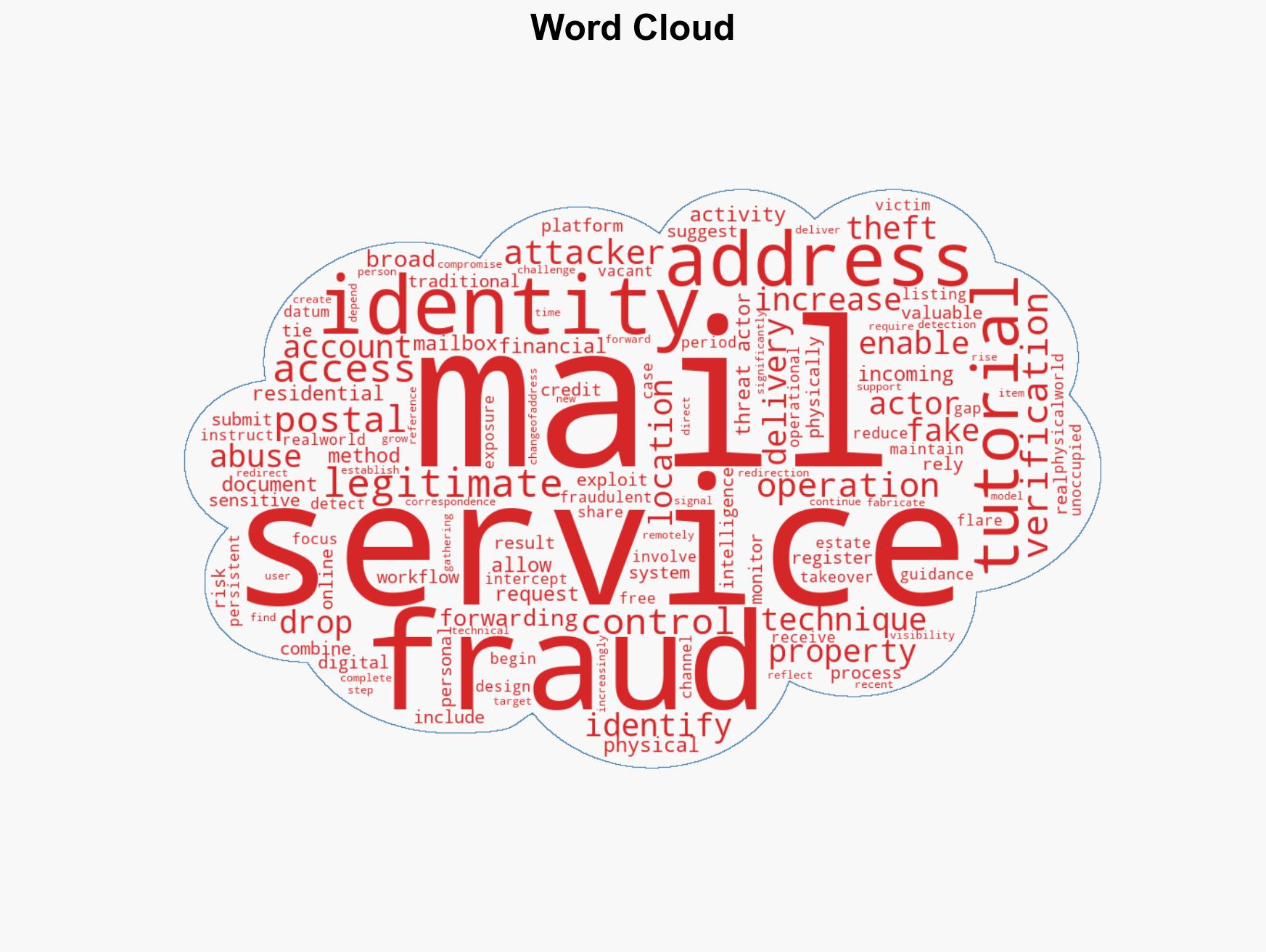
Fraudsters Target Vacant Homes to Steal Mail and Commit Identity Theft in Evolving Cybercrime Tactics
Published on: 2026-04-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Adversaries Exploit Vacant Homes to Intercept Mail in Hybrid Cybercrime
1. BLUF (Bottom Line Up Front)
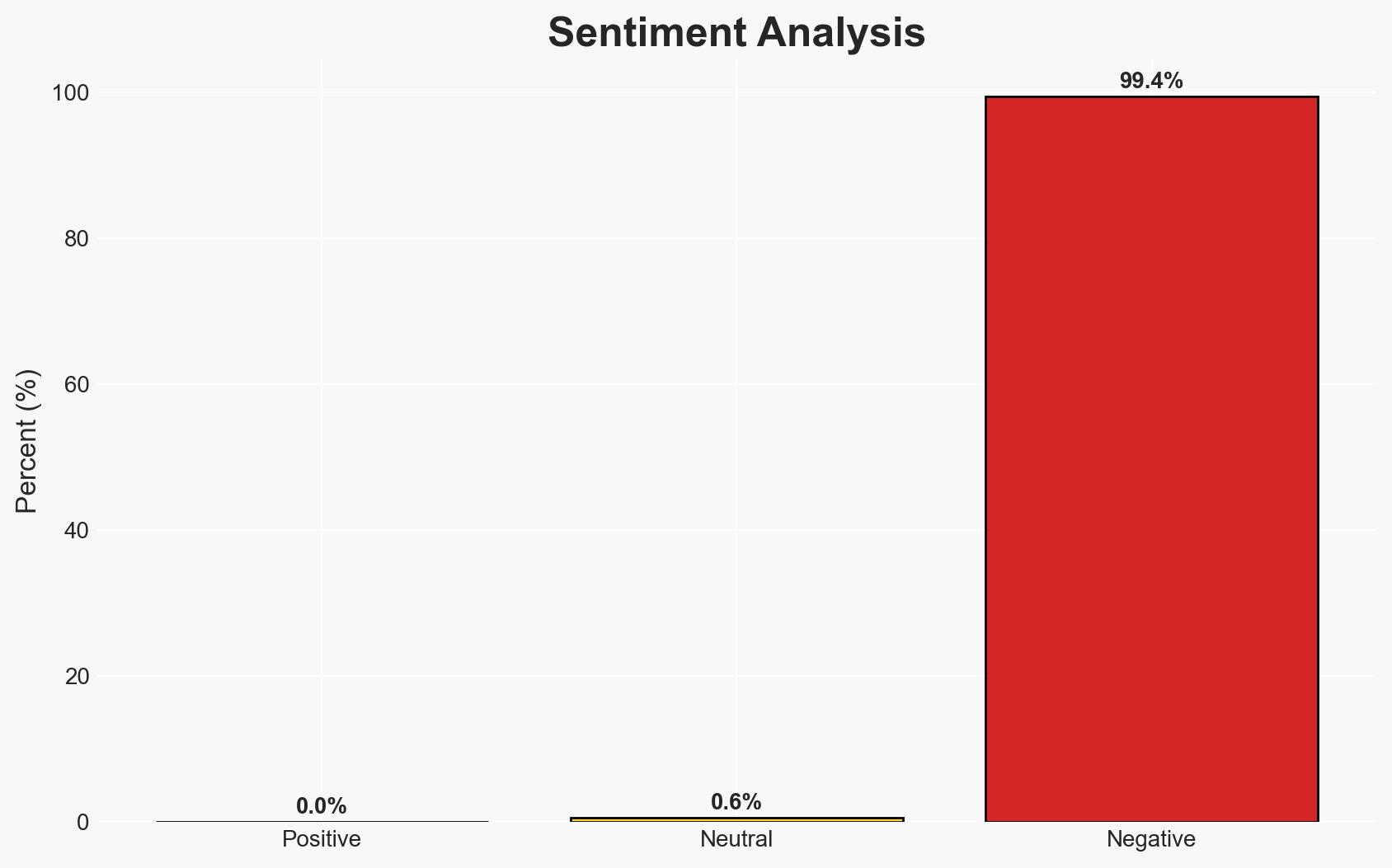
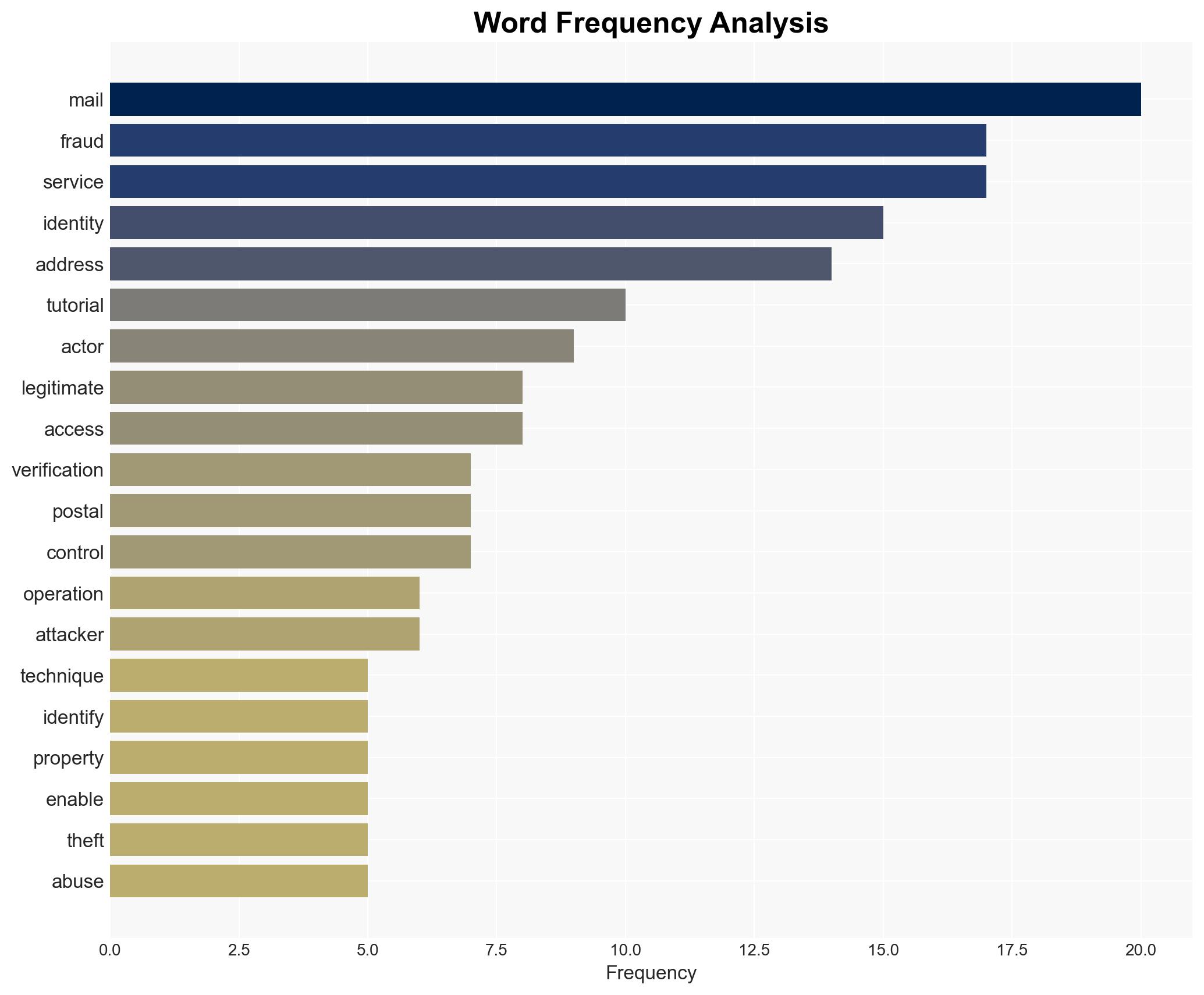
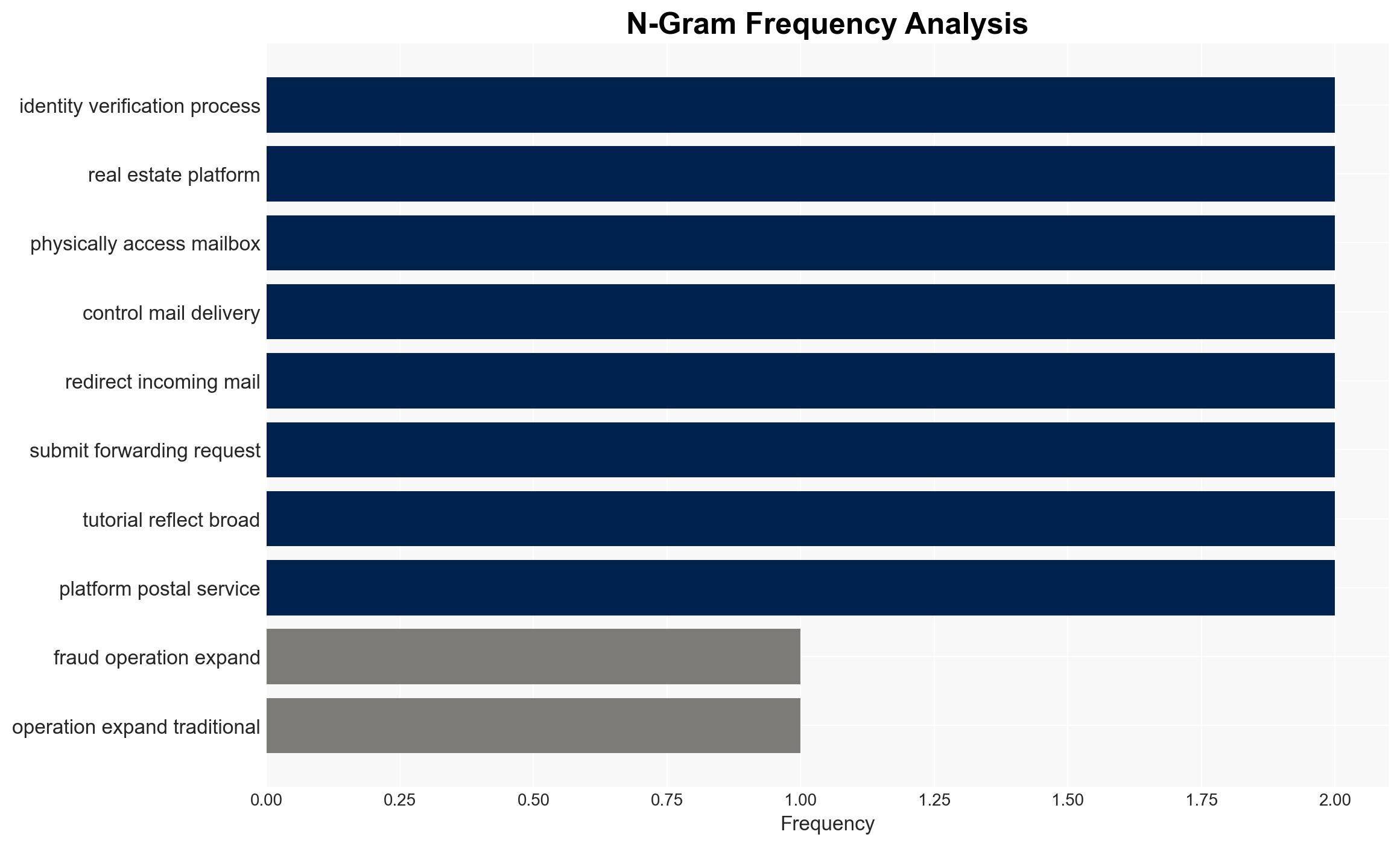
Adversaries are leveraging vacant residential properties to intercept mail, facilitating identity theft and financial fraud through a combination of open-source intelligence and legitimate postal services. This hybrid method is low-cost, scalable, and difficult to detect, posing a significant threat to individuals and financial institutions. Overall, there is moderate confidence in the assessment due to the reliance on open-source data and the potential for rapid adaptation by threat actors.
2. Competing Hypotheses
- Hypothesis A: Threat actors primarily exploit vacant homes to intercept mail as a method of identity theft and financial fraud. This is supported by evidence of detailed tutorials and the use of legitimate services to monitor mail. However, uncertainty remains regarding the scale and geographic spread of these operations.
- Hypothesis B: The exploitation of vacant homes is a secondary tactic, with primary efforts focused on traditional cybercrime methods. This hypothesis is less supported due to the specific guidance and tools shared for mail interception, indicating a dedicated effort in this area.
- Assessment: Hypothesis A is currently better supported due to the detailed operational guidance and the integration of legitimate services into the fraud workflow. Indicators such as increased reports of mail fraud or identity theft linked to vacant properties could further support this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Threat actors have consistent access to updated real estate listings; postal services remain vulnerable to unauthorized registration; vacant properties are not regularly monitored by owners or authorities.
- Information Gaps: The exact number of properties exploited and the geographical distribution of these operations are unknown.
- Bias & Deception Risks: Potential bias in source reporting from fraud-focused forums; deception risk from adversaries intentionally spreading misinformation to obscure true methods.
4. Implications and Strategic Risks
This development could lead to increased sophistication in hybrid cybercrime tactics, blending physical and digital methods. Over time, this may challenge law enforcement and regulatory frameworks.
- Political / Geopolitical: Potential for international collaboration challenges if operations cross borders.
- Security / Counter-Terrorism: Increased burden on law enforcement to monitor and secure vacant properties.
- Cyber / Information Space: Expansion of cybercrime tactics to include physical elements, complicating detection and response.
- Economic / Social: Potential increase in financial fraud cases, impacting consumer trust and financial institution stability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of real estate listings and postal service registrations; increase public awareness campaigns about mail fraud risks.
- Medium-Term Posture (1–12 months): Develop partnerships with real estate and postal services to identify and mitigate vulnerabilities; invest in technology to detect fraudulent registrations.
- Scenario Outlook:
- Best: Improved detection and prevention measures reduce fraud incidents.
- Worst: Tactics evolve faster than mitigation efforts, leading to widespread financial damage.
- Most-Likely: Incremental improvements in detection and response, with ongoing challenges in adapting to new tactics.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, identity theft, financial fraud, cybercrime, OSINT, postal services, real estate, hybrid tactics
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us