A key WordPress feature has been hijacked to show malicious code spam images – TechRadar
Published on: 2025-04-01
Intelligence Report: A Key WordPress Feature Hijacked to Show Malicious Code Spam Images – TechRadar
1. BLUF (Bottom Line Up Front)
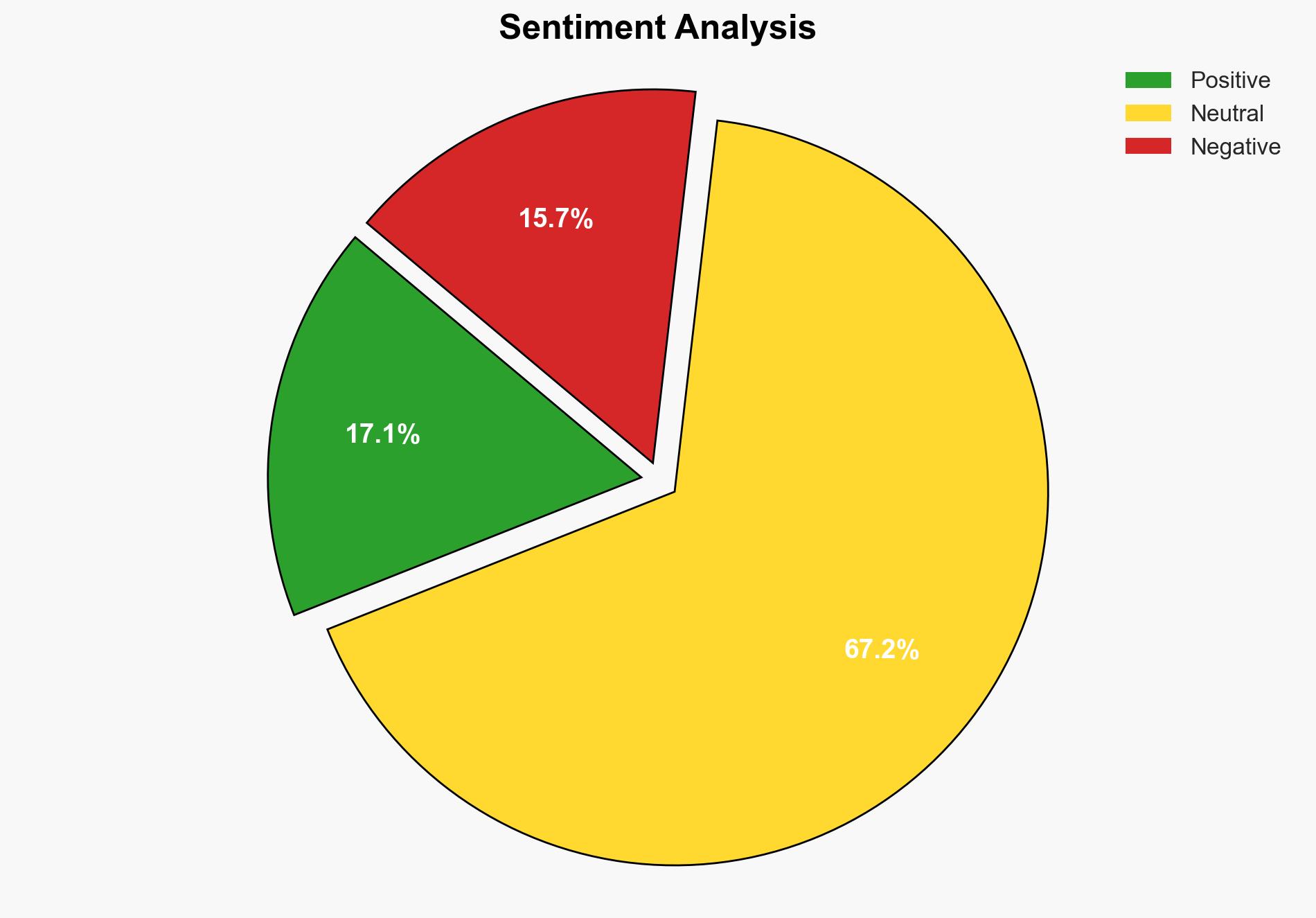
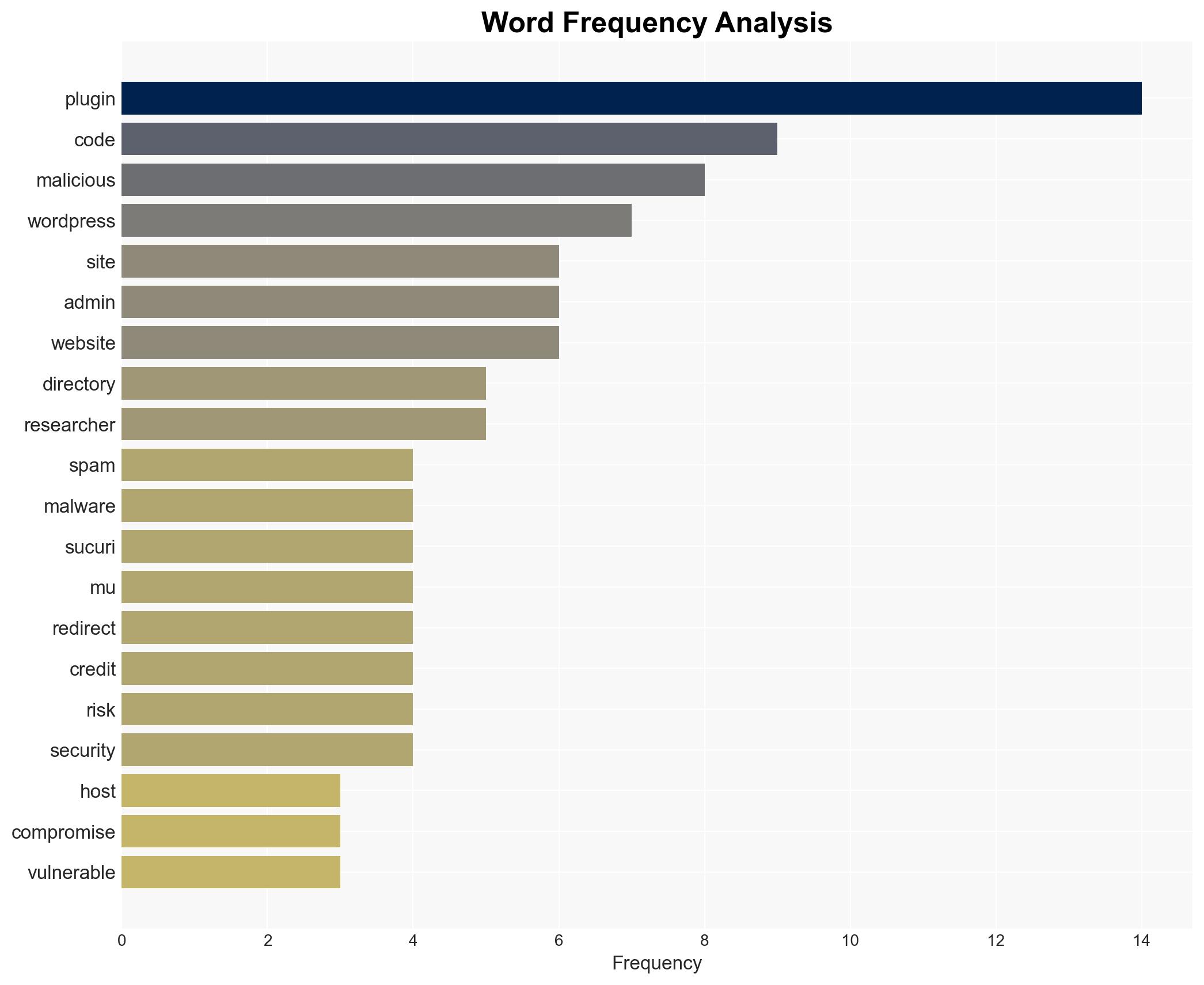
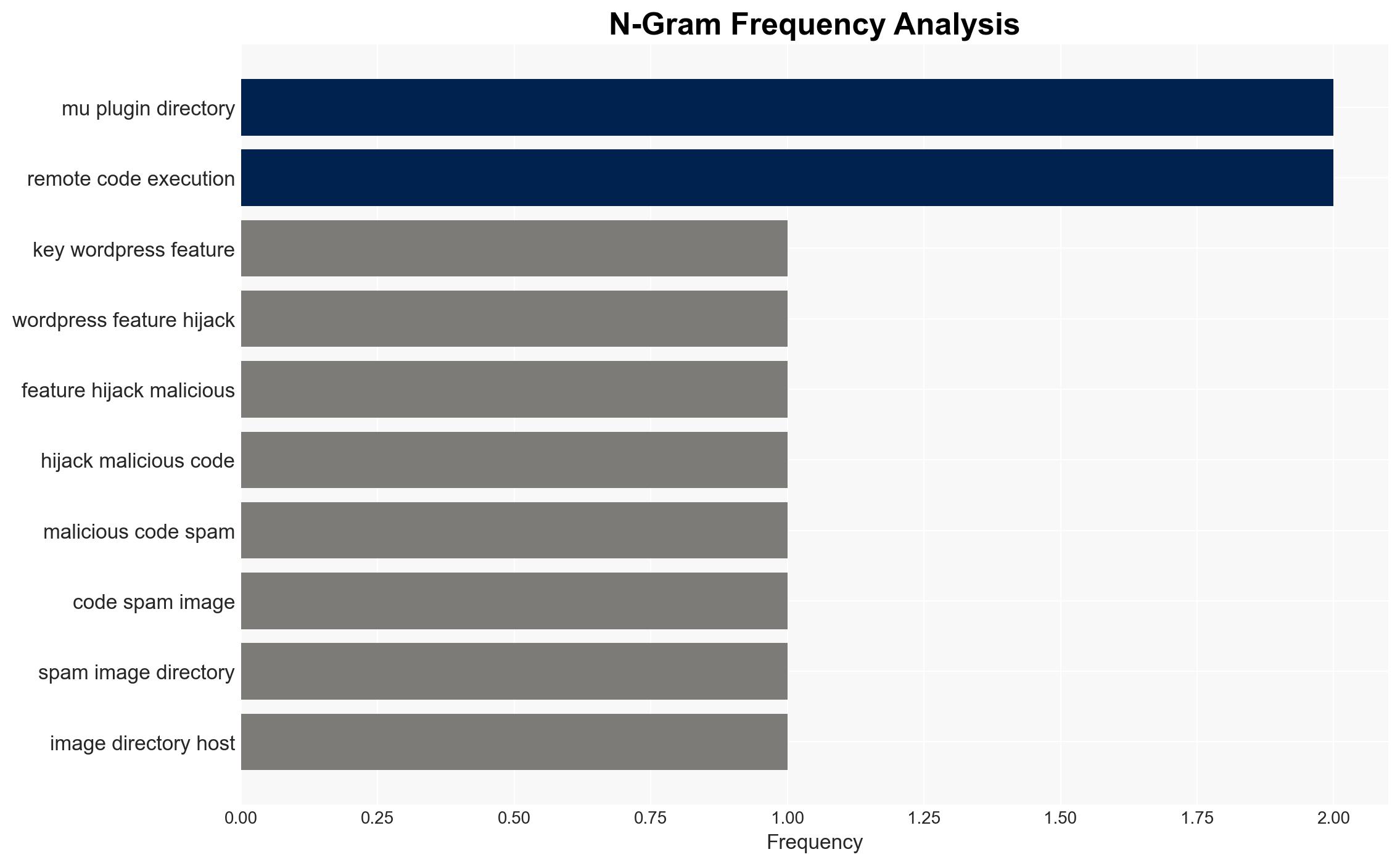
Recent findings indicate that a critical WordPress feature has been exploited to distribute malicious code and spam images. This vulnerability, identified by researchers, poses significant risks to website security, allowing threat actors to execute arbitrary code and redirect users to malicious sites. Immediate action is required to secure affected systems and prevent further exploitation.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
Researchers have discovered that malicious actors are exploiting the WordPress MU-Plugin directory to hide harmful code. This directory, typically used for essential site functionalities, is being abused to execute remote code and inject spam. The threat actors can remain persistent on compromised websites, making detection challenging. The exploitation is facilitated by vulnerable plugins, weak administrative credentials, and insecure hosting environments.
3. Implications and Strategic Risks
The exploitation of WordPress features presents several strategic risks, including:
- Increased vulnerability of websites to cyberattacks, potentially leading to data breaches and loss of sensitive information.
- Economic impacts due to compromised business websites, affecting trust and revenue.
- Potential national security risks if government or critical infrastructure websites are targeted.
The trend of exploiting popular web platforms like WordPress highlights the need for enhanced cybersecurity measures across all sectors.
4. Recommendations and Outlook
Recommendations:
- Conduct regular security audits of WordPress installations to detect and remove unauthorized plugins and malicious code.
- Implement strong password policies and enable two-factor authentication for administrative accounts.
- Regularly update WordPress plugins and themes to patch known vulnerabilities.
- Consider deploying security plugins to monitor file integrity and detect anomalies.
Outlook:
Best-case scenario: Swift implementation of security measures reduces the exploitation of WordPress vulnerabilities, leading to a decrease in cyber incidents.
Worst-case scenario: Failure to address vulnerabilities results in widespread attacks, causing significant economic and reputational damage.
Most likely outcome: Continued vigilance and incremental security improvements will mitigate risks, although isolated incidents may persist.
5. Key Individuals and Entities
The report references the following individuals and entities:
- Sead – A journalist who reported on the issue.
- Sucuri – The research team that identified the vulnerability.
These individuals and entities play a significant role in the discovery and dissemination of information regarding the WordPress vulnerability.