APT37 Enhances Malware Arsenal to Target Air-Gapped Systems via Removable Media
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: North Korea’s APT37 Expands Toolkit to Breach Air-Gapped Networks
1. BLUF (Bottom Line Up Front)
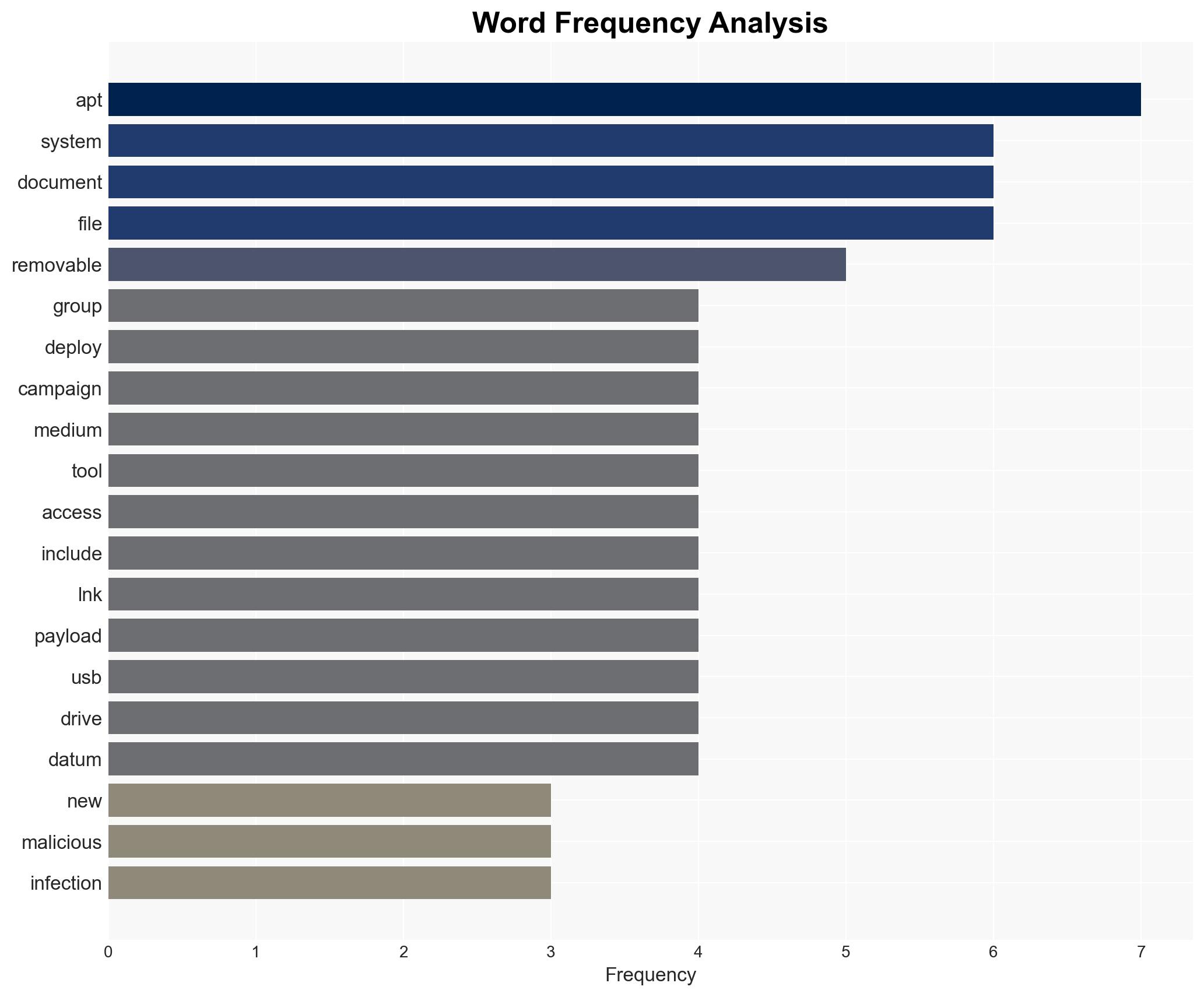
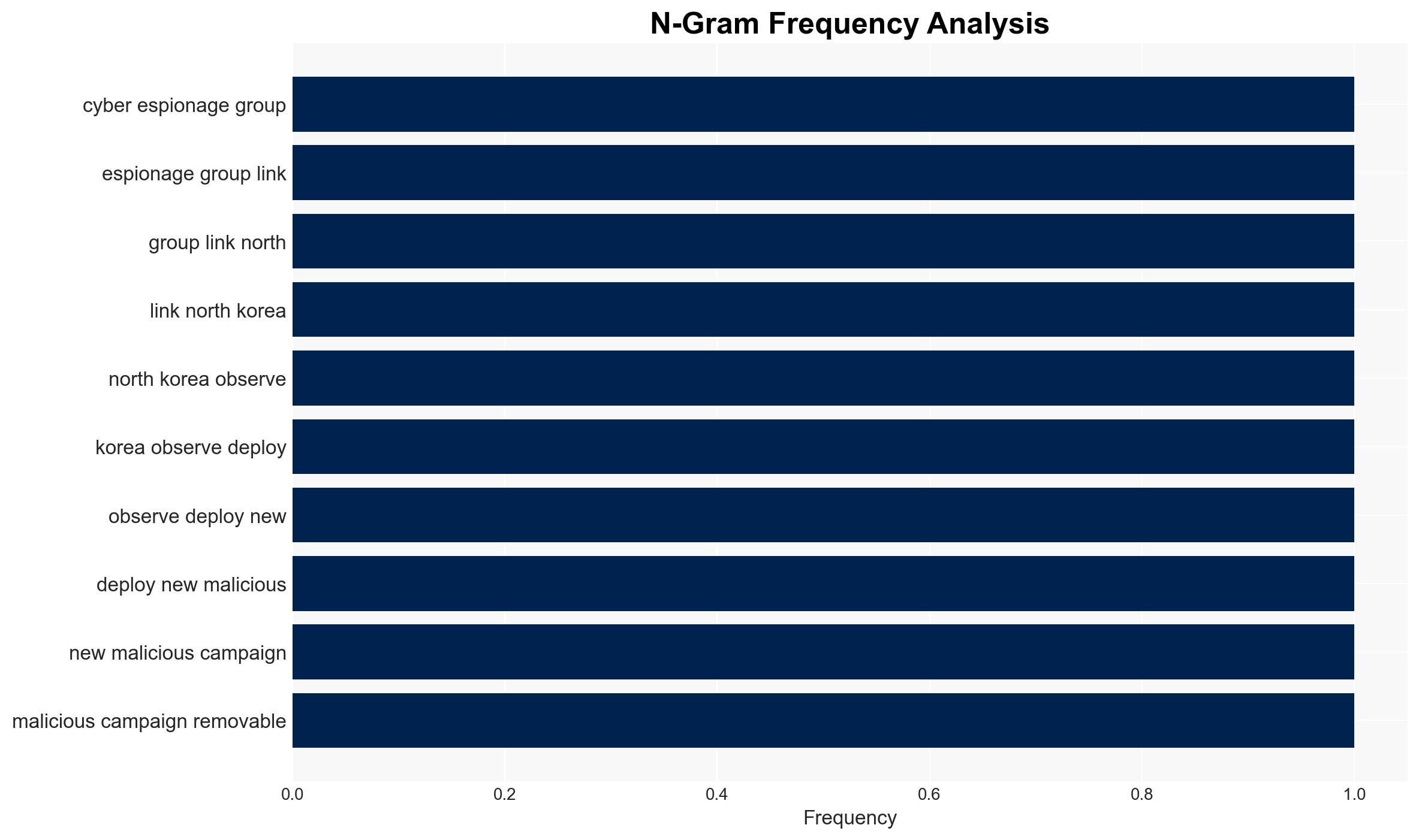
APT37, a North Korean cyber espionage group, has developed a new campaign, ‘Ruby Jumper,’ utilizing novel tools to breach air-gapped networks via removable media. This poses a significant threat to isolated systems across various industries. The assessment holds moderate confidence due to the lack of comprehensive visibility into the group’s full capabilities and intentions.
2. Competing Hypotheses
- Hypothesis A: APT37’s primary objective is to exfiltrate sensitive data from air-gapped networks to support North Korean strategic goals. This is supported by the group’s history of targeting strategic industries and the use of sophisticated tools like ThumbSBD for lateral movement. However, the full extent of their data exfiltration capabilities remains uncertain.
- Hypothesis B: APT37 aims to disrupt operations within targeted industries as a form of cyber warfare or coercion. While the use of disruptive tools is possible, the current evidence primarily indicates espionage activities rather than direct disruption.
- Assessment: Hypothesis A is currently better supported due to APT37’s historical focus on intelligence gathering. Indicators such as the use of Zoho WorkDrive for C2 communications suggest a strategic intent to collect and utilize sensitive information.
3. Key Assumptions and Red Flags
- Assumptions: APT37 has the technical capability to effectively breach air-gapped systems; the group is acting under directives from the North Korean government; the tools used are primarily for espionage rather than sabotage.
- Information Gaps: Details on the full range of APT37’s toolset and their specific targets within air-gapped networks; the extent of data exfiltrated and its impact.
- Bias & Deception Risks: Potential confirmation bias in attributing all activities to North Korea without considering false flag operations; reliance on a single source (Zscaler ThreatLabz) may introduce reporting bias.
4. Implications and Strategic Risks
This development could enhance North Korea’s cyber espionage capabilities, potentially leading to increased geopolitical tensions and a reevaluation of cyber defense postures globally.
- Political / Geopolitical: Escalation in cyber tensions between North Korea and affected nations, potentially leading to diplomatic confrontations.
- Security / Counter-Terrorism: Increased vulnerability of critical infrastructure in targeted countries, necessitating heightened security measures.
- Cyber / Information Space: Potential for increased cyber operations targeting isolated networks, prompting a reevaluation of air-gapped system security protocols.
- Economic / Social: Disruption in industries such as aerospace and manufacturing could have downstream economic impacts, affecting supply chains and market stability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of removable media usage in critical systems; conduct threat hunting for indicators of compromise related to APT37’s tools.
- Medium-Term Posture (1–12 months): Develop partnerships for intelligence sharing on North Korean cyber activities; invest in advanced detection and response capabilities for air-gapped systems.
- Scenario Outlook:
- Best: Successful mitigation efforts lead to minimal data loss and disruption.
- Worst: Widespread data breaches and operational disruptions occur, leading to significant geopolitical fallout.
- Most-Likely: Continued espionage activities with periodic data exfiltration, prompting ongoing defensive adjustments.
6. Key Individuals and Entities
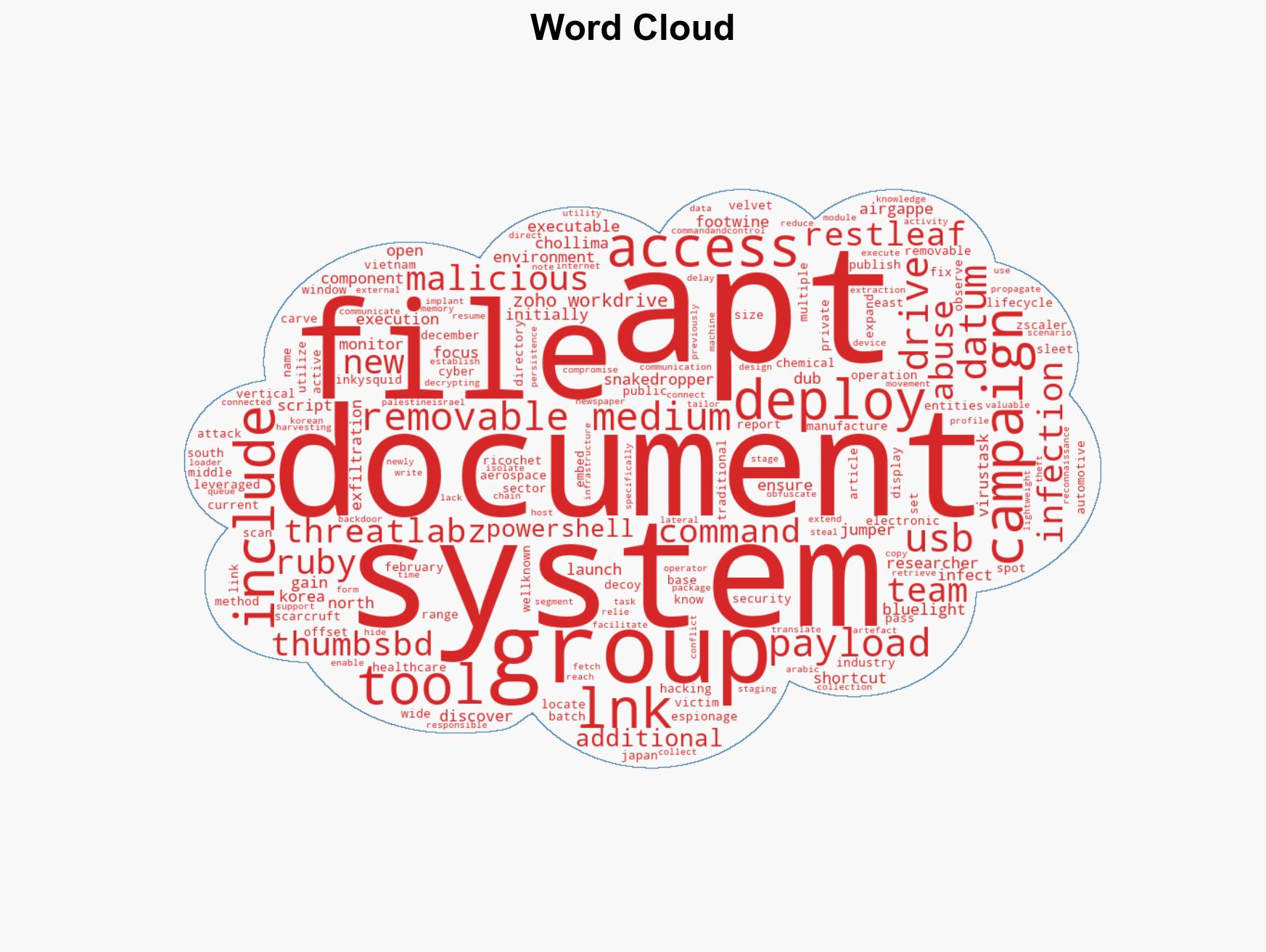
- APT37 (ScarCruft, Ruby Sleet, InkySquid, Ricochet Chollima, Velvet Chollima)
- Zscaler ThreatLabz
- Zoho WorkDrive
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cyber-espionage, North Korea, air-gapped networks, APT37, removable media, cyber defense, intelligence gathering
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us