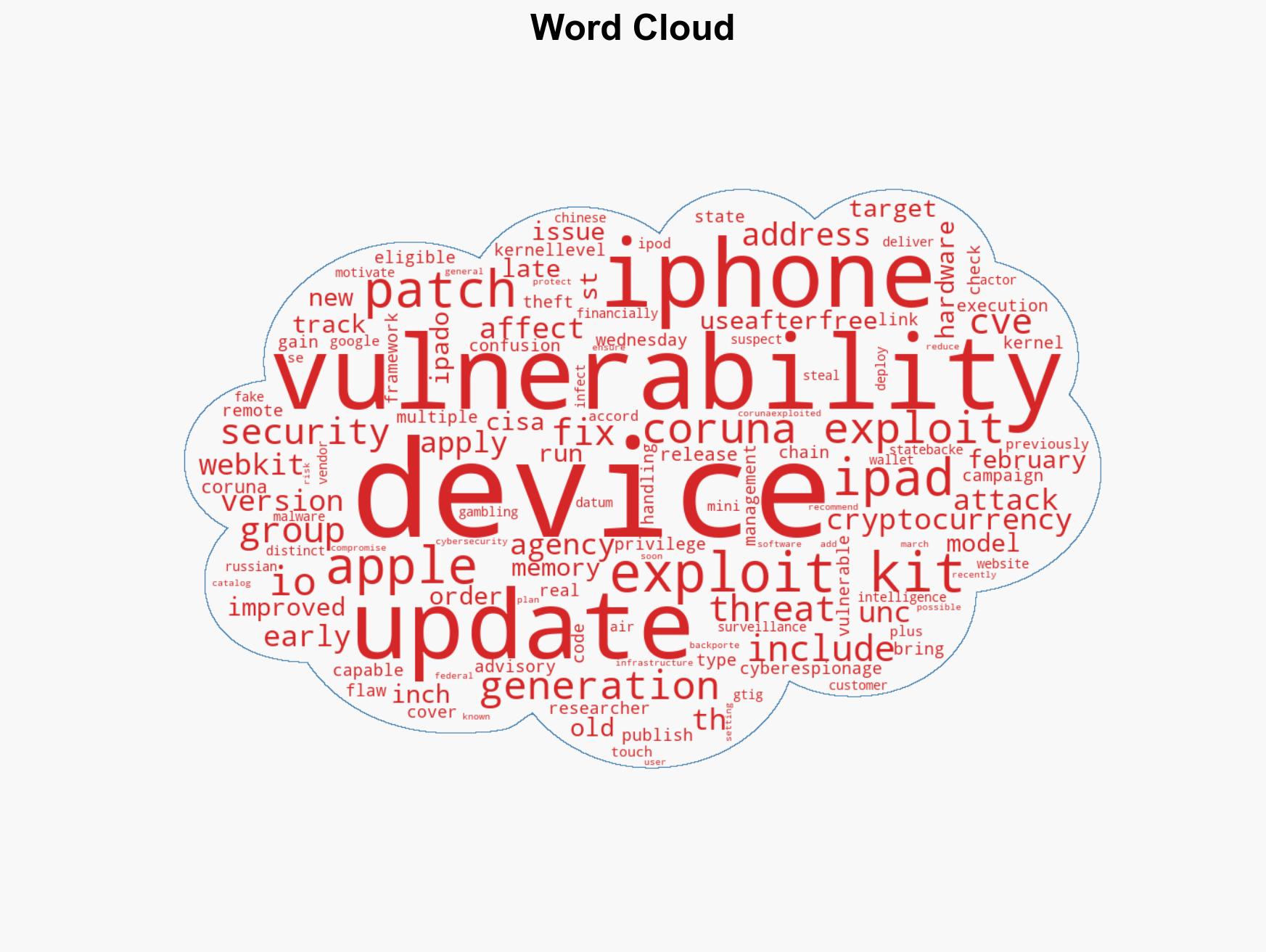
Apple Issues Security Patches for Legacy iPhones and iPads to Combat Coruna Exploit Vulnerabilities
Published on: 2026-03-13
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Apple Releases Security Update for Older iPhones and iPads After Coruna Exploit
1. BLUF (Bottom Line Up Front)
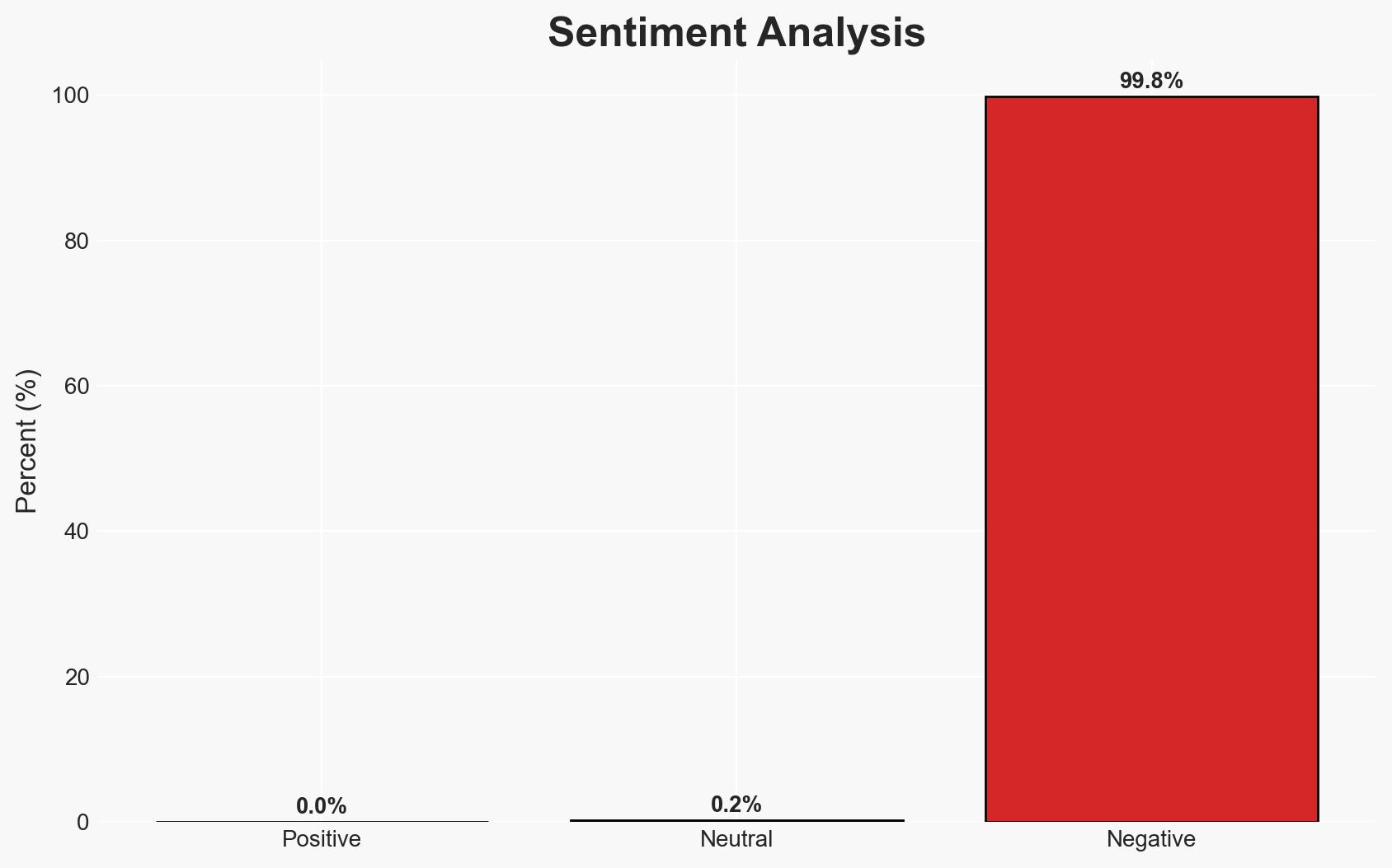
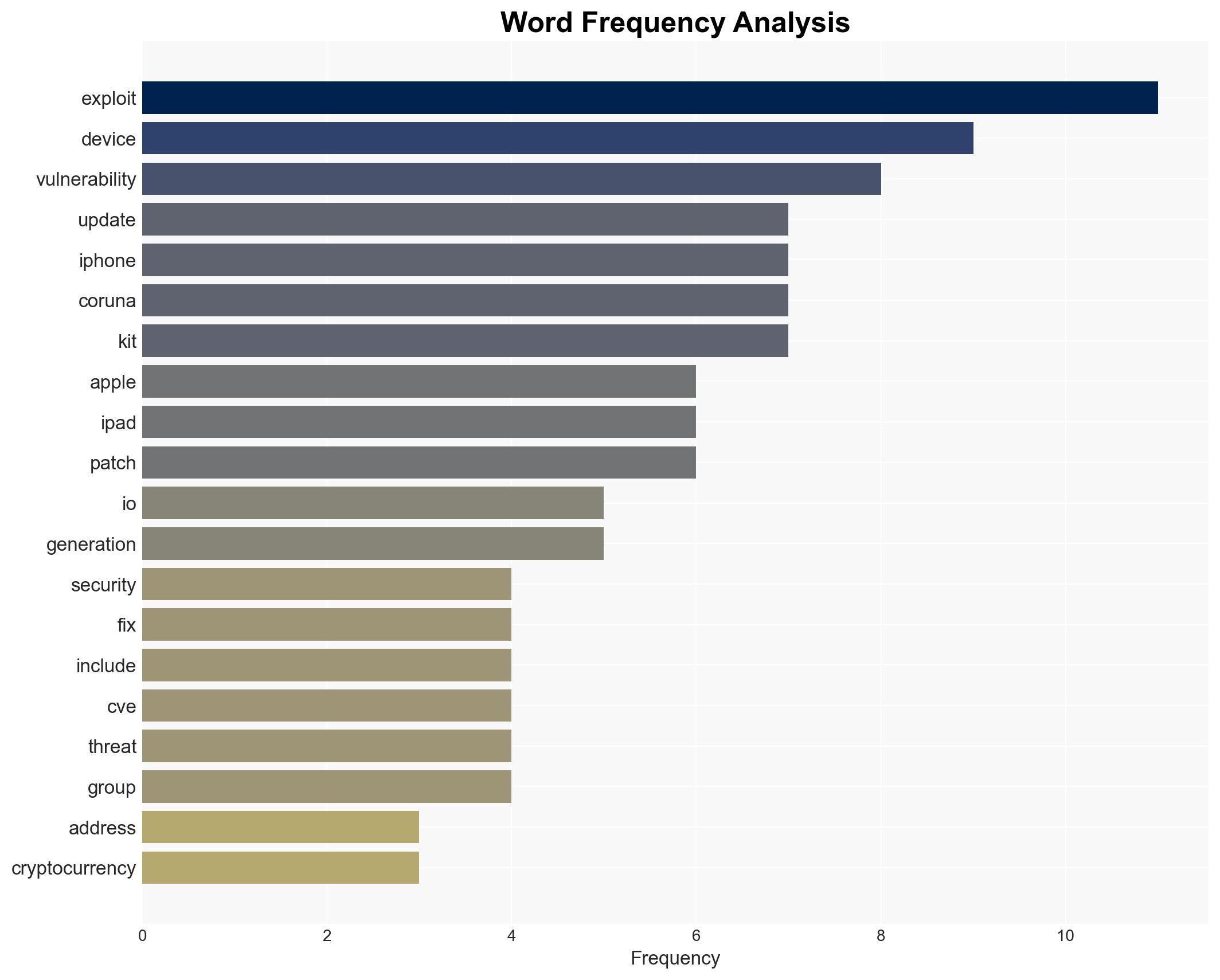
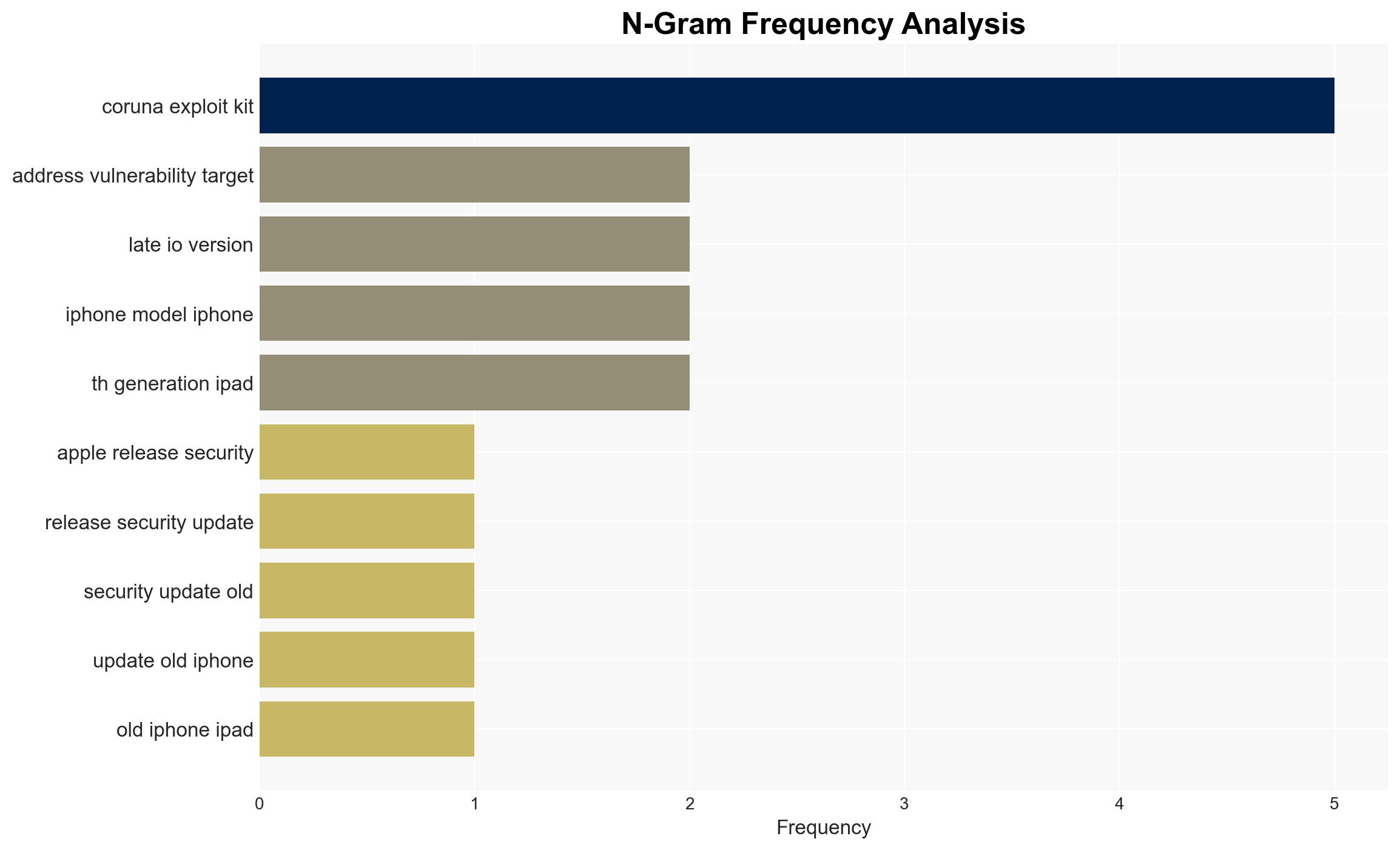
Apple has issued security updates for older iPhones and iPads to mitigate vulnerabilities exploited by the Coruna exploit kit, which has been used in cyberespionage and cryptocurrency theft since February 2025. The update is critical for devices unable to run the latest iOS versions. The Coruna exploit has been linked to multiple threat actors, including state-backed groups. Overall, there is moderate confidence in the assessment that these updates will reduce the immediate risk of exploitation.
2. Competing Hypotheses
- Hypothesis A: The Coruna exploit kit is primarily used by state-backed actors for cyberespionage, with financial motivations being secondary. This is supported by the involvement of a suspected Russian state-backed group. However, the presence of financially motivated actors suggests a dual-use capability.
- Hypothesis B: The Coruna exploit kit is primarily a tool for financially motivated cybercrime, with state-backed espionage as a secondary use. This is supported by the use of the kit in cryptocurrency theft. The involvement of state actors could be opportunistic rather than strategic.
- Assessment: Hypothesis A is currently better supported due to the strategic implications of state-backed cyberespionage and the involvement of sophisticated threat actors. Indicators such as increased targeting of political entities could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The Coruna exploit kit will continue to be used by both state-backed and financially motivated actors; Apple’s updates will effectively mitigate the vulnerabilities; older devices are more susceptible to exploitation.
- Information Gaps: Specific details on the full capabilities of the Coruna exploit kit and the complete list of affected devices are lacking.
- Bias & Deception Risks: Potential bias in attributing the exploit to state-backed actors without conclusive evidence; risk of underestimating the financial motivations of the actors involved.
4. Implications and Strategic Risks
The release of security updates for older devices may temporarily reduce the risk of exploitation, but persistent vulnerabilities in outdated hardware could lead to ongoing threats. The involvement of state-backed actors suggests potential geopolitical tensions.
- Political / Geopolitical: Potential for increased tensions between states if attribution to specific governments is confirmed.
- Security / Counter-Terrorism: Enhanced risk of cyberespionage targeting critical infrastructure and governmental entities.
- Cyber / Information Space: Continued evolution of exploit kits could lead to more sophisticated cyberattacks.
- Economic / Social: Potential financial losses from cryptocurrency theft could impact economic stability and consumer trust in digital platforms.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage rapid deployment of updates on all affected devices; increase monitoring of threat actor activities related to the Coruna exploit.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies for proactive threat intelligence sharing; enhance public awareness campaigns on cybersecurity hygiene.
- Scenario Outlook:
- Best: Successful mitigation of vulnerabilities with no further exploitation.
- Worst: Exploit evolves, leading to significant breaches and geopolitical tensions.
- Most-Likely: Continued low-level exploitation with periodic updates required.
6. Key Individuals and Entities
- Apple Inc.
- Google Threat Intelligence Group (GTIG)
- U.S. Cybersecurity and Infrastructure Security Agency (CISA)
- UNC6353 (Suspected Russian state-backed group)
- UNC6691 (Financially motivated Chinese threat actor)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cyber-espionage, state-backed threats, cryptocurrency theft, software vulnerabilities, threat intelligence, mobile security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us