AI’s Role in Cyberattacks Grows as Threat Actors Enhance Strategies and Execution Speed
Published on: 2026-04-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Threat actor abuse of AI accelerates from tool to cyberattack surface
1. BLUF (Bottom Line Up Front)
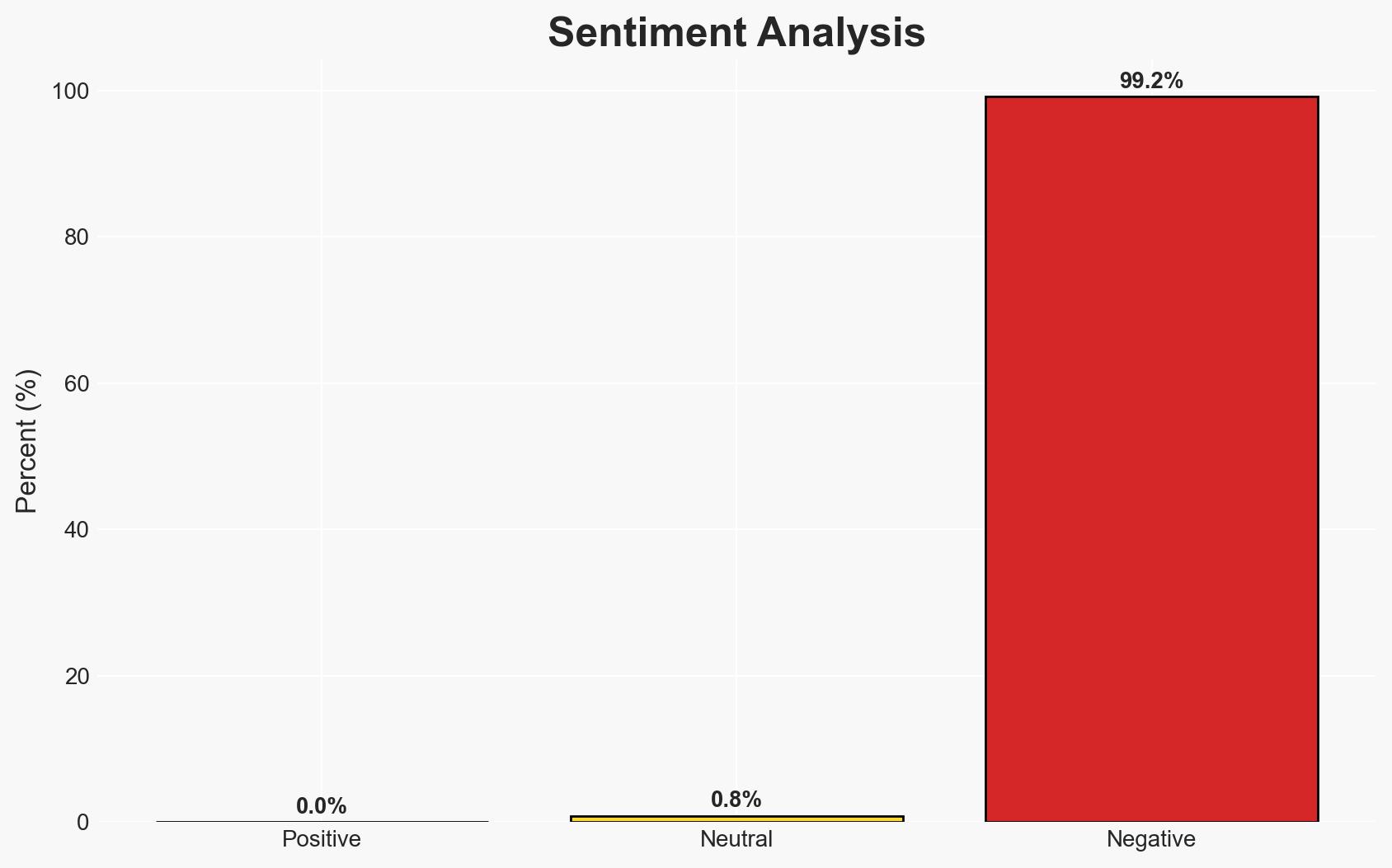
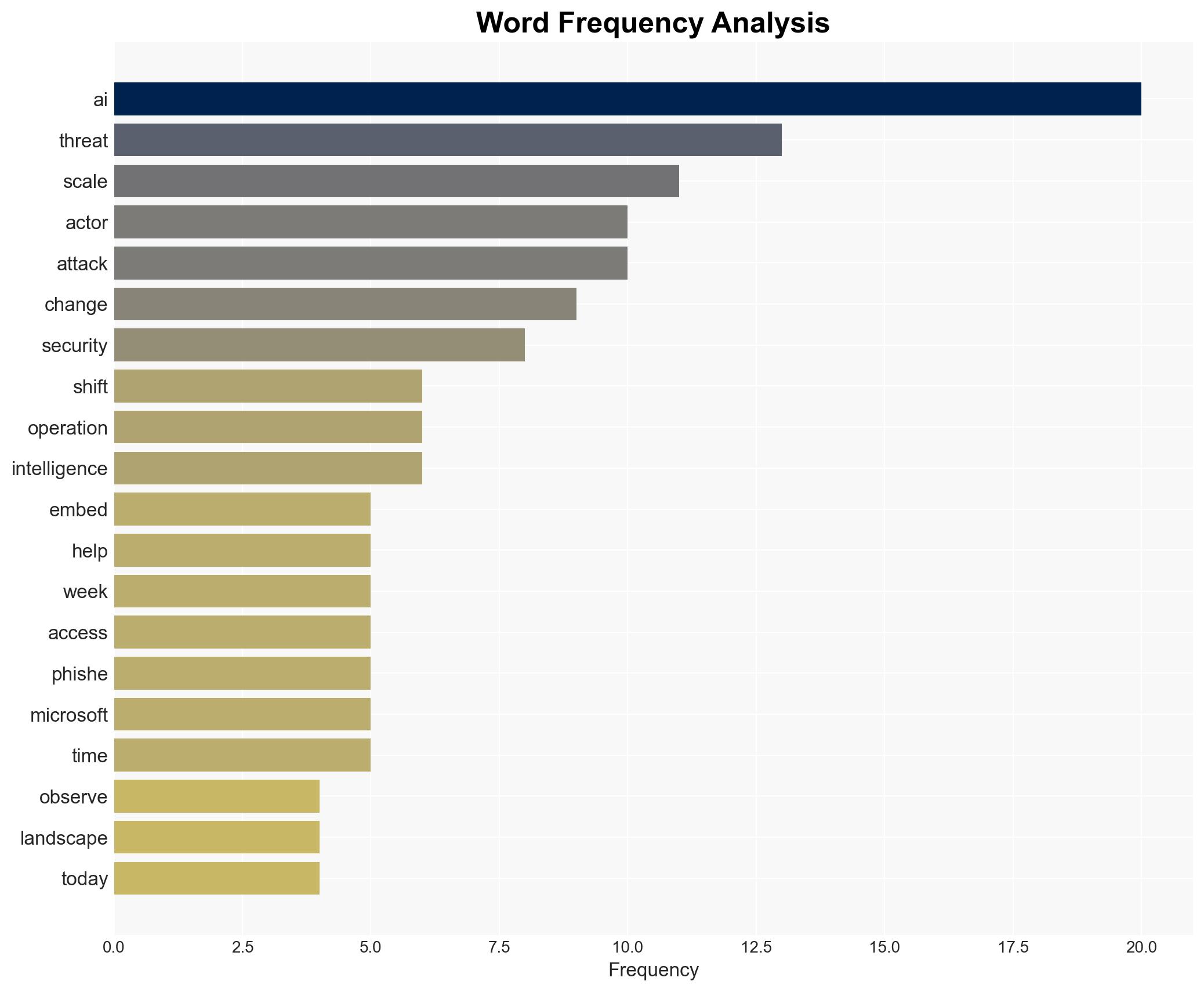
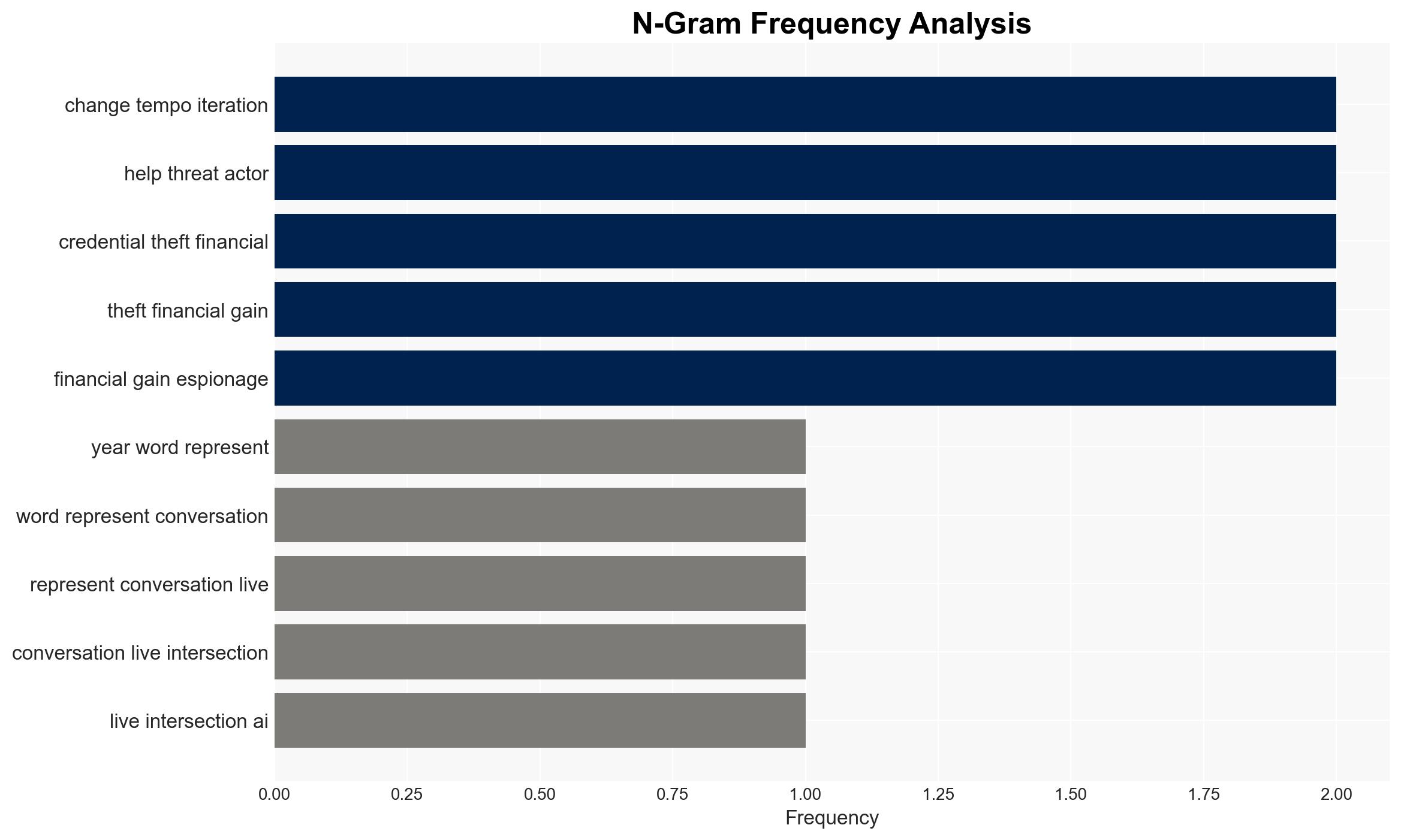
Threat actors are increasingly integrating AI into cyberattack methodologies, enhancing the precision and effectiveness of operations, particularly in phishing campaigns. This trend poses a significant risk to global cybersecurity, with a notable impact on organizations in the United States, United Kingdom, Israel, and Germany. The most likely hypothesis is that AI will continue to be used to refine existing attack vectors rather than create new ones. Overall confidence in this assessment is moderate, given the evolving nature of AI technologies and threat actor capabilities.
2. Competing Hypotheses
- Hypothesis A: AI is primarily being used to enhance existing cyberattack techniques, improving efficiency and effectiveness. Supporting evidence includes the increased click-through rates in AI-enhanced phishing campaigns. Key uncertainties involve the potential for AI to autonomously conduct attacks without human intervention.
- Hypothesis B: AI will lead to the development of entirely new cyberattack methodologies, fundamentally altering the threat landscape. While AI’s current use is largely in enhancing existing methods, there is limited evidence of entirely new techniques emerging. However, the rapid pace of AI development could support this hypothesis in the future.
- Assessment: Hypothesis A is currently better supported due to concrete evidence of AI improving existing techniques. Indicators that could shift this judgment include the emergence of autonomous AI-driven attacks or novel methodologies directly attributable to AI innovations.
3. Key Assumptions and Red Flags
- Assumptions: AI will continue to require human oversight in cyberattacks; AI development will proceed at a similar pace globally; threat actors will prioritize efficiency and effectiveness over novelty.
- Information Gaps: Specific details on AI capabilities in autonomous operations; comprehensive data on AI use by non-state actors; insights into defensive AI measures being developed.
- Bias & Deception Risks: Potential overestimation of AI capabilities due to media hype; reliance on self-reported data from security conferences; potential manipulation of AI-related threat data by state actors.
4. Implications and Strategic Risks
The integration of AI into cyberattack strategies is likely to evolve, potentially increasing the sophistication and impact of cyber threats. This development could interact with broader geopolitical tensions and influence international cybersecurity policies.
- Political / Geopolitical: Increased cyber tensions could lead to escalated geopolitical conflicts, particularly among major AI-developing nations.
- Security / Counter-Terrorism: Enhanced cyber capabilities may complicate counter-terrorism efforts, requiring updated strategies and technologies.
- Cyber / Information Space: AI-driven attacks could challenge existing cybersecurity frameworks, necessitating advanced defensive measures and international cooperation.
- Economic / Social: Increased cyber threats could disrupt economic activities and undermine public trust in digital systems, impacting social cohesion.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of AI-related cyber threats; increase awareness and training on AI-enhanced phishing techniques; collaborate with international partners to share threat intelligence.
- Medium-Term Posture (1–12 months): Develop and deploy AI-based defensive measures; foster public-private partnerships for cybersecurity innovation; invest in research on AI’s role in cyber defense.
- Scenario Outlook:
- Best: AI is effectively integrated into defensive strategies, neutralizing enhanced threats.
- Worst: AI-driven attacks overwhelm current defenses, leading to significant economic and security disruptions.
- Most-Likely: AI continues to enhance existing attack vectors, requiring ongoing adaptation of defensive measures.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
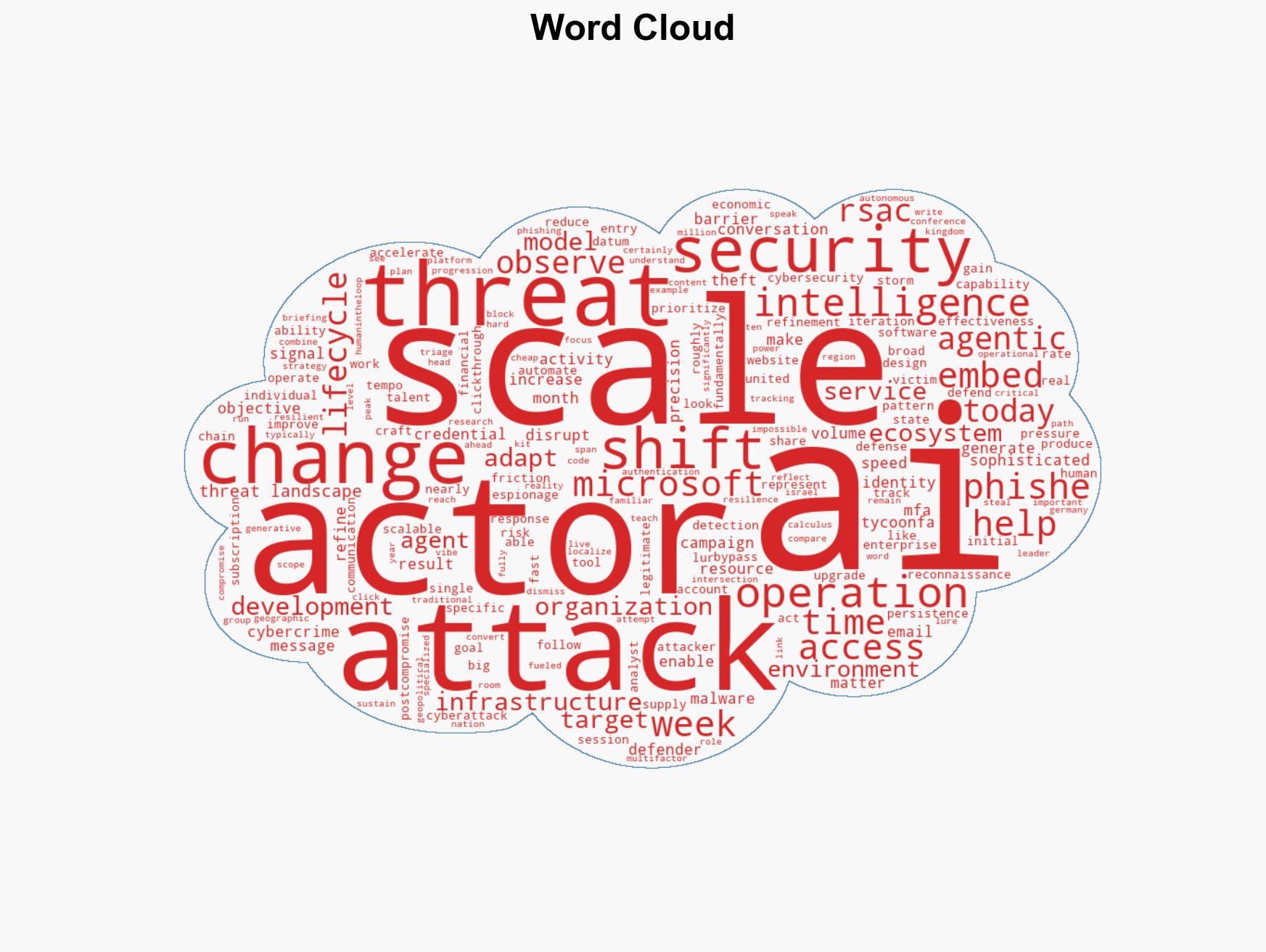
cybersecurity, AI integration, phishing, cyber defense, threat actors, geopolitical tensions, cyber innovation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us