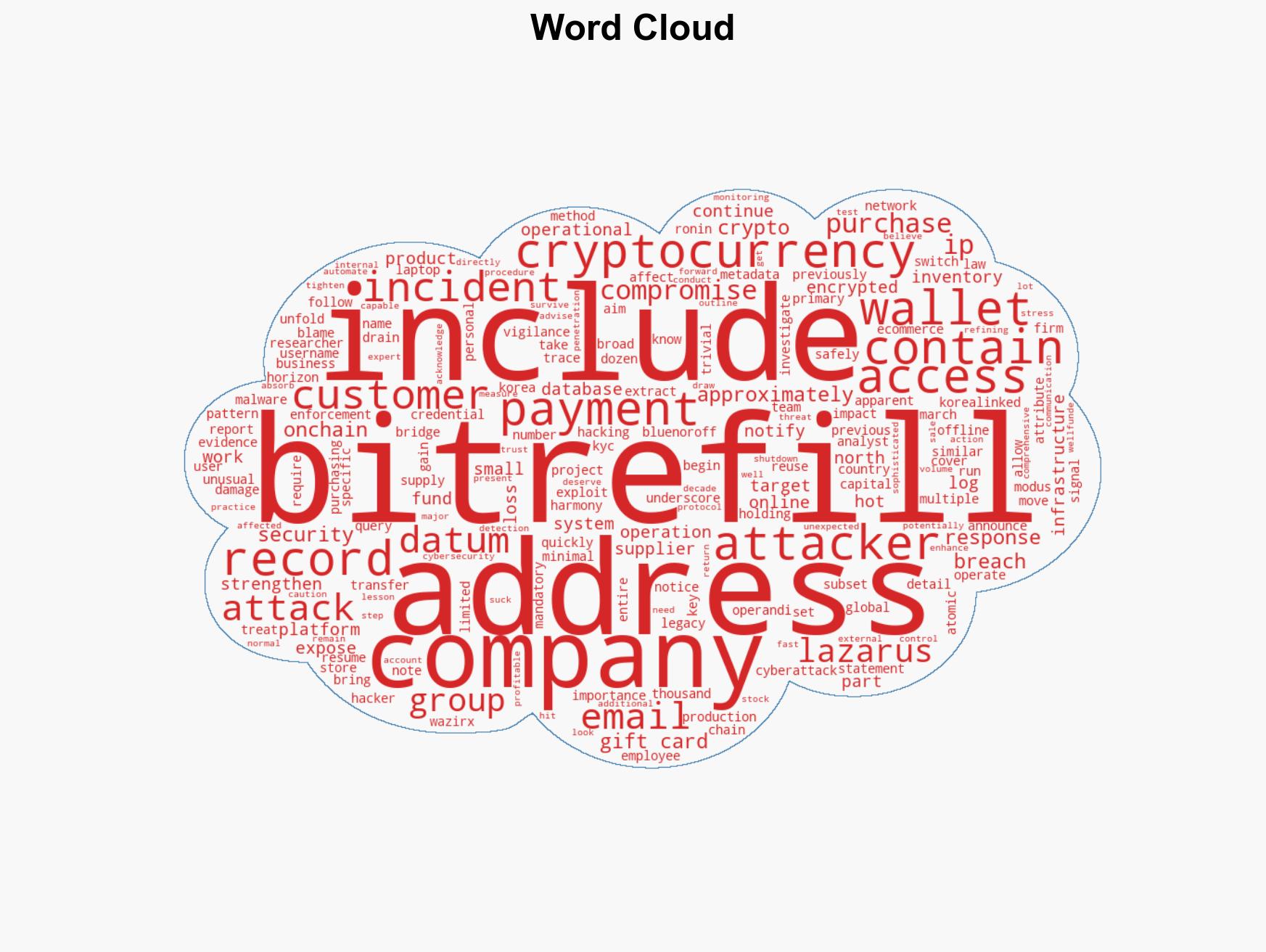
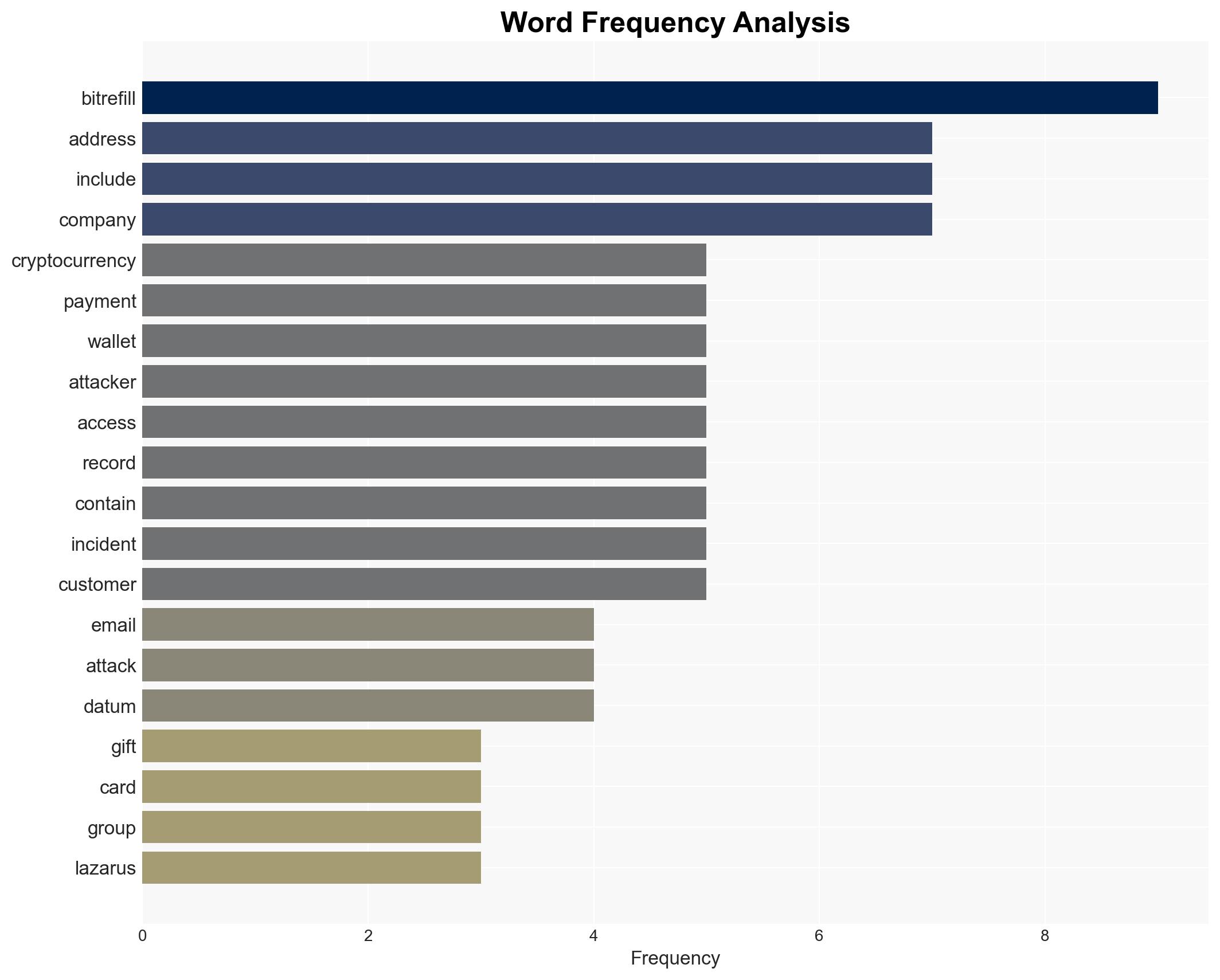
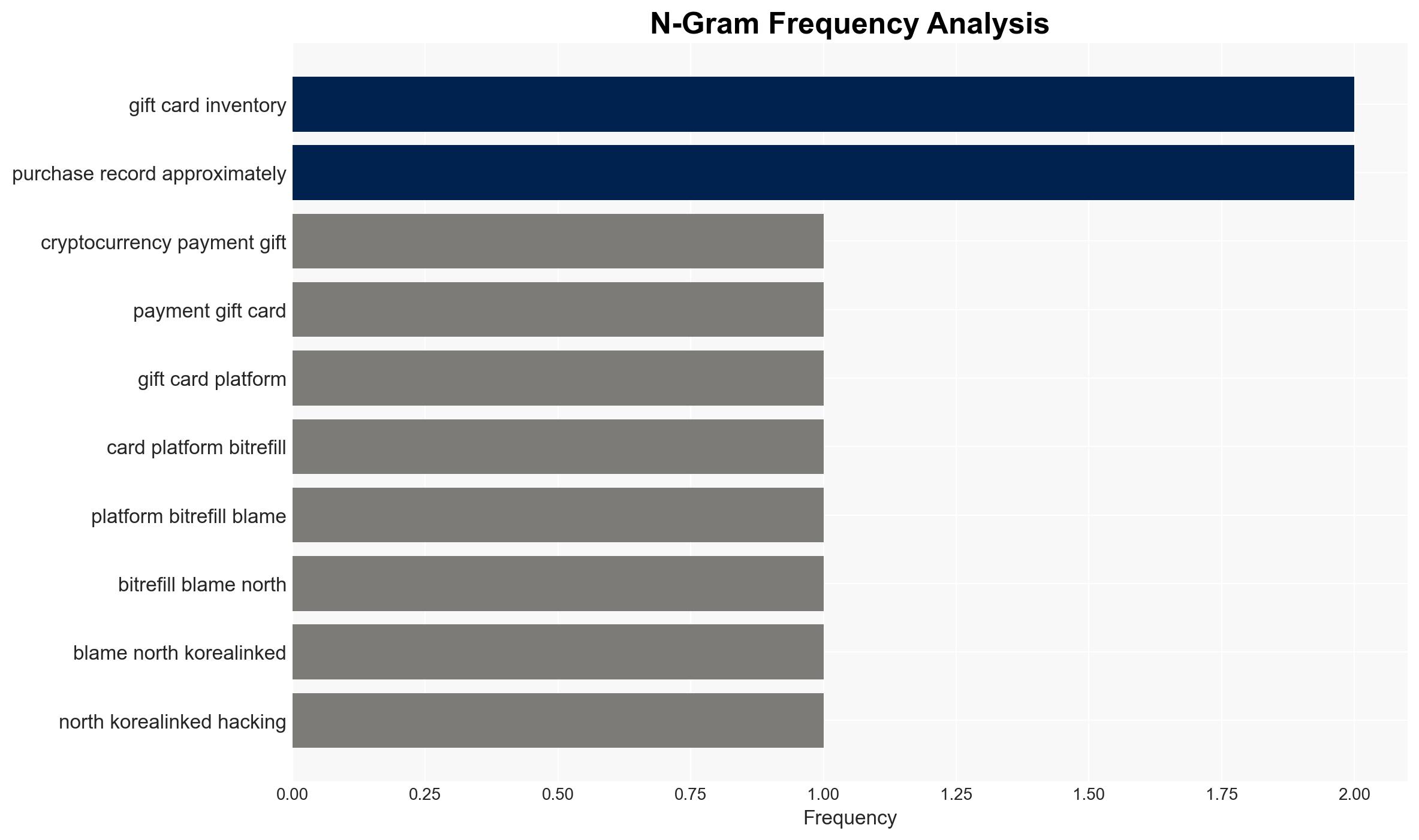
Bitrefill attributes breach of 18,500 purchase records to Lazarus Group linked to North Korea cyberattack
Published on: 2026-03-18
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Bitrefill accuses North Korea-linked Lazarus hacker group for compromising 18500 purchase records
1. BLUF (Bottom Line Up Front)
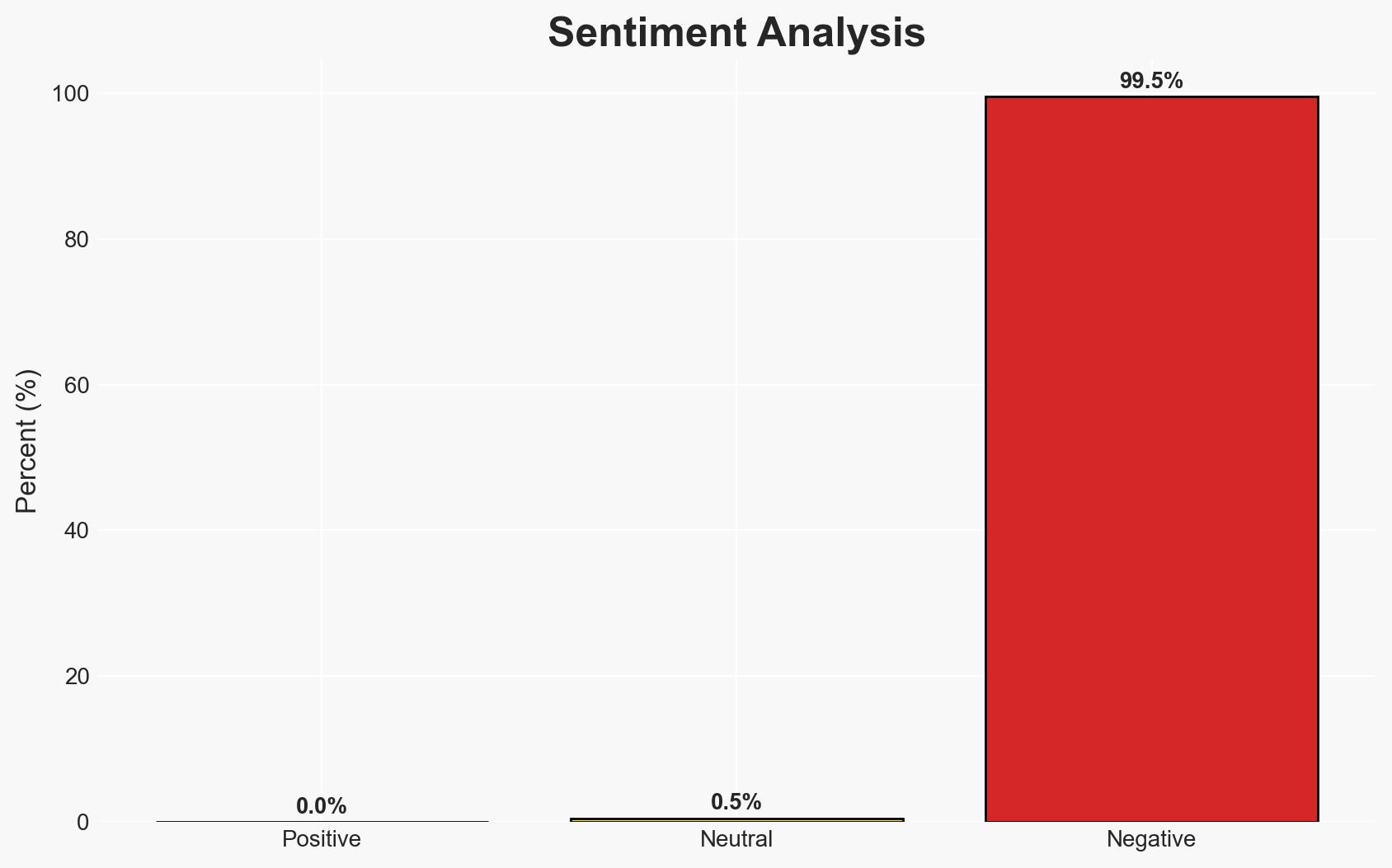
The Lazarus Group, linked to North Korea, is accused of a cyberattack on Bitrefill, compromising 18,500 purchase records and cryptocurrency wallets. The group’s modus operandi aligns with previous attacks attributed to them. The incident highlights vulnerabilities in cryptocurrency platforms. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The Lazarus Group is responsible for the attack, supported by the modus operandi and historical targeting patterns. However, the attribution relies heavily on circumstantial evidence and known tactics, which could be mimicked by other actors.
- Hypothesis B: Another cybercriminal group is responsible, using tactics similar to the Lazarus Group to mislead attribution. This is less supported due to the specific targeting of cryptocurrency platforms, a known focus of Lazarus.
- Assessment: Hypothesis A is currently better supported due to the alignment of tactics and targets with known Lazarus operations. Indicators such as unique malware signatures or further intelligence could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The Lazarus Group continues to target cryptocurrency platforms; the compromised employee laptop was the initial access point; Bitrefill’s report is accurate and complete.
- Information Gaps: Specific malware signatures used; detailed forensic analysis results; potential insider involvement.
- Bias & Deception Risks: Attribution bias due to historical patterns; potential deception by attackers mimicking Lazarus tactics.
4. Implications and Strategic Risks
This incident could lead to increased scrutiny on cryptocurrency security and regulatory measures. It may also embolden other state-sponsored groups to target similar platforms.
- Political / Geopolitical: Potential diplomatic tensions with North Korea; increased calls for international cooperation on cybercrime.
- Security / Counter-Terrorism: Heightened alert for similar attacks on other financial platforms; potential for retaliatory cyber operations.
- Cyber / Information Space: Increased focus on securing cryptocurrency infrastructure; potential misinformation campaigns exploiting the breach.
- Economic / Social: Loss of consumer trust in cryptocurrency platforms; potential financial instability for affected users.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cryptocurrency transactions; collaborate with cybersecurity firms for threat intelligence sharing.
- Medium-Term Posture (1–12 months): Develop partnerships with law enforcement for rapid incident response; invest in advanced cybersecurity measures.
- Scenario Outlook:
- Best: Improved security measures deter future attacks; increased international cooperation.
- Worst: Continued successful attacks by state-sponsored groups; significant financial losses.
- Most-Likely: Incremental improvements in security; sporadic attacks continue.
6. Key Individuals and Entities
- Lazarus Group (North Korea-linked hacking group)
- Bitrefill (Cryptocurrency payments and gift card platform)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cryptocurrency, North Korea, state-sponsored attacks, cyber-espionage, financial security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us