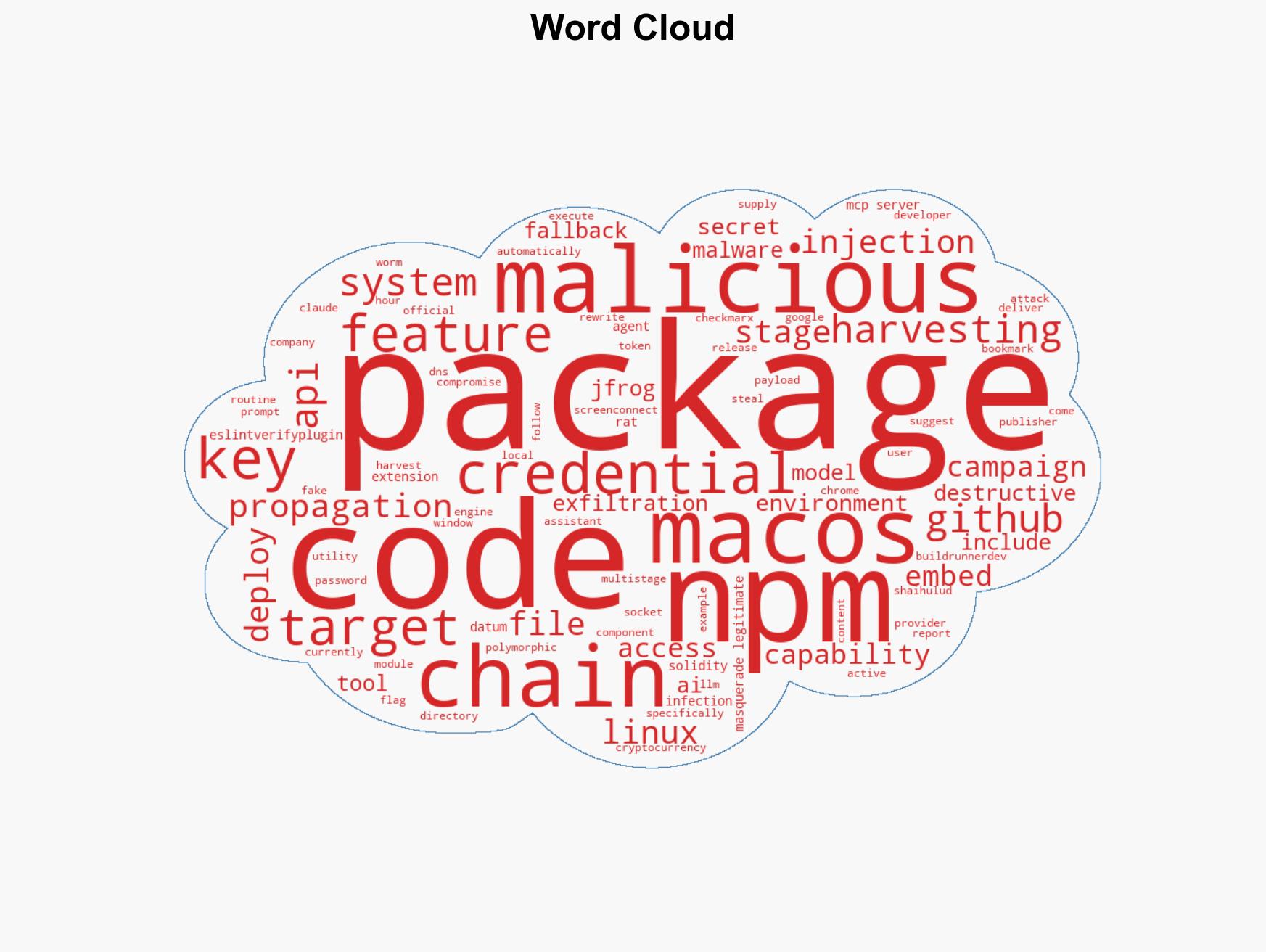
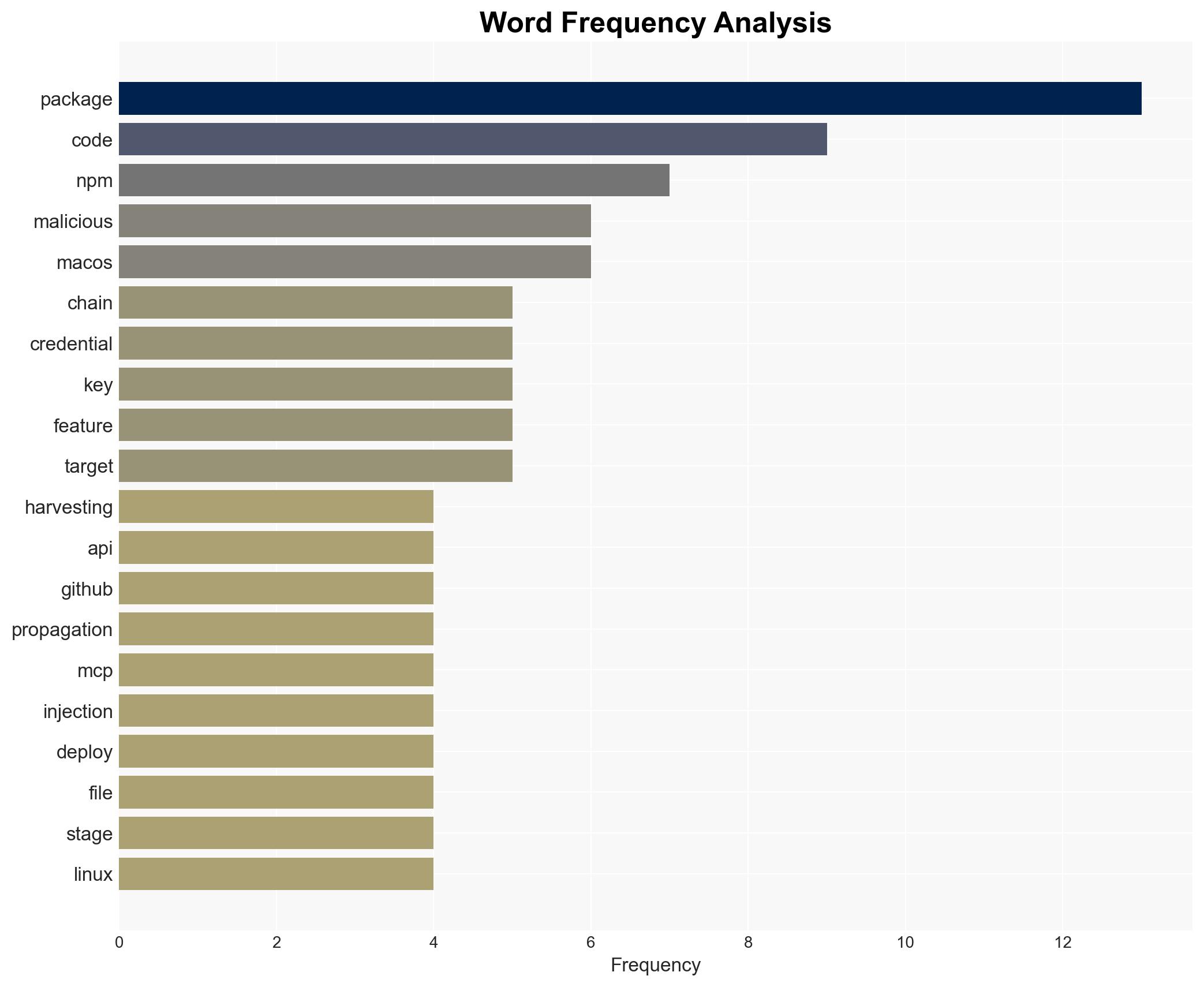
Active Supply Chain Attack Utilizes Malicious npm Packages to Steal Credentials and Crypto Keys
Published on: 2026-02-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Malicious npm Packages Harvest Crypto Keys CI Secrets and API Tokens
1. BLUF (Bottom Line Up Front)
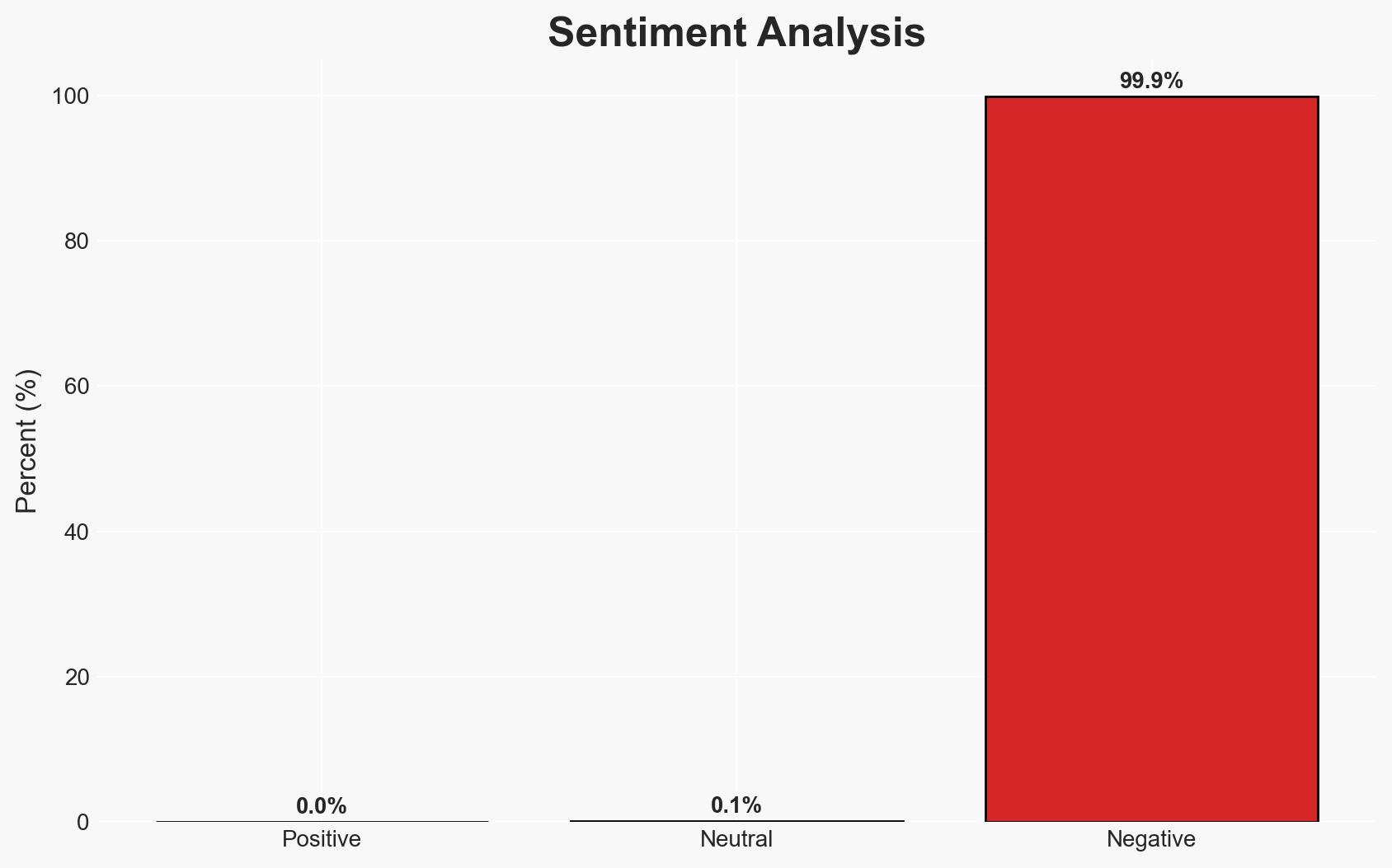
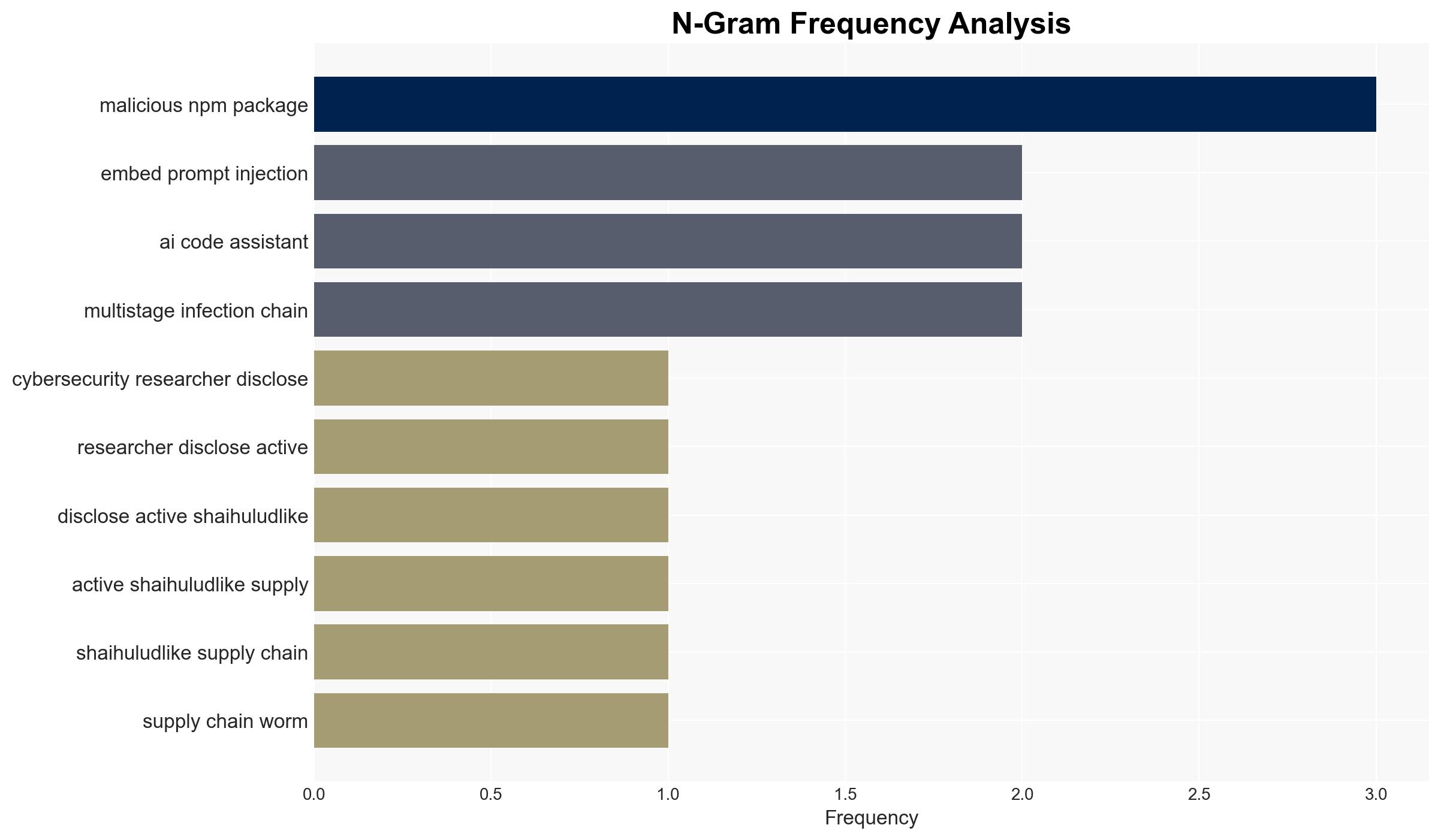
The discovery of a supply chain attack involving malicious npm packages, codenamed SANDWORM_MODE, poses a significant threat to software development environments by harvesting credentials and API keys. This campaign, reminiscent of previous Shai-Hulud attacks, could lead to widespread security breaches and data exfiltration. The overall confidence in this assessment is moderate, given the complexity of the attack and the potential for further evolution.
2. Competing Hypotheses
- Hypothesis A: The campaign is primarily financially motivated, aiming to steal cryptocurrency and sensitive credentials for monetary gain. This is supported by the focus on harvesting cryptocurrency keys and API tokens. However, the sophisticated nature of the attack suggests potential alternative motivations.
- Hypothesis B: The campaign may serve a broader espionage or sabotage purpose, targeting software development environments to disrupt operations or gather intelligence. The use of advanced techniques like polymorphic engines and AI coding assistant targeting supports this hypothesis, though direct evidence is limited.
- Assessment: Hypothesis B is currently better supported due to the complexity and sophistication of the attack, which suggests capabilities beyond simple financial theft. Indicators such as the involvement of AI coding assistants and the potential for widespread disruption could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The attack is ongoing and has not yet reached its full potential impact; the entities behind the aliases official334 and javaorg are coordinated; the attack leverages both npm and GitHub for propagation.
- Information Gaps: The identity and ultimate objectives of the attackers; the full extent of the affected systems and organizations; the potential for further evolution of the attack methodology.
- Bias & Deception Risks: Confirmation bias in attributing the attack to known patterns; potential deception by attackers to mislead attribution efforts; reliance on a single source (Socket) for detailed information.
4. Implications and Strategic Risks
This development could significantly impact the security of software development environments globally, potentially leading to data breaches and operational disruptions.
- Political / Geopolitical: Potential for escalation if state actors are involved or if the attack targets critical infrastructure.
- Security / Counter-Terrorism: Increased threat to cybersecurity, requiring heightened vigilance and response measures.
- Cyber / Information Space: Highlights vulnerabilities in software supply chains and the need for improved security protocols.
- Economic / Social: Possible economic impact due to disruptions in software development and potential loss of sensitive data.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of npm and GitHub activities; implement stricter access controls and credential management; disseminate threat intelligence to affected parties.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing; invest in supply chain security measures; conduct regular security audits and training.
- Scenario Outlook: Best: Attack is contained with minimal impact. Worst: Widespread breaches and significant data loss. Most-Likely: Continued targeted attacks with moderate disruption, triggering increased security measures.
6. Key Individuals and Entities
- official334 (npm publisher alias)
- javaorg (npm publisher alias)
- Socket (supply chain security company)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, supply chain attack, cyber-espionage, credential harvesting, software security, AI exploitation, npm packages, GitHub security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us