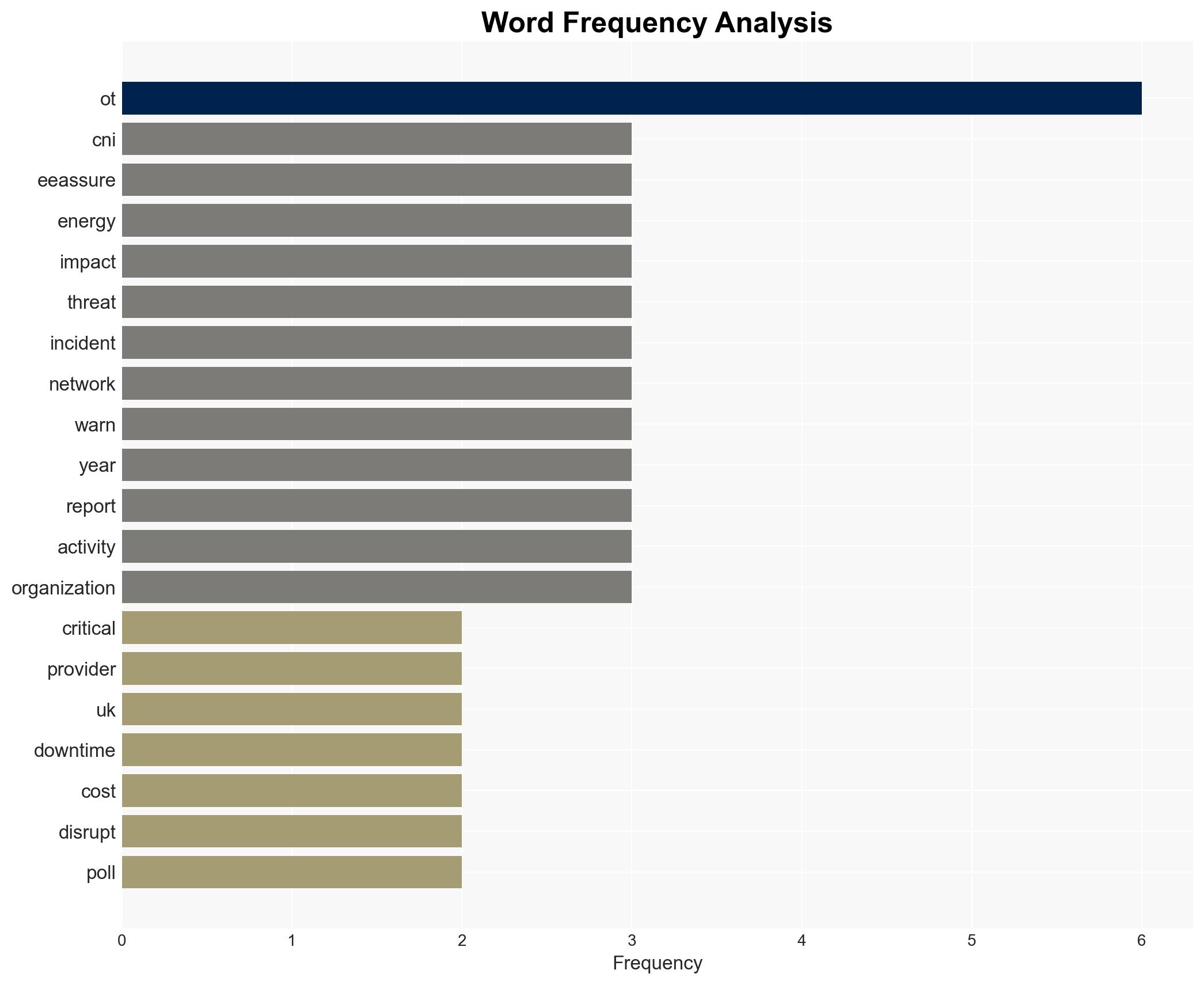
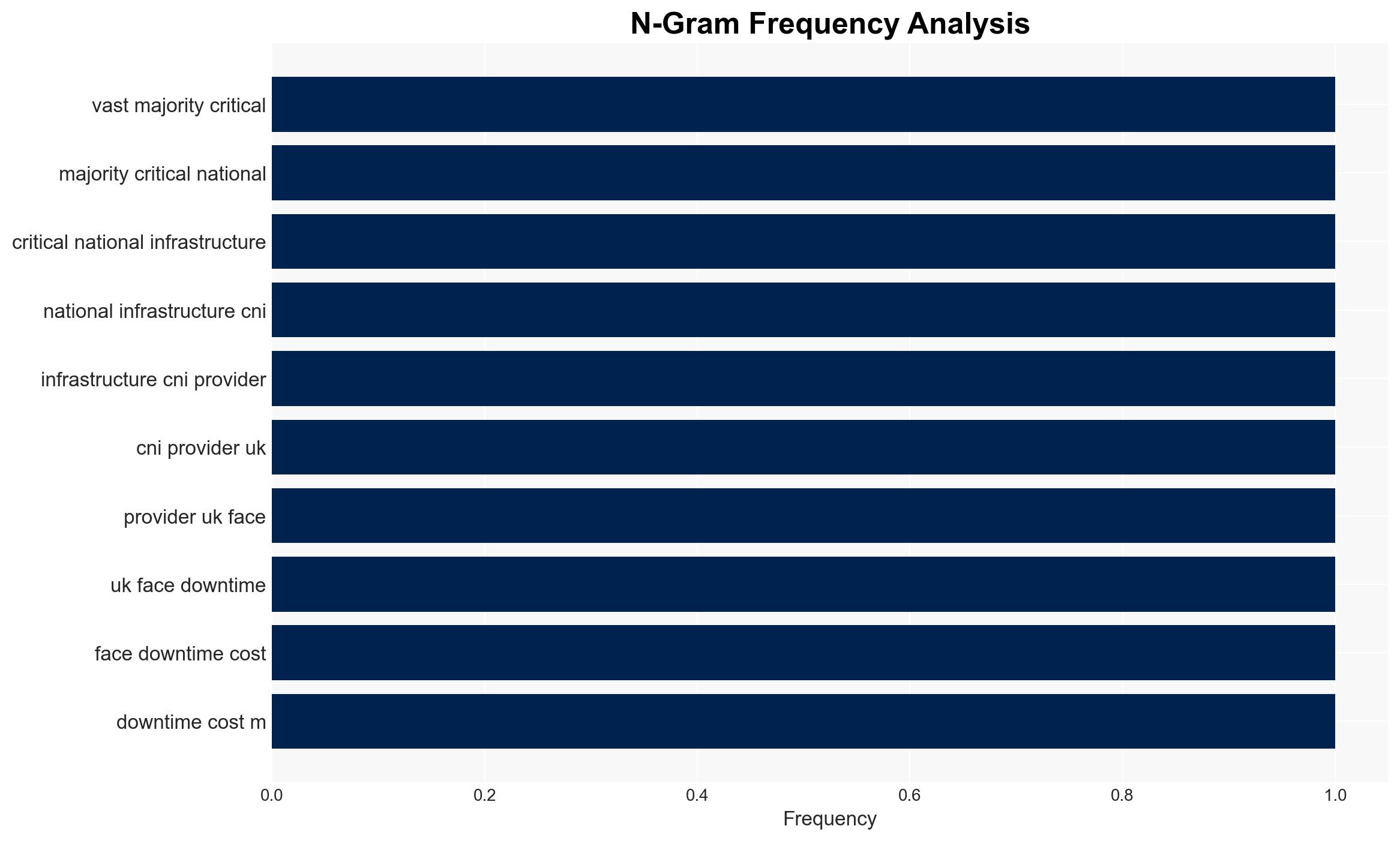
UK CNI Providers Risk Up to £5m in Losses Due to Operational Technology Cyber Attacks
Published on: 2026-04-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Most CNI Firms Face Up to 5m in Downtime from OT Attacks
1. BLUF (Bottom Line Up Front)
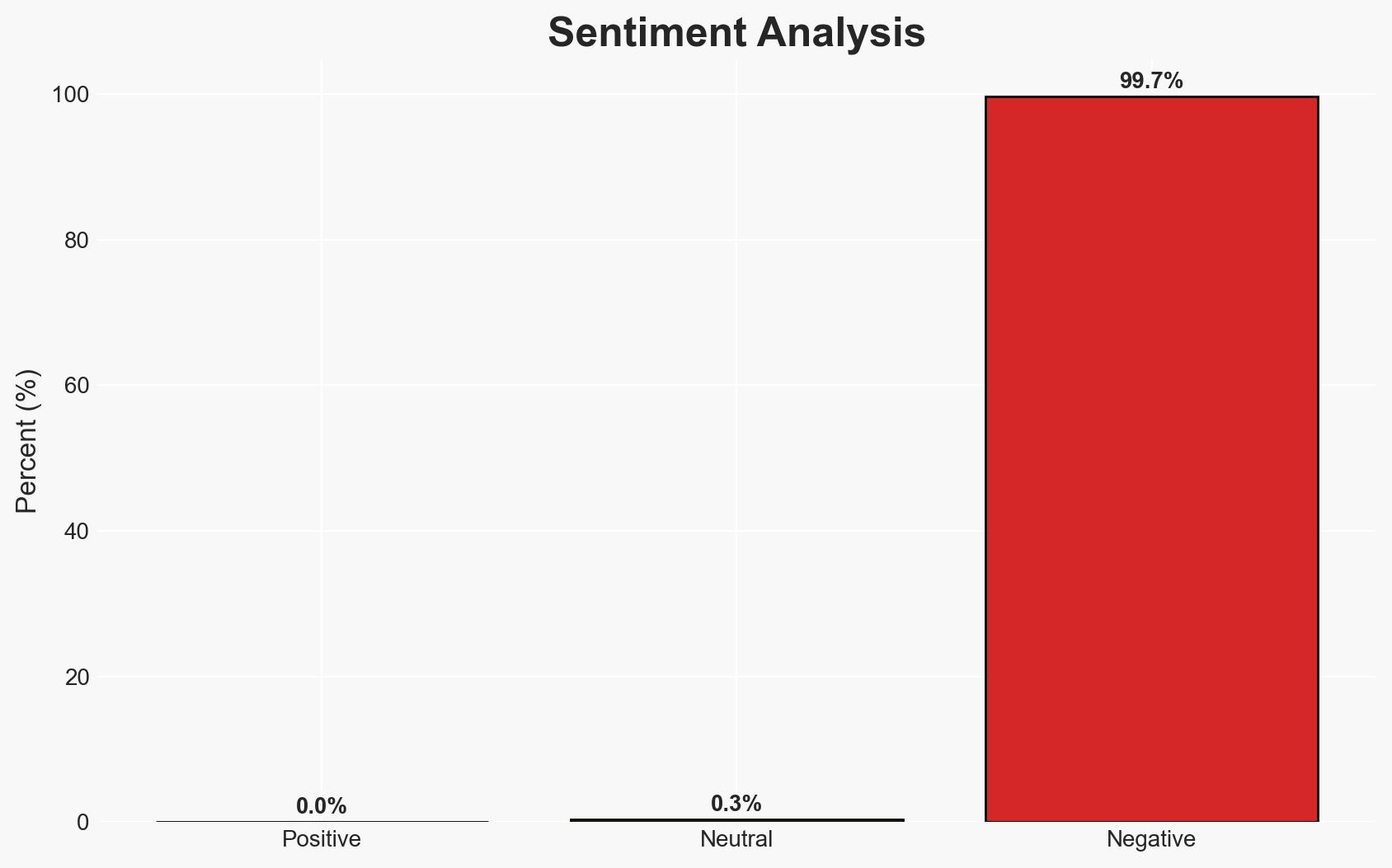
The majority of UK critical national infrastructure (CNI) providers face significant financial risks from operational technology (OT) cyber-attacks, with potential downtime costs reaching up to £5 million. The primary concern is nation-state actors leveraging cyber capabilities to disrupt essential services. The current assessment, with moderate confidence, supports the hypothesis that these threats are primarily driven by geopolitical tensions and strategic objectives.
2. Competing Hypotheses
- Hypothesis A: Nation-state actors are primarily responsible for OT attacks on UK CNI, aiming to disrupt operations for strategic geopolitical gains. Supporting evidence includes the fear expressed by 64% of respondents regarding nation-state attacks and historical precedents of Iranian cyber activities. Contradicting evidence includes the lack of direct attribution in some incidents.
- Hypothesis B: Cybercriminal groups are the main perpetrators, motivated by financial gain rather than geopolitical objectives. This is supported by the significant financial impact reported and the common use of phishing and compromised credentials. However, the strategic nature of targeting CNI suggests a more complex motivation.
- Assessment: Hypothesis A is currently better supported due to the strategic nature of the attacks and the expressed concerns about nation-state threats. Indicators such as increased geopolitical tensions and specific targeting of CNI could further validate this hypothesis.
3. Key Assumptions and Red Flags
- Assumptions: CNI providers have limited detection capabilities; nation-state actors prioritize strategic disruption over financial gain; geopolitical tensions influence cyber threat levels.
- Information Gaps: Detailed attribution of specific OT attacks; comprehensive visibility into OT network activities across all CNI sectors.
- Bias & Deception Risks: Potential bias in survey responses due to fear of nation-state capabilities; possible underreporting of cybercriminal activities due to focus on nation-state threats.
4. Implications and Strategic Risks
The evolving threat landscape suggests increasing sophistication and frequency of OT attacks, potentially exacerbating geopolitical tensions and impacting national security.
- Political / Geopolitical: Escalation of cyber operations could lead to diplomatic tensions and retaliatory measures.
- Security / Counter-Terrorism: Enhanced threat environment necessitates improved defensive measures and intelligence sharing.
- Cyber / Information Space: Increased focus on securing OT environments and mitigating supply chain vulnerabilities.
- Economic / Social: Potential for significant economic losses and public distrust in essential services if disruptions persist.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of OT networks, conduct vulnerability assessments, and increase awareness of phishing tactics.
- Medium-Term Posture (1–12 months): Develop partnerships for intelligence sharing, invest in advanced threat detection technologies, and strengthen supply chain security protocols.
- Scenario Outlook:
- Best Case: Improved defenses deter attacks, leading to decreased incidents.
- Worst Case: Escalation of attacks results in widespread service disruptions and economic damage.
- Most Likely: Continued targeted attacks with incremental improvements in defense and resilience.
6. Key Individuals and Entities
- Rob Demain, CEO at e2e-assure
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
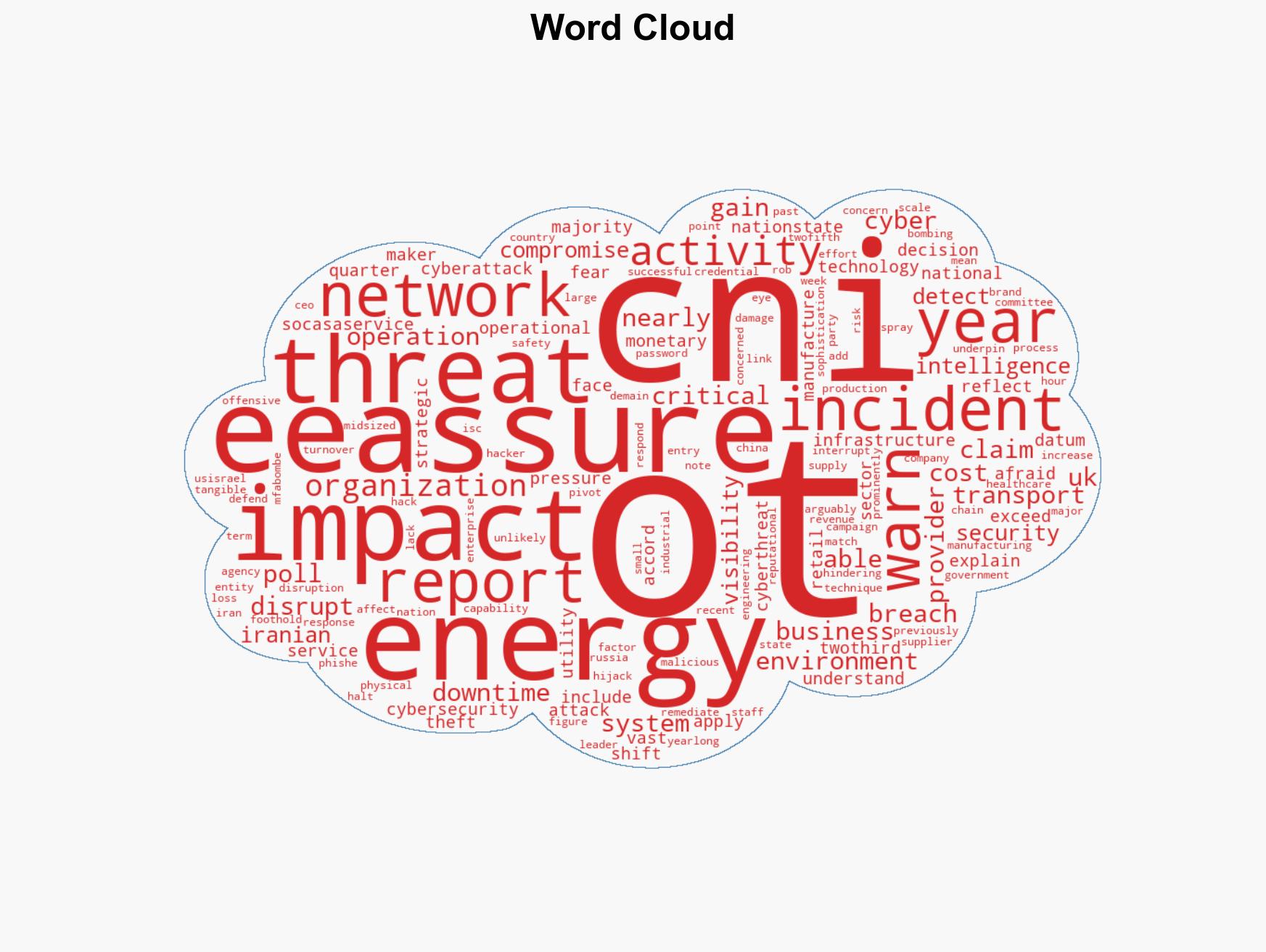
cybersecurity, critical infrastructure, nation-state threats, operational technology, geopolitical tensions, cyber defense, supply chain security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us