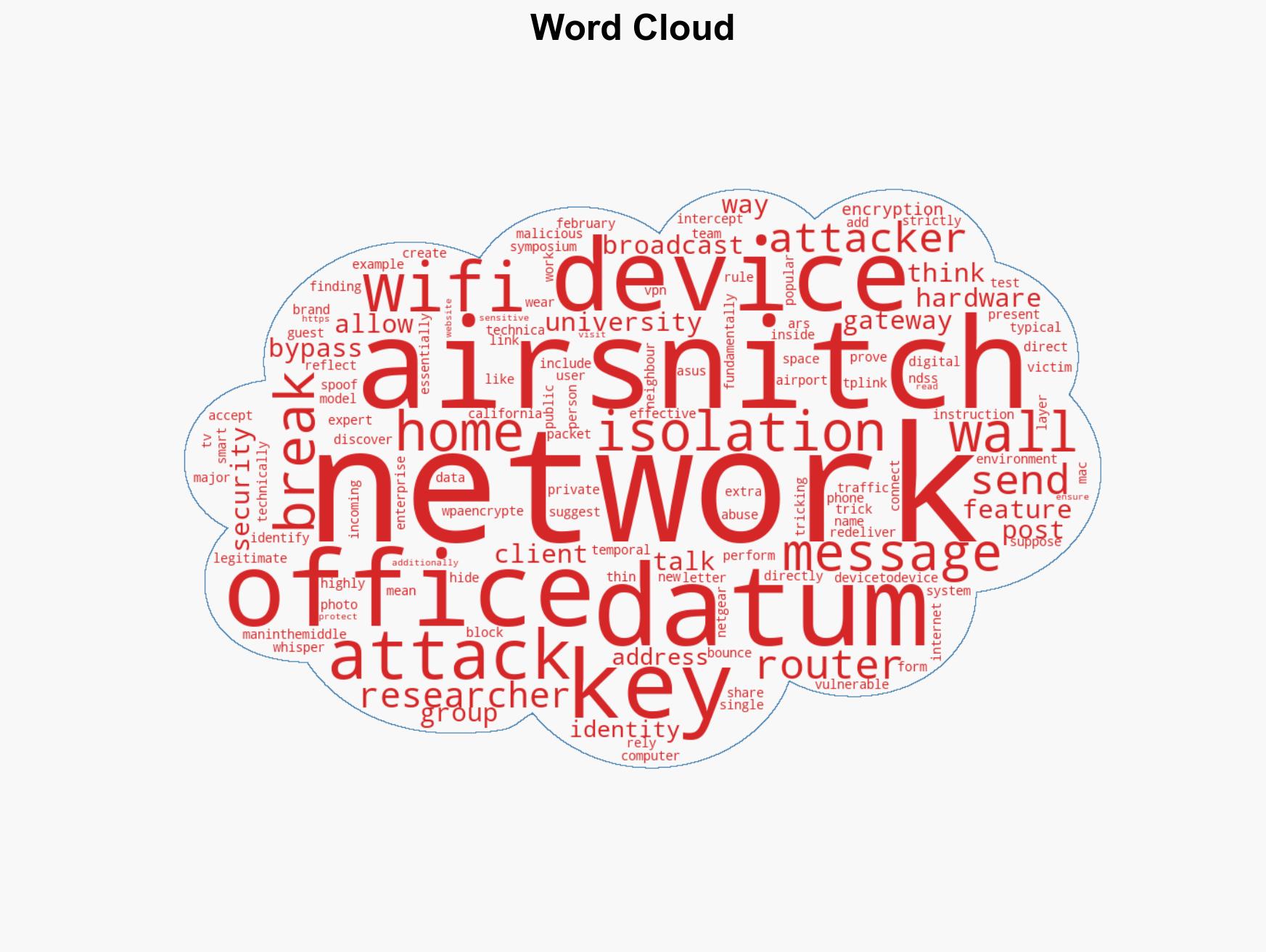
AirSnitch Attack Compromises WPA3 Security, Exposes Flaws in Client Isolation on Wi-Fi Networks
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: New AirSnitch Wi-Fi Attack Breaks WPA3 Encryption
1. BLUF (Bottom Line Up Front)
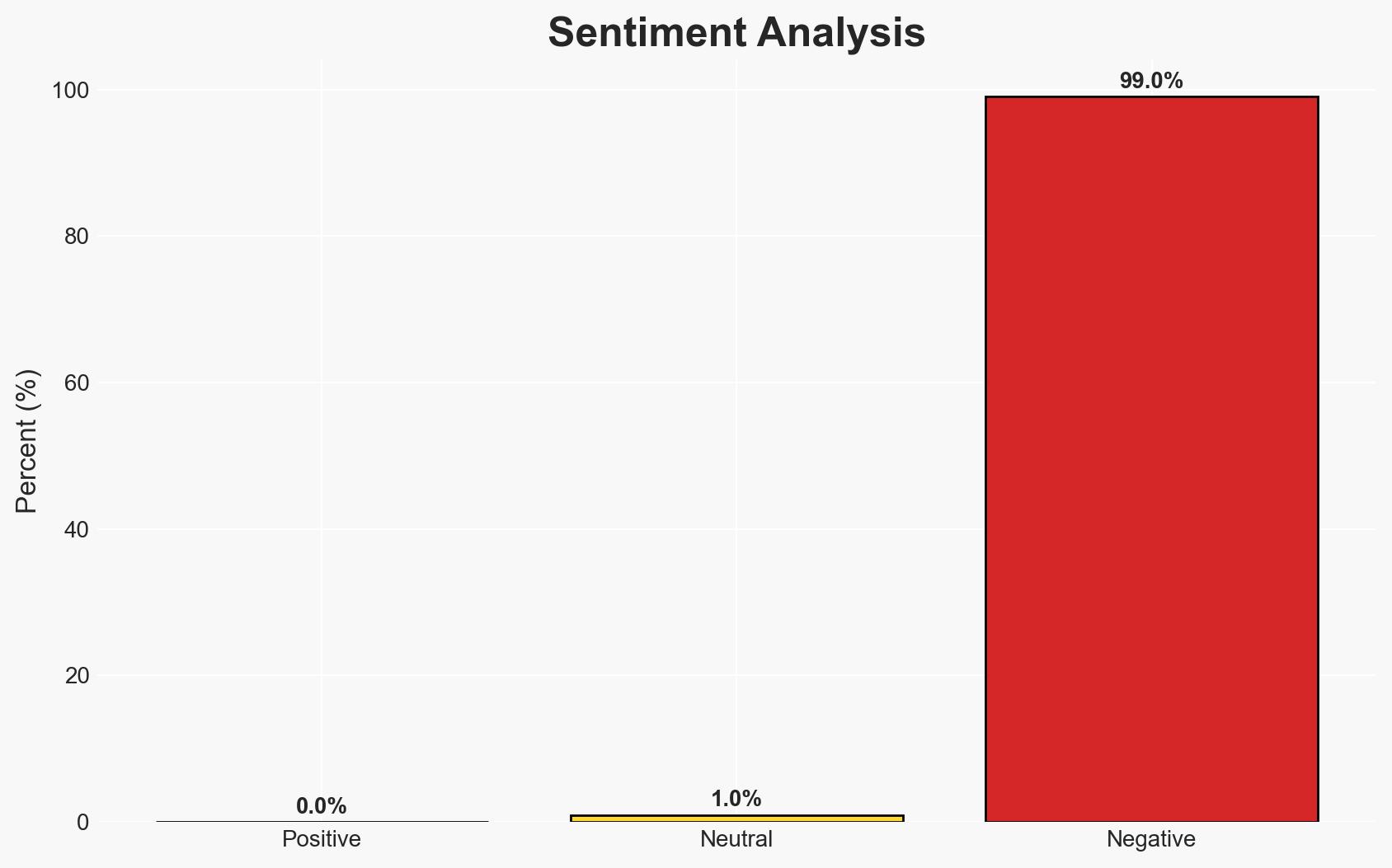
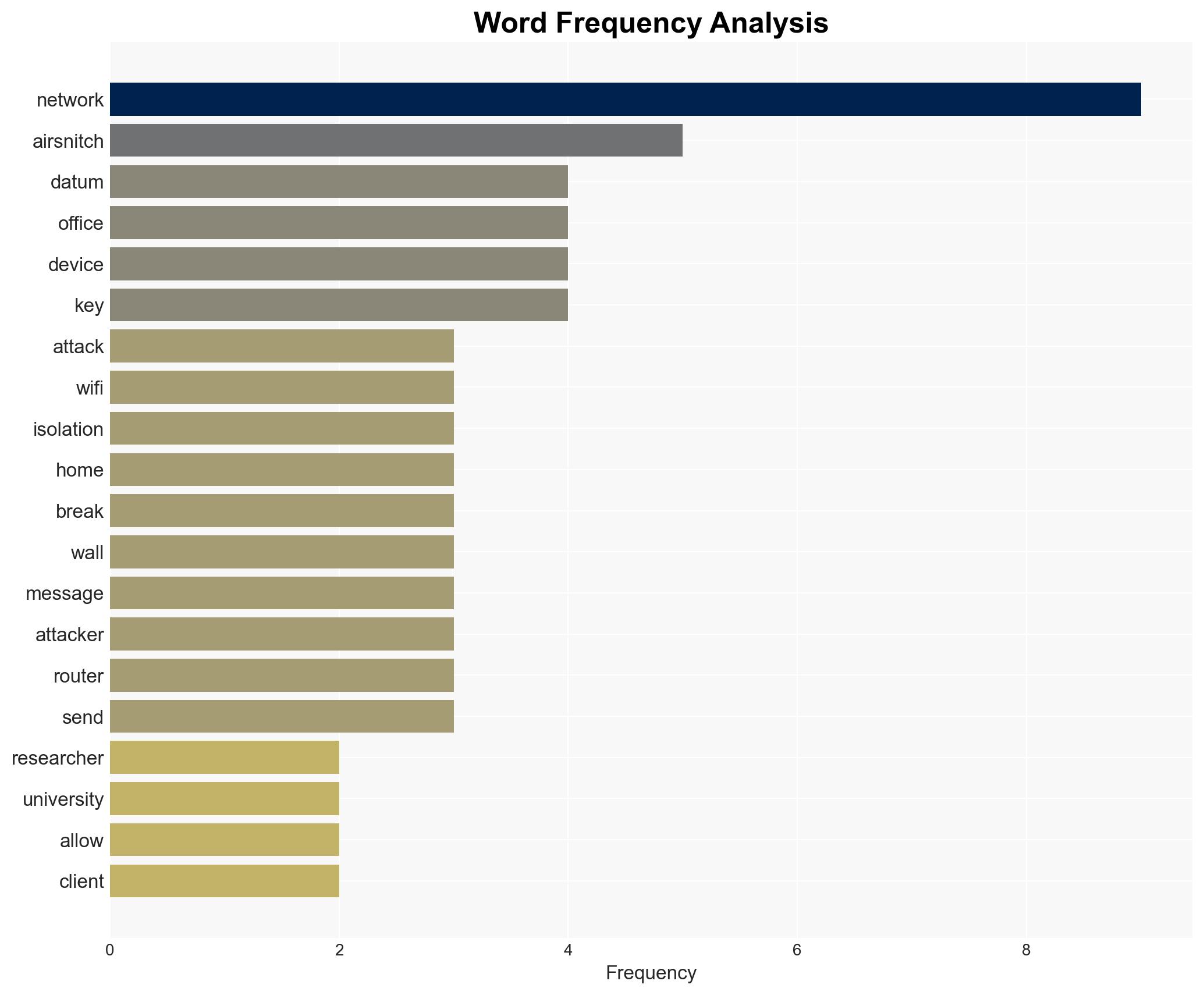
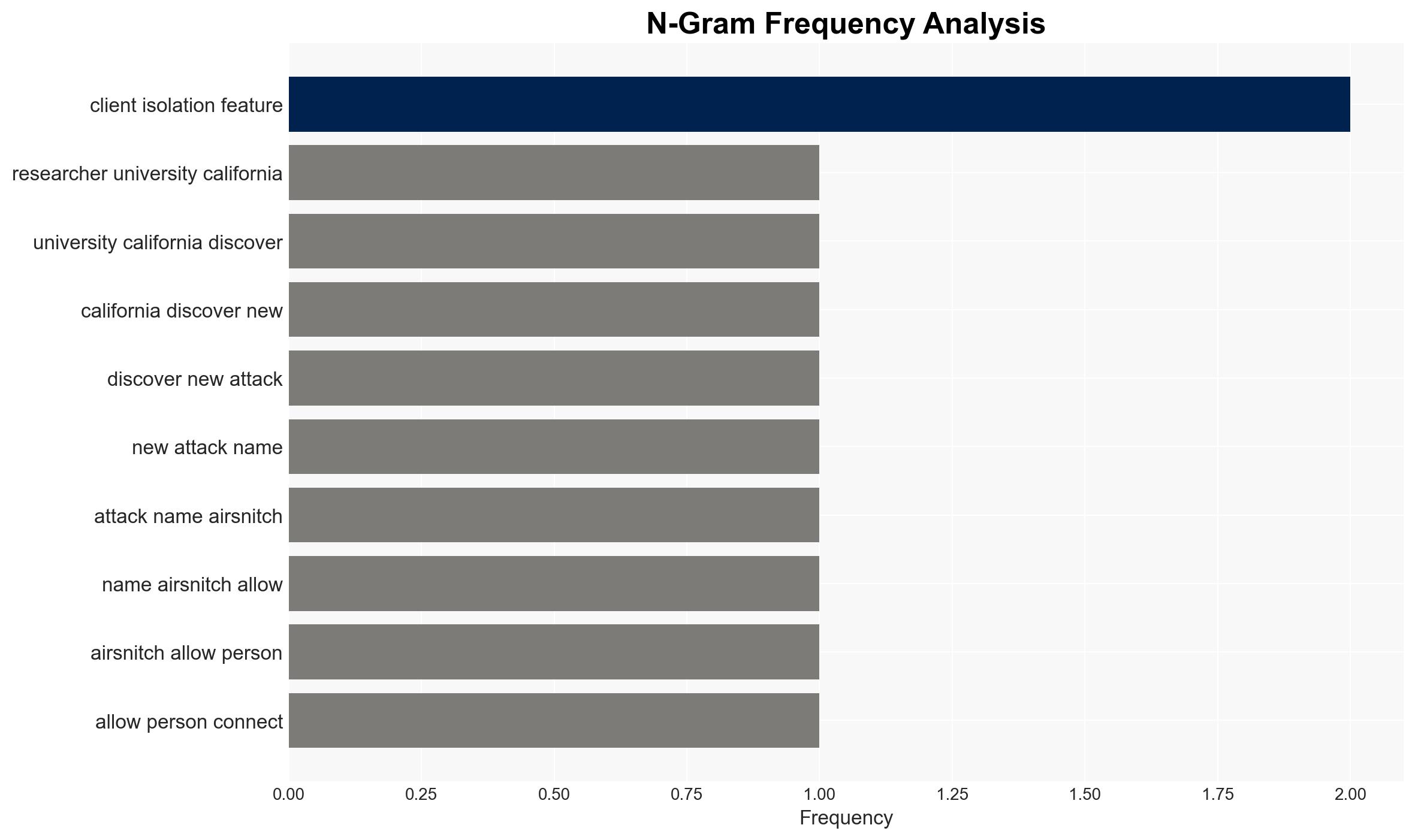
The AirSnitch attack compromises WPA3 encryption, undermining the client isolation feature in Wi-Fi networks, affecting both public and private sectors. This vulnerability poses significant risks to data security across various environments. We assess with moderate confidence that the attack could be exploited by malicious actors, necessitating immediate security enhancements.
2. Competing Hypotheses
- Hypothesis A: AirSnitch represents a significant new vulnerability in WPA3 encryption that can be widely exploited by cybercriminals. This is supported by the successful demonstration across multiple hardware brands and environments. Key uncertainties include the ease of exploitation by non-expert actors and the potential for rapid patch development by manufacturers.
- Hypothesis B: AirSnitch is a theoretical vulnerability with limited practical application due to potential mitigations like VPNs and HTTPS, and the technical expertise required to exploit it. This hypothesis is less supported given the widespread vulnerability across tested devices and environments.
- Assessment: Hypothesis A is currently better supported due to the demonstrated vulnerabilities across major hardware brands and environments. Indicators that could shift this judgment include rapid deployment of effective patches or evidence of limited exploitation in the wild.
3. Key Assumptions and Red Flags
- Assumptions: WPA3 is widely adopted across critical infrastructure; manufacturers will prioritize patch development; VPN and HTTPS usage is not universal.
- Information Gaps: Specific details on the technical complexity of executing AirSnitch; timeline for patch deployment by manufacturers; extent of current exploitation in the wild.
- Bias & Deception Risks: Potential bias from researchers emphasizing the severity of the vulnerability; lack of independent verification of the findings; possible underreporting of successful mitigations by manufacturers.
4. Implications and Strategic Risks
This vulnerability could lead to increased cyber espionage and data breaches if exploited by malicious actors, affecting both public and private sectors. The development may prompt a reevaluation of Wi-Fi security standards and practices.
- Political / Geopolitical: Potential for increased tensions if state actors are implicated in exploiting the vulnerability.
- Security / Counter-Terrorism: Enhanced threat environment as attackers could leverage this vulnerability for espionage or disruptive operations.
- Cyber / Information Space: Increased focus on Wi-Fi security protocols and potential acceleration of alternative security technologies.
- Economic / Social: Potential economic impact on manufacturers facing liability or reputational damage; increased demand for cybersecurity solutions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage the use of VPNs and HTTPS; initiate monitoring for exploitation attempts; engage with manufacturers for patch timelines.
- Medium-Term Posture (1–12 months): Develop resilience measures such as enhanced network monitoring; foster partnerships with cybersecurity firms; invest in research for next-generation encryption standards.
- Scenario Outlook:
- Best Case: Rapid patch deployment mitigates the threat; minimal exploitation occurs.
- Worst Case: Widespread exploitation leads to significant data breaches and economic damage.
- Most-Likely: Gradual patching reduces risk over time; some exploitation occurs, primarily targeting high-value networks.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, Wi-Fi vulnerability, WPA3 encryption, data breach, cyber espionage, network security, encryption standards
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us