New Crocodilus malware steals Android users crypto wallet keys – BleepingComputer
Published on: 2025-03-30
Intelligence Report: New Crocodilus malware steals Android users crypto wallet keys – BleepingComputer
1. BLUF (Bottom Line Up Front)
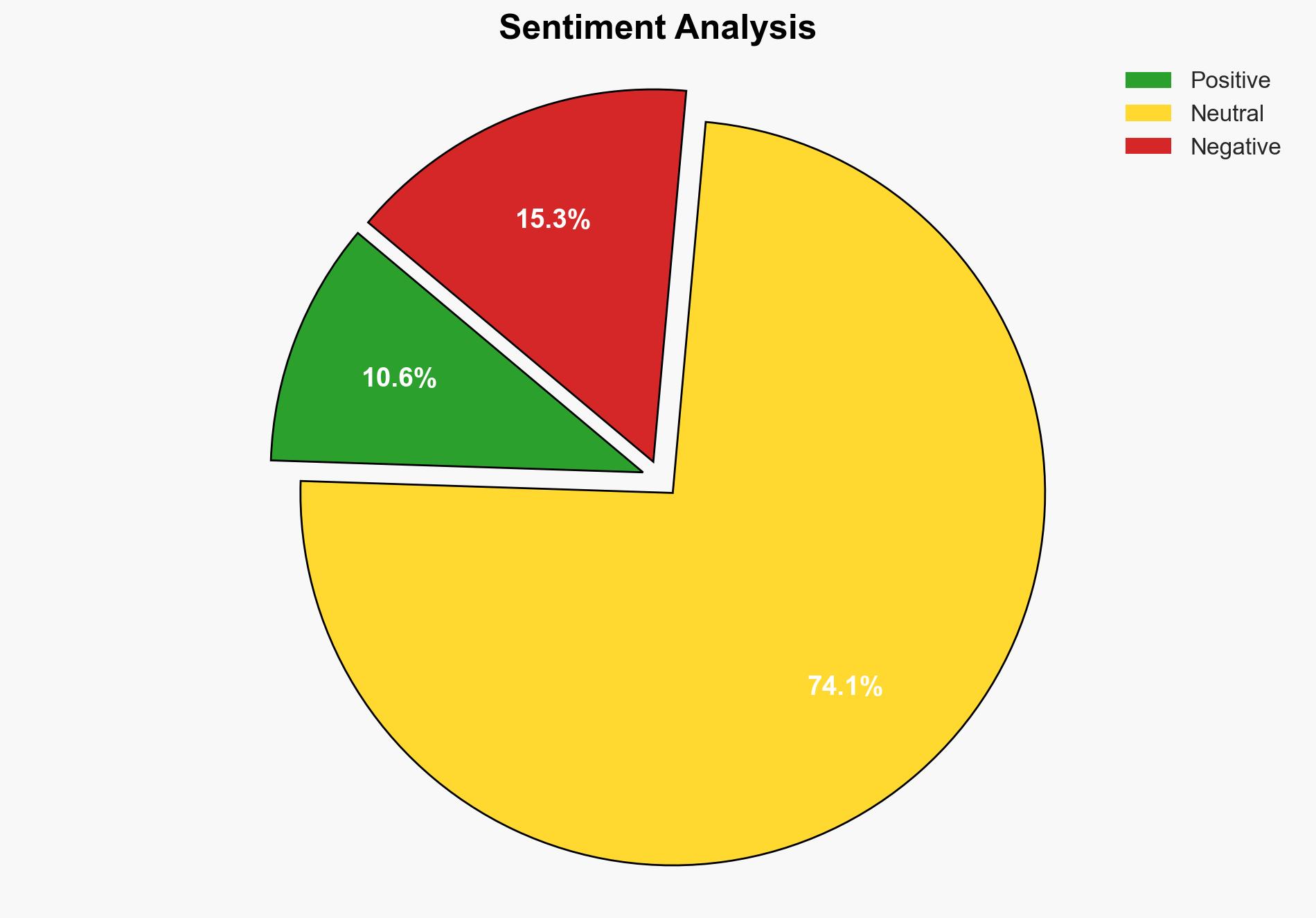
The Crocodilus malware poses a significant threat to Android users by targeting cryptocurrency wallets and banking applications. It employs sophisticated techniques to bypass security measures and harvest sensitive data, including seed phrases and authentication codes. Immediate action is required to mitigate risks and protect user assets.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
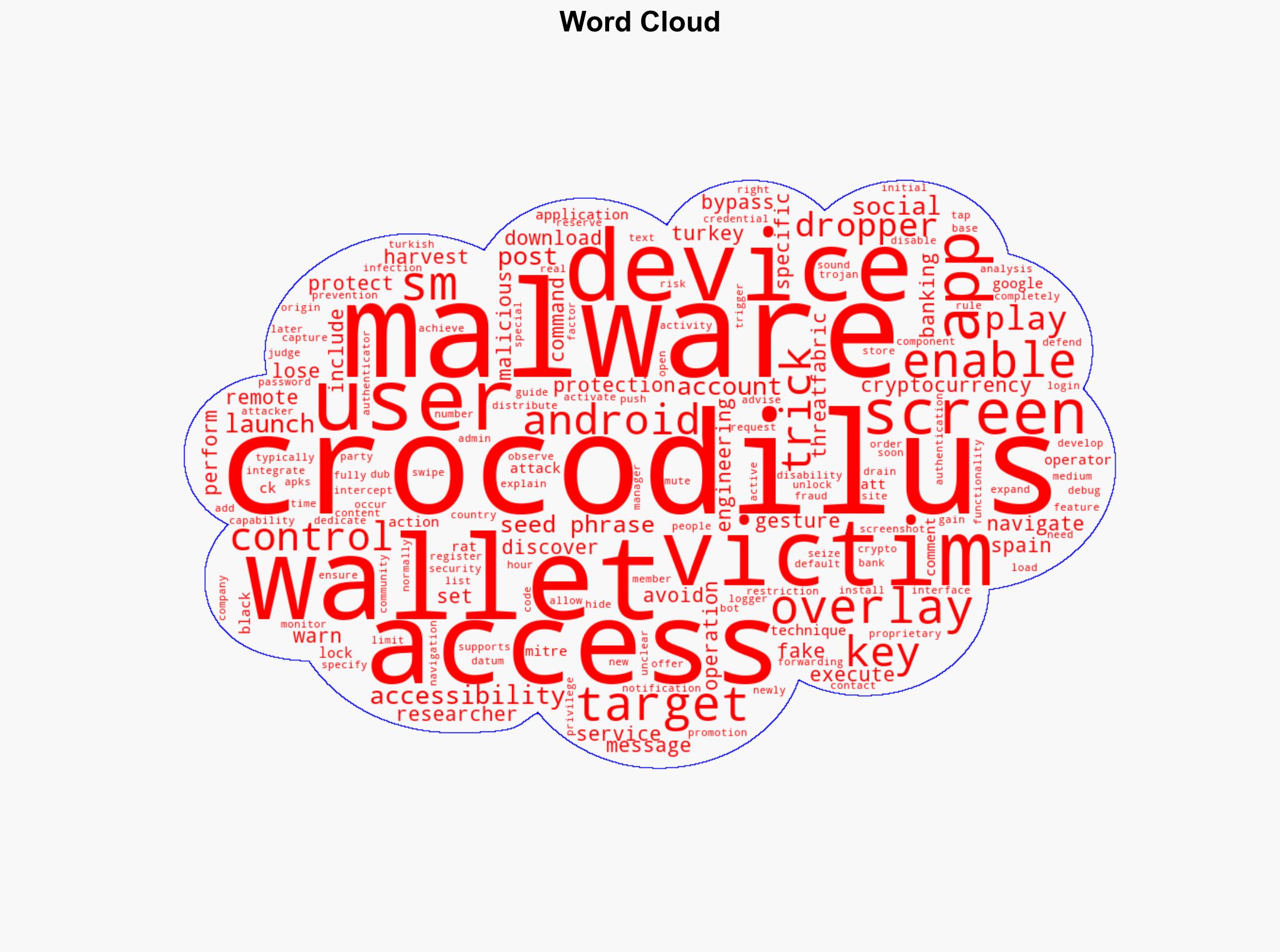
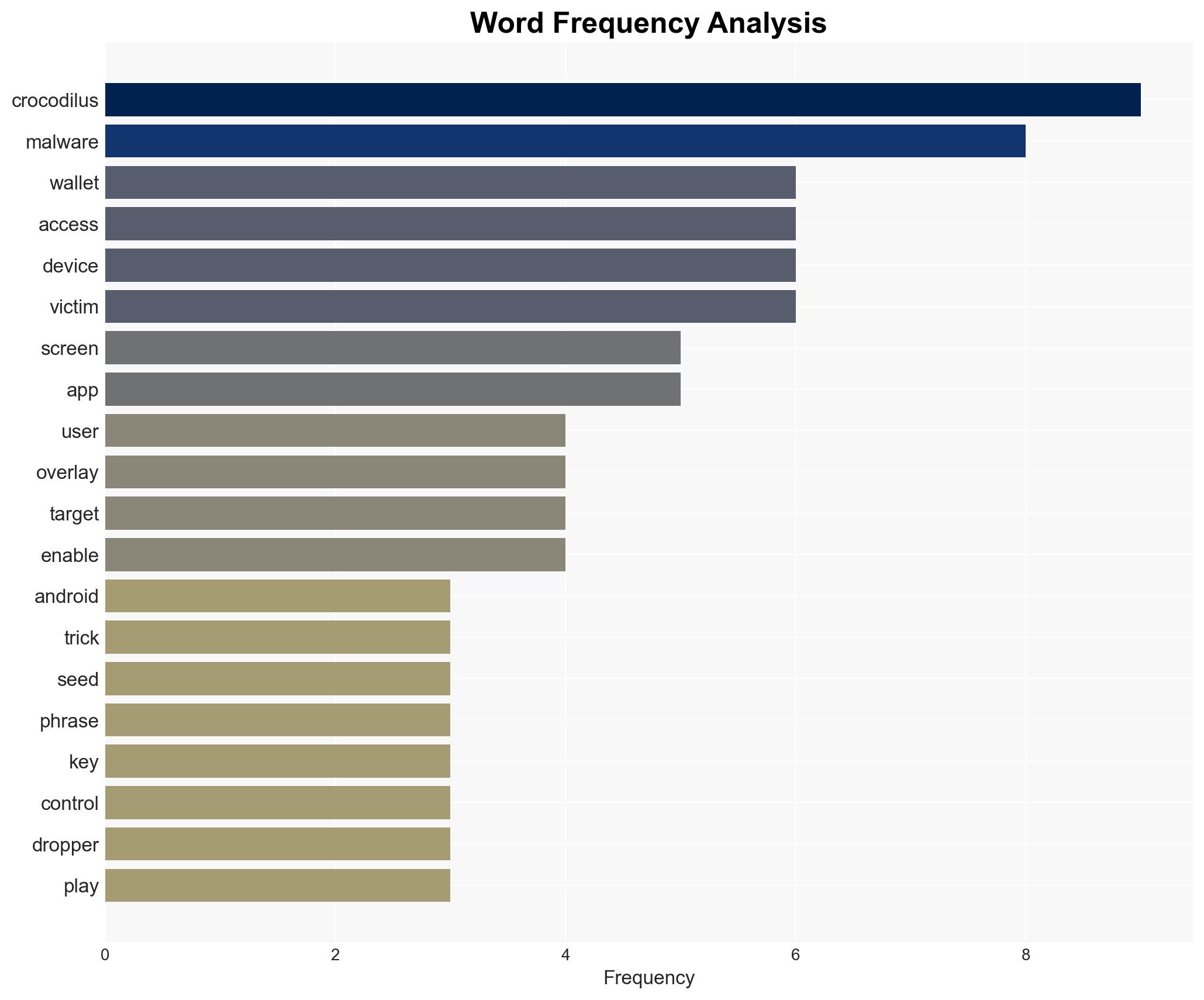
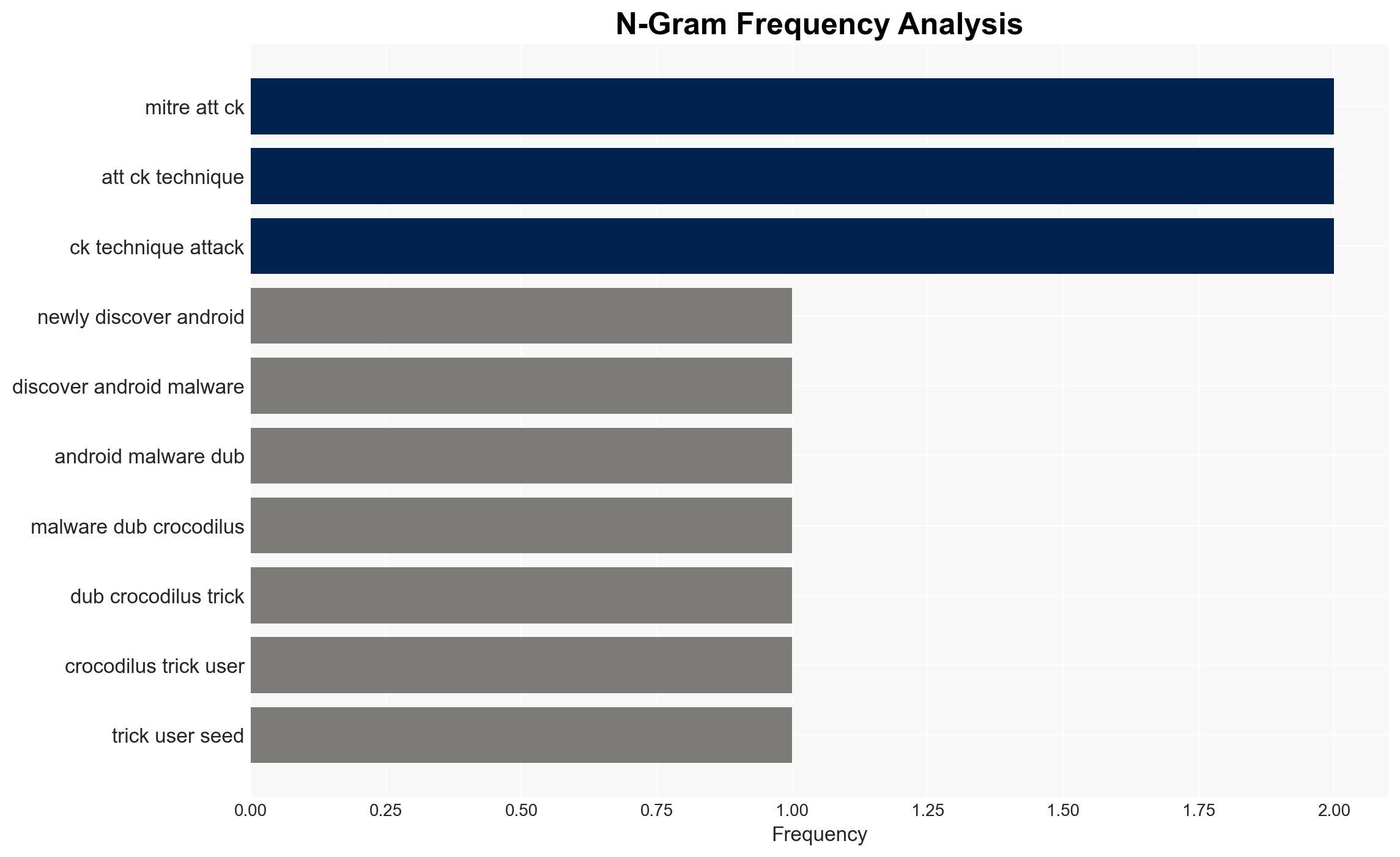
Crocodilus is a newly identified Android malware with advanced capabilities to control devices and harvest data. It is distributed via a proprietary dropper that bypasses Android’s security protections, including Play Protect and accessibility service restrictions. The malware employs social engineering tactics to gain access to users’ crypto wallet seed phrases through screen overlays. Once access is obtained, it can drain wallets completely. The malware has primarily targeted users in Turkey and Spain, indicating a potential Turkish origin. Initial infections occur through malicious sites, fake promotions, and third-party app stores.
3. Implications and Strategic Risks
The Crocodilus malware presents several strategic risks:
- Economic Impact: Potential financial losses for individuals and institutions due to compromised cryptocurrency wallets.
- National Security: Increased vulnerability of financial systems and potential exploitation by malicious actors.
- Regional Stability: Targeted attacks in Turkey and Spain may lead to heightened cybersecurity concerns and regulatory scrutiny.
4. Recommendations and Outlook
Recommendations:
- Enhance public awareness campaigns to educate users on the risks of downloading apps from unverified sources.
- Strengthen Android security protocols to detect and prevent unauthorized access to accessibility services.
- Encourage financial institutions to implement additional security measures for cryptocurrency transactions.
Outlook:
Best-case scenario: Rapid implementation of security measures and user education reduces the spread and impact of Crocodilus.
Worst-case scenario: The malware expands its target list, affecting more regions and causing widespread financial losses.
Most likely outcome: Continued targeting of specific regions with gradual expansion as security measures are incrementally improved.
5. Key Individuals and Entities
The report references ThreatFabric as a key entity involved in the research and analysis of the Crocodilus malware. No specific individuals are mentioned.