Active Exploitation of RCE Flaw CVE-2025-53521 in F5 BIG-IP APM Systems Confirmed by CISA
Published on: 2026-03-28
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
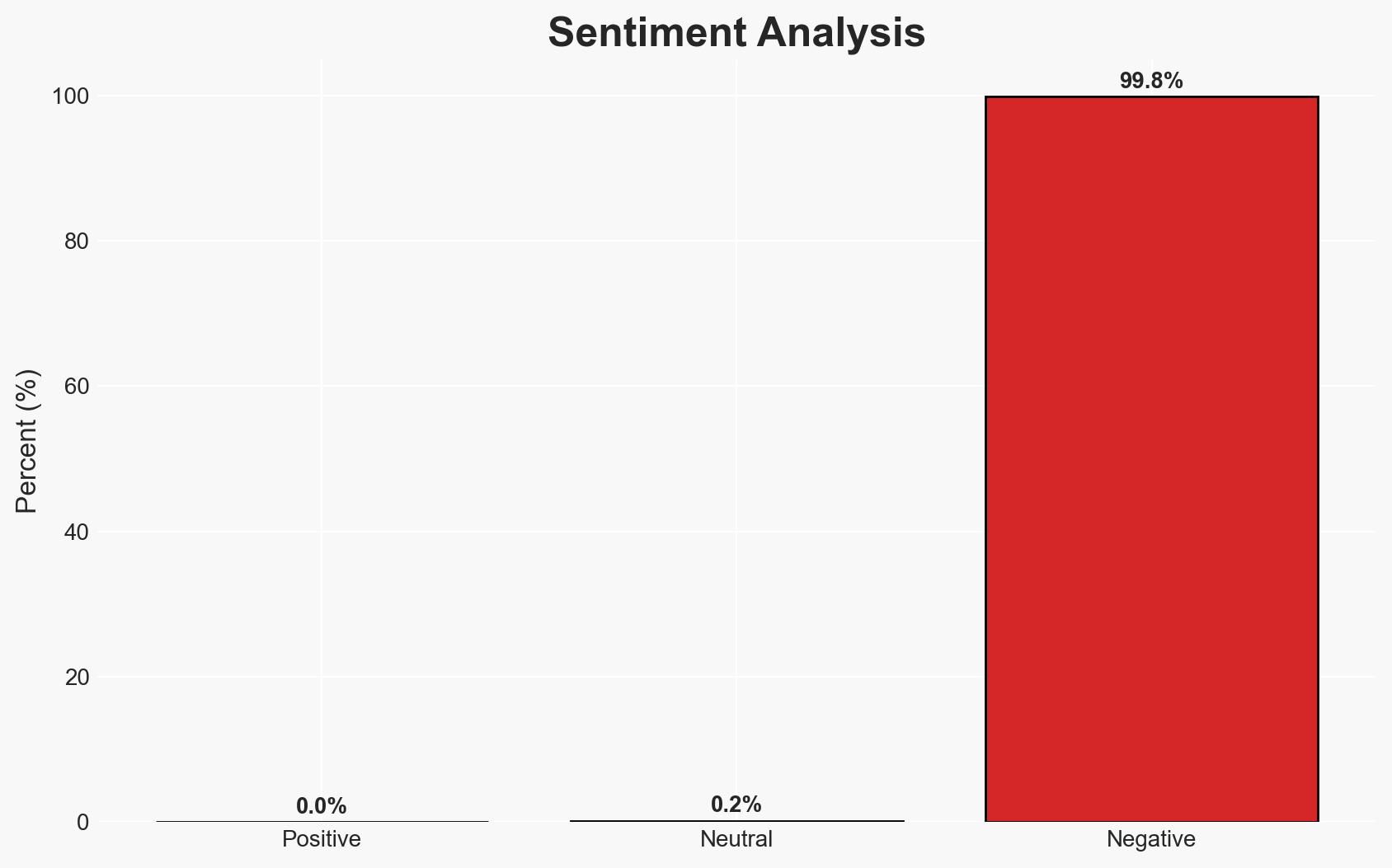
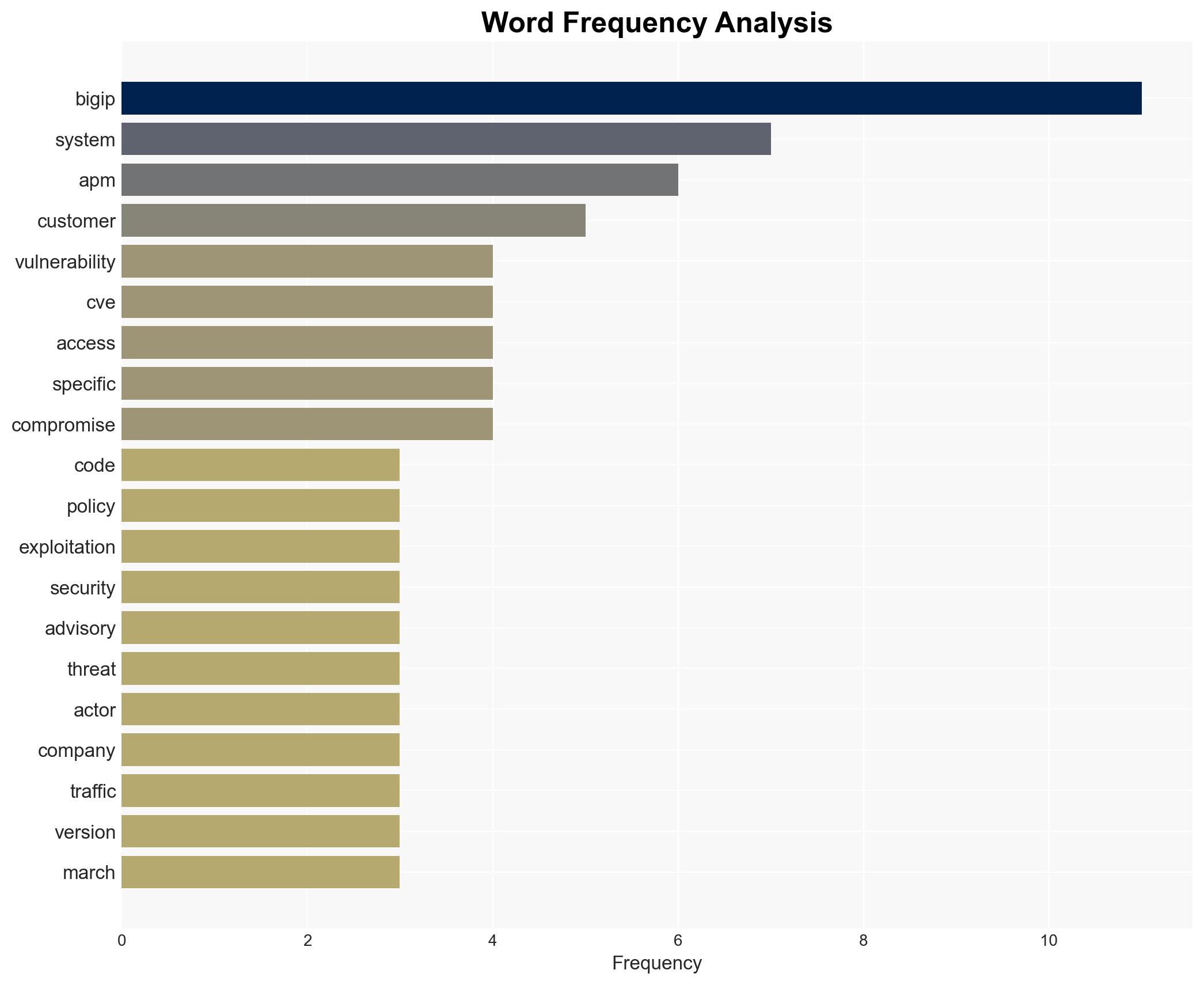
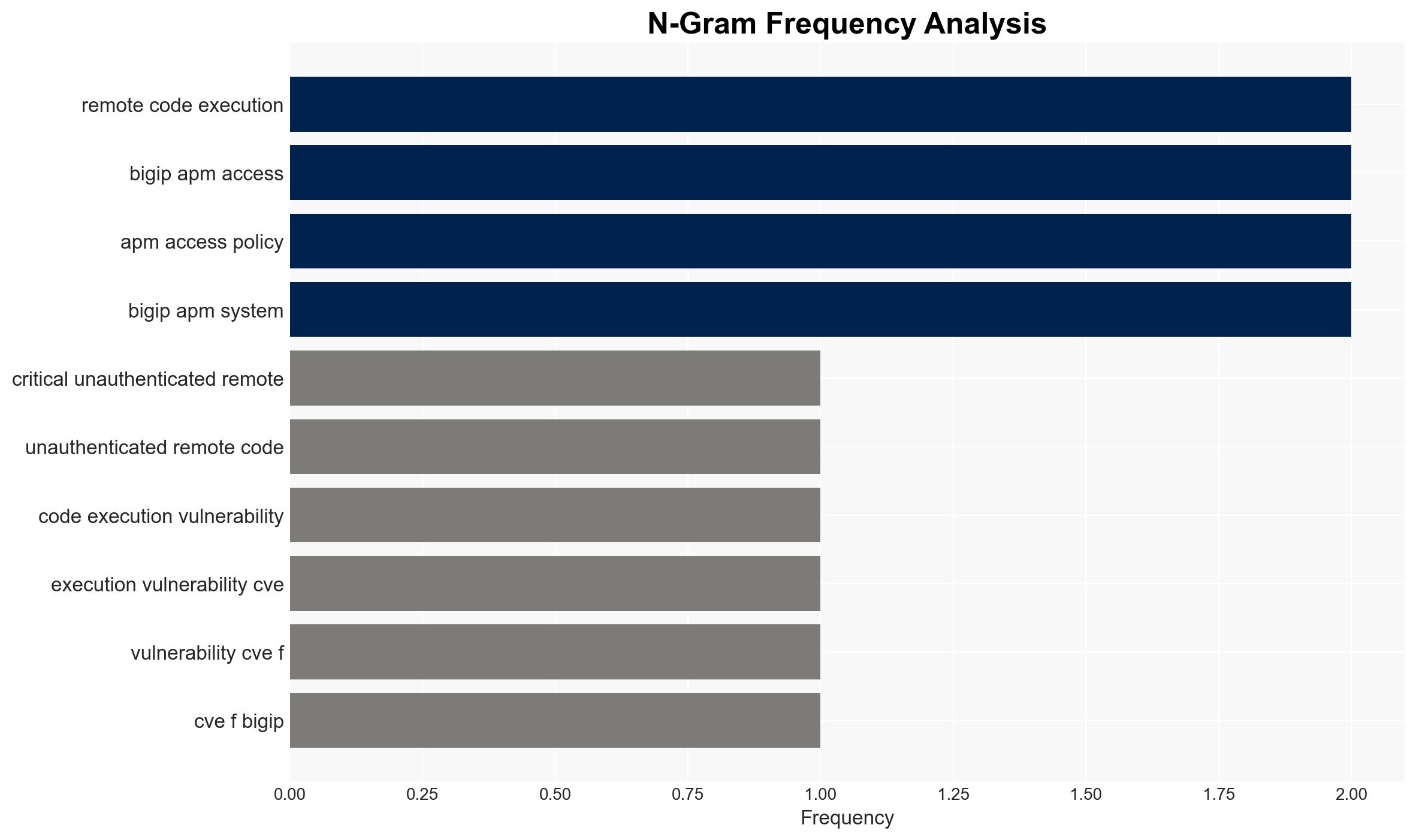
Intelligence Report: Attackers are exploiting RCE vulnerability in BIG-IP APM systems CVE-2025-53521
1. BLUF (Bottom Line Up Front)
A critical remote code execution vulnerability in F5’s BIG-IP Access Policy Manager is being actively exploited, with indications of involvement by a sophisticated nation-state actor linked to China. This affects enterprises, financial institutions, and government sectors using BIG-IP APM. The exploitation could lead to significant security breaches. Overall confidence in this assessment is moderate due to incomplete information on the timeline of exploitation.
2. Competing Hypotheses
- Hypothesis A: The exploitation of CVE-2025-53521 is primarily conducted by a Chinese state-sponsored actor aiming to gather intelligence and disrupt critical infrastructure. Supporting evidence includes the link to China and the sophistication of the attack. However, the exact objectives remain uncertain.
- Hypothesis B: The exploitation is opportunistic, with multiple actors, including non-state entities, leveraging the vulnerability for financial gain or espionage. This is supported by the broad applicability of the vulnerability and the potential for widespread exploitation. Contradicting evidence includes the specific attribution to a nation-state actor.
- Assessment: Hypothesis A is currently better supported due to the identified link to China and the nature of the breach. Key indicators that could shift this judgment include evidence of other actors exploiting the vulnerability or changes in the attack pattern.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerability was not widely known before its public disclosure; the Chinese actor’s primary goal is intelligence gathering; F5’s patches are effective if applied promptly.
- Information Gaps: Exact timeline of initial exploitation, full scope of affected systems, and detailed objectives of the threat actor.
- Bias & Deception Risks: Potential bias in attributing the attack solely to China; risk of deception in the threat actor’s tactics to obscure true intentions.
4. Implications and Strategic Risks
This vulnerability exploitation could lead to increased geopolitical tensions, particularly between the US and China, and may prompt heightened cybersecurity measures globally.
- Political / Geopolitical: Potential escalation in cyber diplomacy tensions, particularly involving US-China relations.
- Security / Counter-Terrorism: Increased risk of data breaches and operational disruptions in critical sectors.
- Cyber / Information Space: Potential for further exploitation by other actors, leading to increased cyber defense measures.
- Economic / Social: Possible economic impacts due to disruptions in financial and governmental operations, affecting public trust.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently apply F5’s patches, monitor for indicators of compromise, and enhance network monitoring for unusual activities.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity partnerships, conduct regular vulnerability assessments, and invest in threat intelligence capabilities.
- Scenario Outlook:
- Best: Rapid patching and international cooperation mitigate the threat.
- Worst: Widespread exploitation leads to significant breaches and geopolitical conflict.
- Most-Likely: Continued exploitation with gradual containment as patches are applied.
6. Key Individuals and Entities
- F5 Networks (vendor of BIG-IP APM)
- US Cybersecurity and Infrastructure Security Agency (CISA)
- Chinese state-sponsored actor (attributed threat actor)
7. Thematic Tags
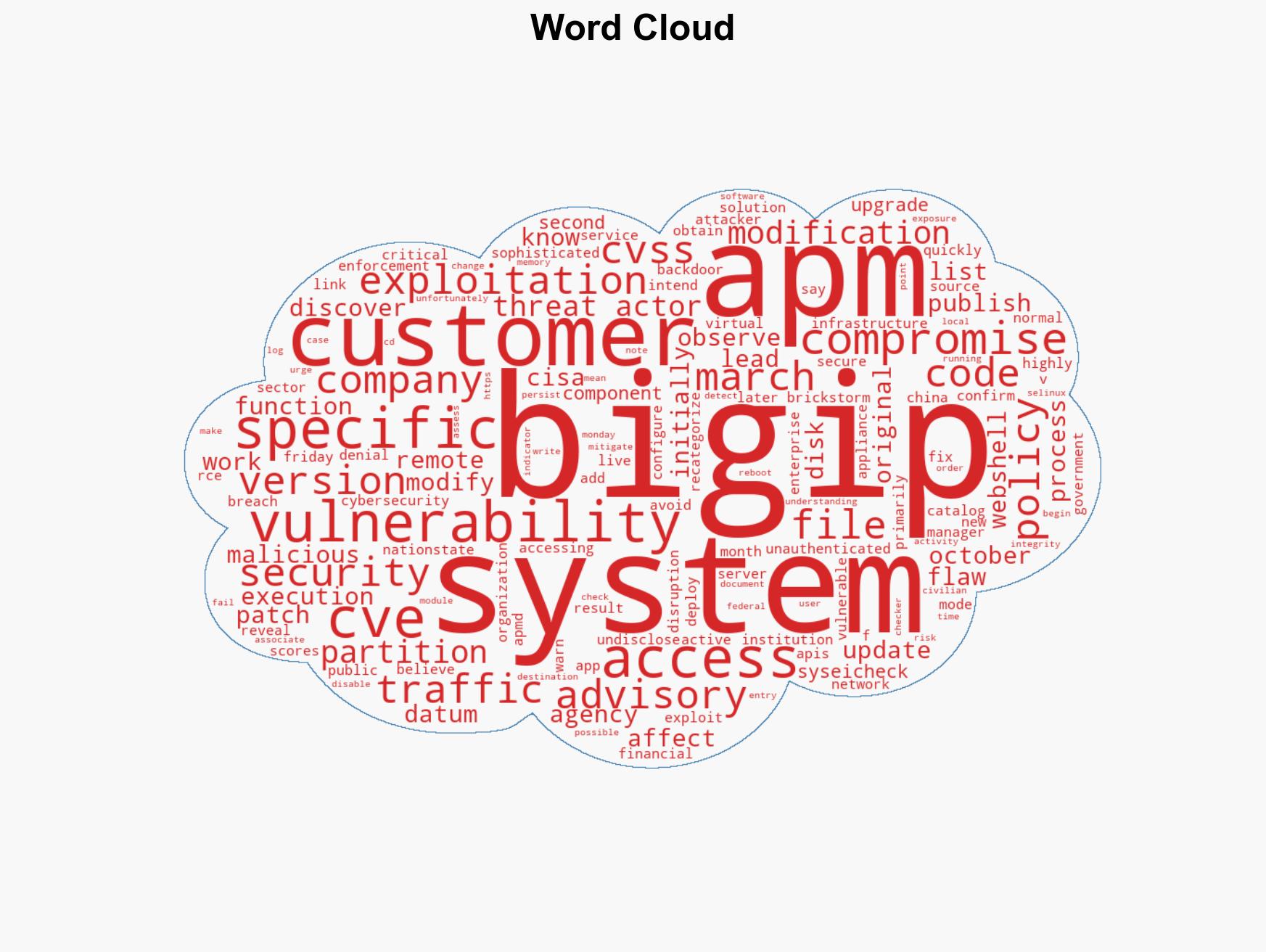
cybersecurity, nation-state actors, remote code execution, vulnerability exploitation, China, critical infrastructure, cyber defense
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us