Capacity is Critical in Riskier Threat Landscape – Trendmicro.com
Published on: 2025-04-04
Intelligence Report: Capacity is Critical in Riskier Threat Landscape – Trendmicro.com
1. BLUF (Bottom Line Up Front)
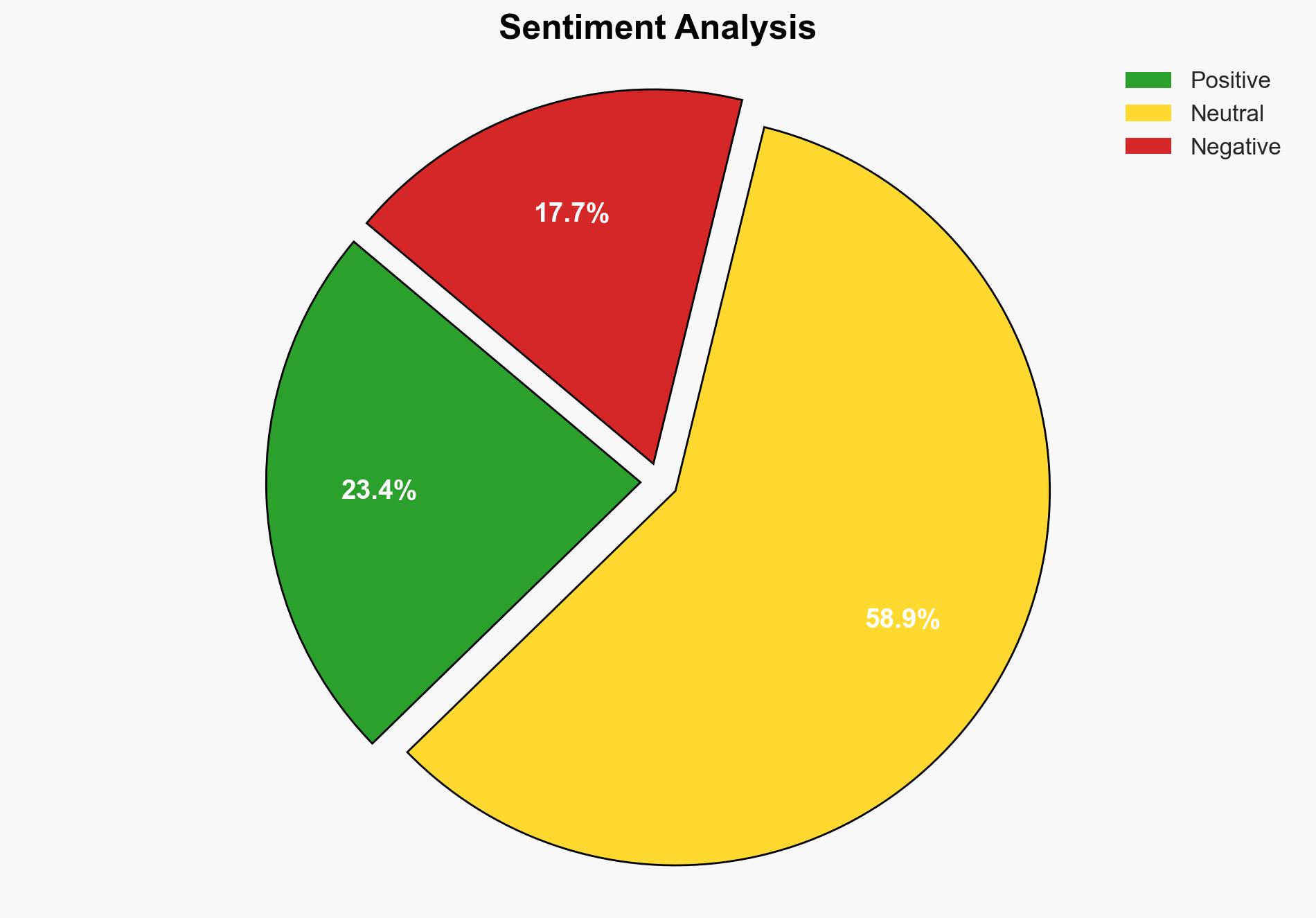
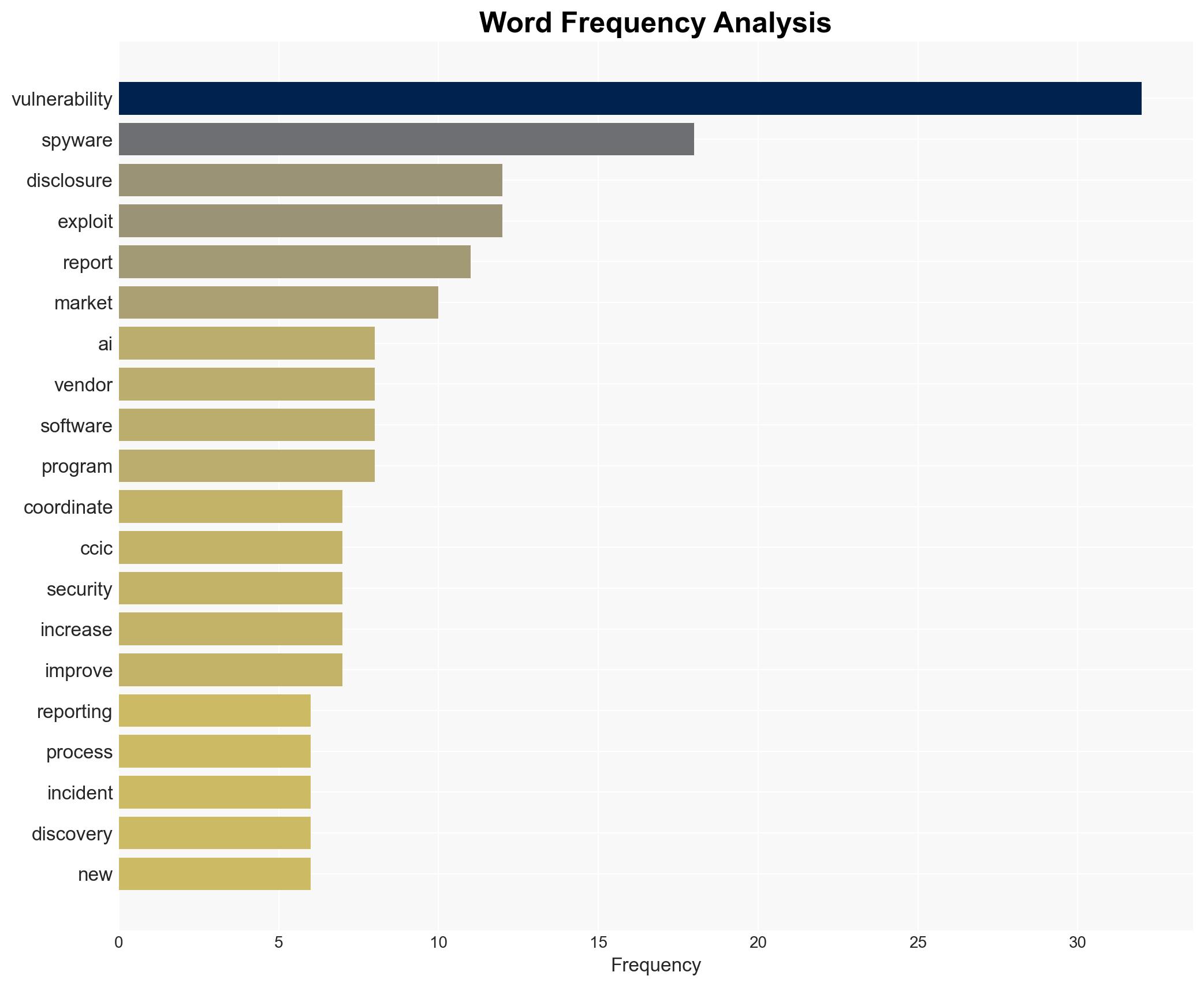
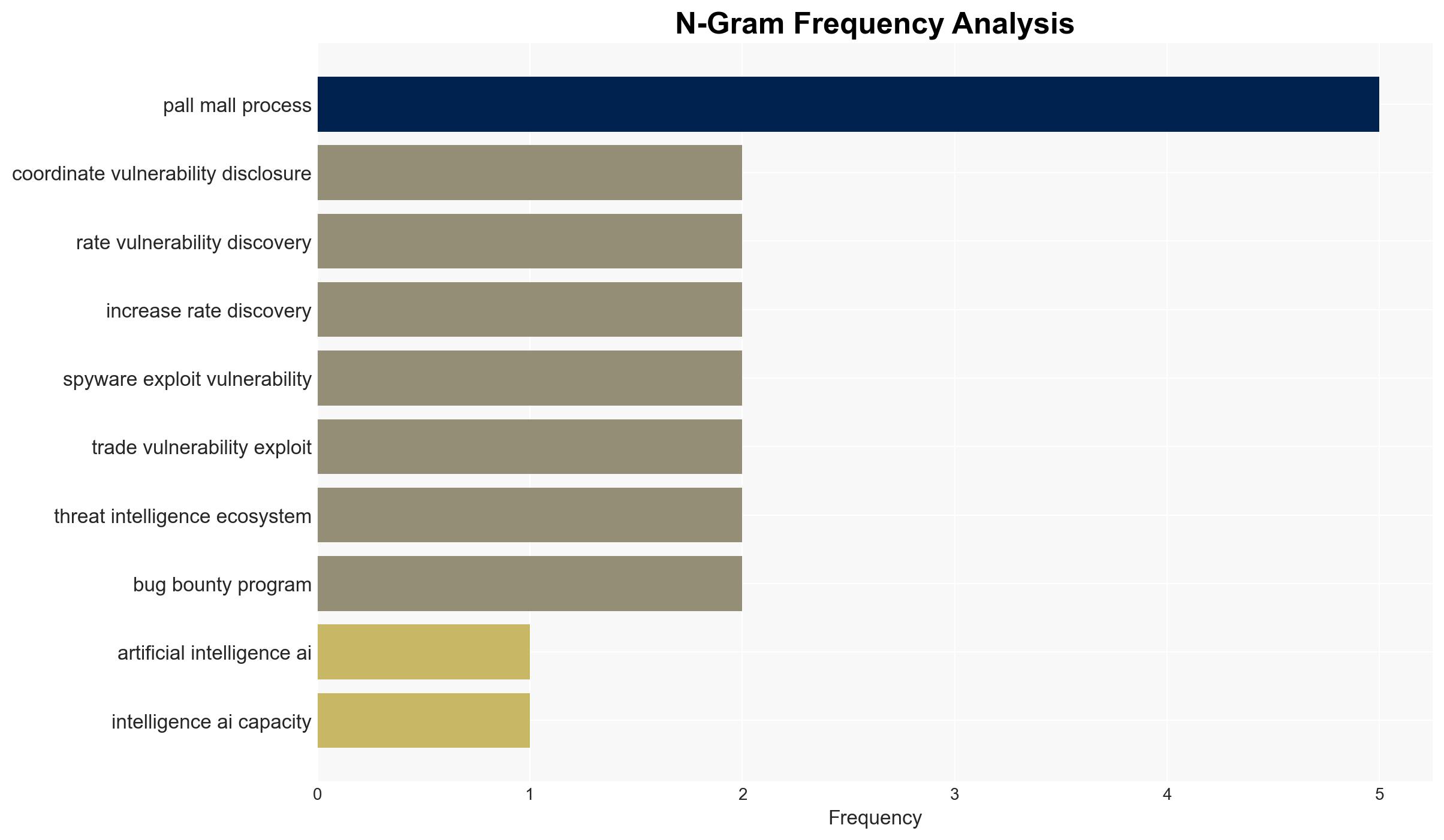
The current cybersecurity landscape is increasingly risky, necessitating enhanced capacity and international cooperation. Key findings indicate a rise in cyber intrusion capabilities and a growing concern over spyware proliferation. The report underscores the importance of coordinated vulnerability disclosure and the need for effective governance to mitigate these threats. Recommendations focus on improving cybersecurity defenses and promoting ethical vulnerability research.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
The threat landscape is characterized by an increase in vulnerability discovery and exploitation, driven by advancements in artificial intelligence. The proliferation of commercial cyber intrusion capabilities, such as spyware, poses significant risks to individual privacy, human rights, and national security. Despite legal actions against entities like NSO Group, the spyware market continues to adapt and expand. The emergence of agentic AI tools has lowered the bar for vulnerability discovery, complicating efforts to secure software systems.
3. Implications and Strategic Risks
The rise in cyber threats has significant implications for national security, regional stability, and economic interests. The fragmentation in vulnerability disclosure and the ongoing trade in spyware exacerbate these risks. The lack of coordinated efforts in vulnerability management and the ethical challenges in vulnerability research further complicate the cybersecurity landscape. These factors contribute to a heightened risk environment that requires immediate attention from policymakers and industry leaders.
4. Recommendations and Outlook
Recommendations:
- Enhance international cooperation to improve visibility and coordination in vulnerability disclosure.
- Promote ethical vulnerability research and establish robust bug bounty programs to incentivize responsible disclosure.
- Implement regulatory frameworks to curb the proliferation of spyware and enforce stringent penalties for violations.
- Invest in advanced cybersecurity technologies and training to build capacity and resilience against emerging threats.
Outlook:
Best-case scenario: Enhanced international collaboration and regulatory measures lead to a reduction in cyber threats and improved cybersecurity resilience.
Worst-case scenario: Continued fragmentation in vulnerability disclosure and unchecked spyware proliferation result in significant breaches and geopolitical tensions.
Most likely outcome: Incremental improvements in cybersecurity practices and international cooperation, with ongoing challenges in managing emerging threats.
5. Key Individuals and Entities
The report references significant individuals and organizations involved in the cybersecurity landscape. Notable mentions include NSO Group and New Yorker magazine, highlighting their roles in the context of spyware trade and vulnerability disclosure.