Apple issues critical iOS 18.7.7 update to protect older devices from DarkSword web exploit threats
Published on: 2026-04-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Apple releases rare iOS 1877 security update to shield older iPhones and iPads from DarkSword hacking tool
1. BLUF (Bottom Line Up Front)
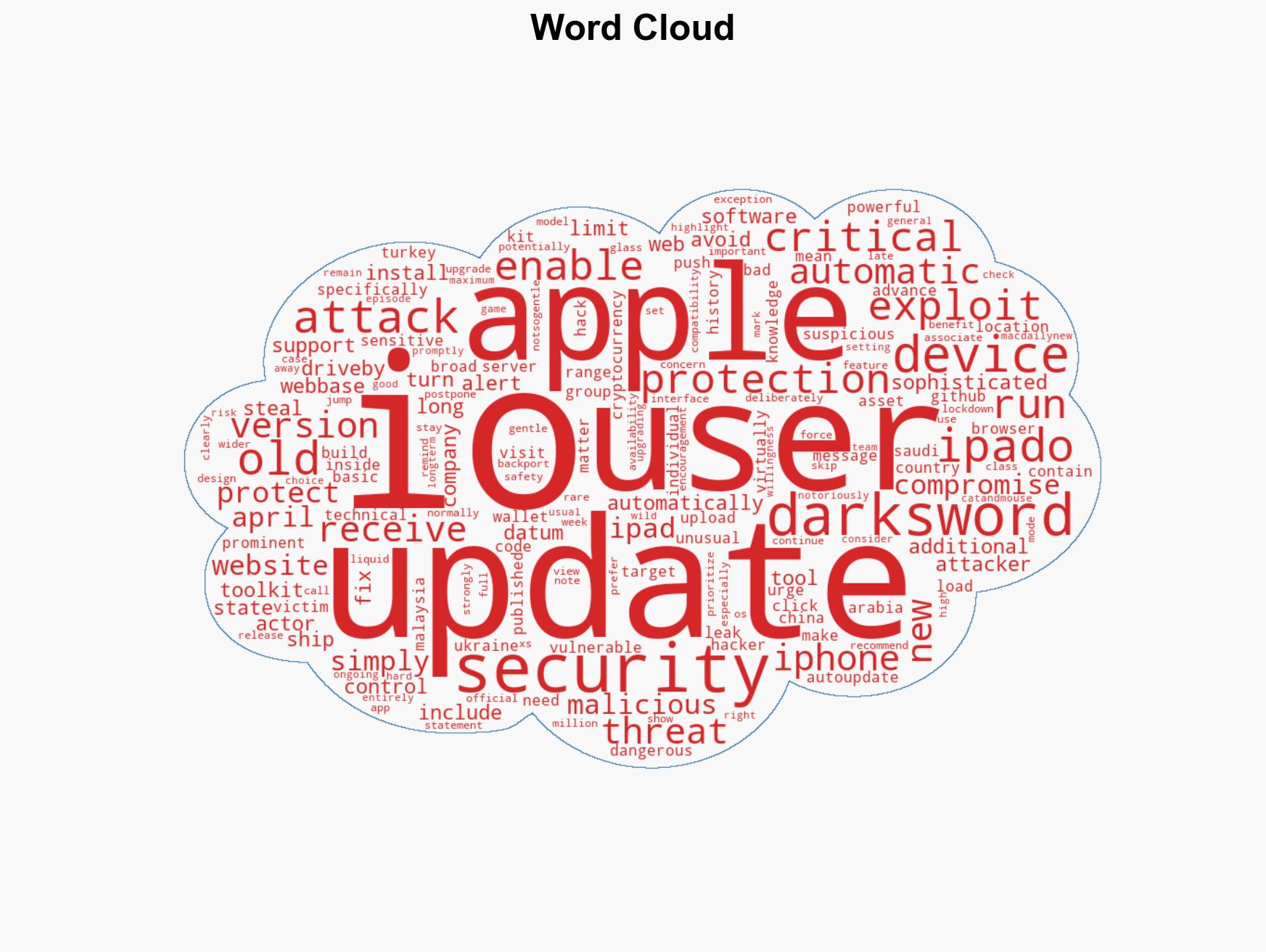
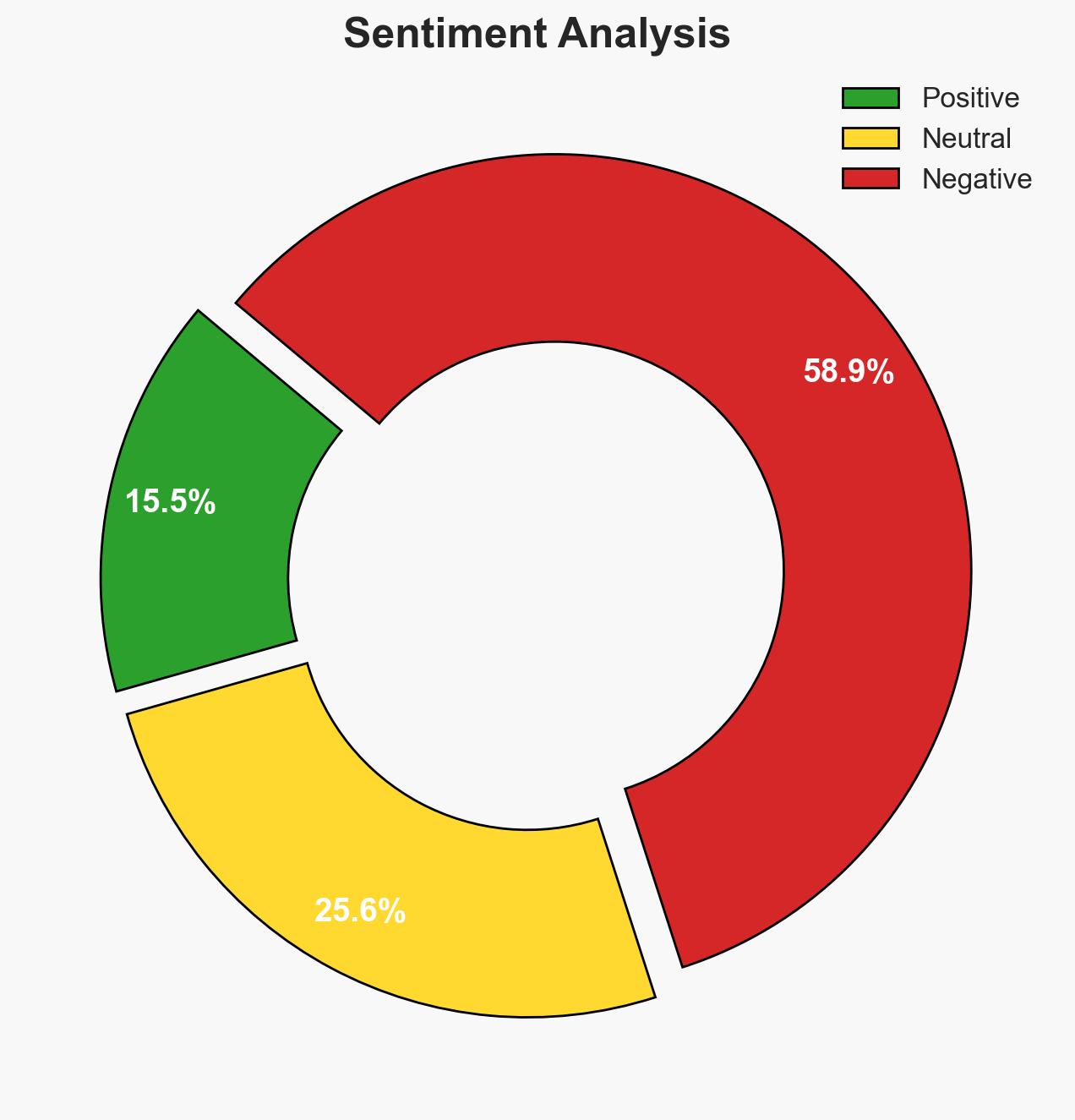
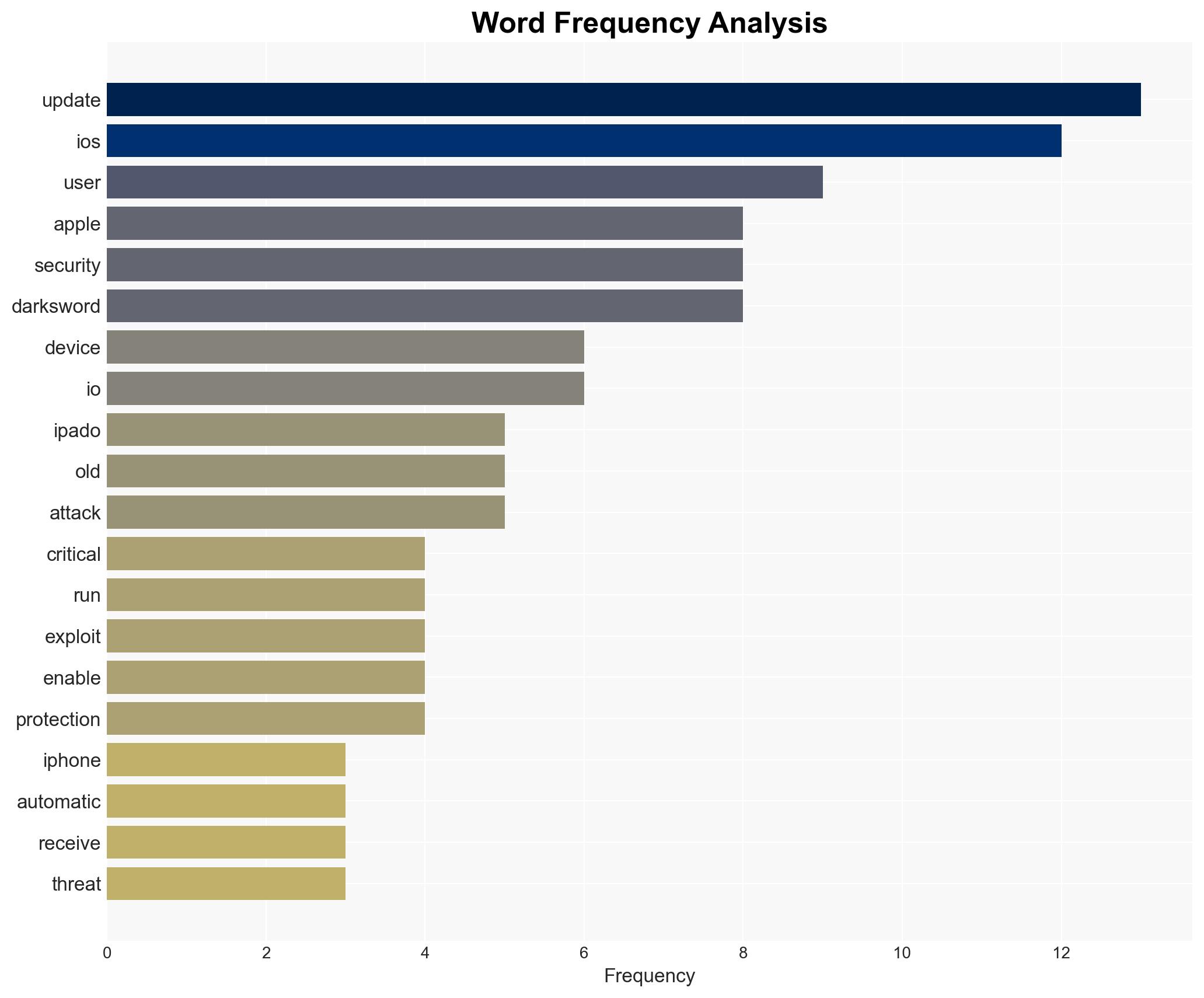
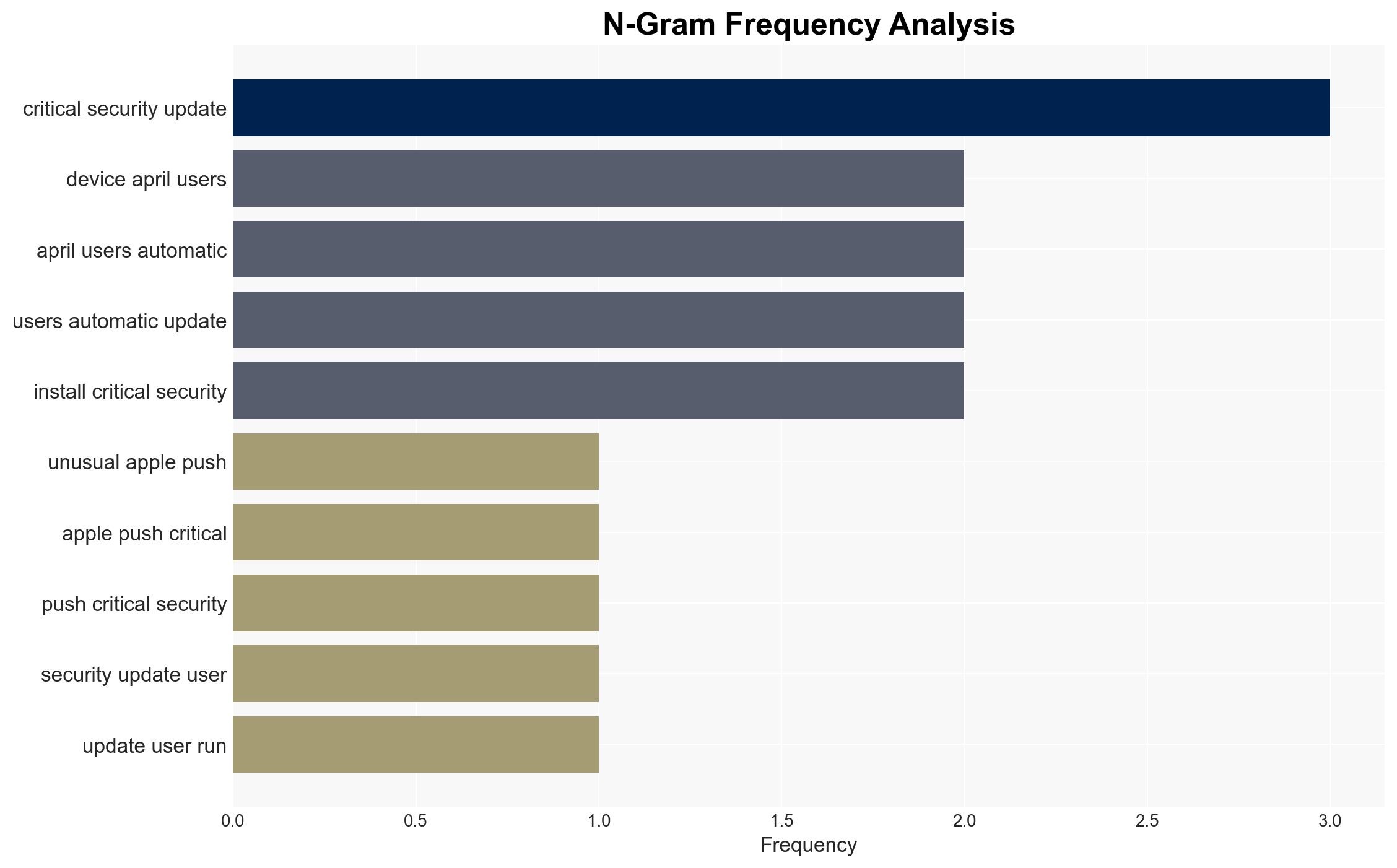
Apple’s release of iOS 18.7.7 and iPadOS 18.7.7 is a critical response to the DarkSword exploit, which poses a significant threat to users of older devices. The update aims to mitigate risks from a widely accessible hacking toolkit. This move indicates a high threat level, prompting Apple to deviate from its usual strategy of encouraging users to upgrade to the latest OS. The overall confidence in this assessment is moderate due to potential unknowns about the exploit’s full capabilities and distribution.
2. Competing Hypotheses
- Hypothesis A: Apple issued the update primarily due to the increased accessibility of the DarkSword exploit, which has been leaked online, making it a widespread threat. Supporting evidence includes the toolkit’s publication on GitHub and its use in multiple countries. A key uncertainty is the extent of the exploit’s current deployment.
- Hypothesis B: The update is a strategic move to protect Apple’s brand reputation and user trust, given the potential backlash from a significant security breach. While this is plausible, it is less supported by direct evidence compared to the immediate threat posed by the exploit’s availability.
- Assessment: Hypothesis A is currently better supported due to the direct threat from the exploit’s public availability and its use in targeted attacks. Indicators that could shift this judgment include new information on the exploit’s impact on Apple’s market perception or user trust metrics.
3. Key Assumptions and Red Flags
- Assumptions: Apple has accurately assessed the threat level of DarkSword; the exploit’s capabilities are as reported; the update effectively mitigates the exploit.
- Information Gaps: The full scope of devices affected by DarkSword and the extent of its deployment remain unclear.
- Bias & Deception Risks: Potential bias in reporting from Apple to minimize perceived vulnerability; risk of underestimating the exploit’s sophistication or reach.
4. Implications and Strategic Risks
The release of this update could have significant implications across multiple domains, influencing both short-term and long-term dynamics.
- Political / Geopolitical: Increased tensions in regions where the exploit has been used, potentially leading to diplomatic strains or cyber policy shifts.
- Security / Counter-Terrorism: Heightened alertness among law enforcement and intelligence agencies to monitor for exploit usage in critical infrastructure or sensitive sectors.
- Cyber / Information Space: Potential surge in similar exploit kits being developed or distributed, increasing the overall cyber threat landscape.
- Economic / Social: Possible economic impact on Apple if users lose trust in device security; social implications if personal data is widely compromised.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage users to update devices promptly; monitor for signs of exploit usage in critical sectors; engage with cybersecurity firms to assess threat levels.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies for shared threat intelligence; enhance public awareness campaigns on cybersecurity hygiene.
- Scenario Outlook:
- Best: Successful mitigation of the exploit with minimal data breaches.
- Worst: Widespread exploitation leading to significant data theft and loss of trust in Apple products.
- Most-Likely: Limited exploitation with gradual user compliance in updating devices, stabilizing the threat landscape.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, software updates, exploit mitigation, cyber threats, data protection, mobile security, technology policy
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us