Apple to release iOS 18 update to address DarkSword exploit for users not on iOS 26
Published on: 2026-04-01
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Apple confirms iOS 18 update to patch DarkSword exploit for users who havent upgraded to iOS 26
1. BLUF (Bottom Line Up Front)
Apple is releasing an iOS 18 update to patch the DarkSword exploit, which affects devices not upgraded to iOS 26. This move aims to protect users who have not updated their devices, reducing the risk of exploitation. The most likely hypothesis is that Apple is responding to increased threat exposure due to the public availability of the exploit. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Apple is proactively patching iOS 18 to mitigate the risk posed by the DarkSword exploit, which has been publicly disclosed on GitHub. Supporting evidence includes Apple’s statement and the timing of the update following the exploit’s disclosure. Key uncertainties include the extent of the exploit’s use in the wild.
- Hypothesis B: The update is primarily a public relations move to reassure users and stakeholders of Apple’s commitment to security. Supporting evidence includes Apple’s emphasis on encouraging updates to iOS 26 for advanced protections. Contradicting evidence is the technical necessity of the patch due to the exploit’s public availability.
- Assessment: Hypothesis A is currently better supported due to the immediate security threat posed by the exploit’s public disclosure. Indicators that could shift this judgment include reports of widespread exploitation or further updates from Apple addressing additional vulnerabilities.
3. Key Assumptions and Red Flags
- Assumptions: Apple has accurately assessed the threat level of the DarkSword exploit; the patch will effectively mitigate the vulnerabilities; users will update their devices promptly.
- Information Gaps: The exact number of devices still running iOS 18 and the prevalence of the exploit in the wild.
- Bias & Deception Risks: Potential bias in Apple’s communication strategy to downplay the severity of the exploit; reliance on open-source reporting may not capture the full scope of the threat.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of Apple’s security practices and influence user trust. It may also prompt other tech companies to reassess their patch management strategies.
- Political / Geopolitical: Limited direct implications, though could affect perceptions of U.S. tech company security standards globally.
- Security / Counter-Terrorism: Potential reduction in the attack surface for cybercriminals exploiting the DarkSword vulnerability.
- Cyber / Information Space: Highlights the importance of timely security updates and the risks of publicly disclosed exploits.
- Economic / Social: Possible short-term impact on Apple’s brand reputation and consumer trust, with longer-term implications for market competitiveness.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor for reports of exploitation; encourage users to update devices; assess the effectiveness of the patch.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms to enhance threat intelligence; invest in user education on the importance of updates.
- Scenario Outlook: Best: Rapid user adoption of updates mitigates threat. Worst: Exploit leads to significant breaches. Most-Likely: Gradual reduction in threat as updates are applied, with isolated incidents of exploitation.
6. Key Individuals and Entities
- Apple Inc.
- Wired (as a reporting source)
- GitHub (platform where exploit was posted)
- Not clearly identifiable from open sources in this snippet for individual actors involved in the exploit.
7. Thematic Tags
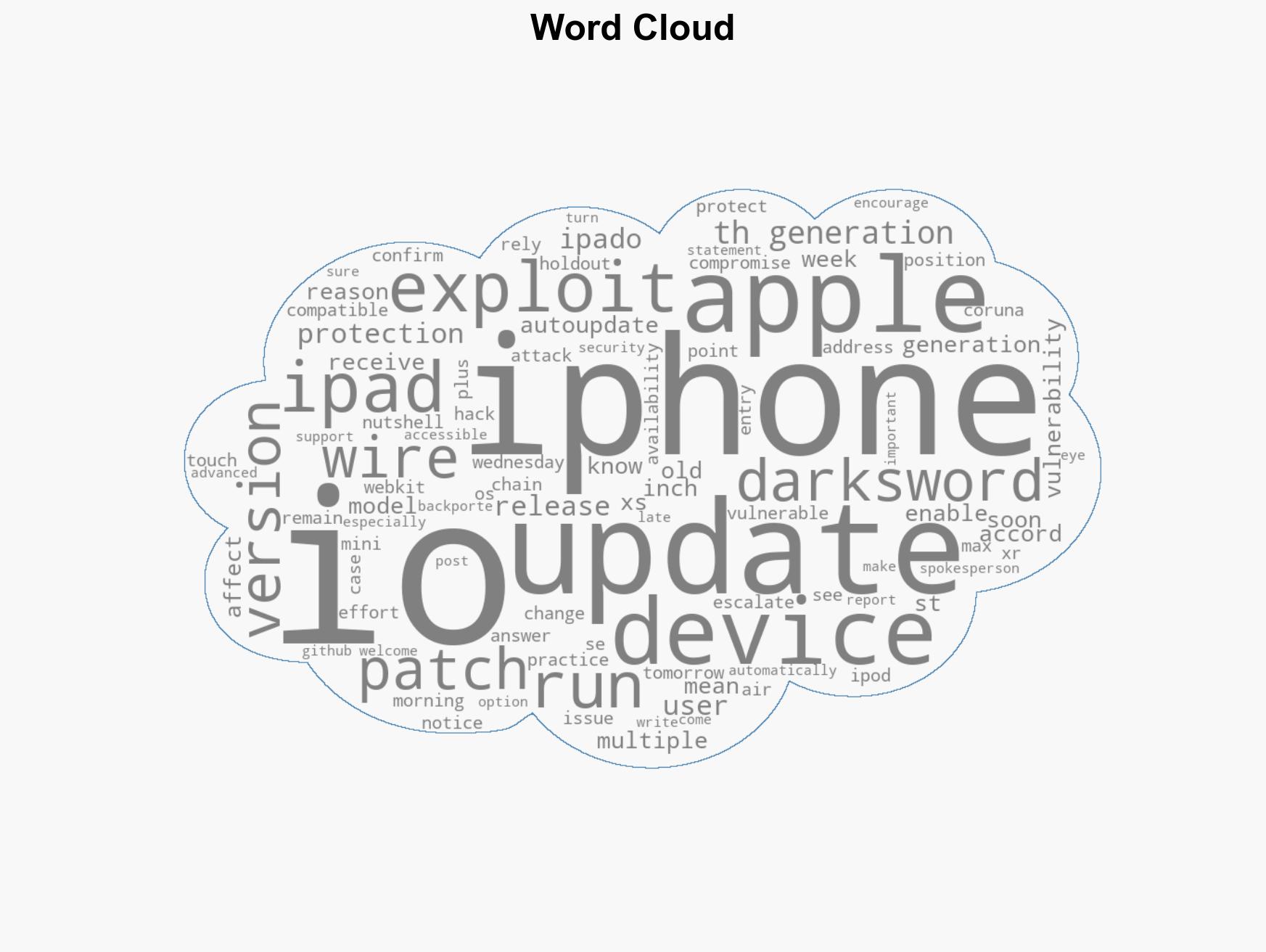
cybersecurity, software updates, vulnerability management, Apple, mobile security, public disclosure, threat mitigation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us