Apple confirms Lockdown Mode has successfully thwarted all hacking attempts on its devices.
Published on: 2026-03-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Apple products using Lockdown Mode have never been hacked company confirms
1. BLUF (Bottom Line Up Front)
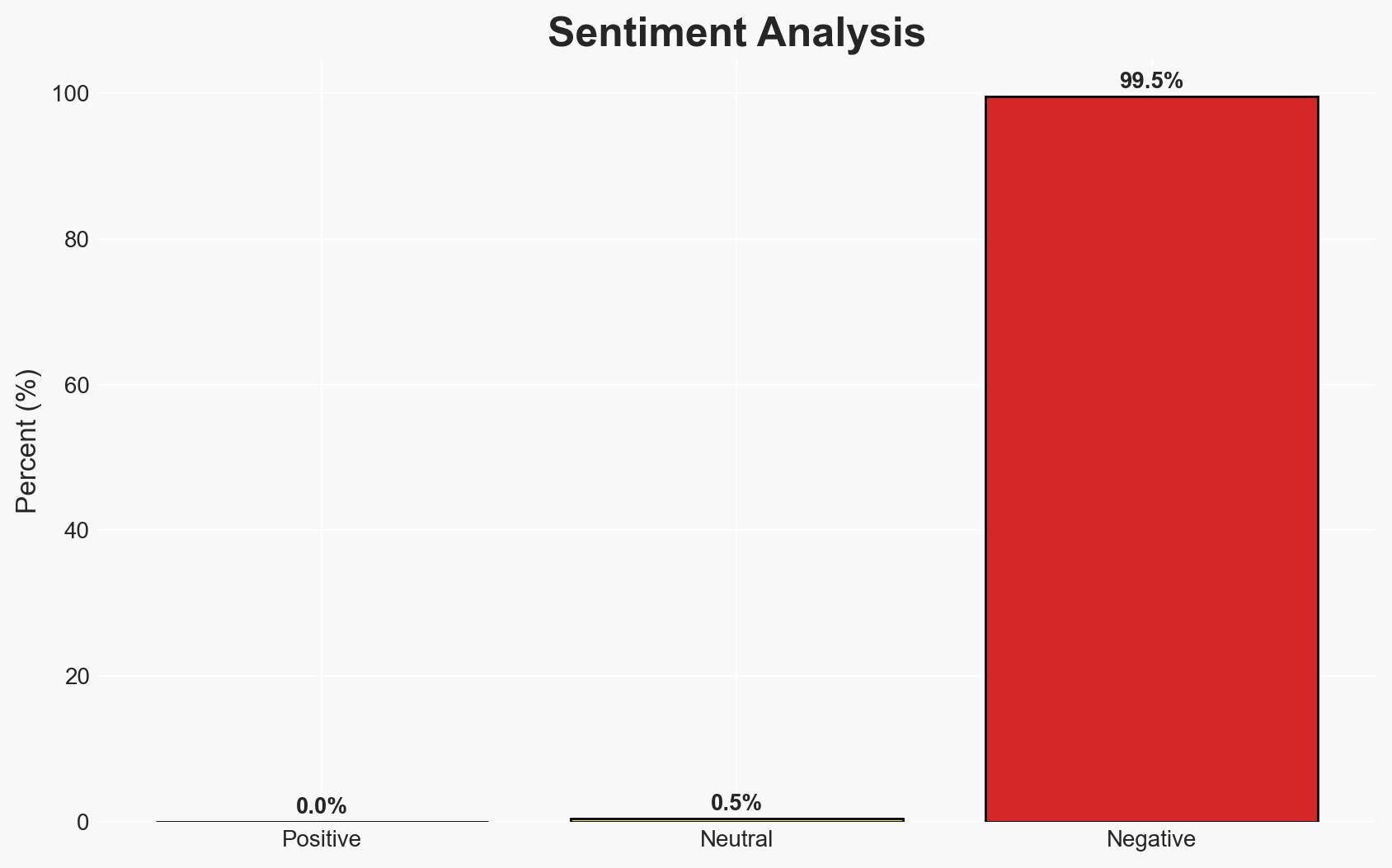
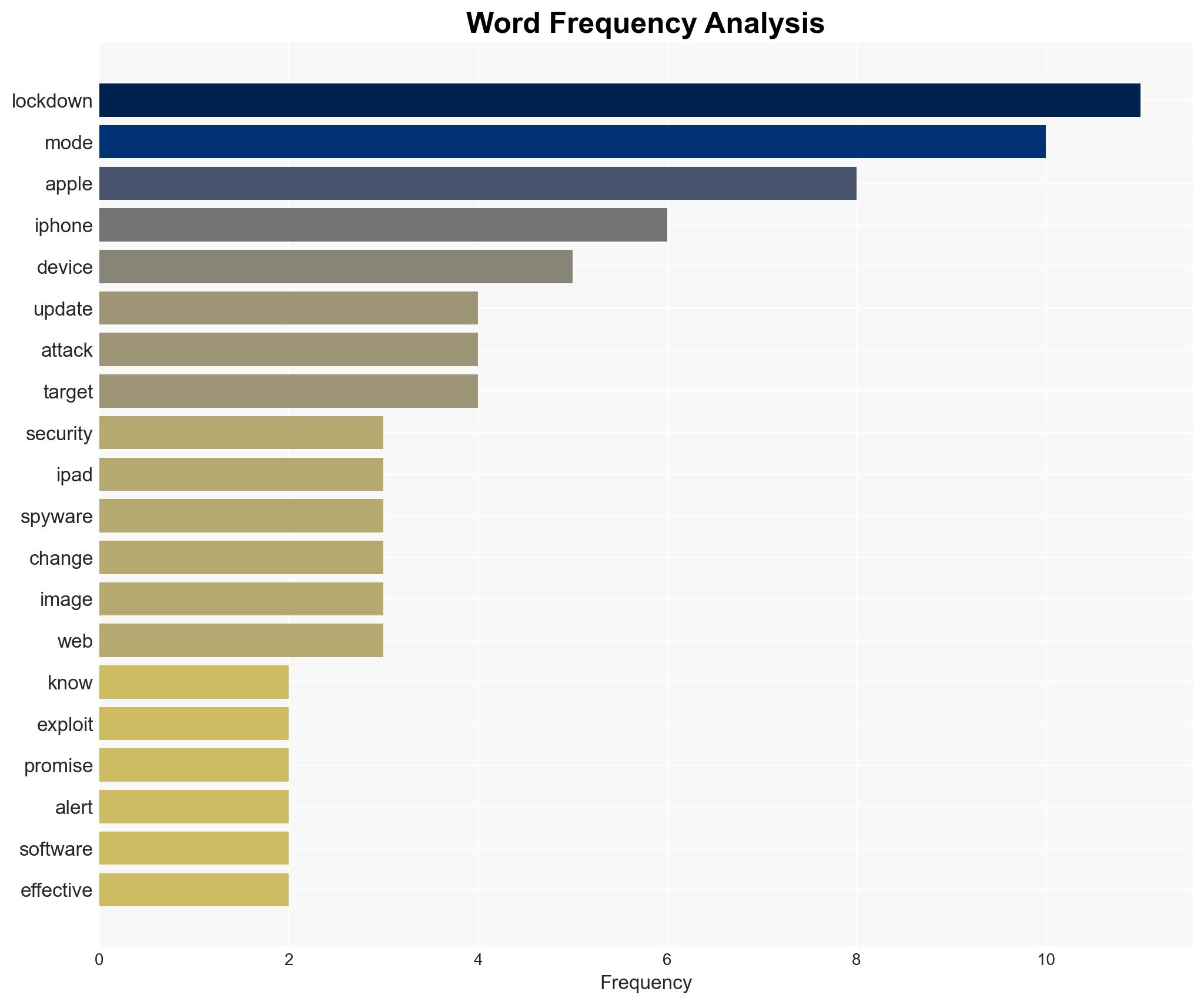
Apple’s Lockdown Mode has reportedly not been breached by any known cyber attacks, suggesting its effectiveness against sophisticated threats. This development primarily affects high-risk individuals targeted by advanced spyware. Overall, there is moderate confidence in the security claims due to limited independent verification and potential information gaps.
2. Competing Hypotheses
- Hypothesis A: Apple’s Lockdown Mode is genuinely effective in preventing sophisticated cyber attacks, as evidenced by the absence of reported breaches. However, this relies heavily on Apple’s internal reporting, which may not capture all incidents or attempted breaches.
- Hypothesis B: The absence of reported breaches may be due to underreporting or lack of detection rather than the inherent effectiveness of Lockdown Mode. This hypothesis is supported by the potential for undisclosed vulnerabilities and the complexity of confirming non-events.
- Assessment: Hypothesis A is currently better supported due to Apple’s public statement and the specific design of Lockdown Mode to counter advanced threats. However, increased transparency and independent verification could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Apple’s reporting is accurate and comprehensive; Lockdown Mode is used correctly by targeted individuals; no undisclosed vulnerabilities exist in Lockdown Mode; attackers have attempted to breach devices with Lockdown Mode enabled.
- Information Gaps: Independent verification of Apple’s claims; detailed data on attempted breaches; understanding of attacker strategies against Lockdown Mode.
- Bias & Deception Risks: Potential corporate bias in Apple’s reporting; lack of independent oversight may lead to overconfidence in security claims.
4. Implications and Strategic Risks
The effectiveness of Lockdown Mode could influence the broader cybersecurity landscape, particularly for high-risk individuals and organizations. Its success or failure may impact public trust in tech companies’ security measures.
- Political / Geopolitical: Increased pressure on governments to regulate or endorse similar security measures; potential diplomatic tensions if state actors are implicated in attacks.
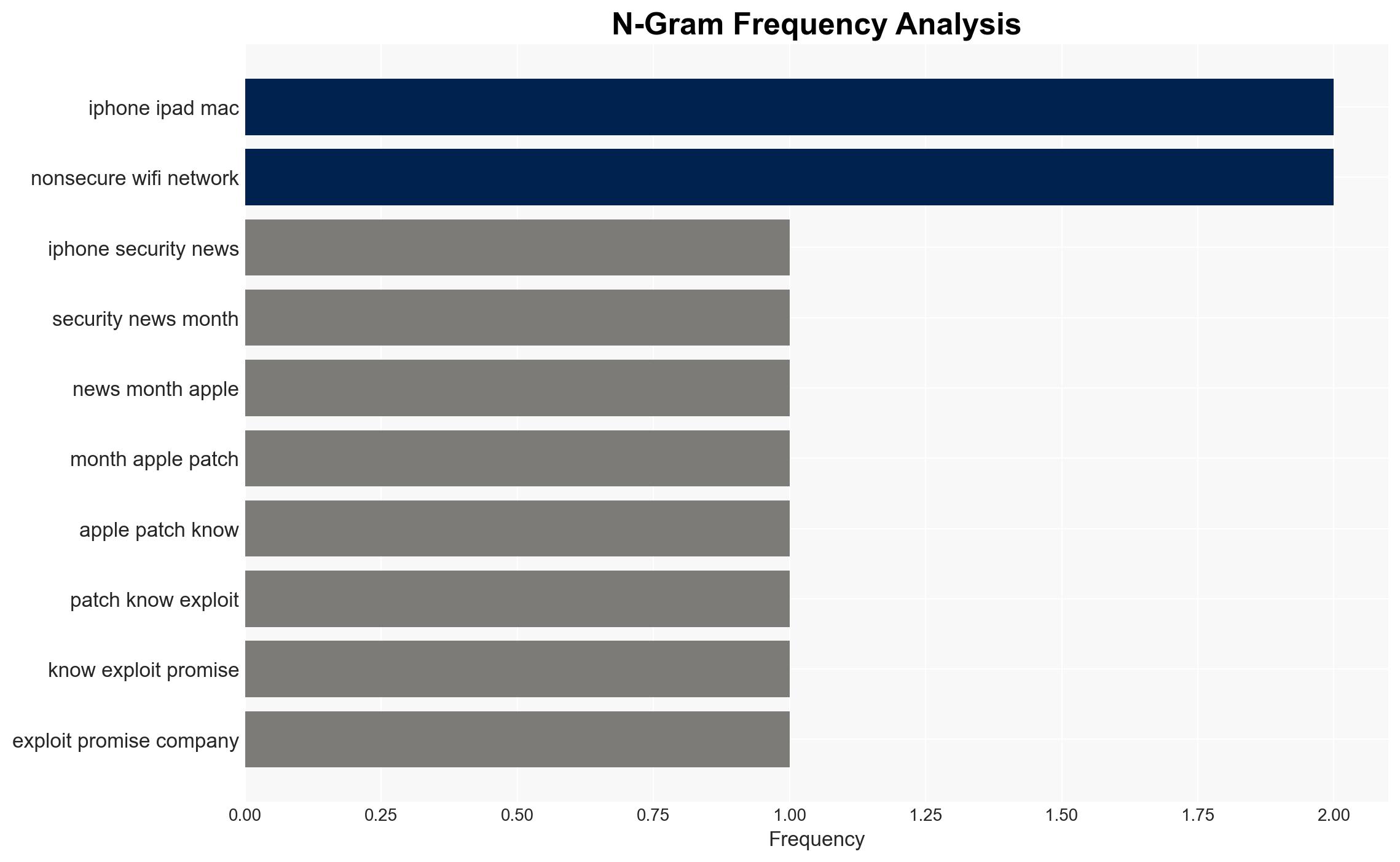
- Security / Counter-Terrorism: Enhanced protection for high-profile targets could shift threat actors’ focus to less secure platforms or methods.
- Cyber / Information Space: Potential escalation in cyber capabilities as adversaries seek to overcome Lockdown Mode; increased emphasis on developing similar technologies by competitors.
- Economic / Social: Strengthened consumer trust in Apple products may influence market dynamics; potential social implications if high-risk individuals are better protected.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage independent security audits of Lockdown Mode; monitor for any emerging reports of breaches; engage with cybersecurity experts to validate claims.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to enhance security measures; invest in research to counteract potential vulnerabilities; promote awareness among high-risk users.
- Scenario Outlook:
- Best: Lockdown Mode remains unbreached, leading to widespread adoption and improved security standards.
- Worst: Undetected vulnerabilities are exploited, undermining trust in Apple’s security measures.
- Most-Likely: Continued effectiveness with occasional minor breaches, prompting iterative improvements and increased scrutiny.
6. Key Individuals and Entities
- Apple Inc.
- Sarah O’Rourke (Apple spokesperson)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
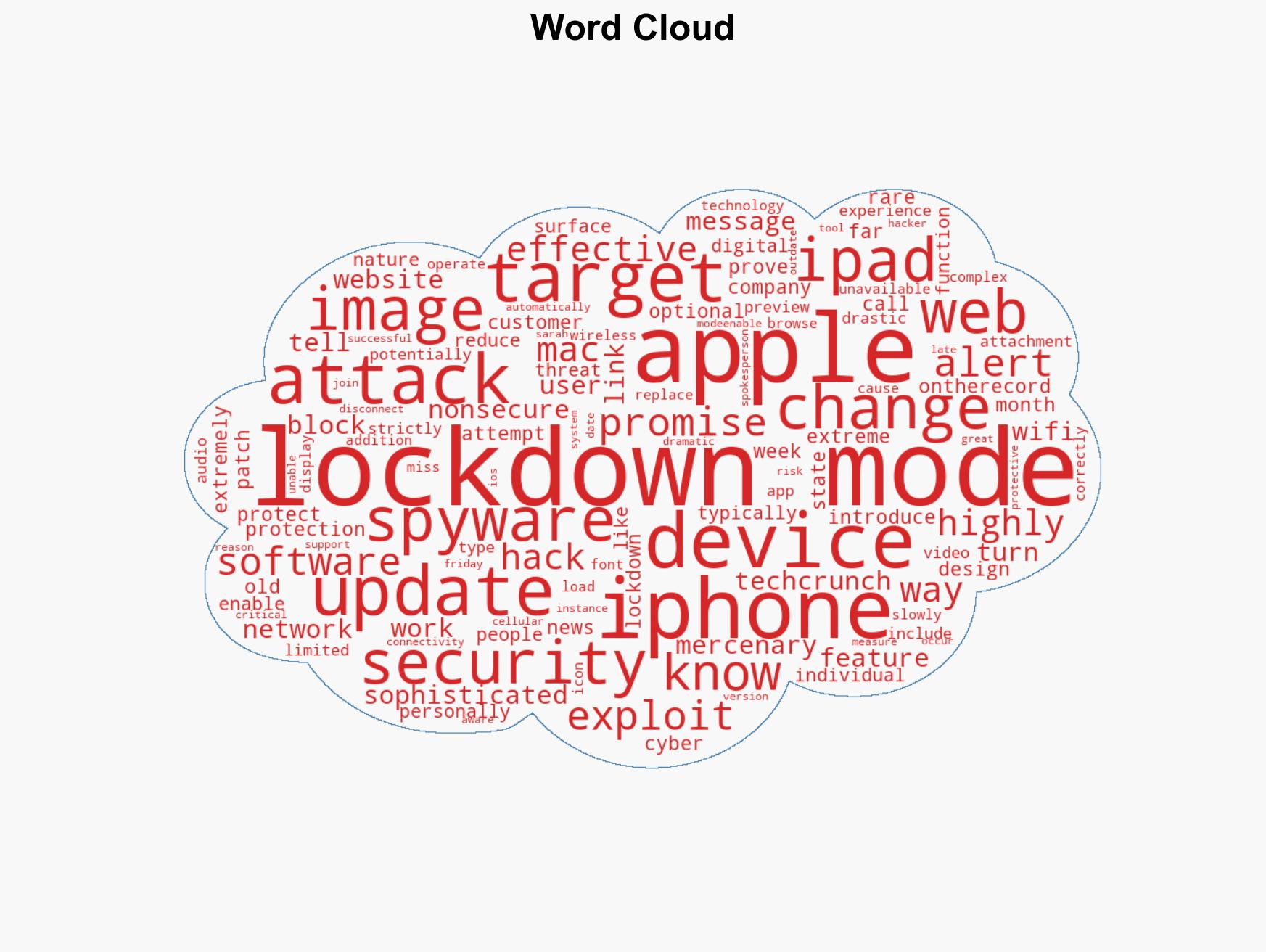
cybersecurity, Apple, Lockdown Mode, spyware, high-risk individuals, tech industry, digital threats
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us