Attackers are targeting CrushFTP vulnerability with public PoC CVE-2025-2825 – Help Net Security
Published on: 2025-04-01
Intelligence Report: Attackers are targeting CrushFTP vulnerability with public PoC CVE-2025-2825 – Help Net Security
1. BLUF (Bottom Line Up Front)
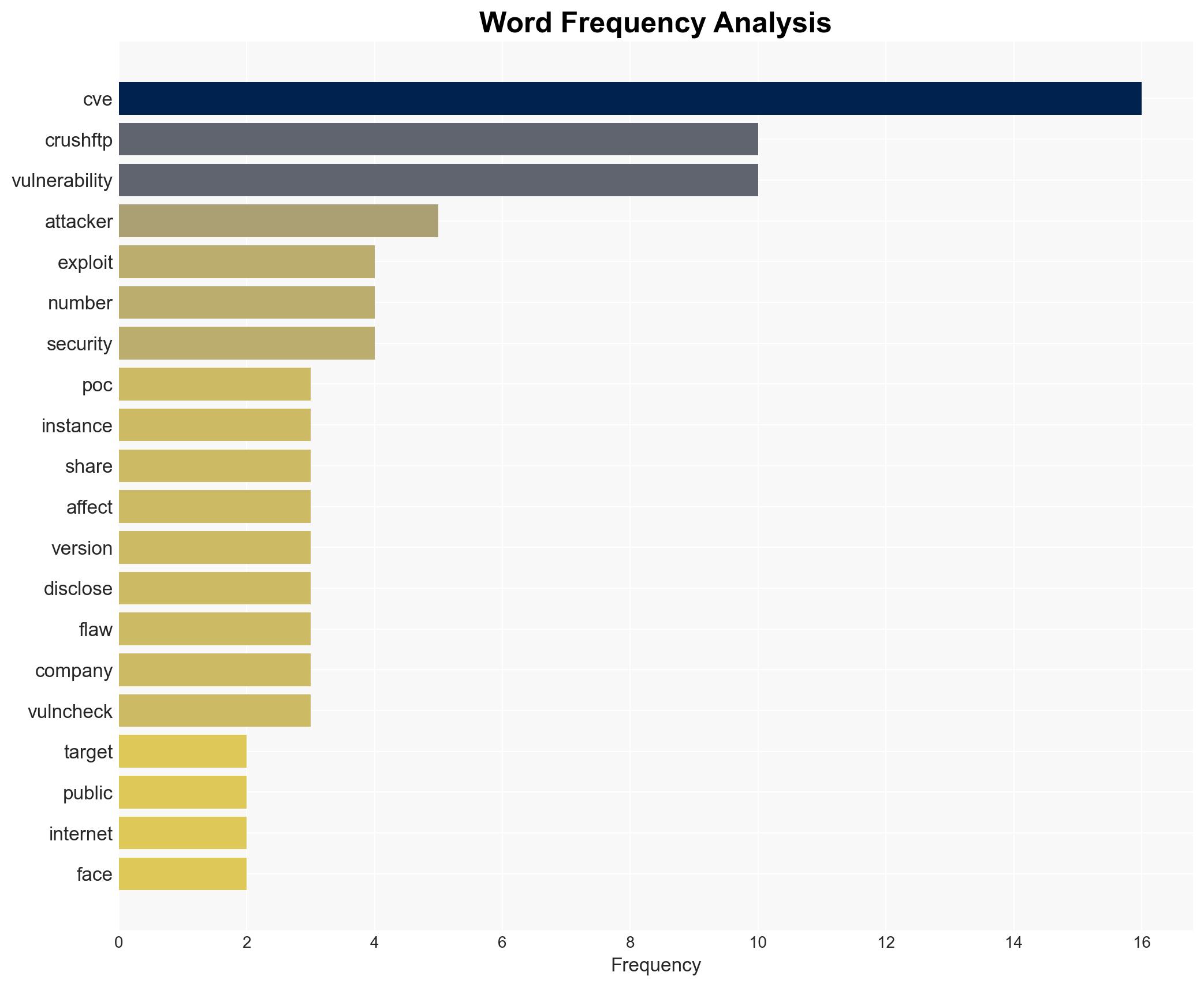
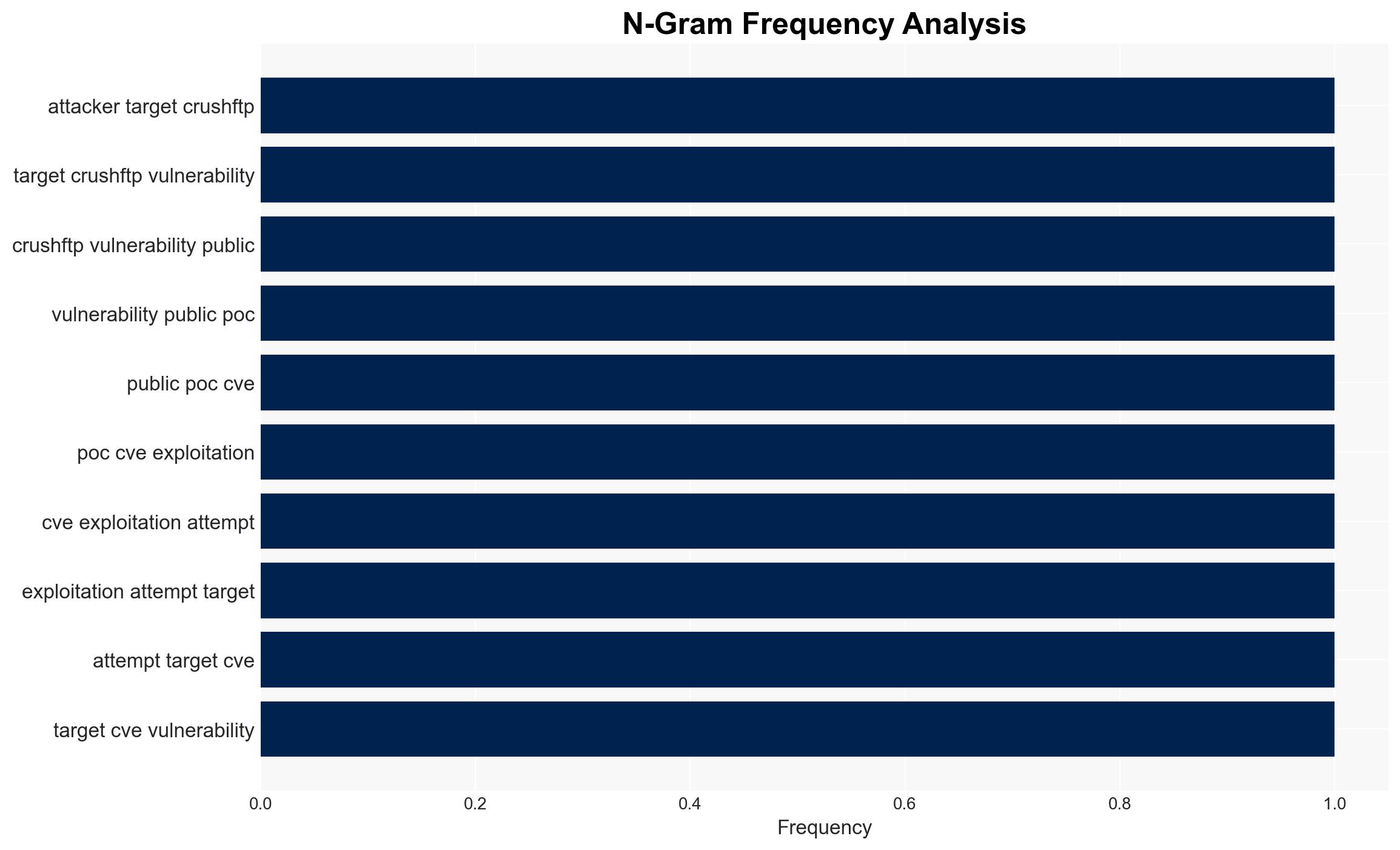
Attackers are actively exploiting a vulnerability in CrushFTP, identified as CVE-2025-2825, using publicly available proof-of-concept (PoC) exploit code. This vulnerability allows unauthorized access to CrushFTP servers with exposed ports. Immediate action is required to patch affected systems to prevent unauthorized access and potential data breaches.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
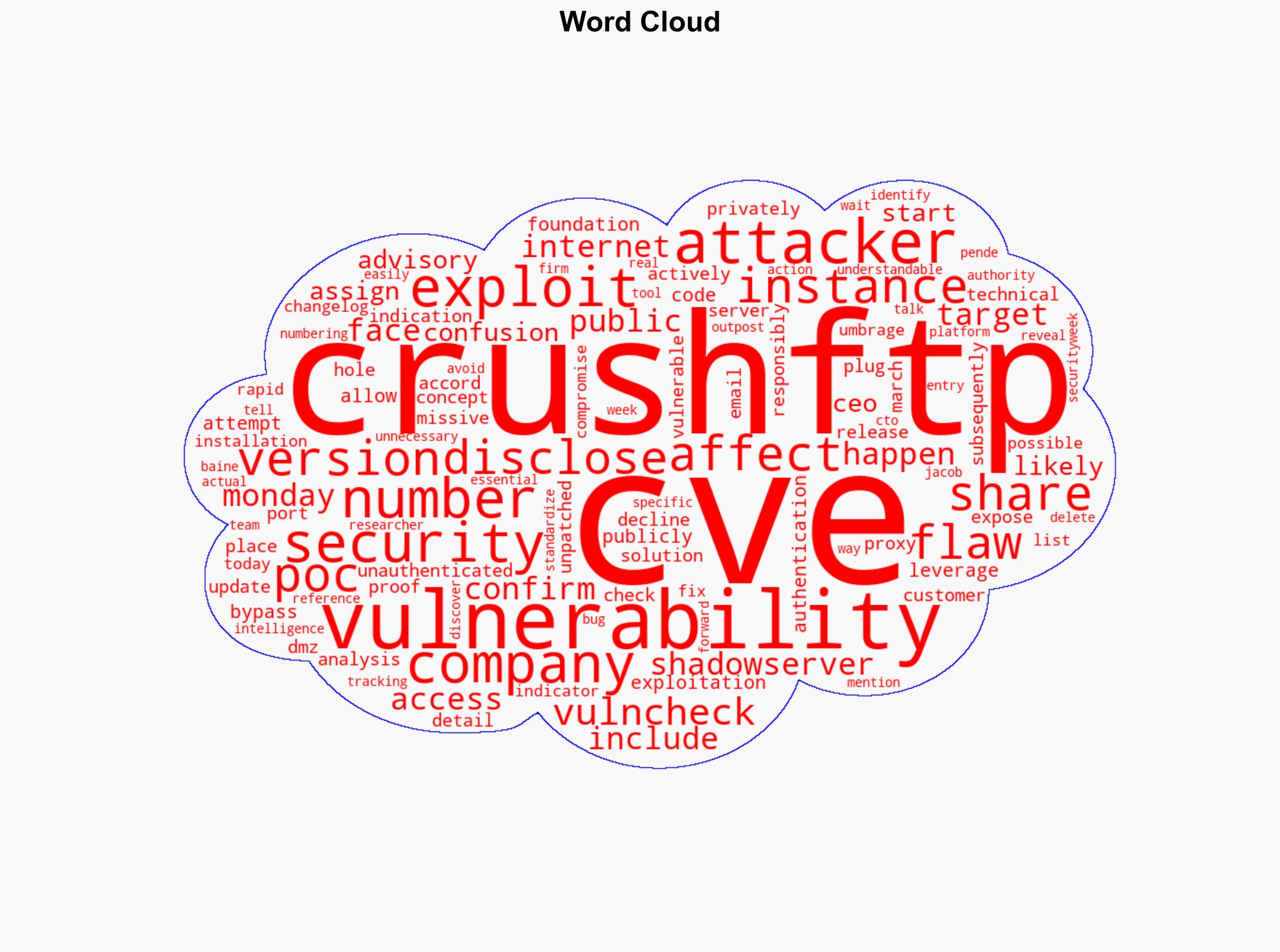
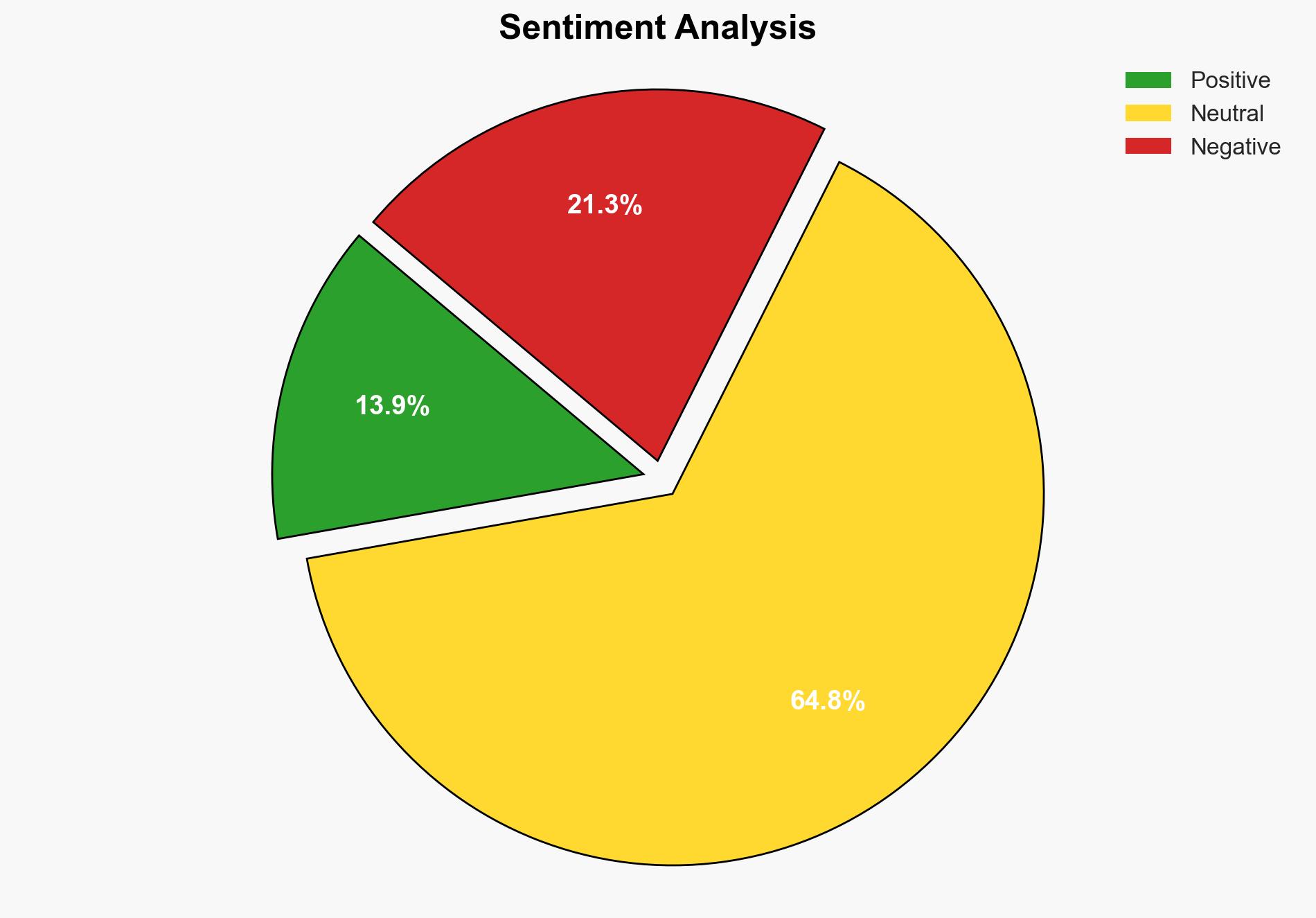
The vulnerability CVE-2025-2825 affects CrushFTP versions that allow authentication bypass, granting attackers access to servers without credentials. The Shadowserver Foundation has confirmed the presence of unpatched, internet-facing instances vulnerable to this exploit. Despite the vulnerability being privately disclosed to customers in March, there is confusion due to discrepancies in the CVE numbering and advisory details. The vulnerability was discovered and disclosed by researchers at Outpost, highlighting the need for standardized vulnerability tracking.
3. Implications and Strategic Risks
The exploitation of CVE-2025-2825 poses significant risks to organizations using CrushFTP, including potential data breaches and unauthorized data access. This could lead to national security concerns if sensitive information is compromised. The economic impact could be substantial, affecting businesses reliant on secure data transfer and storage. Additionally, the confusion surrounding CVE numbering could undermine trust in vulnerability reporting systems.
4. Recommendations and Outlook
Recommendations:
- Organizations using CrushFTP should immediately apply the latest patches and verify the security of their installations.
- Enhance monitoring for indicators of compromise related to CVE-2025-2825.
- Improve communication and coordination between vulnerability numbering authorities and software vendors to prevent future discrepancies.
Outlook:
In the best-case scenario, organizations swiftly patch their systems, mitigating the risk of exploitation. In the worst-case scenario, widespread exploitation could occur, leading to significant data breaches and economic losses. The most likely outcome involves increased awareness and patching efforts, reducing the number of vulnerable instances over time.
5. Key Individuals and Entities
The report mentions the following individuals and entities:
- Jacob Baine
- Shadowserver Foundation
- Outpost
- VulnCheck