Abnormal AI Launches Attune 1.0 to Enhance Behavioral Detection Against AI-Powered Cyber Attacks
Published on: 2026-03-18
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
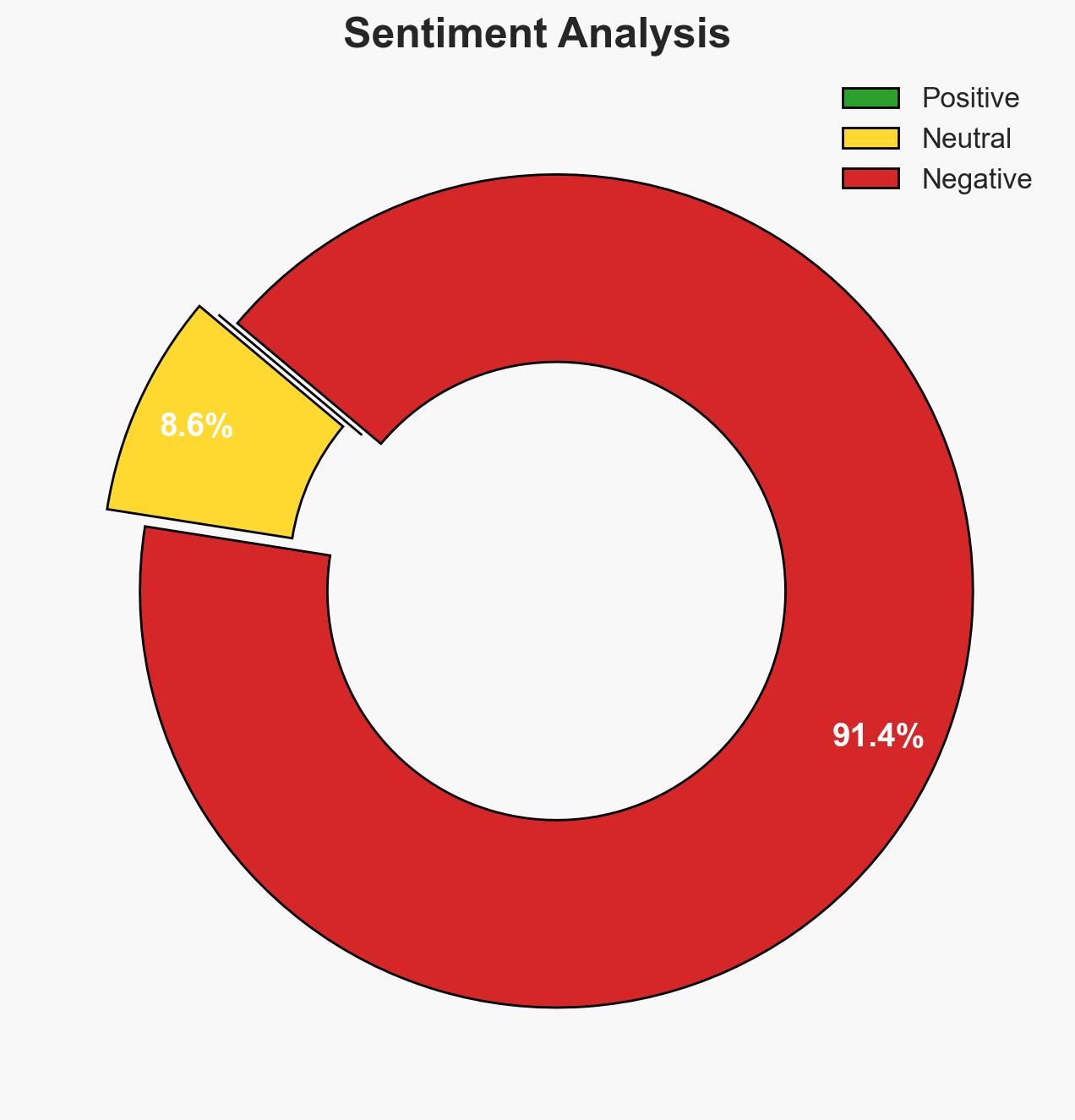
Intelligence Report: Abnormal AI Attune 10 targets AI-driven attacks with behavioral detection
1. BLUF (Bottom Line Up Front)
Abnormal AI’s launch of Attune 1.0 represents a significant advancement in cybersecurity by leveraging a behavioral foundation model to counter AI-driven attacks. This development is likely to enhance detection capabilities across various organizational communication platforms, affecting cybersecurity operations globally. Overall, there is moderate confidence in the effectiveness of Attune 1.0 due to its early success in identifying novel attack patterns.
2. Competing Hypotheses
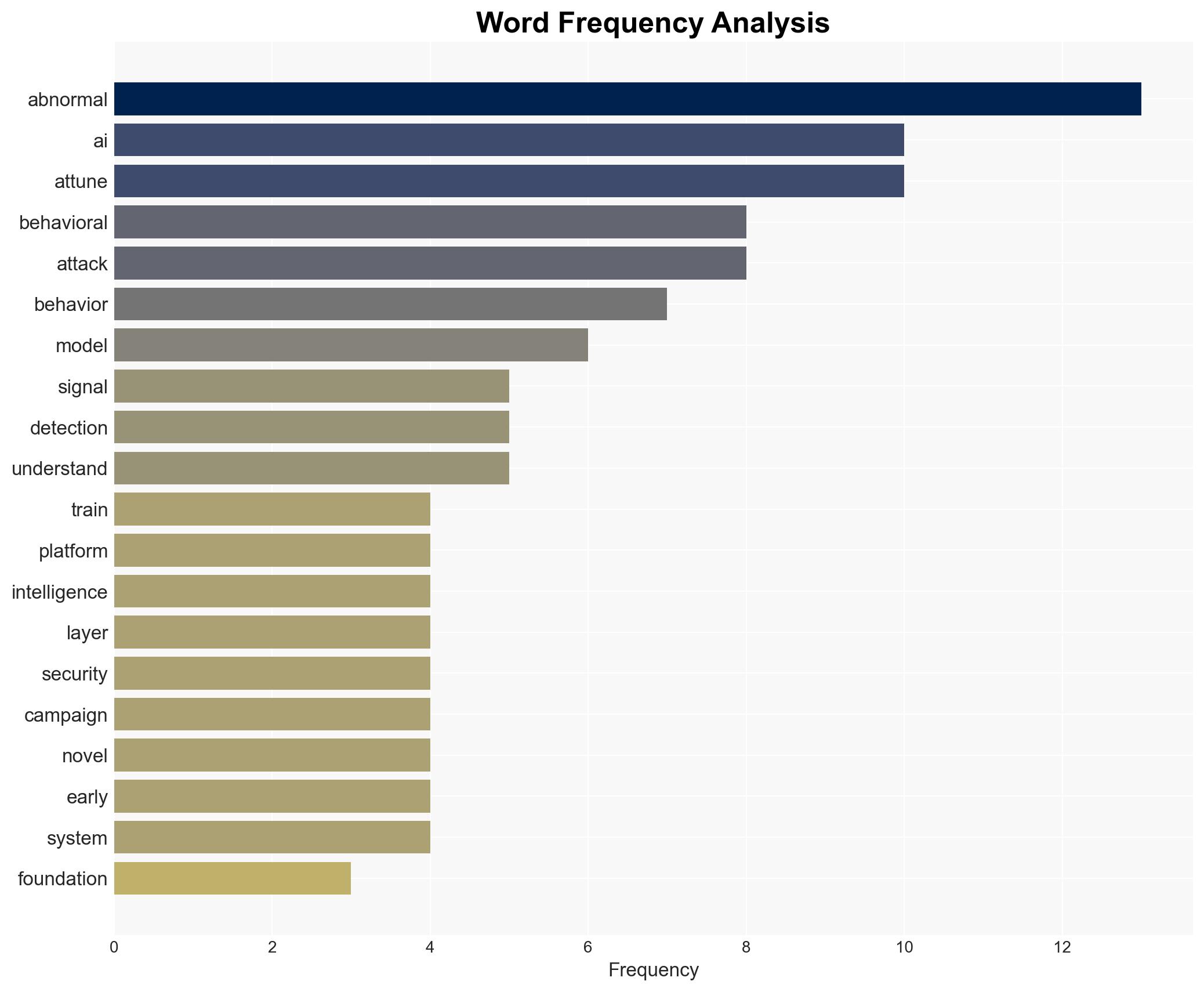
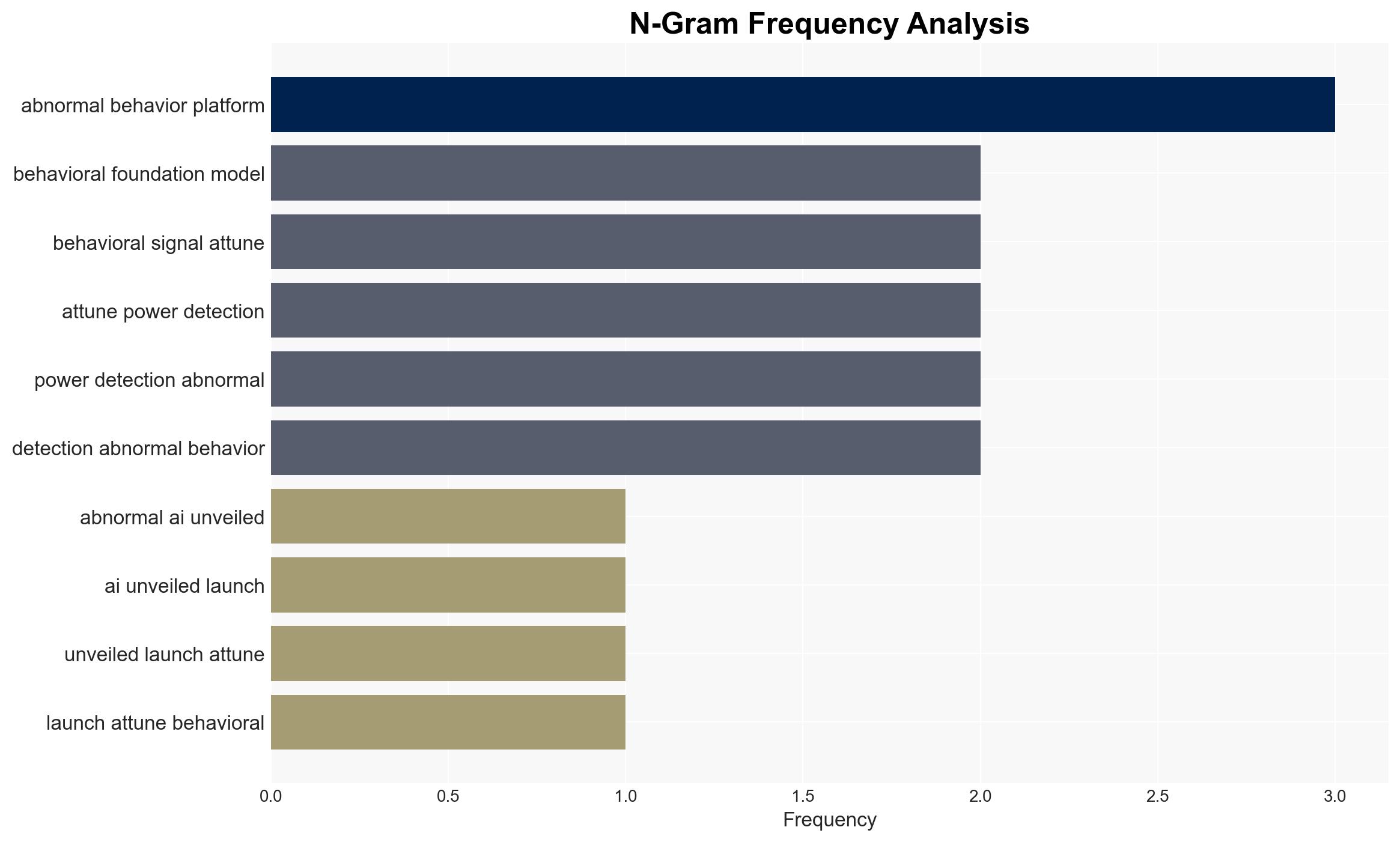
- Hypothesis A: Attune 1.0 significantly improves detection of AI-driven attacks by utilizing a unified multimodal architecture, as evidenced by its ability to detect 150,000 more attack campaigns weekly and its higher precision rate. However, uncertainties remain regarding its scalability and adaptability to future attack vectors.
- Hypothesis B: The effectiveness of Attune 1.0 is overstated, and traditional detection systems may still be necessary to complement its capabilities. This hypothesis is supported by the potential for attackers to develop new methods that could bypass behavioral detection models.
- Assessment: Hypothesis A is currently better supported due to the reported efficacy gains and precision improvements of Attune 1.0. Key indicators that could shift this judgment include the emergence of new attack techniques that evade behavioral detection and any reported failures of Attune 1.0 in live environments.
3. Key Assumptions and Red Flags
- Assumptions: The model’s training data is representative of current and emerging attack patterns; attackers will continue to exploit AI for cyberattacks; organizations will adopt Attune 1.0 widely; the model will remain adaptable to new threats.
- Information Gaps: Detailed performance metrics in diverse operational environments; information on how Attune 1.0 integrates with existing security infrastructures; data on long-term adaptability to evolving threats.
- Bias & Deception Risks: Potential over-reliance on vendor-reported efficacy data; risk of confirmation bias in interpreting early successes; possibility of adversaries testing the system to identify weaknesses.
4. Implications and Strategic Risks
The deployment of Attune 1.0 could reshape the cybersecurity landscape by setting new standards for AI-driven threat detection. However, it may also lead to an arms race in AI capabilities between attackers and defenders.
- Political / Geopolitical: Increased cybersecurity capabilities may influence national security policies and international cyber norms.
- Security / Counter-Terrorism: Enhanced detection could reduce the success rate of cyber-terrorism and state-sponsored cyber operations.
- Cyber / Information Space: Potential for increased sophistication in cyberattacks as adversaries adapt to new detection methods.
- Economic / Social: Improved cybersecurity could bolster trust in digital communications, but may also increase costs for organizations to implement advanced detection systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor initial deployment results of Attune 1.0 in diverse environments; engage with cybersecurity experts to assess integration strategies.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms to share threat intelligence; invest in training for cybersecurity personnel on behavioral detection models.
- Scenario Outlook: Best: Widespread adoption of Attune 1.0 leads to significant reduction in successful cyberattacks. Worst: Attackers quickly adapt, rendering the model less effective. Most-Likely: Incremental improvements in detection capabilities with ongoing adaptation by both defenders and attackers.
6. Key Individuals and Entities
- Evan Reiser, CEO of Abnormal AI
- Abnormal AI
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, AI-driven attacks, behavioral detection, cyber defense, threat intelligence, organizational communication, cybersecurity innovation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us