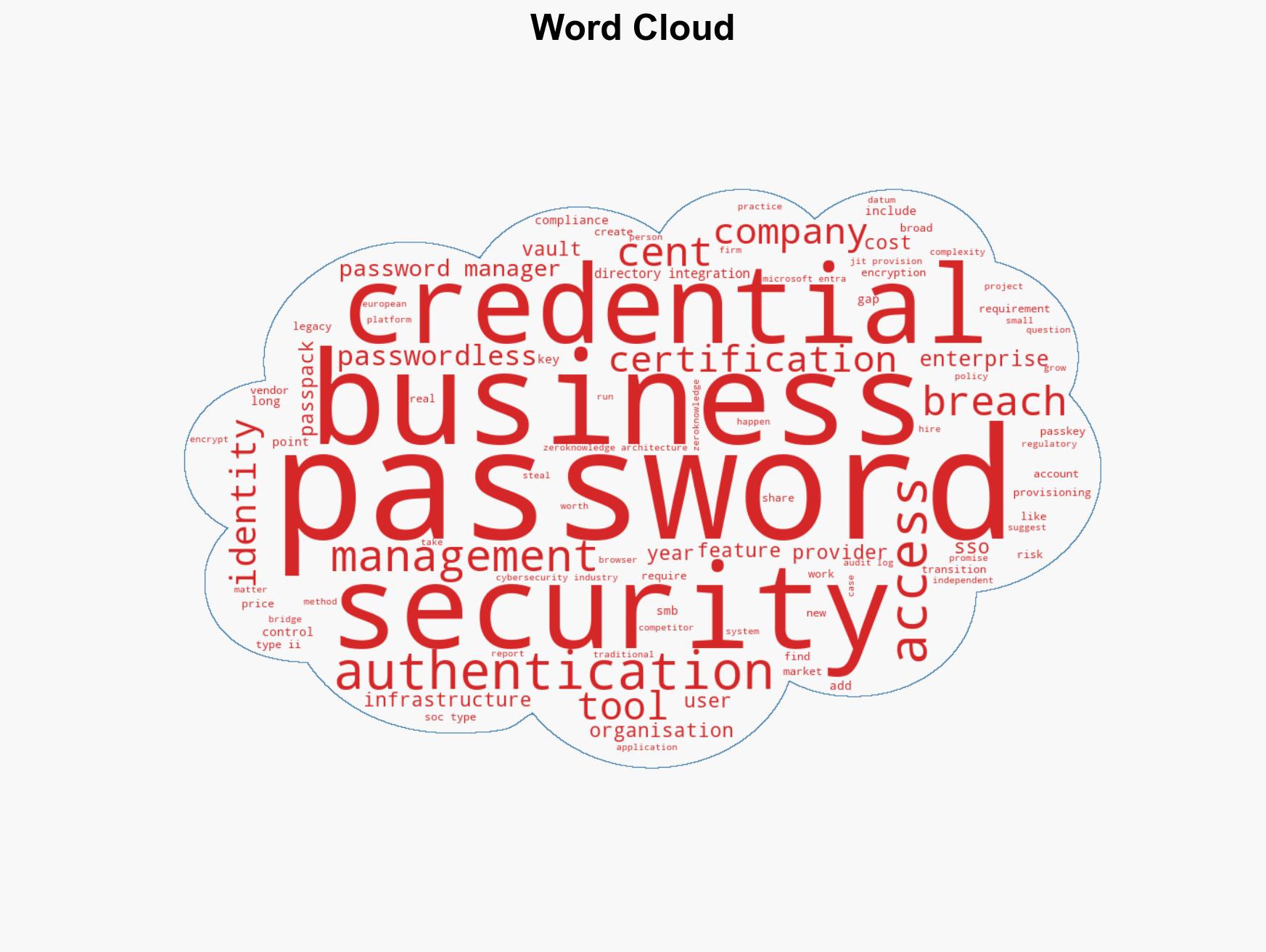
Businesses Must Prepare for a Passwordless Future, Despite Years of Slow Adoption and Ongoing Credential Risks
Published on: 2026-03-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: The passwordless future is years away Here is what businesses should do now
1. BLUF (Bottom Line Up Front)
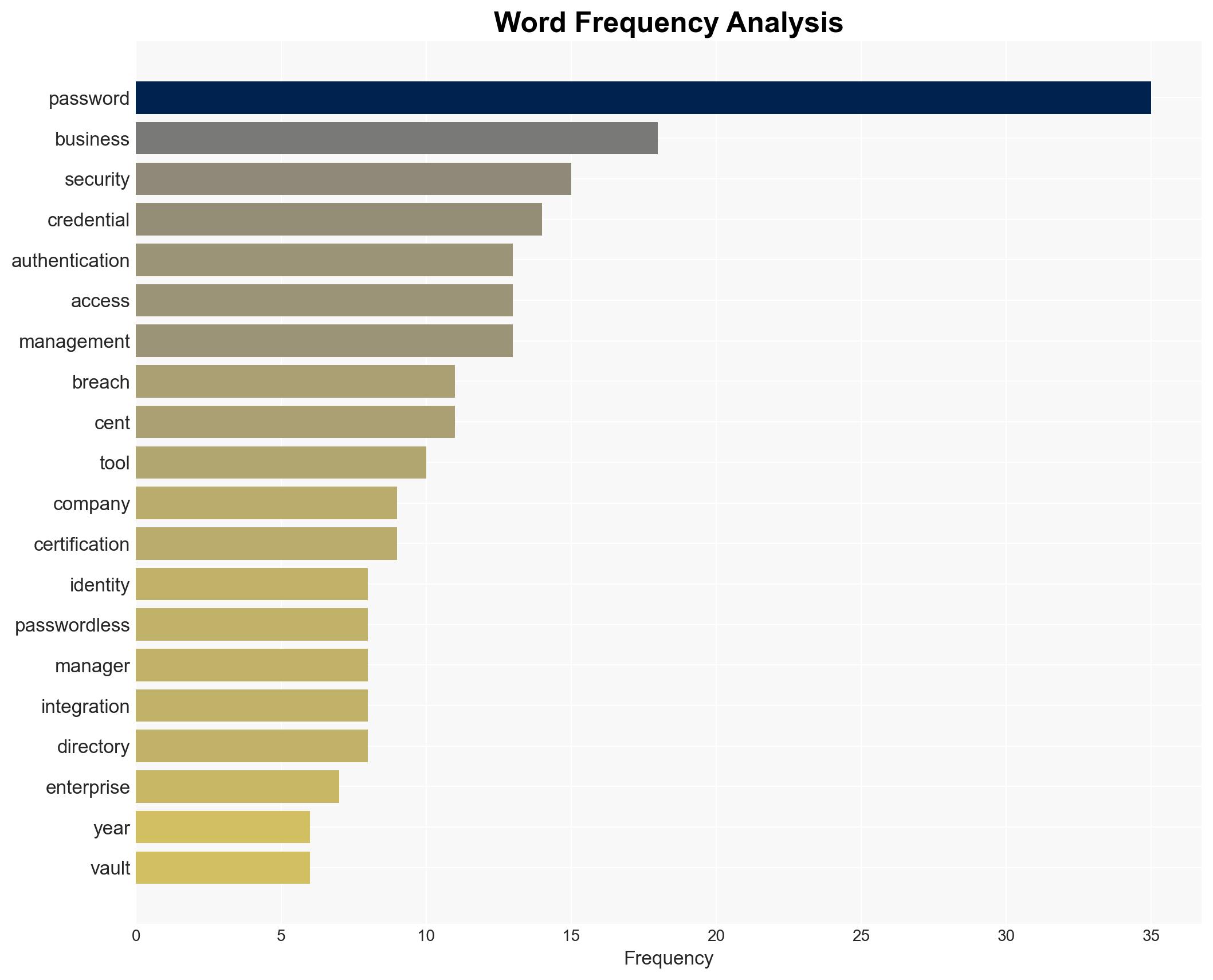
The transition to a passwordless future is progressing slowly, with most organizations still reliant on traditional passwords. This delay poses significant security risks, particularly for small and mid-size businesses (SMBs) that lack the resources for comprehensive identity transformation. The most likely hypothesis is that passwords will coexist with newer authentication methods until at least 2028. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
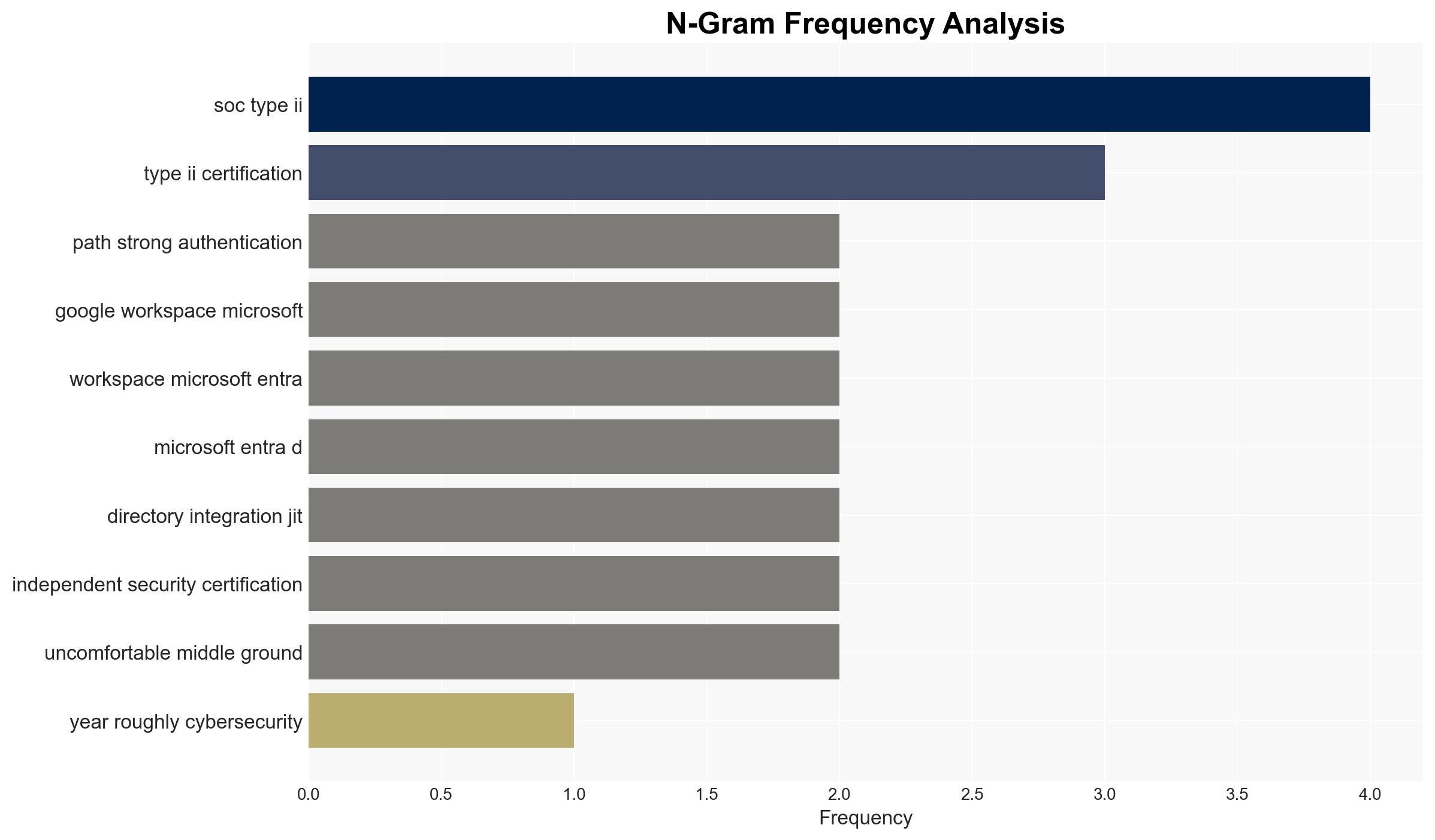
- Hypothesis A: The slow adoption of passwordless technologies is due to technical and resource constraints, particularly among SMBs. Supporting evidence includes the complexity of migrating legacy systems and the lack of resources for smaller organizations. Key uncertainties involve the pace of technological advancements and regulatory changes that could accelerate adoption.
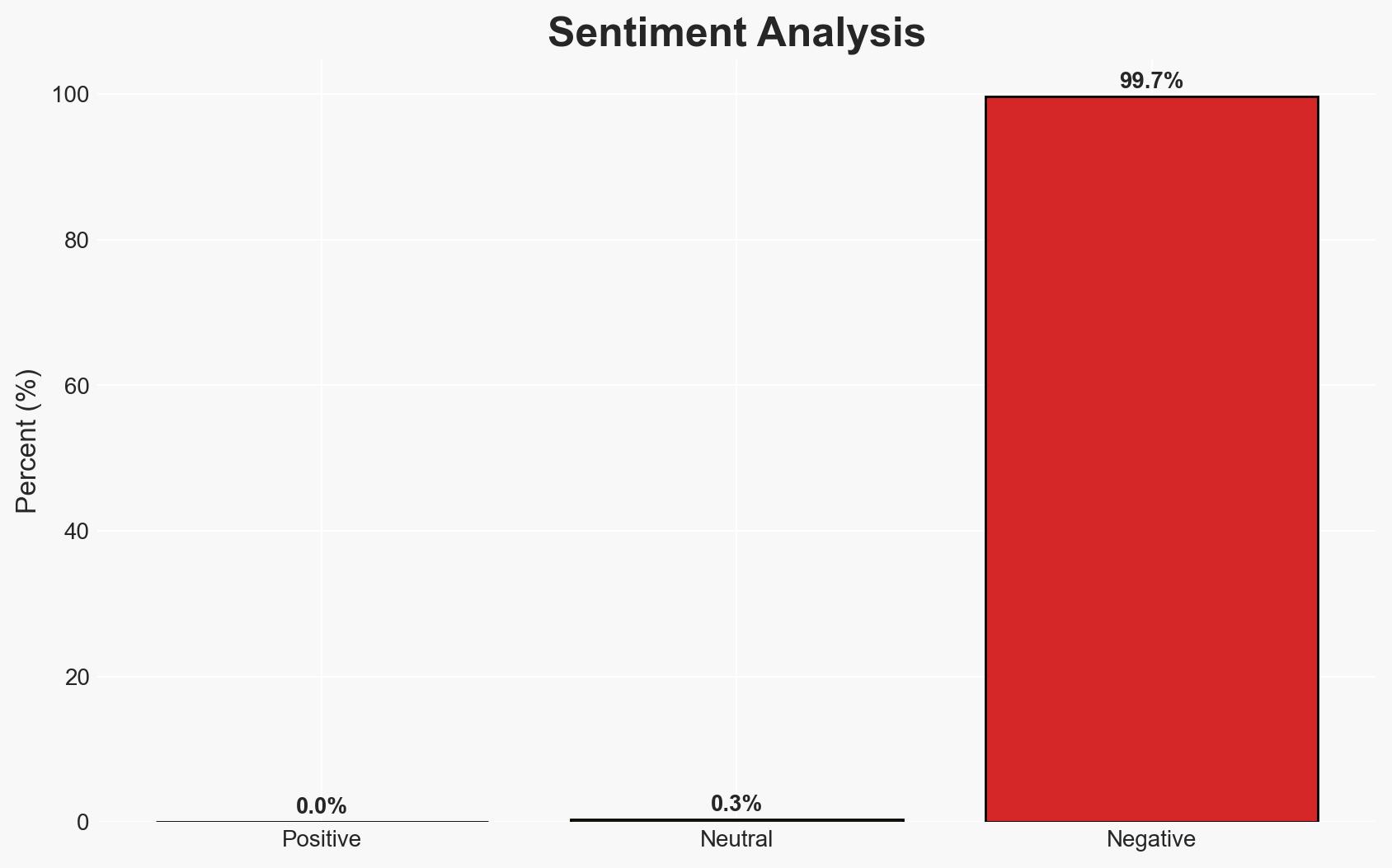
- Hypothesis B: The slow adoption is primarily due to a lack of awareness and prioritization of cybersecurity risks associated with passwords. While some evidence suggests that organizations are aware of the risks, the continued prevalence of breaches indicates a possible underestimation of the threat. Contradicting evidence includes ongoing investments in passwordless infrastructure.
- Assessment: Hypothesis A is currently better supported due to the documented technical and resource challenges faced by organizations. Indicators that could shift this judgment include significant technological breakthroughs or regulatory mandates that force faster adoption.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will continue to prioritize cybersecurity investments; technological advancements will gradually reduce the complexity of passwordless adoption; regulatory environments will remain stable.
- Information Gaps: Detailed data on the specific barriers SMBs face in adopting passwordless technologies; insights into the effectiveness of current passwordless solutions in reducing breaches.
- Bias & Deception Risks: Potential bias in industry reports favoring passwordless solutions; risk of underreporting breaches due to reputational concerns.
4. Implications and Strategic Risks
The slow transition to passwordless authentication may lead to sustained cybersecurity vulnerabilities, particularly for SMBs. This could result in increased breach incidents and associated economic losses.
- Political / Geopolitical: Limited direct implications, but potential for increased regulatory scrutiny on cybersecurity practices.
- Security / Counter-Terrorism: Continued reliance on passwords may increase vulnerability to cyber threats, impacting national security.
- Cyber / Information Space: Persistent password-related breaches could undermine trust in digital systems and services.
- Economic / Social: Potential economic impact from breaches, particularly on SMBs, could affect market stability and consumer confidence.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage organizations to conduct comprehensive security audits to identify password vulnerabilities; promote awareness campaigns on the risks of password reliance.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms to support SMBs in transitioning to passwordless solutions; advocate for regulatory incentives to accelerate adoption.
- Scenario Outlook:
- Best: Rapid technological advancements and regulatory support lead to widespread adoption of passwordless solutions by 2026.
- Worst: Continued reliance on passwords results in escalating breach incidents and significant economic losses.
- Most-Likely: Gradual adoption of passwordless technologies with coexistence of passwords until at least 2028.
6. Key Individuals and Entities
- HYPR (identity security firm)
- Verizon (Data Breach Investigations Report)
- Gartner (research organization)
- Okta (identity management company)
- CyberArk (identity security company)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, passwordless authentication, identity security, SMBs, data breaches, technological adoption, regulatory environment
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Cognitive Bias Stress Test: Structured challenge to expose and correct biases.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us