Amateur Hacker Leverages Russian Bulletproof Hosting Server to Spread Malware – Infosecurity Magazine
Published on: 2025-04-03
Intelligence Report: Amateur Hacker Leverages Russian Bulletproof Hosting Server to Spread Malware – Infosecurity Magazine
1. BLUF (Bottom Line Up Front)
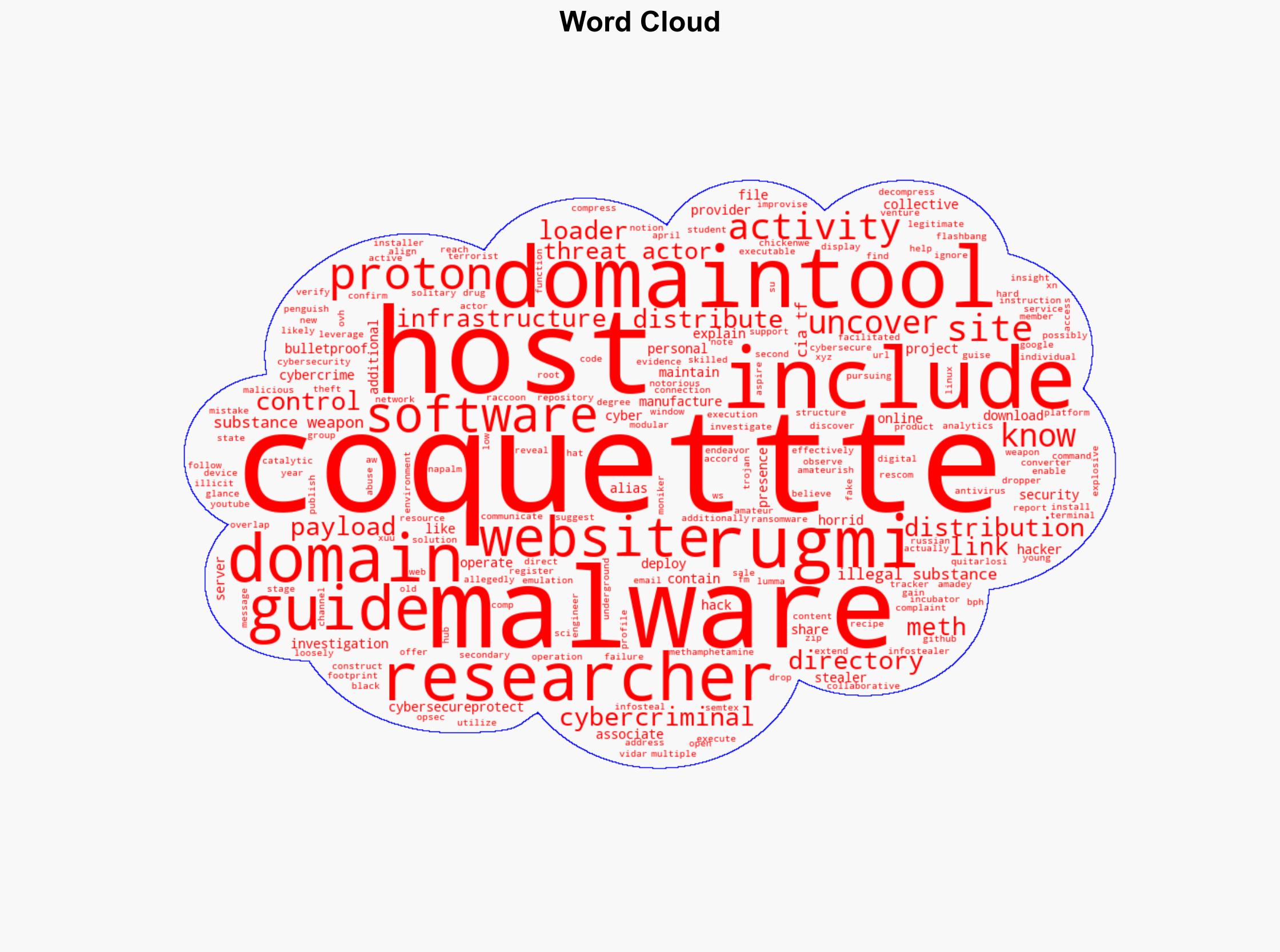
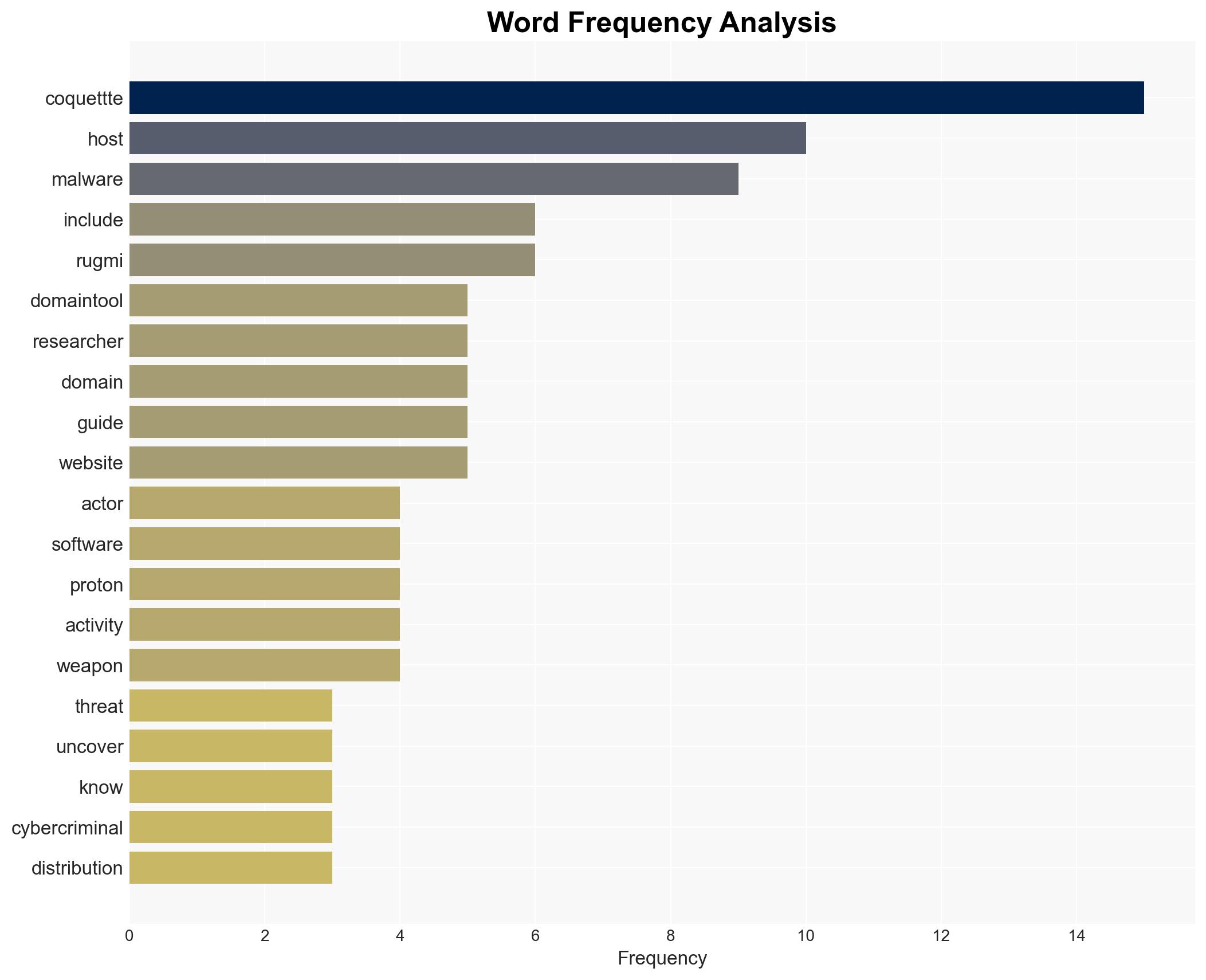
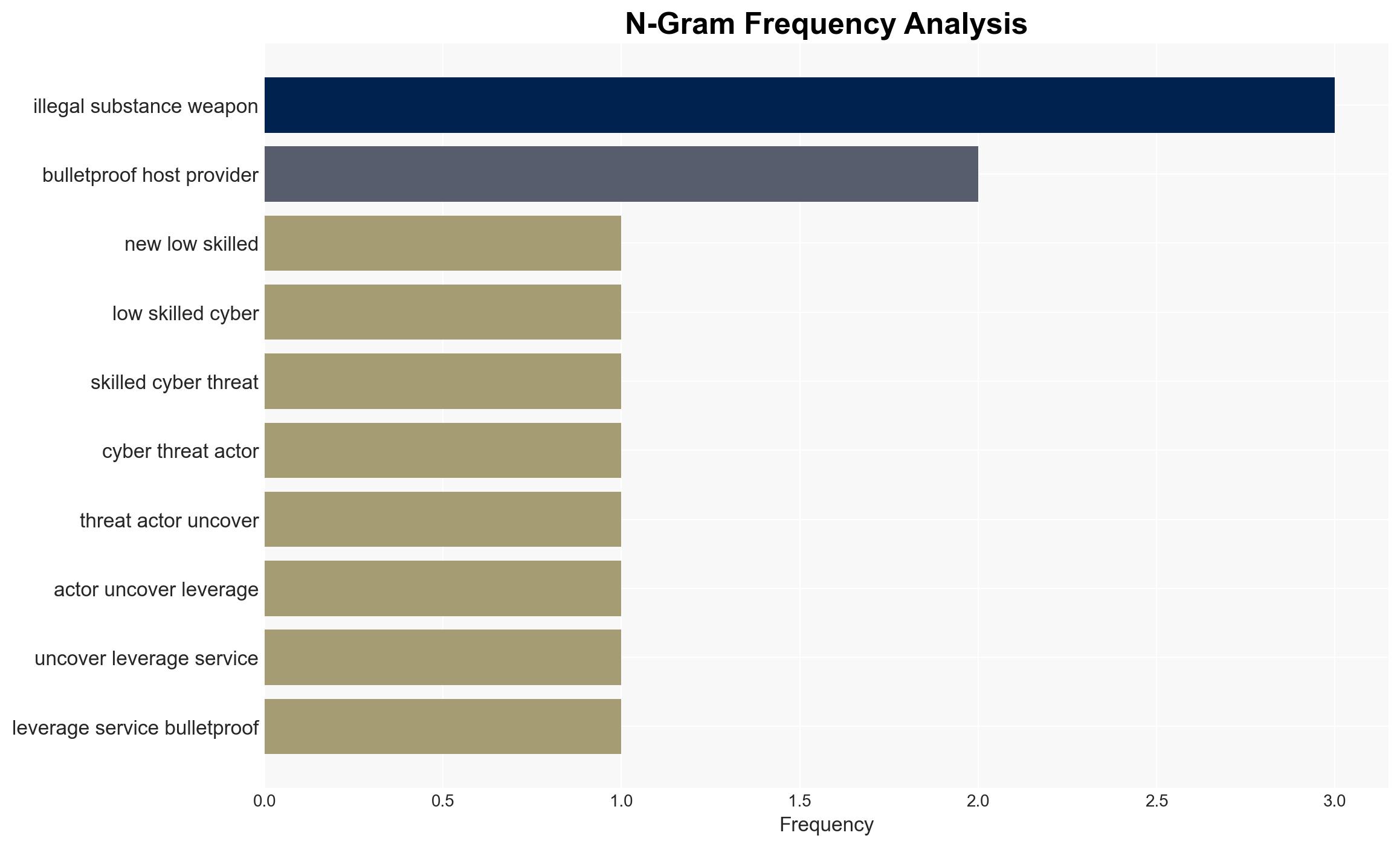
A new low-skilled cyber threat actor, known by the moniker coquettte, has been identified leveraging a Russian bulletproof hosting provider, Proton, to distribute malware under the guise of legitimate software. This actor’s activities include malware distribution and the sale of guides for manufacturing illegal substances and weapons. The use of bulletproof hosting services allows coquettte to operate with minimal interference from law enforcement, posing a significant threat to cybersecurity and public safety.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
Coquettte has been identified as an amateur hacker exploiting the services of Proton, a notorious bulletproof hosting provider, to deploy malware disguised as legitimate cybersecurity software. The malicious software, known as Rugmi, acts as a modular malware loader capable of deploying secondary payloads such as infostealers, trojans, and ransomware. The investigation revealed that coquettte operates a fake cybersecurity product site, CyberSecureProtect, which distributes the Rugmi malware loader. The actor’s operational security failures allowed researchers to access the website’s web directory, uncovering the malware distribution mechanisms.
3. Implications and Strategic Risks
The activities of coquettte pose several strategic risks, including:
- Increased cybercrime activities due to the availability of bulletproof hosting services that ignore abuse complaints.
- Potential threats to national security and public safety from the distribution of guides for manufacturing illegal substances and weapons.
- Economic impacts on businesses and individuals affected by the malware distributed through coquettte‘s operations.
4. Recommendations and Outlook
Recommendations:
- Enhance international cooperation to regulate and shut down bulletproof hosting providers like Proton.
- Increase public awareness and education on identifying and avoiding fake cybersecurity products.
- Implement stricter cybersecurity measures and monitoring to detect and mitigate malware distribution activities.
Outlook:
Best-case scenario: Successful international collaboration leads to the shutdown of bulletproof hosting providers, significantly reducing cybercrime activities.
Worst-case scenario: Continued proliferation of bulletproof hosting services results in increased cyber threats and public safety risks.
Most likely scenario: Incremental improvements in cybersecurity measures and awareness reduce the impact of coquettte‘s activities but do not eliminate the threat entirely.
5. Key Individuals and Entities
The report mentions significant individuals and organizations:
- Coquettte – The amateur hacker responsible for the malware distribution activities.
- Proton – The Russian bulletproof hosting provider enabling coquettte‘s operations.
- CyberSecureProtect – The fake cybersecurity product site used to distribute malware.
- Rugmi – The modular malware loader deployed by coquettte.