Politically motivated DDoS attacks target critical infrastructure – BetaNews
Published on: 2025-04-02
Intelligence Report: Politically motivated DDoS attacks target critical infrastructure – BetaNews
1. BLUF (Bottom Line Up Front)
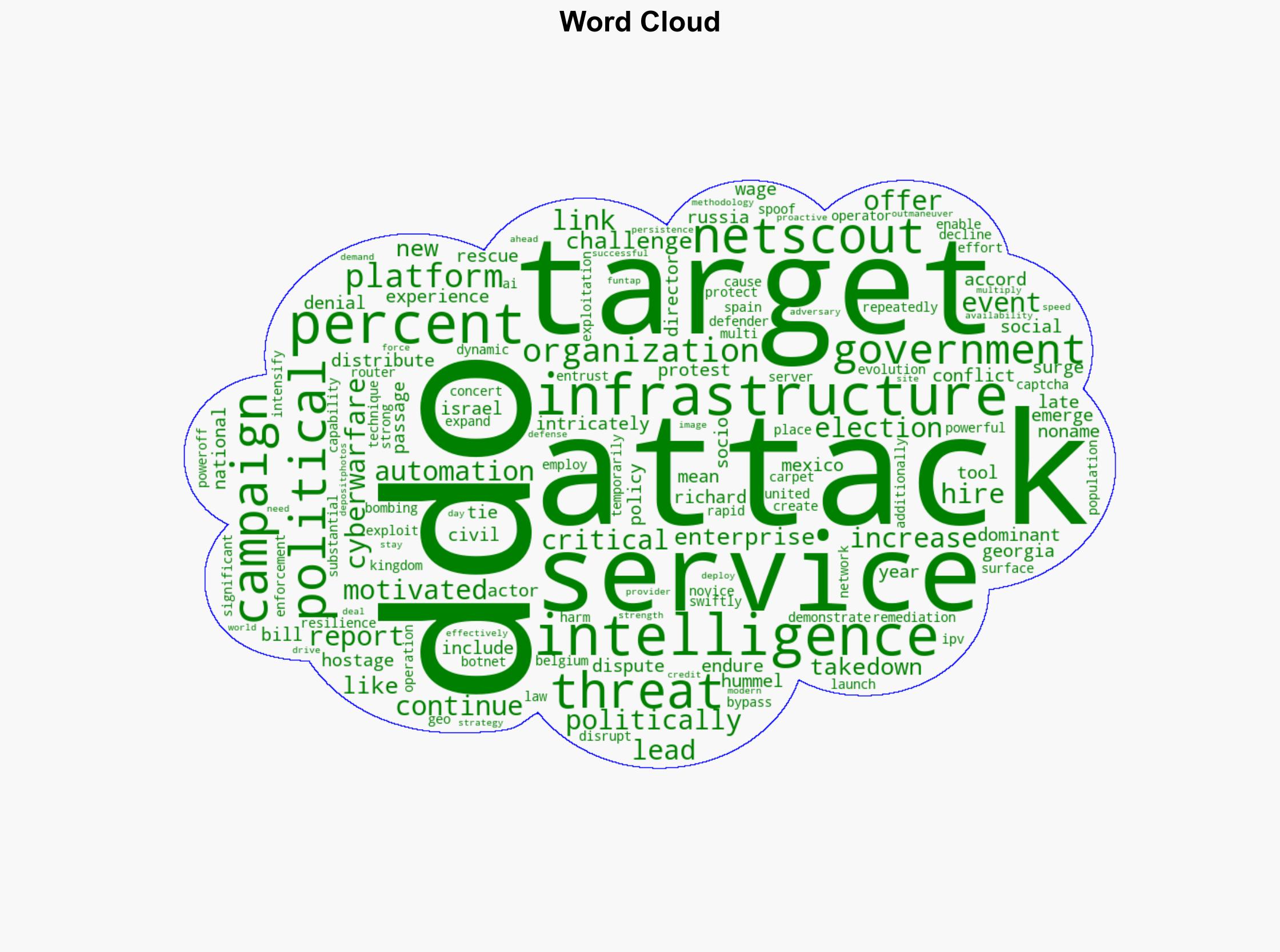
Politically motivated Distributed Denial of Service (DDoS) attacks are increasingly targeting critical infrastructure, leveraging socio-political events such as elections and policy disputes. Recent data indicates a significant rise in DDoS activities linked to geopolitical tensions, with notable increases in Israel, Georgia, and Mexico. The evolution of DDoS tactics, including AI-driven CAPTCHA bypass and geo-spoofing, presents substantial challenges to defenders. Immediate strategic measures are required to enhance resilience and protect vital services.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
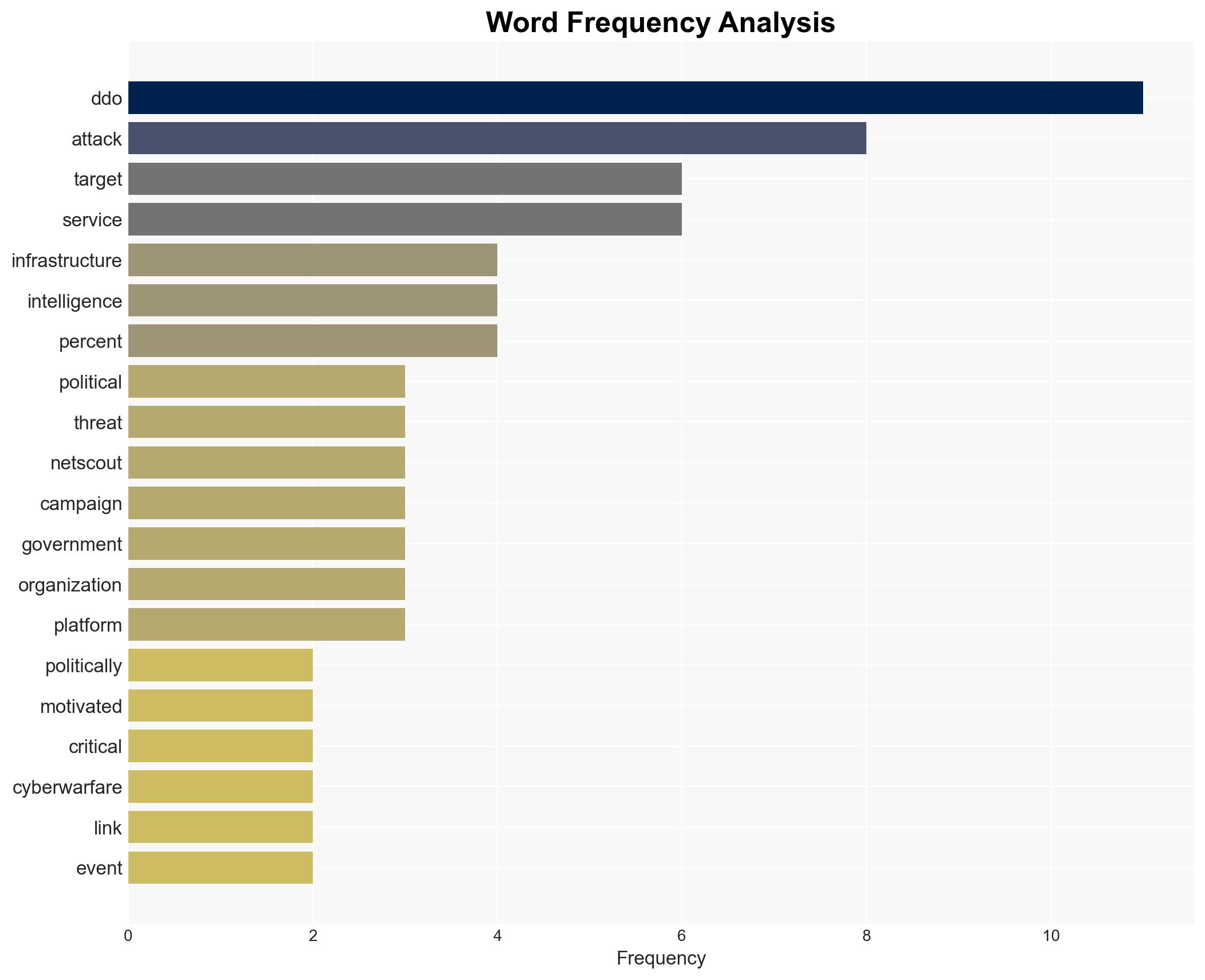
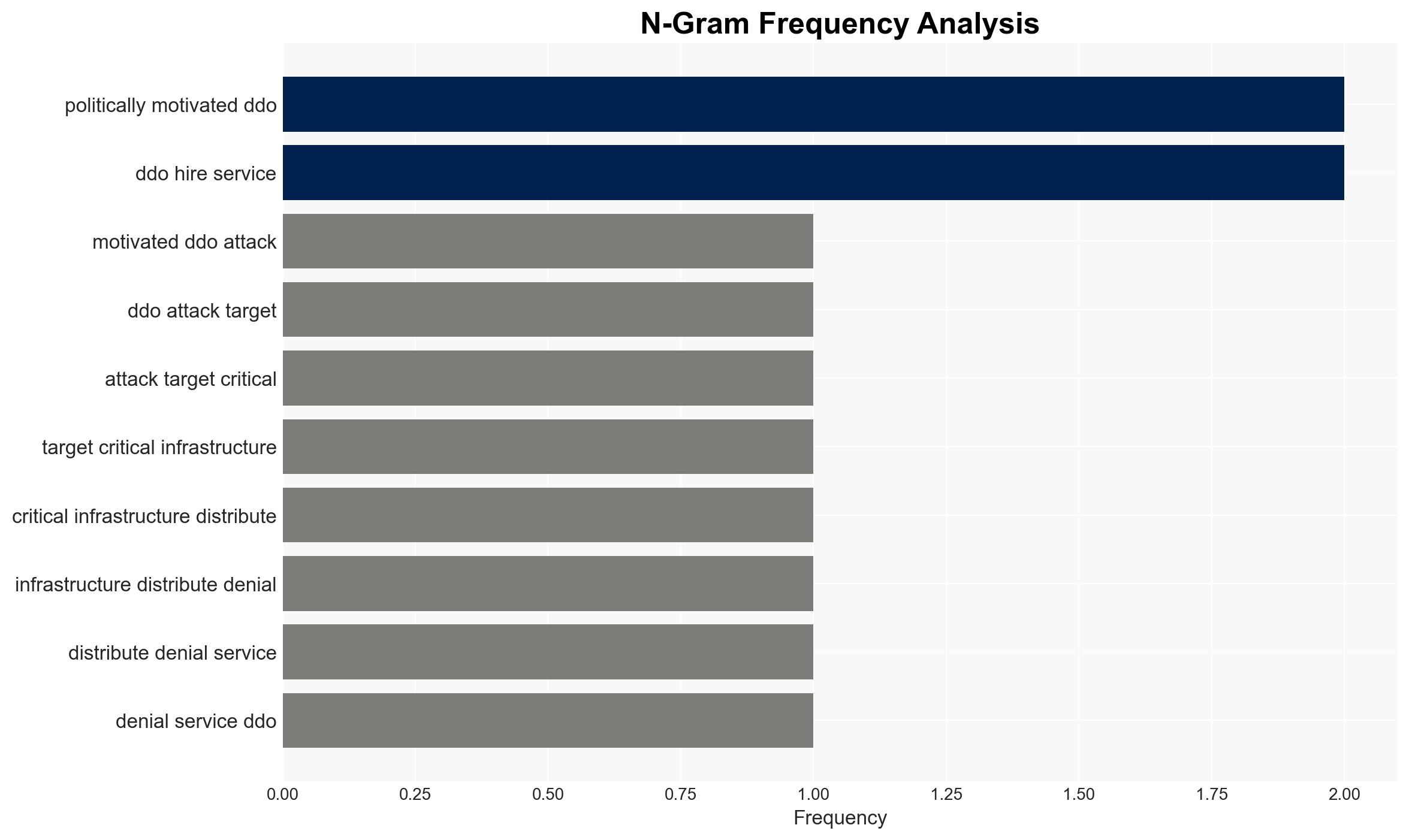
DDoS attacks have become a dominant tool in cyber warfare, intricately tied to socio-political events. The report highlights a 200% surge in attacks in Israel linked to political conflicts, a 300% increase in Georgia following legislative changes, and a 400% rise in Mexico during national elections. These attacks are often orchestrated by actors like Noname, who target government infrastructure in countries such as the United Kingdom, Belgium, and Spain. The use of DDoS-for-hire services and advanced automation techniques has expanded the attack surface, enabling even novice operators to execute significant campaigns.
3. Implications and Strategic Risks
The increasing frequency and sophistication of DDoS attacks pose significant risks to national security, regional stability, and economic interests. The resilience of botnets, despite law enforcement efforts like Operation PowerOff, underscores the persistent threat to critical infrastructure. The rapid adaptation of attack platforms challenges defenders, necessitating continuous innovation in defense strategies. Failure to address these threats could lead to widespread service disruptions and undermine public trust in governmental and enterprise systems.
4. Recommendations and Outlook
Recommendations:
- Enhance intelligence-driven methodologies to anticipate and mitigate DDoS threats proactively.
- Invest in advanced technological solutions, including AI and machine learning, to detect and respond to attacks swiftly.
- Strengthen international collaboration and regulatory frameworks to disrupt DDoS-for-hire services and prosecute offenders.
Outlook:
In the best-case scenario, enhanced cooperation and technological advancements could significantly reduce the impact of DDoS attacks. In the worst-case scenario, failure to adapt could result in severe disruptions to critical services. The most likely outcome involves a continued arms race between attackers and defenders, necessitating sustained investment in cybersecurity measures.
5. Key Individuals and Entities
The report mentions Richard Hummel and Noname as significant individuals involved in the analysis of DDoS threats. The organization Netscout is identified as a key entity providing threat intelligence.