AI-Driven Threat Actors Shorten Exploitation Timeline Post-Vulnerability Disclosure, Says Rapid7 Report
Published on: 2026-03-18
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: AI-Enabled Adversaries Compress Time-to-Exploit Following Vulnerability Disclosure
1. BLUF (Bottom Line Up Front)
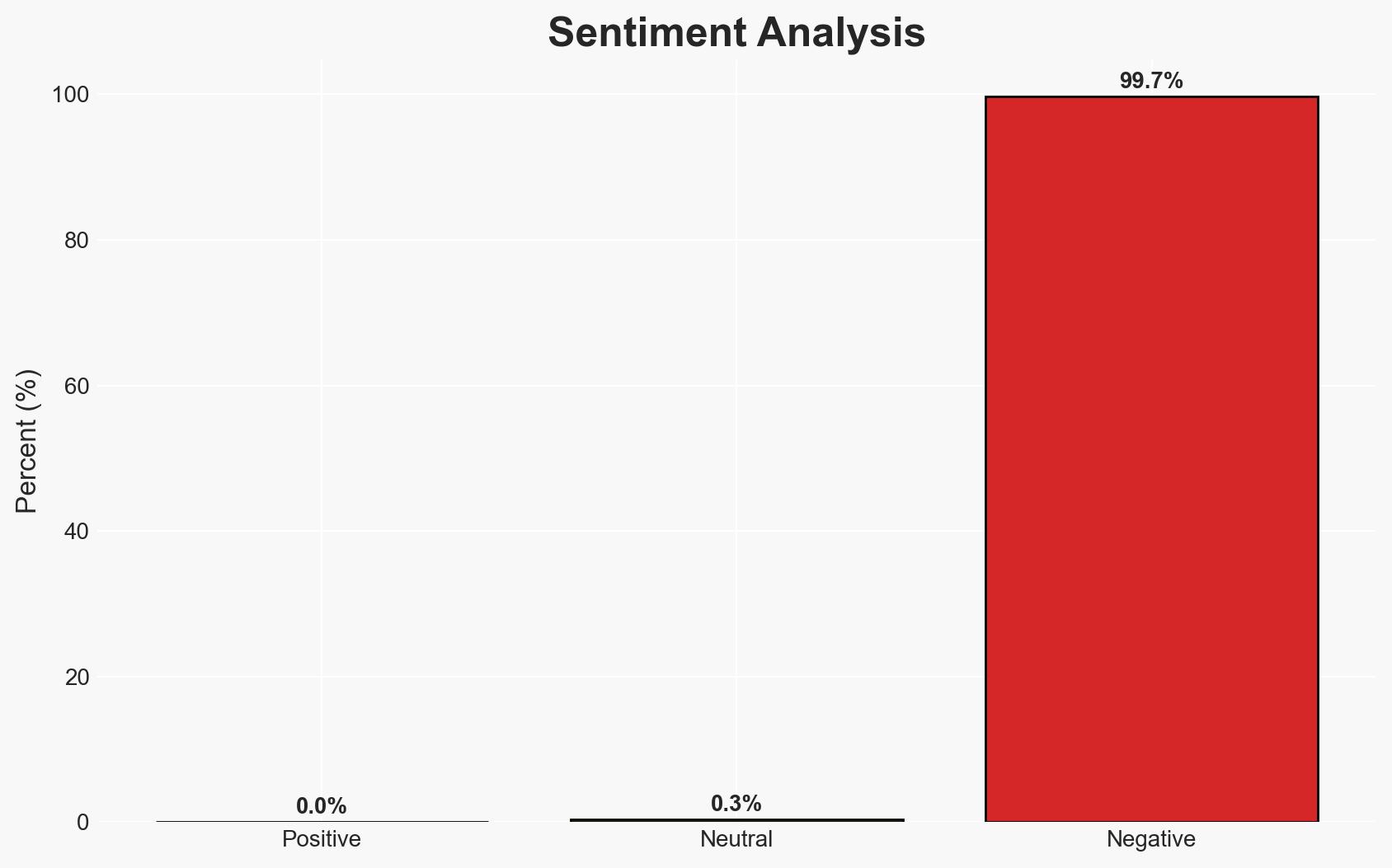
AI and automation have significantly reduced the time between vulnerability disclosure and exploitation, posing increased risks to cybersecurity. The most likely hypothesis is that AI is being used to enhance existing attack methodologies, rather than creating new ones. This affects organizations with weak cybersecurity postures, particularly those with unpatched systems. Overall confidence in this assessment is moderate due to potential information gaps and evolving threat landscapes.
2. Competing Hypotheses
- Hypothesis A: AI and automation are primarily accelerating existing attack methods, not fundamentally changing threat actor capabilities. This is supported by the lack of transformation in threat actor intent or sophistication, as reported by Rapid7. However, there is uncertainty about the full extent of AI’s role in future threat landscapes.
- Hypothesis B: AI is enabling entirely new forms of cyber threats and capabilities that are not yet fully understood or documented. While there is no direct evidence in the report to support this, the rapid pace of technological advancement could lead to unforeseen developments.
- Assessment: Hypothesis A is currently better supported due to the evidence of accelerated existing methods rather than new capabilities. Indicators that could shift this judgment include the emergence of novel attack vectors directly attributed to AI innovations.
3. Key Assumptions and Red Flags
- Assumptions: AI will continue to be used to enhance existing cyber attack methods; Organizations will remain vulnerable due to slow patching cycles; Threat actors will prioritize speed over sophistication.
- Information Gaps: Detailed data on the specific AI tools and techniques being used by threat actors; Comprehensive analysis of AI’s role in emerging cyber threats.
- Bias & Deception Risks: Potential bias in Rapid7’s data due to its commercial interests; Risk of underestimating the sophistication of threat actors leveraging AI.
4. Implications and Strategic Risks
This development could lead to a persistent increase in successful cyber intrusions, challenging current defensive measures and necessitating rapid adaptation in cybersecurity strategies.
- Political / Geopolitical: Increased cyber threats could strain international relations, especially if state-sponsored actors are involved.
- Security / Counter-Terrorism: Faster exploitation cycles may overwhelm current cybersecurity defenses, increasing the risk of significant breaches.
- Cyber / Information Space: The speed of exploitation may outpace current detection and response capabilities, leading to more frequent and severe data breaches.
- Economic / Social: Increased cyber incidents could lead to financial losses and erode trust in digital systems, impacting economic stability and social cohesion.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of vulnerability disclosures; prioritize patching of critical systems; increase awareness and training on AI-driven threats.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; invest in AI-driven defensive technologies; strengthen identity and access management protocols.
- Scenario Outlook:
- Best: Organizations rapidly adapt to AI-driven threats, minimizing successful exploits.
- Worst: AI advancements outpace defensive measures, leading to widespread and severe breaches.
- Most-Likely: Incremental improvements in defenses mitigate some risks, but the threat landscape remains challenging.
6. Key Individuals and Entities
- Rapid7 (Security Vendor)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
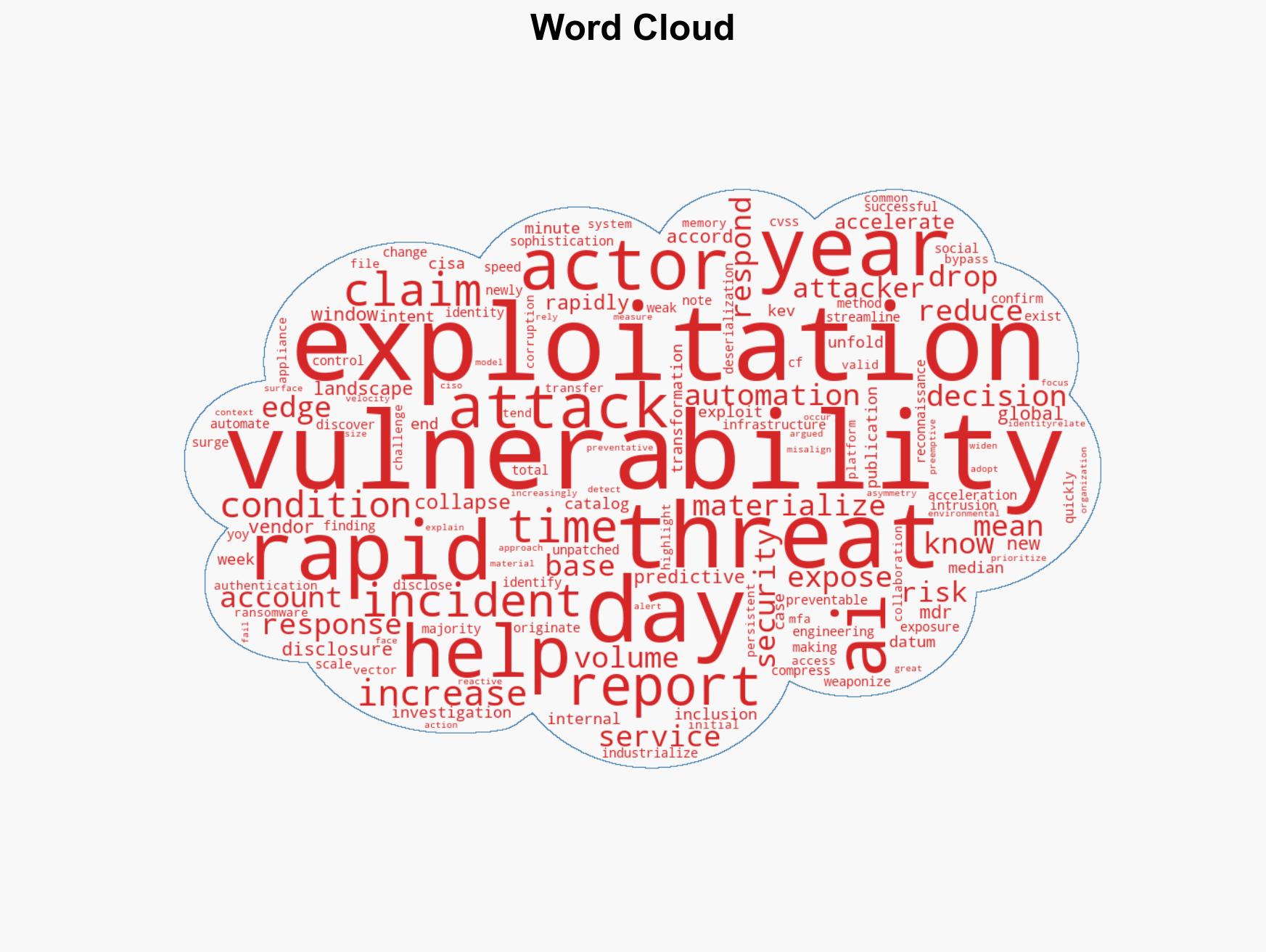
cybersecurity, AI, vulnerability exploitation, threat intelligence, automation, cyber defense, risk management
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us