AI-Driven Cyber Attacks Surge 44% Targeting Public Applications, IBM Reports
Published on: 2026-02-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: 44 Surge in App Exploits as AI Speeds Up Cyber-Attacks IBM Finds
1. BLUF (Bottom Line Up Front)
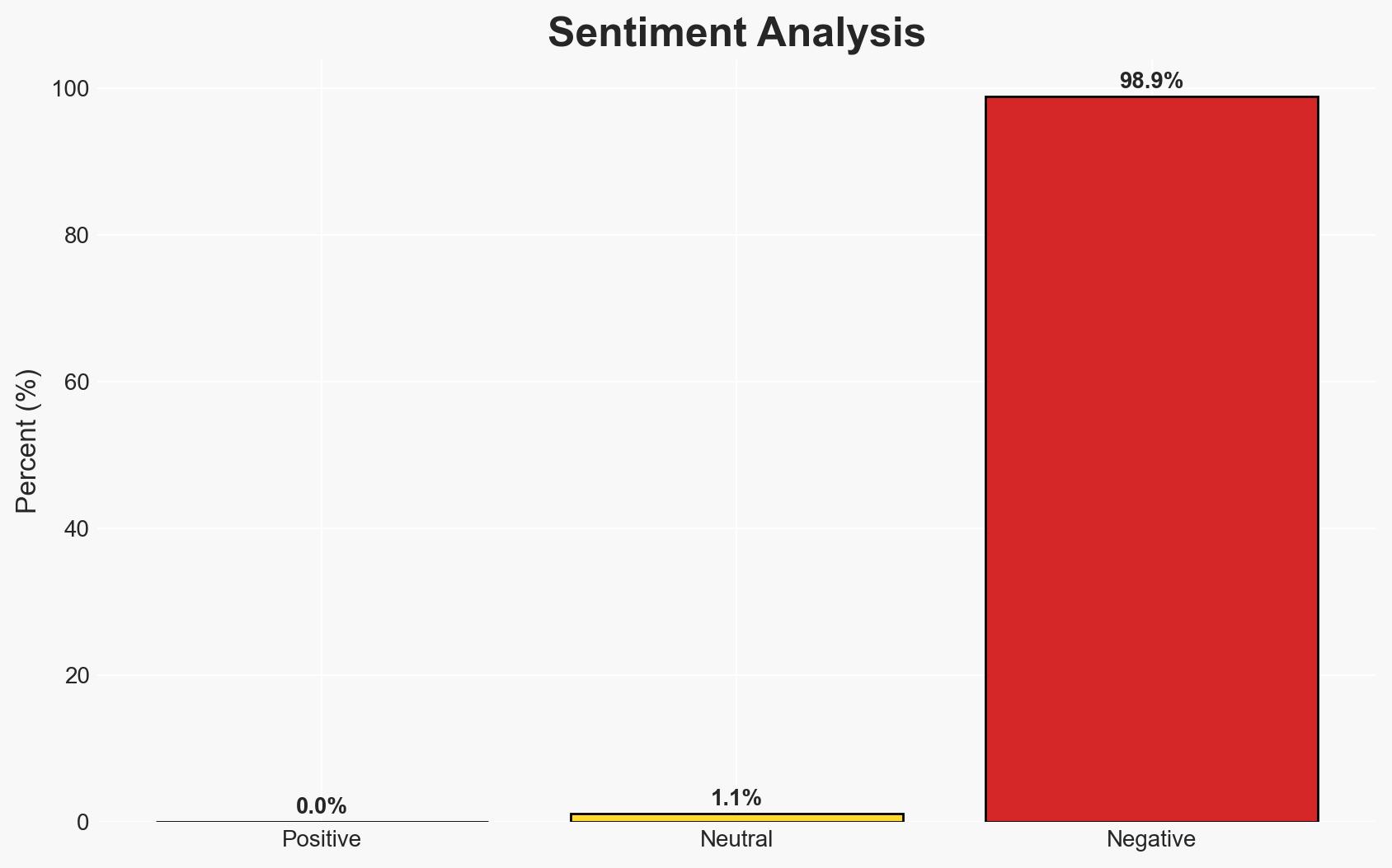
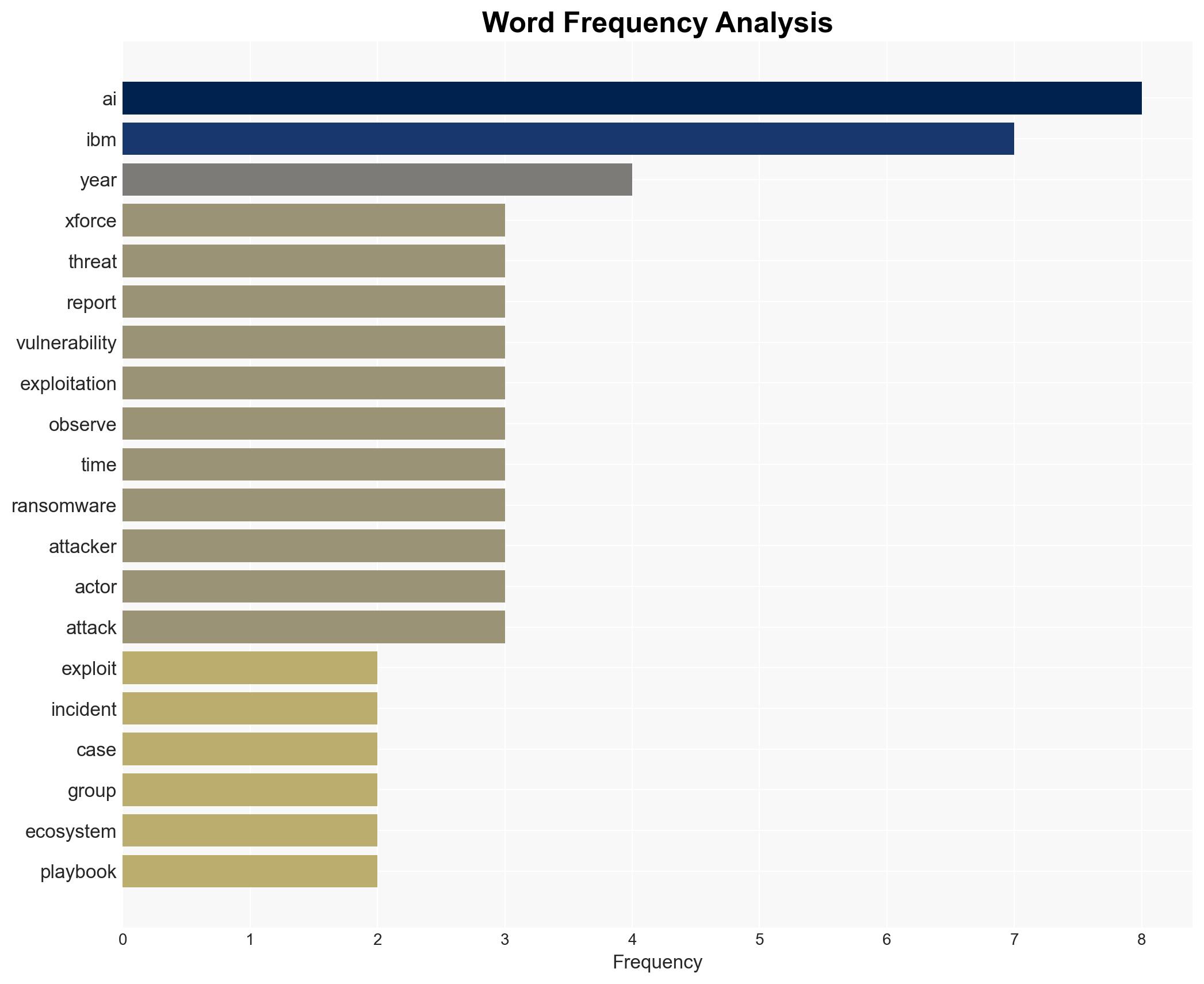
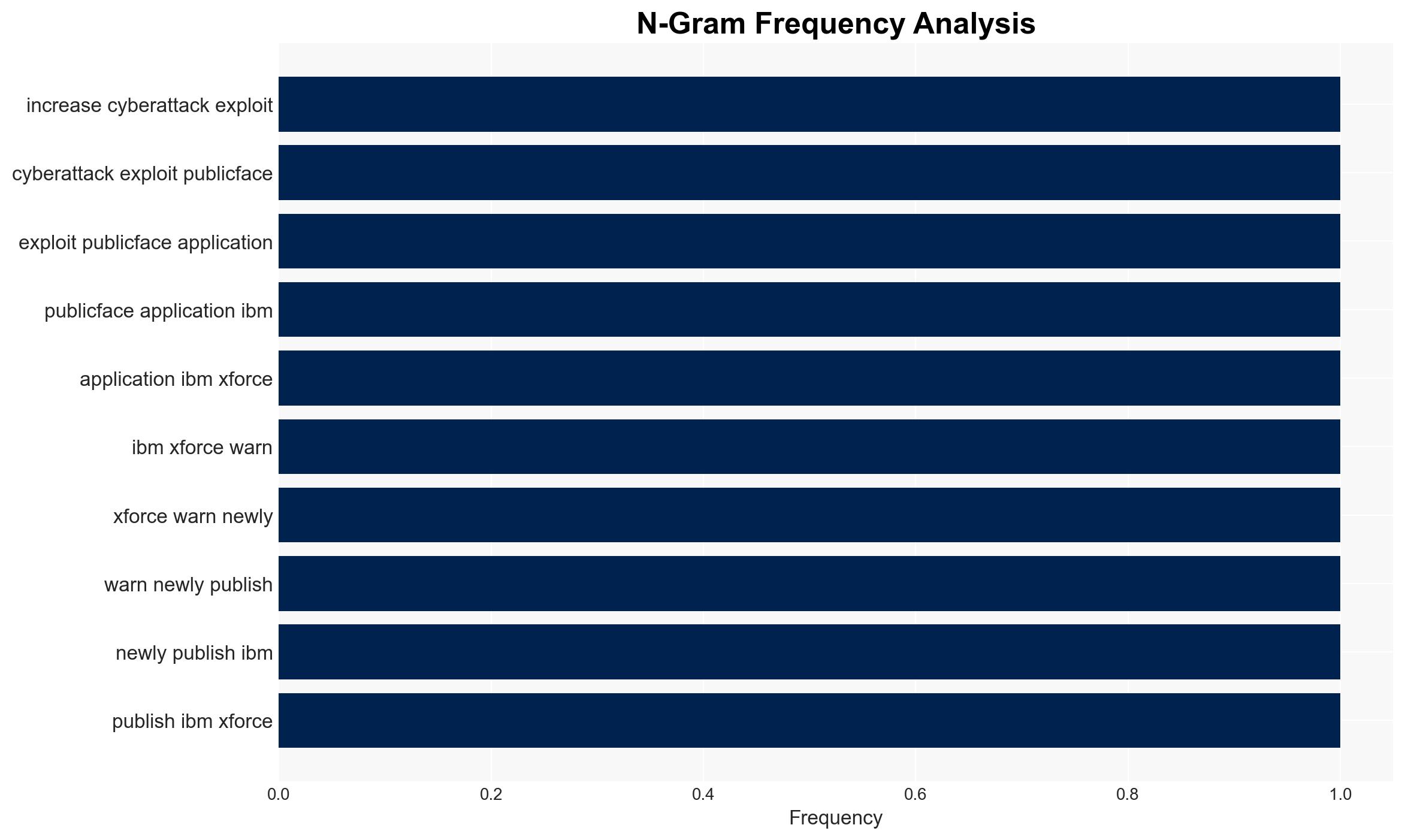
The IBM X-Force report highlights a significant 44% increase in cyber-attacks exploiting public-facing applications, driven by AI-enabled vulnerability scanning and missing authentication controls. The rapid adoption of AI by threat actors is accelerating the pace of cyber threats, impacting sectors such as manufacturing and regions like North America. This development poses a growing risk to national security and economic stability. Overall confidence in this assessment is moderate due to existing information gaps.
2. Competing Hypotheses
- Hypothesis A: The surge in cyber-attacks is primarily due to the increased use of AI by threat actors, which enhances their ability to exploit vulnerabilities quickly. Supporting evidence includes the report’s findings on AI-enabled vulnerability scanning and the acceleration of the attacker lifecycle. Key uncertainties include the extent of AI’s role compared to other factors.
- Hypothesis B: The increase in cyber-attacks is largely due to systemic weaknesses in cybersecurity practices, such as missing authentication controls and inadequate software vulnerability management. While AI plays a role, the primary driver is the persistent vulnerability landscape. This is supported by the report’s emphasis on businesses being overwhelmed by software vulnerabilities.
- Assessment: Hypothesis A is currently better supported due to the specific mention of AI’s role in accelerating attack vectors and the observed increase in AI-driven activities. However, further data on the relative impact of AI versus traditional vulnerabilities could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: AI capabilities will continue to evolve and be adopted by threat actors; the current cybersecurity infrastructure remains insufficient to handle AI-accelerated threats; the report’s data accurately reflects broader trends.
- Information Gaps: Detailed data on the specific AI tools and techniques used by threat actors; comparative analysis of AI’s impact versus traditional methods; insights into defensive measures being developed.
- Bias & Deception Risks: Potential bias in the report due to IBM’s vested interest in cybersecurity services; possible exaggeration of AI’s role to highlight emerging threats.
4. Implications and Strategic Risks
The integration of AI into cyber-attack methodologies could lead to a paradigm shift in the threat landscape, necessitating a reevaluation of current defensive strategies. This development may exacerbate existing geopolitical tensions and increase the complexity of cyber defense.
- Political / Geopolitical: Potential for increased cyber conflict between nation-states as AI tools become more accessible and effective.
- Security / Counter-Terrorism: Heightened threat environment with more sophisticated and rapid attacks, challenging existing counter-terrorism frameworks.
- Cyber / Information Space: Escalation in cyber espionage and misinformation campaigns, leveraging AI for enhanced impact.
- Economic / Social: Increased costs for businesses due to heightened cybersecurity needs, potential for economic disruption if critical infrastructure is targeted.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of AI-related cyber threats, prioritize patching of known vulnerabilities, and increase awareness of AI-driven attack vectors among stakeholders.
- Medium-Term Posture (1–12 months): Develop partnerships for AI threat intelligence sharing, invest in AI-based defensive technologies, and strengthen supply chain cybersecurity protocols.
- Scenario Outlook:
- Best: Effective countermeasures reduce AI-driven attack success rates, stabilizing the threat landscape.
- Worst: AI capabilities outpace defensive measures, leading to widespread disruption and economic damage.
- Most-Likely: Continued increase in AI-driven attacks with gradual adaptation by defenders, resulting in a prolonged period of elevated threat levels.
6. Key Individuals and Entities
- Mark Hughes, Global Managing Partner for Cybersecurity Services at IBM
- IBM X-Force
- North Korean IT worker schemes (as an example of AI-driven activities)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
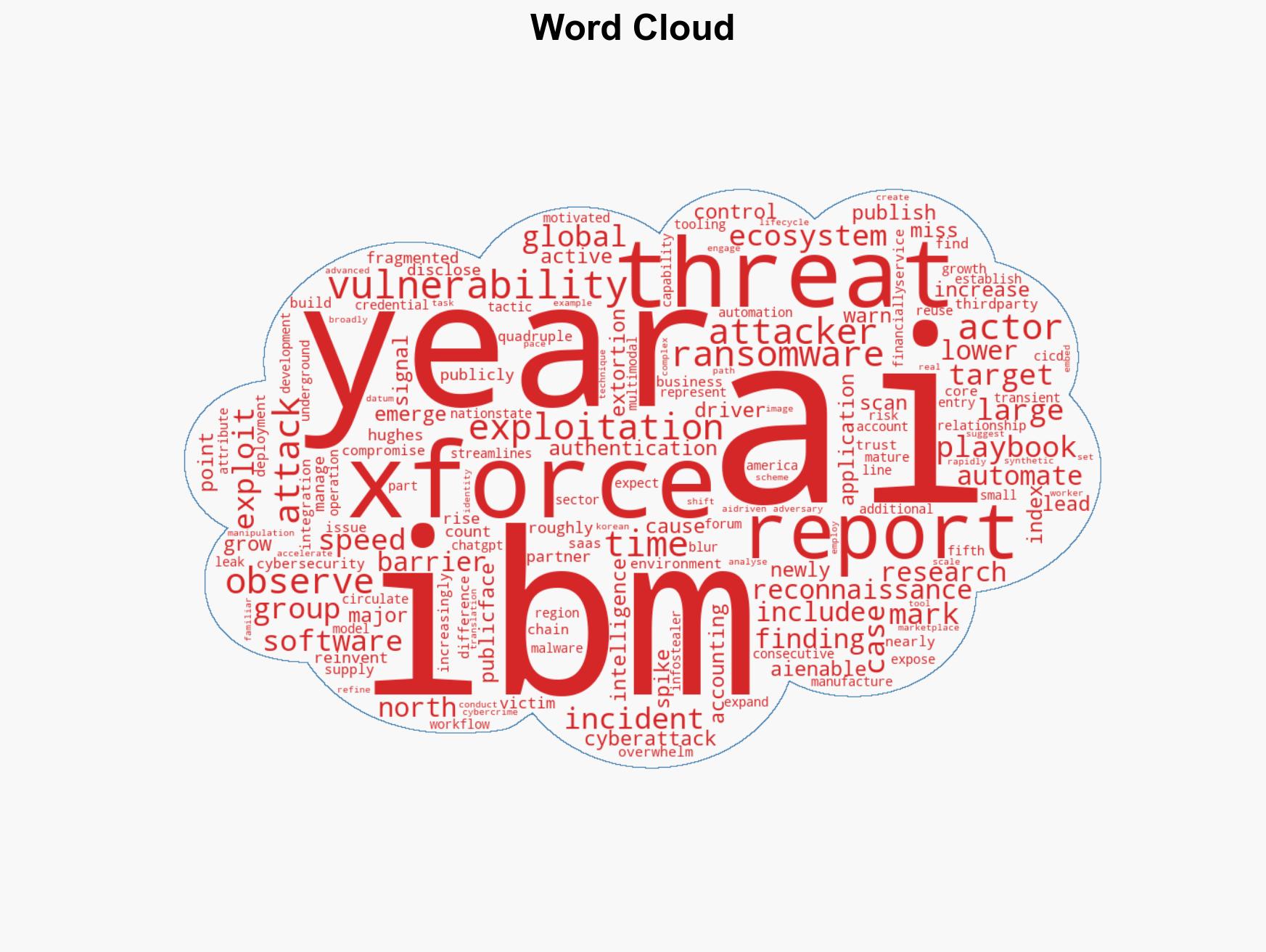
cybersecurity, AI in cybercrime, vulnerability exploitation, ransomware, supply chain attacks, North America cyber threats, manufacturing sector cyber risks
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us