Border Security Gaps Heighten Fears of Domestic Terrorism Amid Rising Threats from Iranian-Backed Cells
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: A gathering storm Border vulnerabilities amplify domestic terror fears
1. BLUF (Bottom Line Up Front)
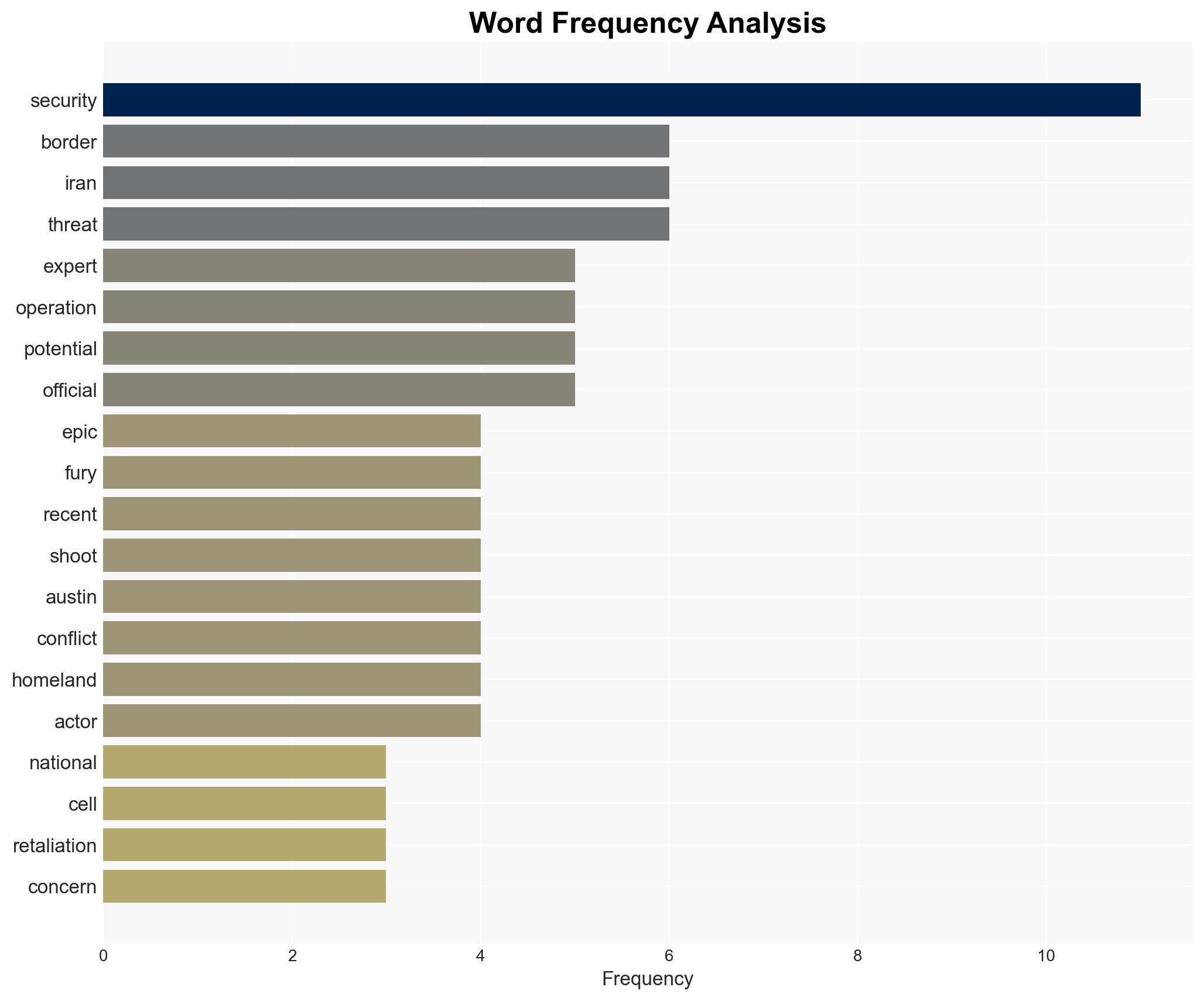
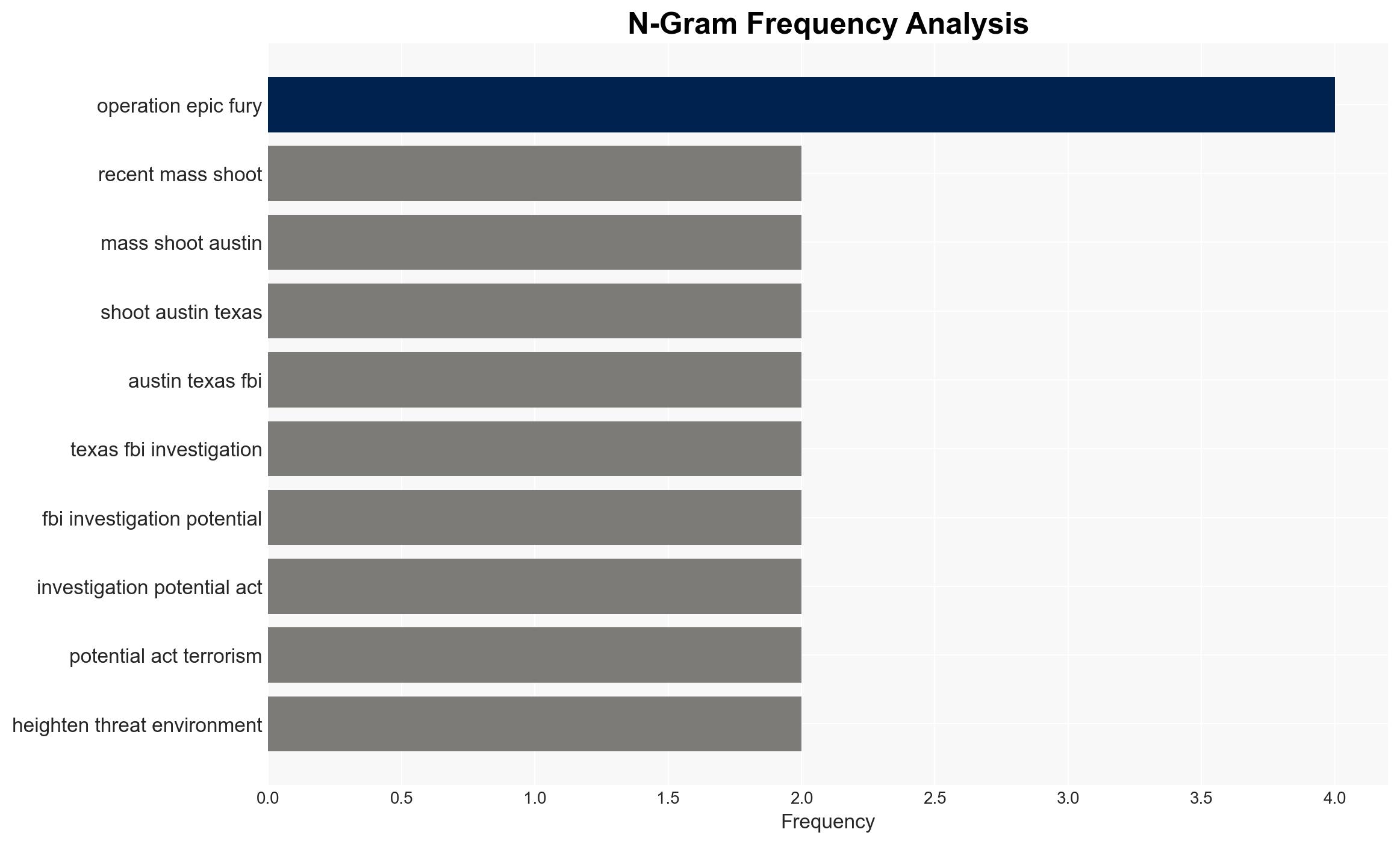
The potential activation of Iranian-backed sleeper cells in the U.S. poses a significant threat, exacerbated by historical border security vulnerabilities. The recent mass shooting in Austin, Texas, under investigation as a potential terrorist act, underscores the immediacy of this threat. Current intelligence suggests a moderate confidence level in the likelihood of retaliatory attacks following Operation Epic Fury.
2. Competing Hypotheses
- Hypothesis A: Iranian-backed sleeper cells are likely to be activated in the U.S. in retaliation for Operation Epic Fury. This is supported by historical Iranian plots against U.S. targets and the recent mass shooting in Austin. However, the specific involvement of sleeper cells remains unconfirmed, and the connection to the Austin incident is still under investigation.
- Hypothesis B: The recent threats and incidents are not directly linked to Iranian-backed sleeper cells but are instead isolated acts of domestic terrorism or unrelated criminal activities. This is supported by the lack of concrete evidence directly linking the Austin shooting to Iranian operatives.
- Assessment: Hypothesis A is currently better supported due to historical context and heightened threat levels post-Operation Epic Fury. Key indicators such as confirmed links between the Austin shooter and Iranian operatives could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Iranian sleeper cells exist within the U.S.; border security failures have allowed potential threats to enter; Iran will retaliate for Operation Epic Fury.
- Information Gaps: Specific identities and locations of sleeper cells; direct evidence linking recent incidents to Iranian operatives; comprehensive data on individuals who entered the U.S. undetected.
- Bias & Deception Risks: Potential overestimation of threat due to historical bias against Iran; reliance on incomplete or politically influenced border security data; possible Iranian disinformation campaigns.
4. Implications and Strategic Risks
The activation of sleeper cells could lead to increased domestic terrorism, straining law enforcement and national security resources. This may also exacerbate geopolitical tensions and influence U.S. foreign policy.
- Political / Geopolitical: Potential escalation of U.S.-Iran tensions; impact on U.S.-Israel relations and Middle Eastern stability.
- Security / Counter-Terrorism: Increased domestic threat level; potential for further attacks; need for enhanced intelligence and law enforcement coordination.
- Cyber / Information Space: Potential for cyber retaliation by Iran; increased misinformation and propaganda efforts.
- Economic / Social: Potential economic impact due to heightened security measures; increased public fear and social unrest.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance border security and intelligence sharing; increase public awareness and vigilance campaigns; monitor potential sleeper cell activities.
- Medium-Term Posture (1–12 months): Strengthen international partnerships for counter-terrorism; invest in border security technology; develop resilience against potential retaliatory attacks.
- Scenario Outlook:
- Best: No further incidents; improved U.S.-Iran relations.
- Worst: Multiple coordinated attacks; significant casualties and geopolitical instability.
- Most-Likely: Sporadic incidents; heightened security and diplomatic tensions.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
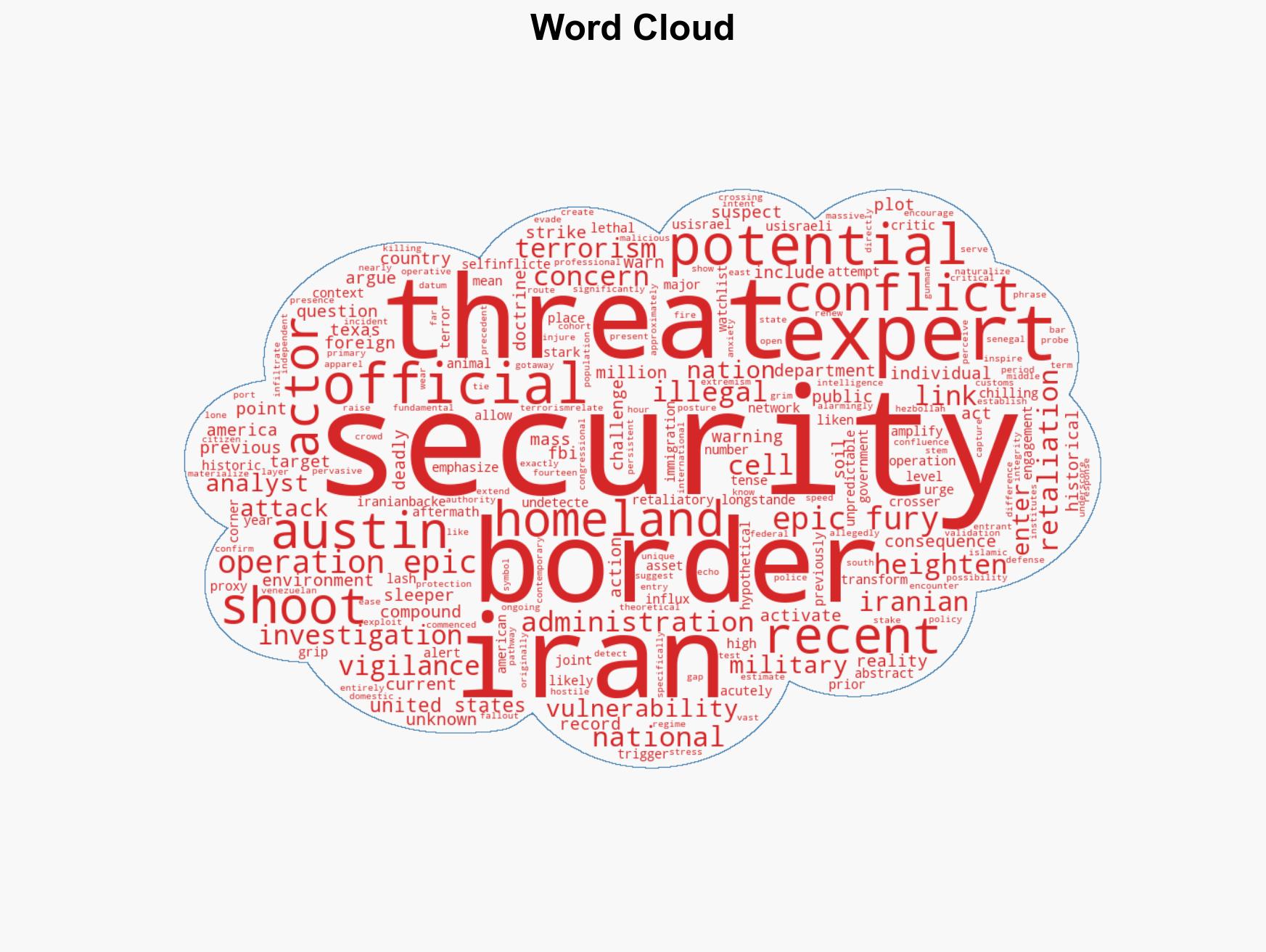
national security threats, counter-terrorism, border security, Iran-U.S. relations, sleeper cells, Operation Epic Fury, domestic terrorism, intelligence gaps
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Expose and correct potential biases in assessments through red-teaming and structured challenge.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us