Akira Group Executes Ransomware Attacks in Under One Hour, Highlighting Increased Threat Velocity
Published on: 2026-04-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Researchers Observe Sub-One-Hour Ransomware Attacks
1. BLUF (Bottom Line Up Front)
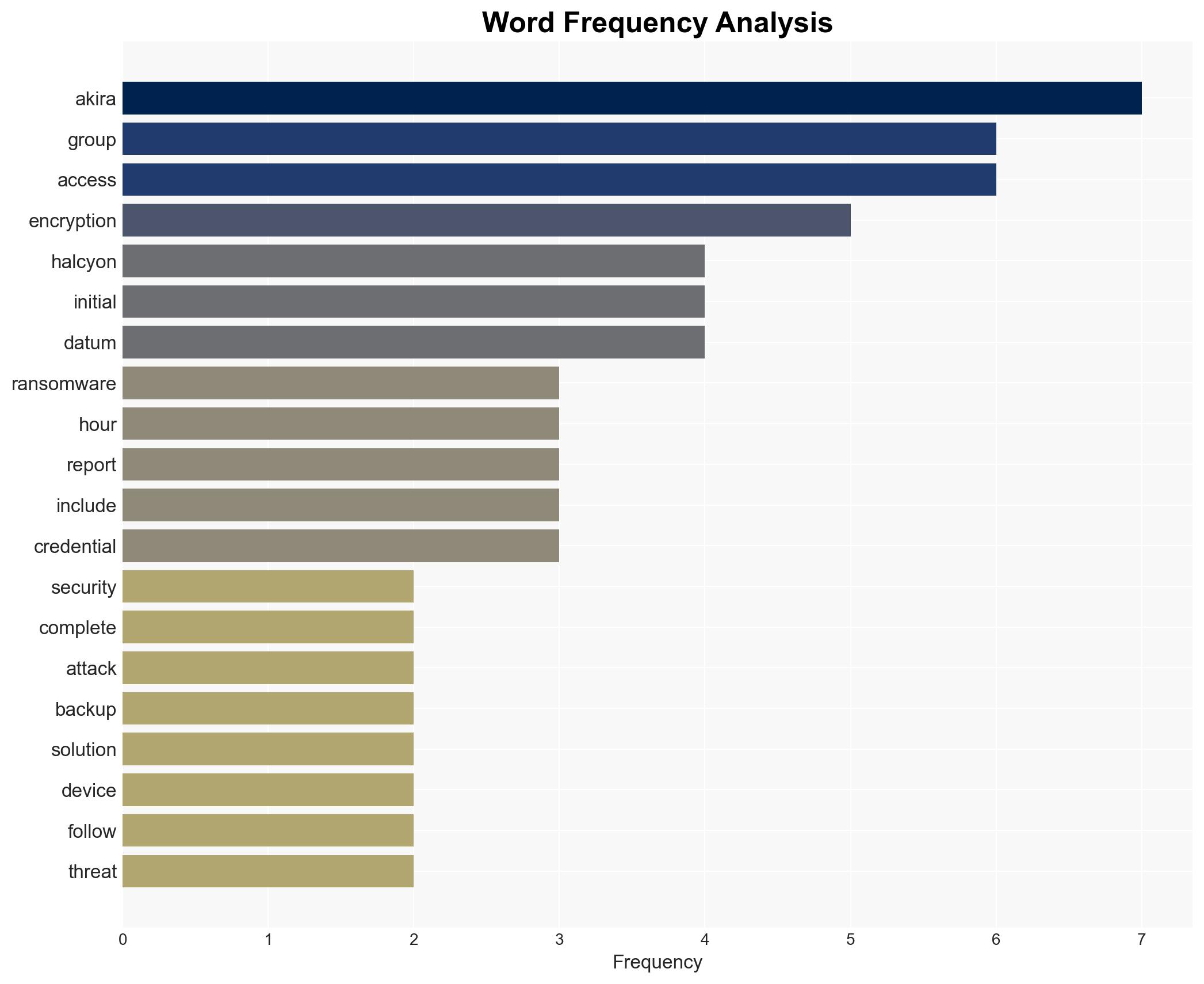
The Akira ransomware group has demonstrated the capability to execute complete ransomware attacks in under one hour, posing a significant threat to organizations with inadequate cybersecurity measures. This rapid attack velocity is primarily facilitated by exploiting vulnerabilities in VPN appliances and backup solutions. The most likely hypothesis is that Akira will continue to refine its techniques, increasing the frequency and impact of attacks. Overall confidence level: moderate.
2. Competing Hypotheses
- Hypothesis A: Akira’s rapid attack capability is primarily due to exploiting specific vulnerabilities in VPN appliances and backup solutions. Evidence includes observed use of these vulnerabilities and the group’s sophisticated operational methods. Key uncertainties include the potential for Akira to develop new attack vectors.
- Hypothesis B: Akira’s success is largely due to its use of credential theft and initial access brokers, rather than specific technical vulnerabilities. Supporting evidence includes reports of credential theft and use of IABs. Contradicting evidence is the emphasis on exploiting VPN and backup vulnerabilities.
- Assessment: Hypothesis A is currently better supported due to the detailed evidence of specific vulnerabilities being exploited. Indicators that could shift this judgment include new reports of Akira using alternative methods for initial access.
3. Key Assumptions and Red Flags
- Assumptions: Akira will continue to target known vulnerabilities; organizations will not universally adopt MFA; Akira’s operational tempo will remain high; current defensive measures are insufficient.
- Information Gaps: Detailed technical specifics of Akira’s encryption methods; comprehensive list of targeted organizations; full extent of financial impact.
- Bias & Deception Risks: Potential source bias from cybersecurity firms with vested interests in promoting certain solutions; deception risk from Akira using misinformation to mislead defenders.
4. Implications and Strategic Risks
The rapid evolution of ransomware tactics by groups like Akira could lead to increased frequency and severity of cyber-attacks, challenging existing cybersecurity frameworks.
- Political / Geopolitical: Potential for increased tensions between nations over perceived state-sponsored cyber activities.
- Security / Counter-Terrorism: Heightened threat environment requiring enhanced cybersecurity measures and collaboration among law enforcement agencies.
- Cyber / Information Space: Accelerated arms race in cyber capabilities between attackers and defenders, with potential for significant data breaches.
- Economic / Social: Increased financial losses for businesses, potential for economic instability, and erosion of public trust in digital systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Implement MFA across all systems, conduct vulnerability assessments, and enhance monitoring for suspicious activities.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms, invest in employee training, and update incident response plans.
- Scenario Outlook:
- Best Case: Organizations adopt robust defenses, reducing attack success rates.
- Worst Case: Akira and similar groups increase attack frequency and sophistication, overwhelming defenses.
- Most-Likely: Continued evolution of ransomware tactics with incremental improvements in organizational defenses.
6. Key Individuals and Entities
- Akira ransomware group
- SonicWall
- Veeam
- Cisco
- Halcyon (cybersecurity firm)
- US government
7. Thematic Tags
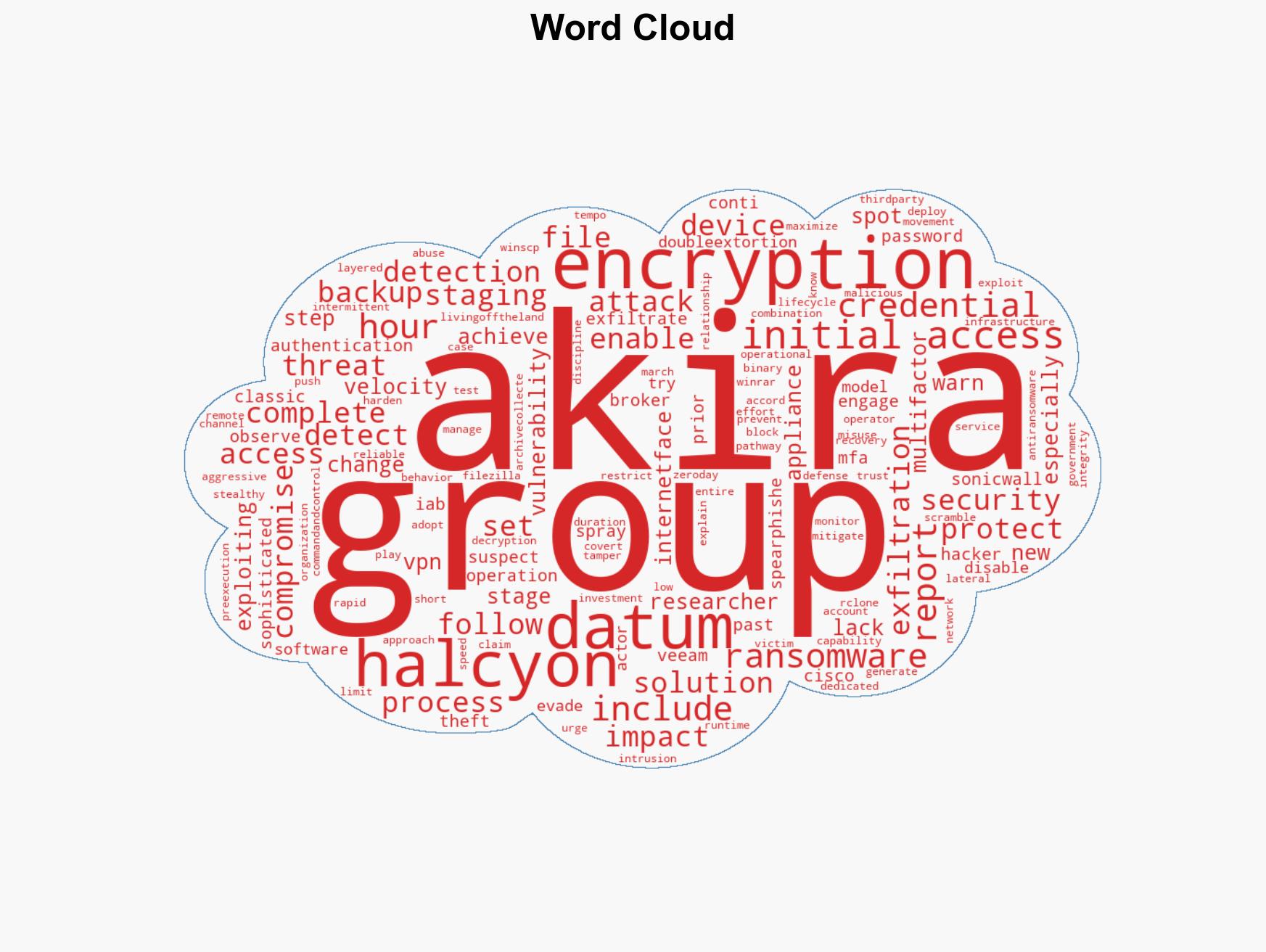
cybersecurity, ransomware, cyber-attacks, data exfiltration, threat actors, vulnerability exploitation, cyber defense
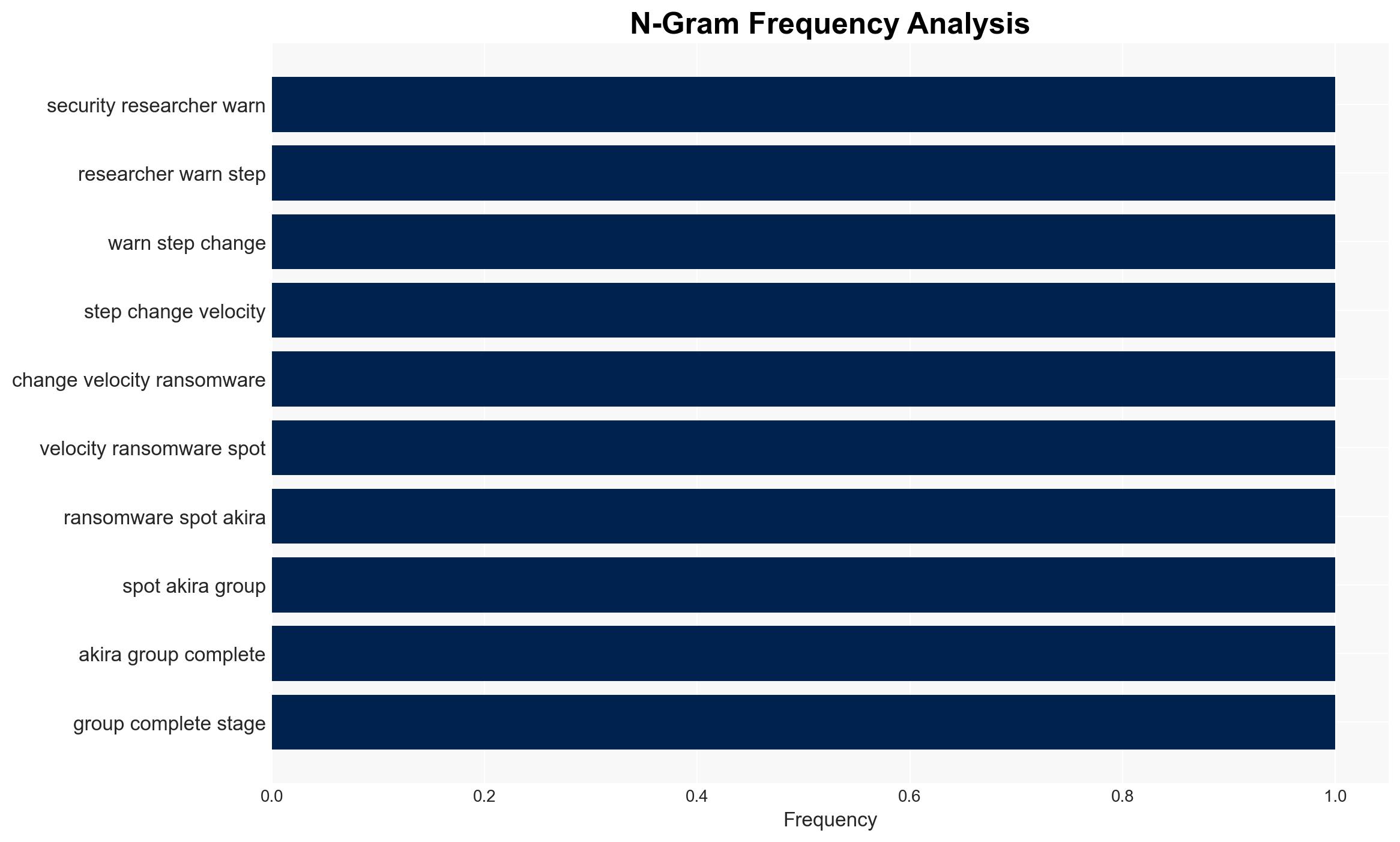
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us