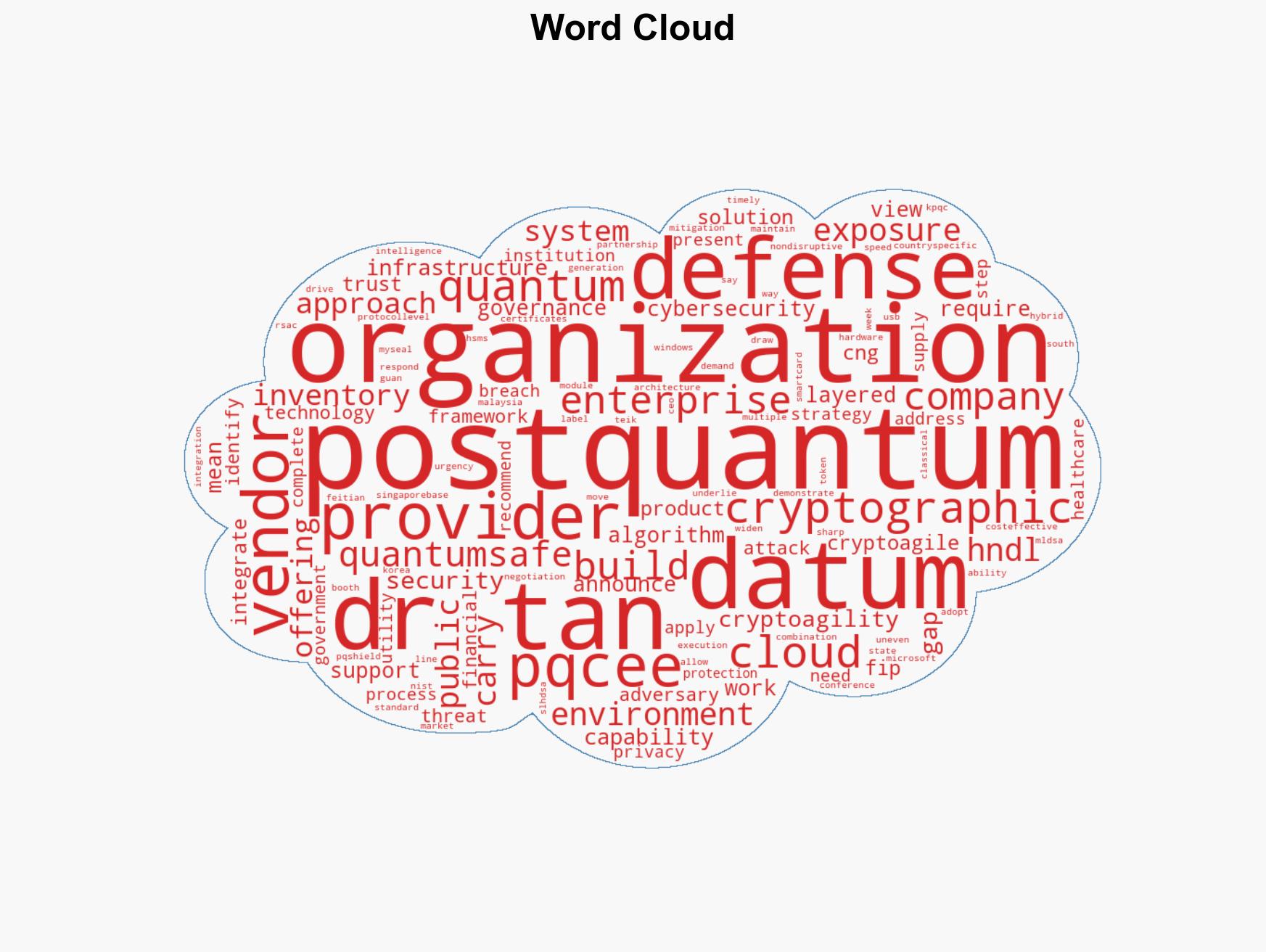
Active quantum threats highlight the need for cohesive and effective defense strategies across enterprises
Published on: 2026-03-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Quantum threats are already active and the defense response remains fragmented
1. BLUF (Bottom Line Up Front)
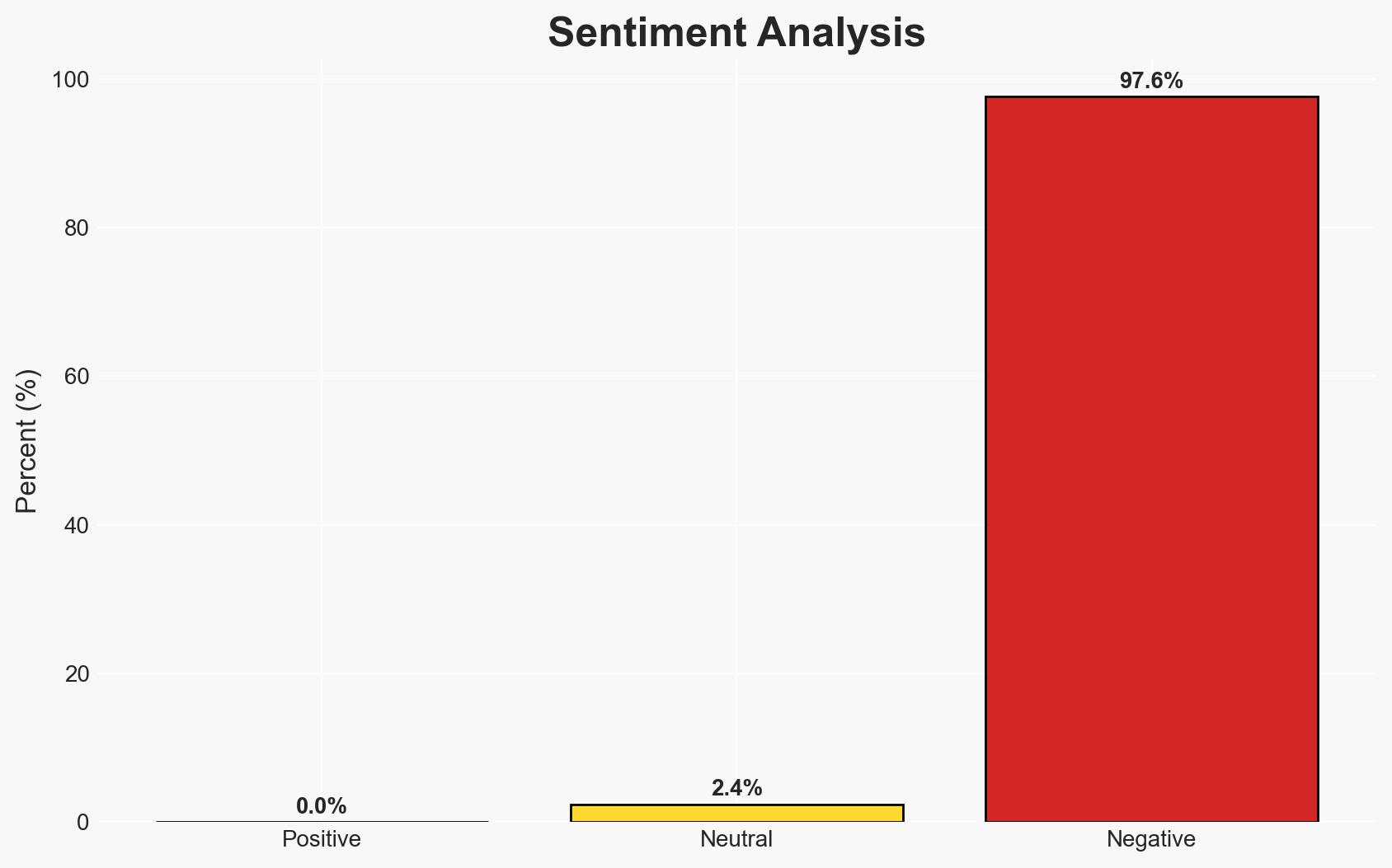
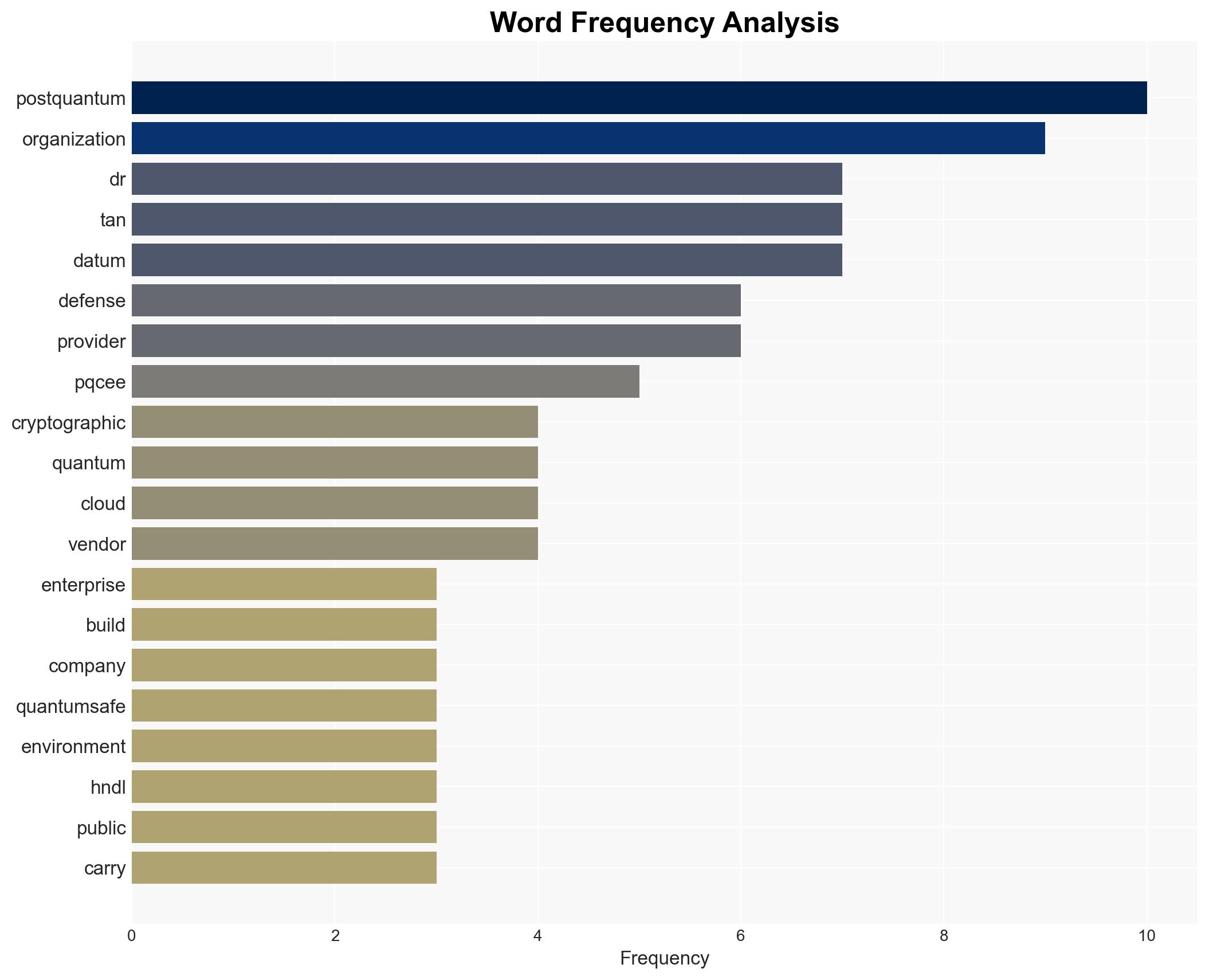
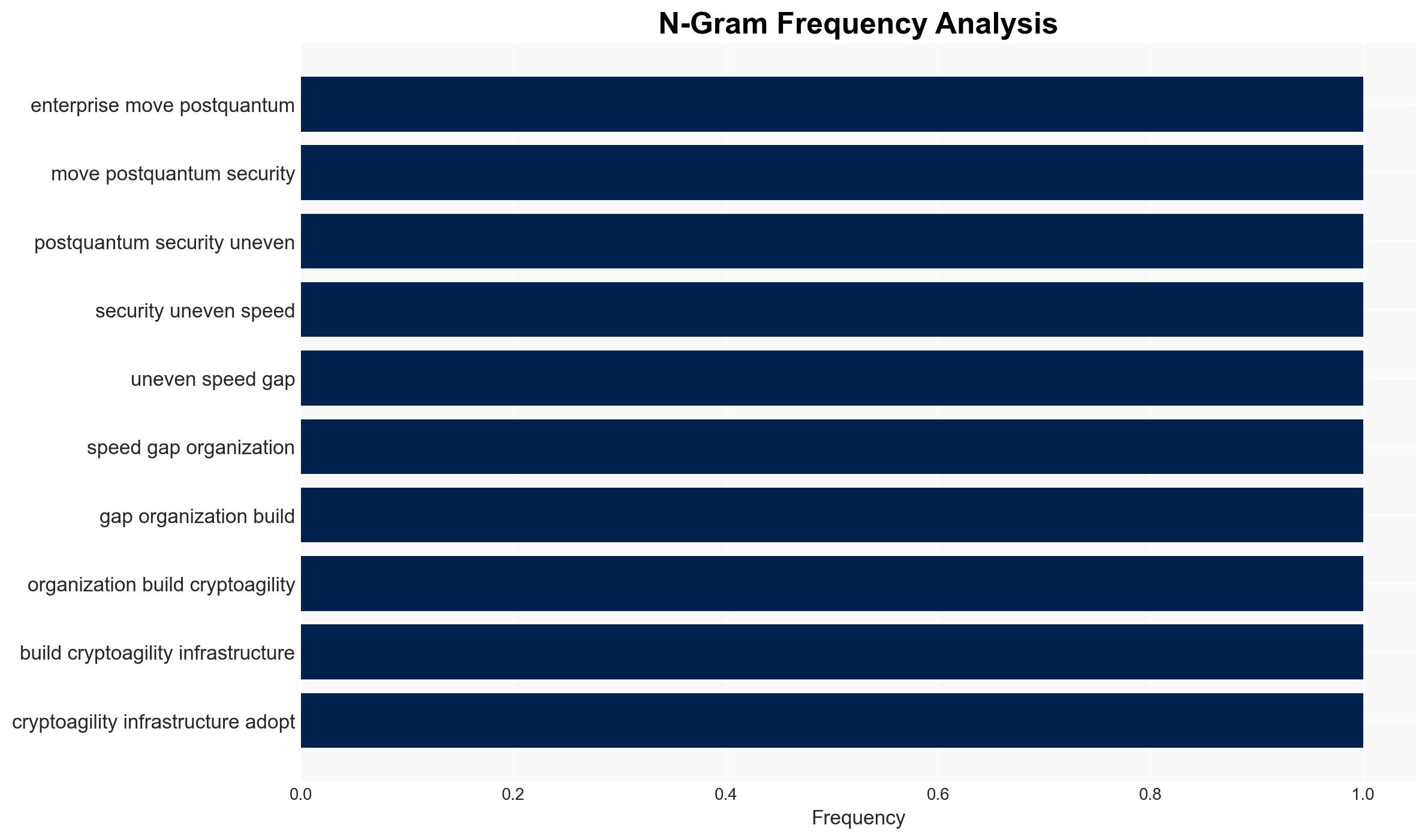
The current landscape of quantum threats, particularly the harvest-now-decrypt-later (HNDL) method, poses significant risks to sectors such as finance, healthcare, and government. The response to these threats is uneven, with a widening gap between organizations that have achieved crypto-agility and those that have not. This disparity increases vulnerability to future quantum threats. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The fragmented response to quantum threats will lead to significant breaches in critical sectors as quantum computing capabilities advance. Evidence supporting this includes the current uneven adoption of crypto-agility and the specific vulnerabilities identified in financial, healthcare, and government sectors. Key uncertainties include the timeline for quantum computing advancements and the pace of organizational adaptation.
- Hypothesis B: Organizations will rapidly adapt to quantum threats, minimizing potential breaches through increased collaboration and technological advancements. This hypothesis is supported by emerging solutions like pQCee’s CNG provider and partnerships with cryptographic module providers. However, the current lack of widespread adoption and integration contradicts this view.
- Assessment: Hypothesis A is currently better supported due to the observable gap in crypto-agility and the specific vulnerabilities in critical sectors. Indicators that could shift this judgment include accelerated adoption of quantum-safe technologies and enhanced cross-sector collaboration.
3. Key Assumptions and Red Flags
- Assumptions: Quantum computing will advance to a level capable of breaking current cryptographic systems; organizations will not uniformly adopt quantum-safe measures; HNDL attacks will continue to be a priority for adversaries.
- Information Gaps: Detailed timelines for quantum computing breakthroughs; comprehensive data on the adoption rates of quantum-safe technologies across sectors.
- Bias & Deception Risks: Potential over-reliance on vendor-provided information; confirmation bias in assessing the readiness of organizations based on limited case studies.
4. Implications and Strategic Risks
The development of quantum threats and the fragmented defense response could lead to significant security breaches and erosion of trust in critical sectors. This situation may evolve with technological advancements and policy changes.
- Political / Geopolitical: Potential for increased geopolitical tensions as nations race to develop quantum capabilities and defenses.
- Security / Counter-Terrorism: Enhanced threat environment with adversaries exploiting quantum vulnerabilities, necessitating updated security protocols.
- Cyber / Information Space: Increased cyber espionage and data breaches as adversaries leverage quantum computing capabilities.
- Economic / Social: Potential economic instability due to breaches in financial institutions; social unrest from privacy violations in healthcare and government sectors.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive audit of current cryptographic practices; prioritize sectors with high exposure for immediate intervention.
- Medium-Term Posture (1–12 months): Develop cross-sector partnerships to share best practices; invest in R&D for quantum-safe technologies.
- Scenario Outlook:
- Best: Rapid adoption of quantum-safe measures mitigates risks.
- Worst: Major breaches occur due to slow adaptation, leading to economic and social disruption.
- Most-Likely: Gradual improvement in defenses with periodic breaches highlighting vulnerabilities.
6. Key Individuals and Entities
- Dr. Tan Teik Guan, CEO of pQCee
- pQCee
- PQShield
- Feitian Technologies
- Not clearly identifiable from open sources in this snippet for other individuals/entities.
7. Thematic Tags
cybersecurity, quantum computing, crypto-agility, harvest-now-decrypt-later, financial sector, healthcare privacy, government security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us