AI Drives Innovation While Fueling a Surge in Automated Cyber Attacks
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: AI powers innovation but its also powering the next wave of cyber attacks
1. BLUF (Bottom Line Up Front)
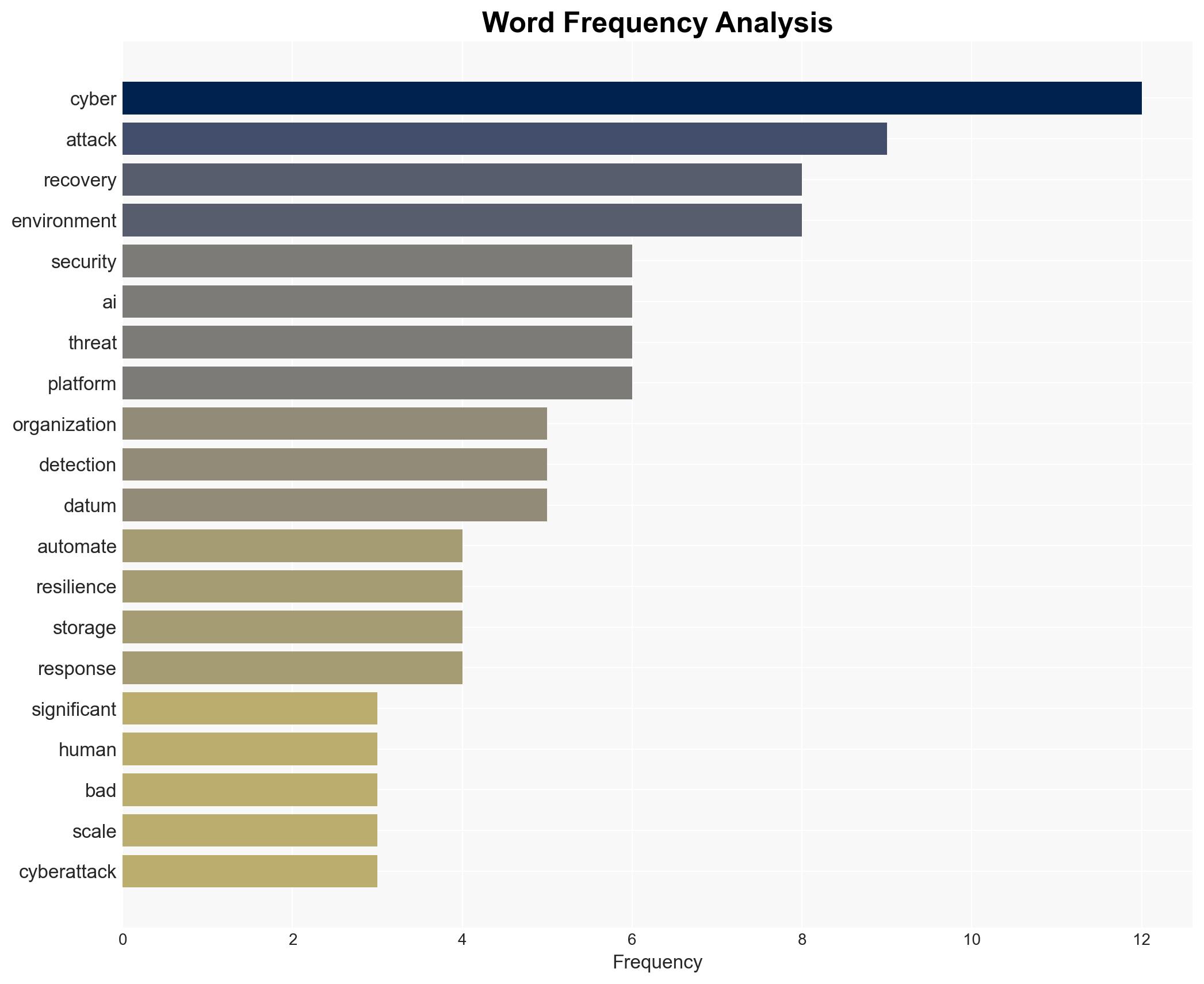
The integration of AI into cyberattack strategies is significantly increasing the frequency and sophistication of cyber threats, with the UK experiencing a notable rise in nationally significant attacks. The most likely hypothesis is that AI will continue to enhance the capabilities of cybercriminals, leading to a digital divide between organizations that adapt and those that remain vulnerable. This assessment is made with moderate confidence, given the current trends and expert warnings.
2. Competing Hypotheses
- Hypothesis A: AI advancements will lead to fully automated cyberattacks, increasing both the scale and speed of threats. This is supported by the reported increase in significant cyberattacks and expert warnings about AI’s role in cybercriminal activities. However, uncertainties remain about the full extent of AI’s capabilities and the timeline for widespread adoption.
- Hypothesis B: While AI will enhance cyberattack capabilities, existing cybersecurity measures and organizational adaptations will mitigate the overall impact. This hypothesis is less supported due to the current increase in attack frequency and the predicted digital divide, which suggests that many organizations are not yet prepared for AI-enhanced threats.
- Assessment: Hypothesis A is currently better supported due to the observed increase in cyberattacks and expert predictions about AI’s role in future threats. Key indicators that could shift this judgment include significant advancements in cybersecurity technologies or widespread adoption of cyber resilience strategies.
3. Key Assumptions and Red Flags
- Assumptions: AI technologies will continue to evolve and be accessible to cybercriminals; organizations will not uniformly adopt advanced cybersecurity measures; AI-driven attacks will be more effective than traditional methods.
- Information Gaps: Specific data on the effectiveness of AI-enhanced cybersecurity measures and the timeline for their adoption; detailed analysis of AI’s current capabilities in cyberattacks.
- Bias & Deception Risks: Potential bias in reporting from cybersecurity firms with vested interests; risk of exaggeration in AI capabilities by stakeholders to drive policy or investment.
4. Implications and Strategic Risks
The integration of AI into cyberattack strategies could lead to significant shifts in the cybersecurity landscape, affecting multiple domains.
- Political / Geopolitical: Increased cyber threats could strain international relations and lead to calls for new cybersecurity treaties or regulations.
- Security / Counter-Terrorism: Enhanced cyber capabilities could be leveraged by state and non-state actors, complicating counter-terrorism efforts.
- Cyber / Information Space: The digital divide may widen, with vulnerable organizations becoming prime targets for cybercriminals, potentially leading to increased data breaches and information warfare.
- Economic / Social: Economic instability could arise from increased cyberattacks on critical infrastructure, while social trust in digital systems may erode.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of AI-related cyber threats; enhance information sharing between organizations and cybersecurity agencies; conduct vulnerability assessments.
- Medium-Term Posture (1–12 months): Develop and implement comprehensive cyber resilience strategies; invest in AI-driven cybersecurity solutions; foster public-private partnerships for threat intelligence sharing.
- Scenario Outlook:
- Best Case: Rapid adaptation to AI threats leads to improved cybersecurity posture globally.
- Worst Case: Widespread AI-driven cyberattacks cause significant economic and social disruption.
- Most Likely: Continued increase in cyber threats with gradual adaptation by organizations, leading to a mixed security landscape.
6. Key Individuals and Entities
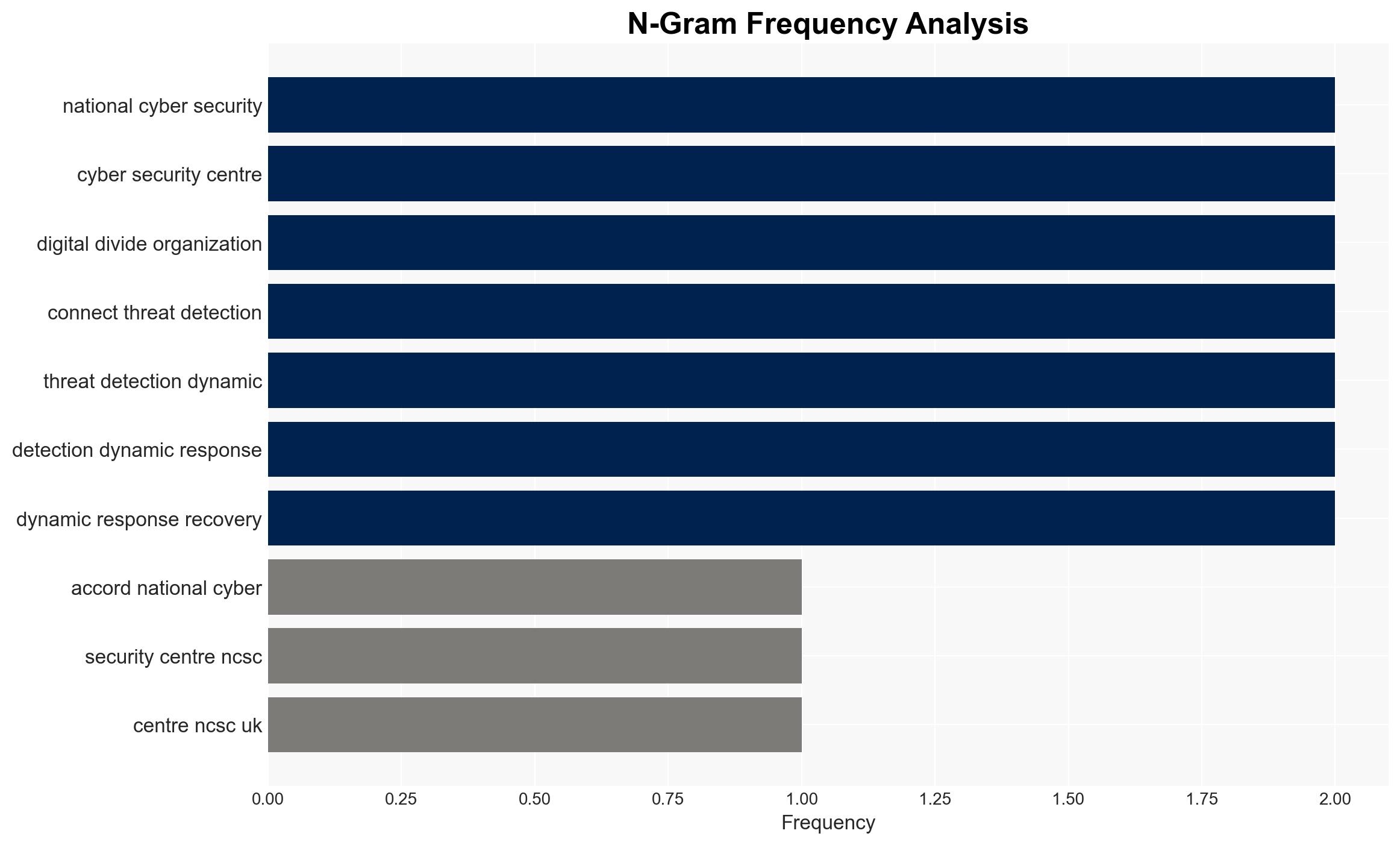
- National Cyber Security Centre (NCSC)
- Anthropic
- Claude family of large language models (LLMs)
- Cybercriminal organizations (not clearly identifiable from open sources in this snippet)
7. Thematic Tags
cybersecurity, AI-driven threats, cyber resilience, digital divide, cybercrime
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us