CISA warns of RESURGE malware exploiting Ivanti flaw – Securityaffairs.com
Published on: 2025-03-30
Intelligence Report: CISA warns of RESURGE malware exploiting Ivanti flaw – Securityaffairs.com
1. BLUF (Bottom Line Up Front)
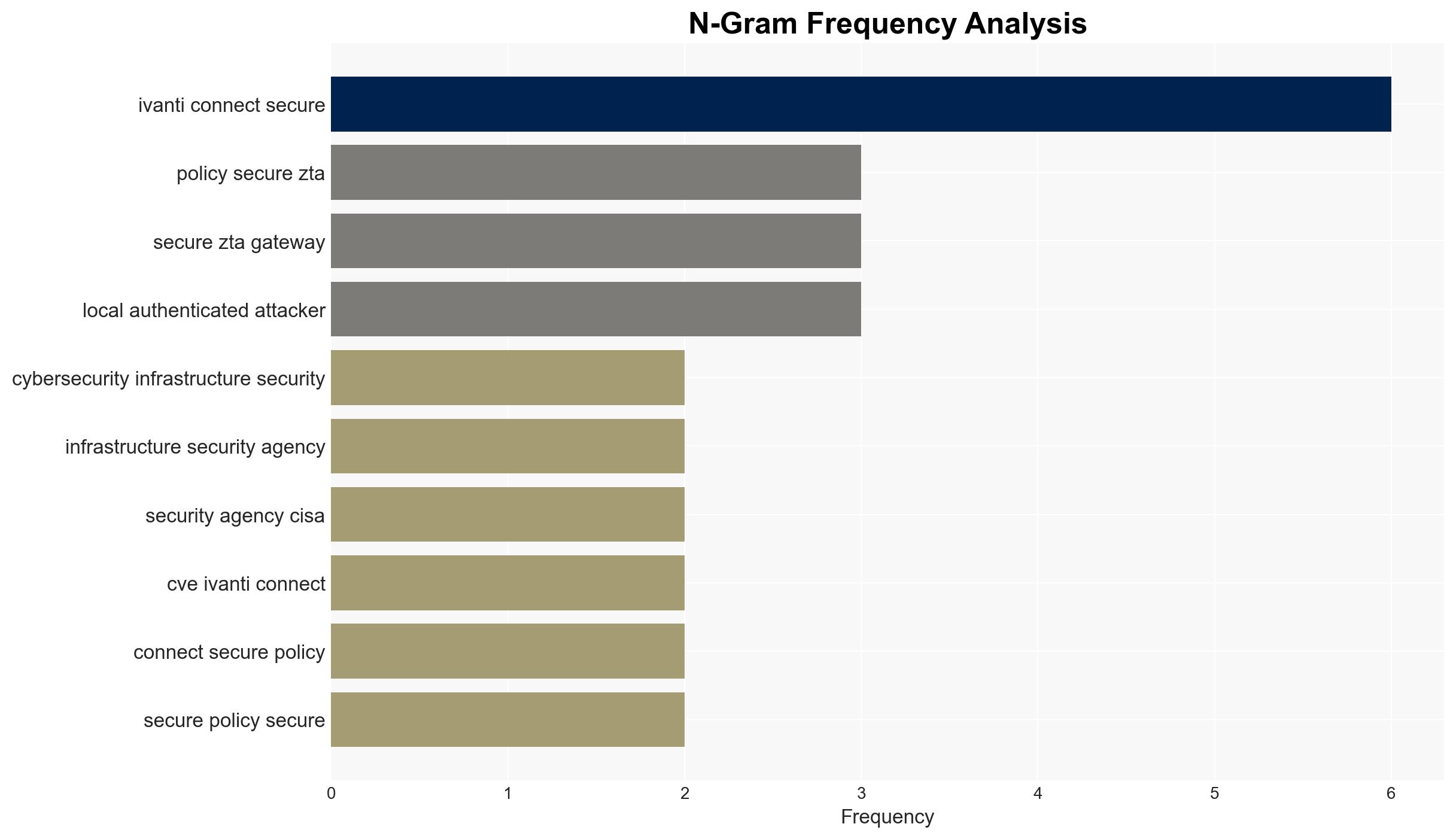
The Cybersecurity and Infrastructure Security Agency (CISA) has issued a warning regarding the RESURGE malware, which exploits a vulnerability in Ivanti’s Connect Secure appliances. The malware allows unauthorized access and privilege escalation, posing significant risks to affected systems. Immediate action is required to mitigate potential breaches and secure vulnerable systems.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
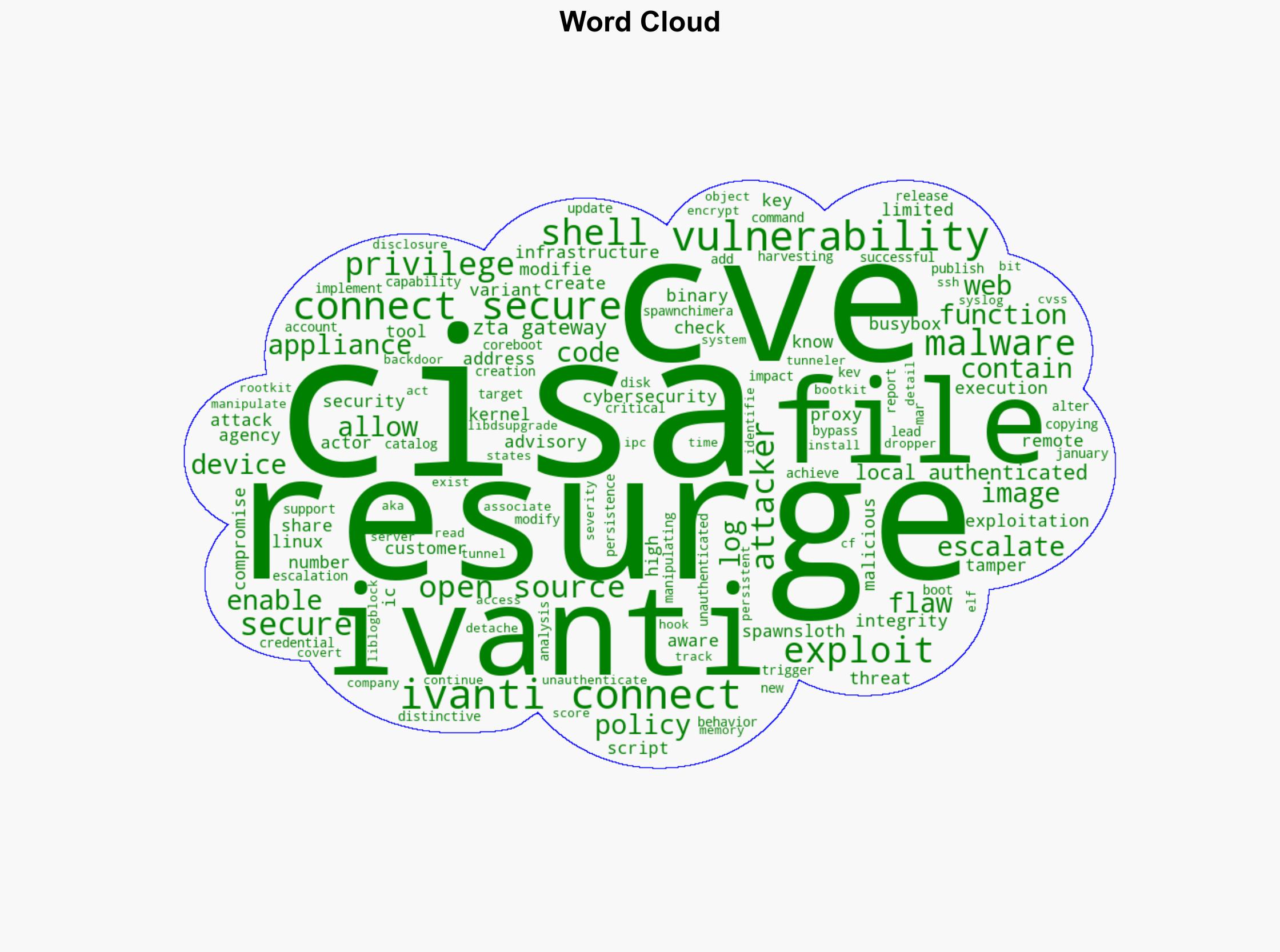
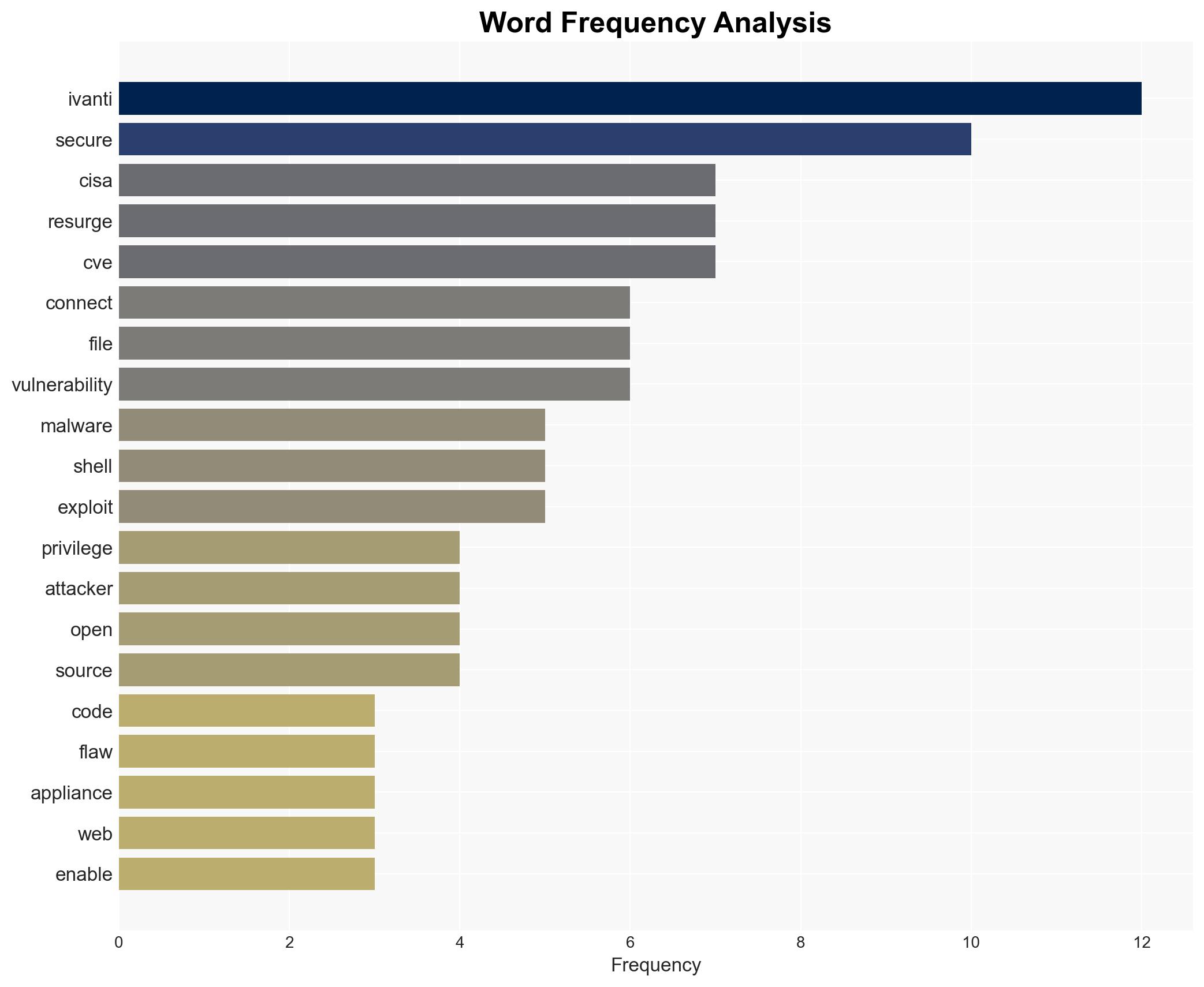
The RESURGE malware targets a specific vulnerability identified as CVE in Ivanti Connect Secure appliances. This malware is capable of deploying additional malicious code, altering system behaviors, and creating persistent backdoors. It utilizes a web shell to bypass integrity checks and manipulate system files, enabling credential harvesting and unauthorized account creation. The malware’s ability to exploit this vulnerability poses a high risk of remote code execution and privilege escalation.
3. Implications and Strategic Risks
The exploitation of the Ivanti vulnerability by RESURGE malware presents significant risks to national security and economic interests. The potential for unauthorized access and control over critical systems could lead to data breaches, operational disruptions, and financial losses. The threat extends to regional stability, as compromised systems may be used for further cyber-attacks or espionage activities.
4. Recommendations and Outlook
Recommendations:
- Organizations using Ivanti Connect Secure appliances should immediately apply available security updates to mitigate the vulnerability.
- Implement enhanced monitoring and logging to detect unusual activities and potential breaches.
- Consider adopting a Zero Trust Architecture to minimize the impact of unauthorized access.
Outlook:
In the best-case scenario, swift action and patch deployment will prevent further exploitation of the vulnerability. In the worst-case scenario, failure to address the issue could lead to widespread breaches and significant operational impacts. The most likely outcome involves a combination of successful mitigations and isolated incidents of exploitation.
5. Key Individuals and Entities
The report mentions significant individuals and organizations involved in addressing the RESURGE malware threat. Key entities include CISA and Ivanti. No specific individuals are named in the report.