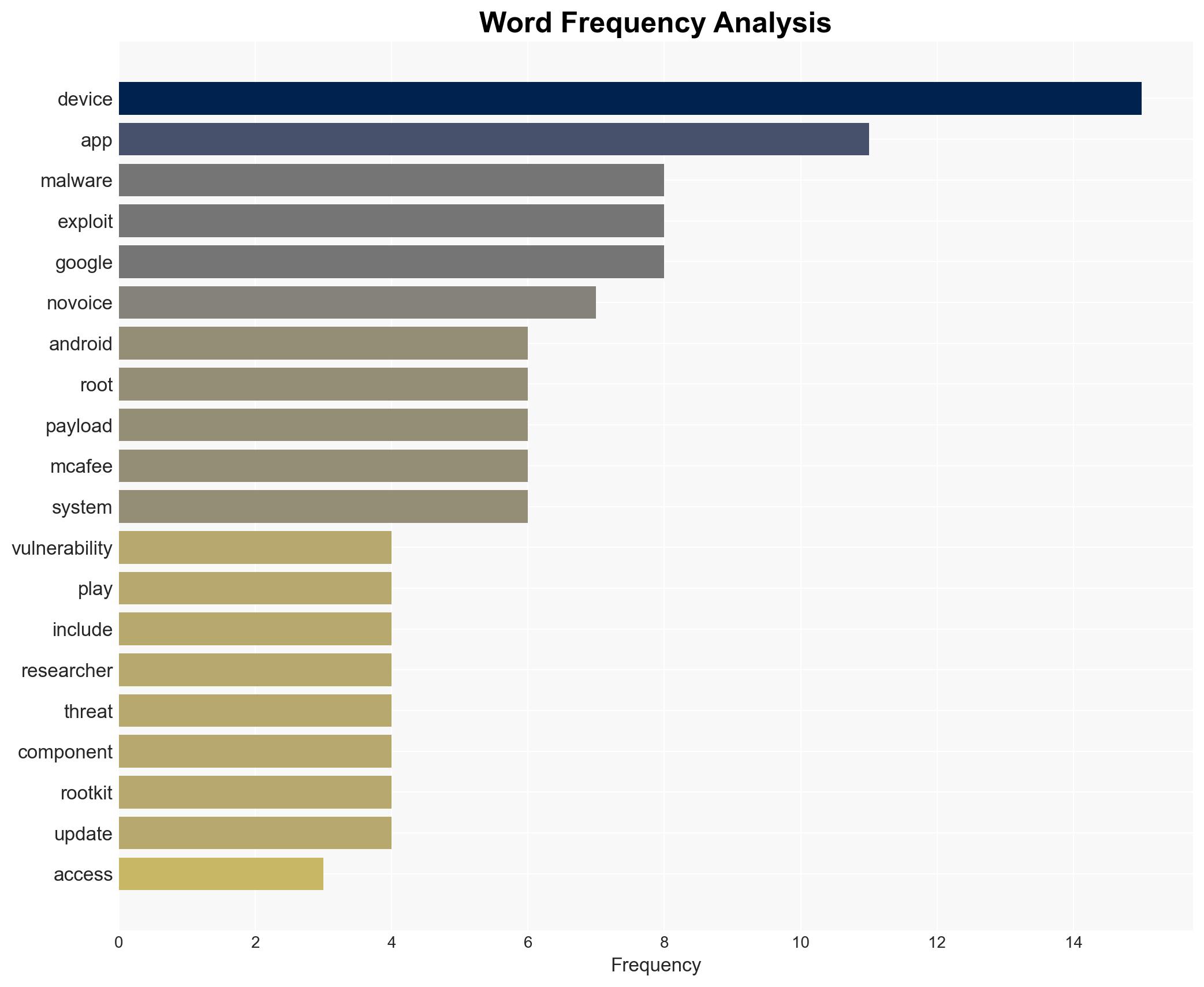
Android Malware NoVoice Infects 23 Million Devices via Over 50 Apps on Google Play Store
Published on: 2026-04-01
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: ‘NoVoice’ Android malware on Google Play infected 23 million devices
1. BLUF (Bottom Line Up Front)
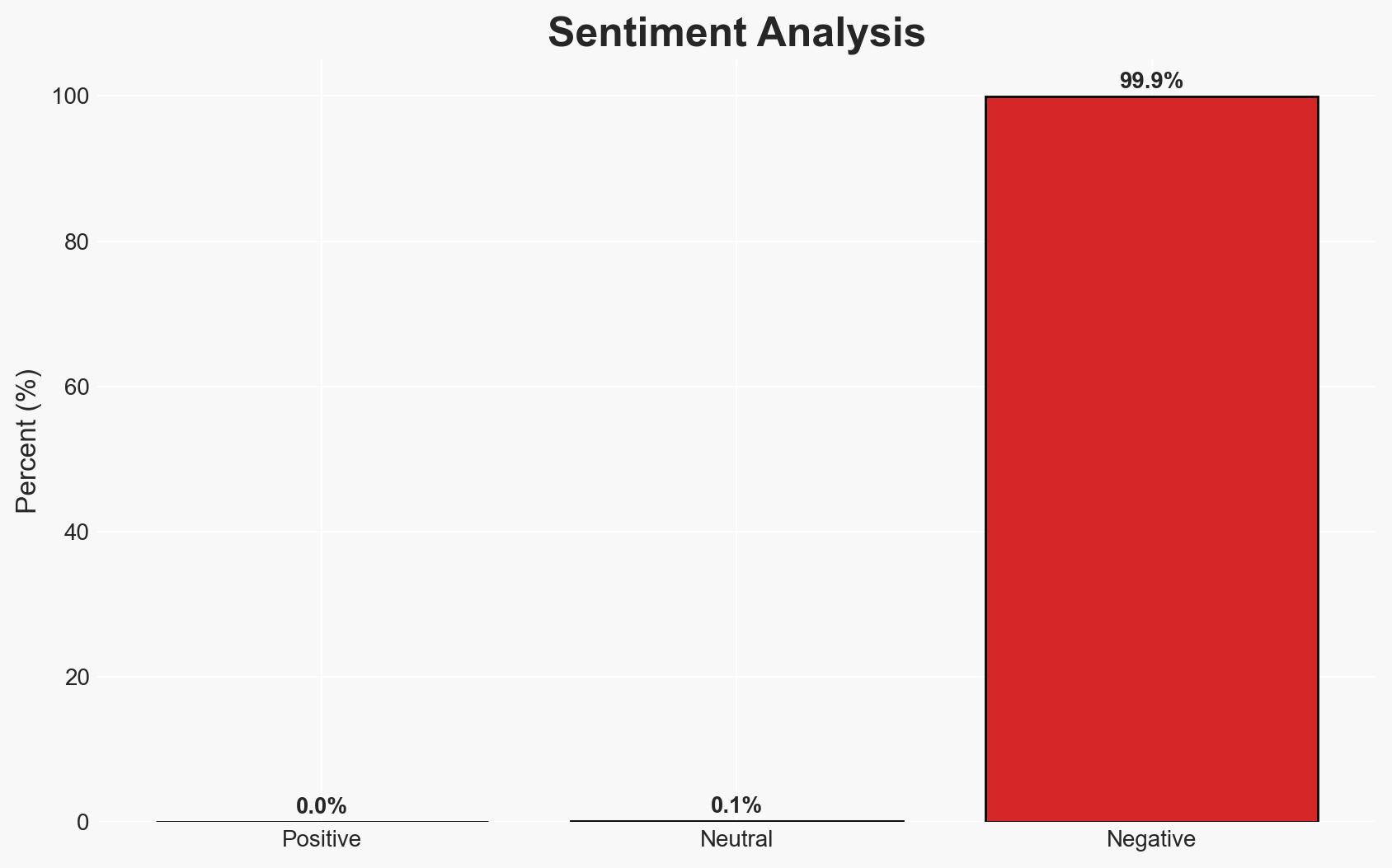
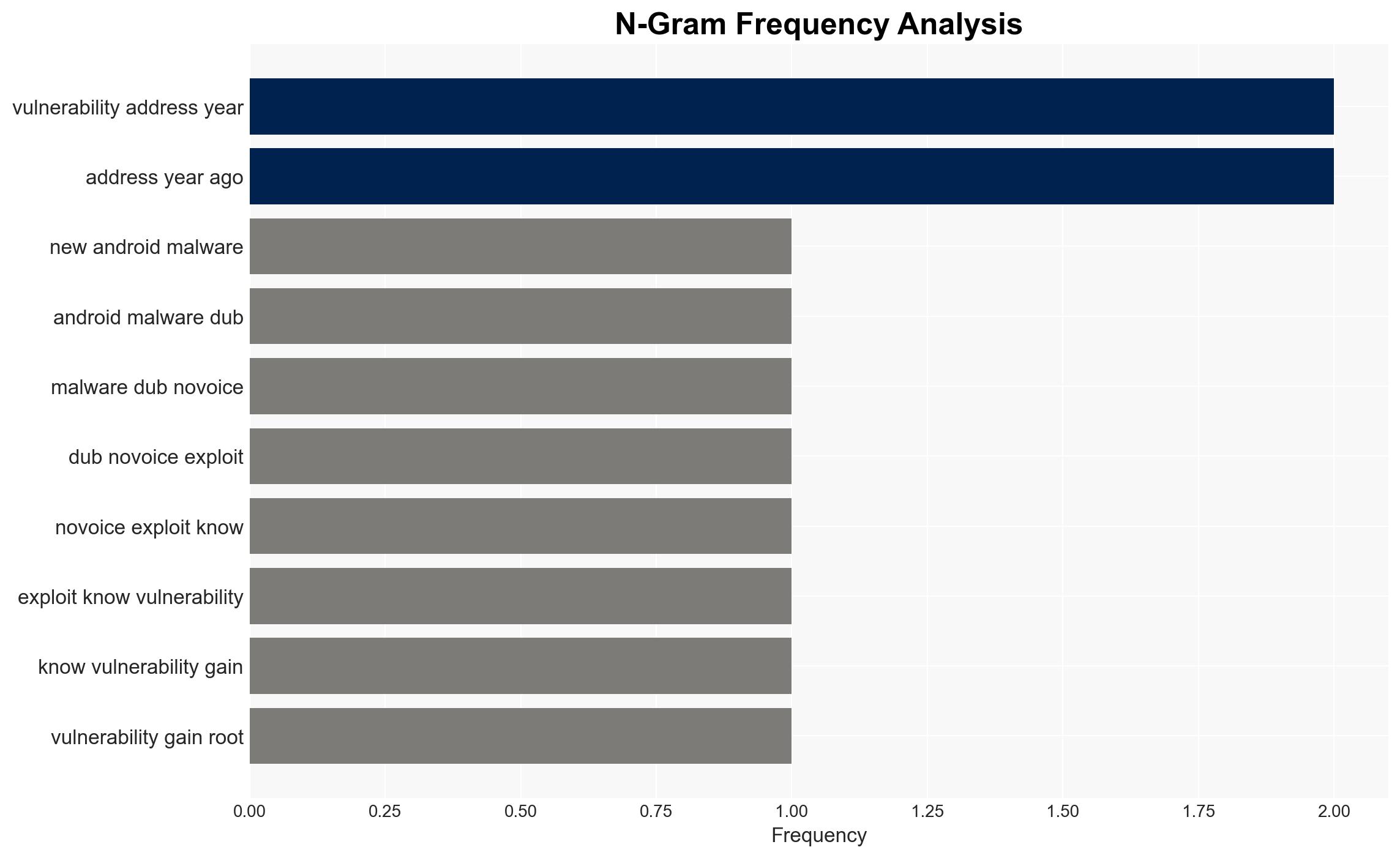
The ‘NoVoice’ malware has infected approximately 23 million Android devices via the Google Play Store, exploiting known vulnerabilities to gain root access. The malware’s sophisticated evasion techniques and persistence mechanisms pose a significant threat to device security and user privacy. The absence of a clearly identified threat actor complicates attribution efforts. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The ‘NoVoice’ malware is the work of a sophisticated cybercriminal group aiming for financial gain through device exploitation. This is supported by the malware’s advanced techniques and the potential for monetization through data theft or selling access. However, the lack of direct financial transactions observed contradicts this.
- Hypothesis B: The malware is part of a state-sponsored cyber-espionage campaign, possibly targeting specific regions or individuals. The selective infection avoidance in certain Chinese regions and the advanced evasion techniques support this. Contradictory evidence includes the lack of direct links to any state actor.
- Assessment: Hypothesis B is currently better supported due to the malware’s complexity and regional infection patterns. Indicators that could shift this judgment include the discovery of financial transactions or direct links to known cybercriminal groups.
3. Key Assumptions and Red Flags
- Assumptions: The malware’s primary goal is to maintain persistent access to infected devices; the threat actor has advanced technical capabilities; the infection pattern is deliberate and strategic.
- Information Gaps: The identity of the threat actor; specific objectives of the malware beyond device rooting; the full scope of affected regions and devices.
- Bias & Deception Risks: Potential bias in attributing state sponsorship without clear evidence; deception risks include false flag operations or misdirection by the threat actor.
4. Implications and Strategic Risks
The ‘NoVoice’ malware’s persistence and evasion capabilities could lead to prolonged exploitation of affected devices, impacting user privacy and security. The ongoing threat may necessitate increased scrutiny of app marketplaces and device security protocols.
- Political / Geopolitical: Potential diplomatic tensions if state sponsorship is confirmed, particularly involving China.
- Security / Counter-Terrorism: Increased risk of cyber-attacks on critical infrastructure if similar techniques are employed.
- Cyber / Information Space: Heightened awareness and potential regulatory changes in app distribution and security practices.
- Economic / Social: Potential loss of consumer trust in digital marketplaces, impacting app developers and platform operators.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of app stores for similar threats; issue security patches and advisories to affected users; collaborate with cybersecurity firms for threat intelligence sharing.
- Medium-Term Posture (1–12 months): Develop partnerships with international cybersecurity agencies; invest in advanced threat detection and response capabilities; promote user education on device security.
- Scenario Outlook:
- Best: Rapid identification and neutralization of the threat actor, leading to minimal long-term impact.
- Worst: Escalation to widespread cyber-attacks on critical infrastructure, causing significant disruption.
- Most-Likely: Continued low-level exploitation with periodic spikes in activity, prompting ongoing security enhancements.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, malware, mobile security, cyber-espionage, app security, threat intelligence, digital privacy
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us