Chalker Played a Key Role in Preventing Iran’s Nuclear Weapons Development
Published on: 2026-03-30
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: He Helped Stop Iran from Getting the Bomb
1. BLUF (Bottom Line Up Front)
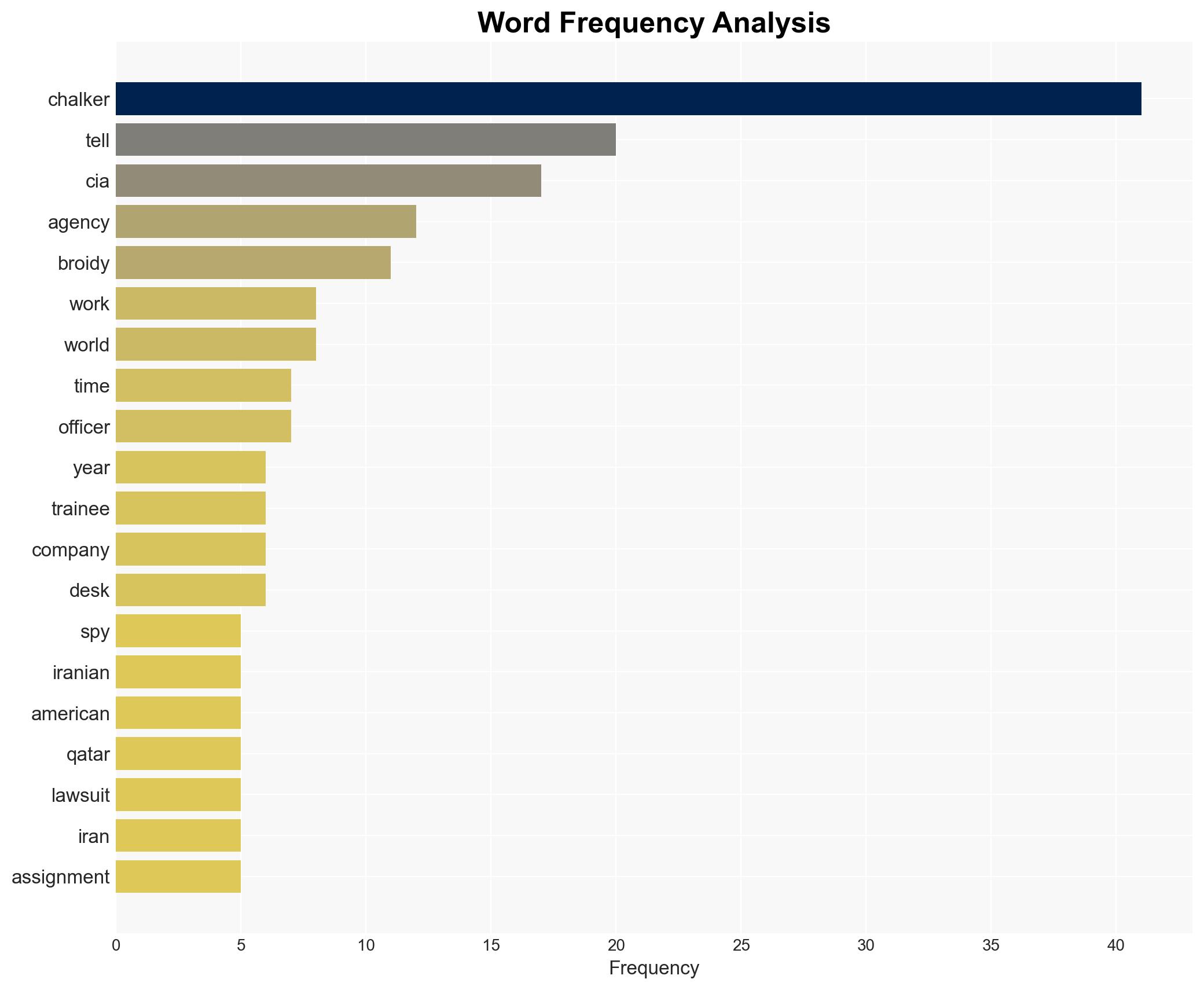
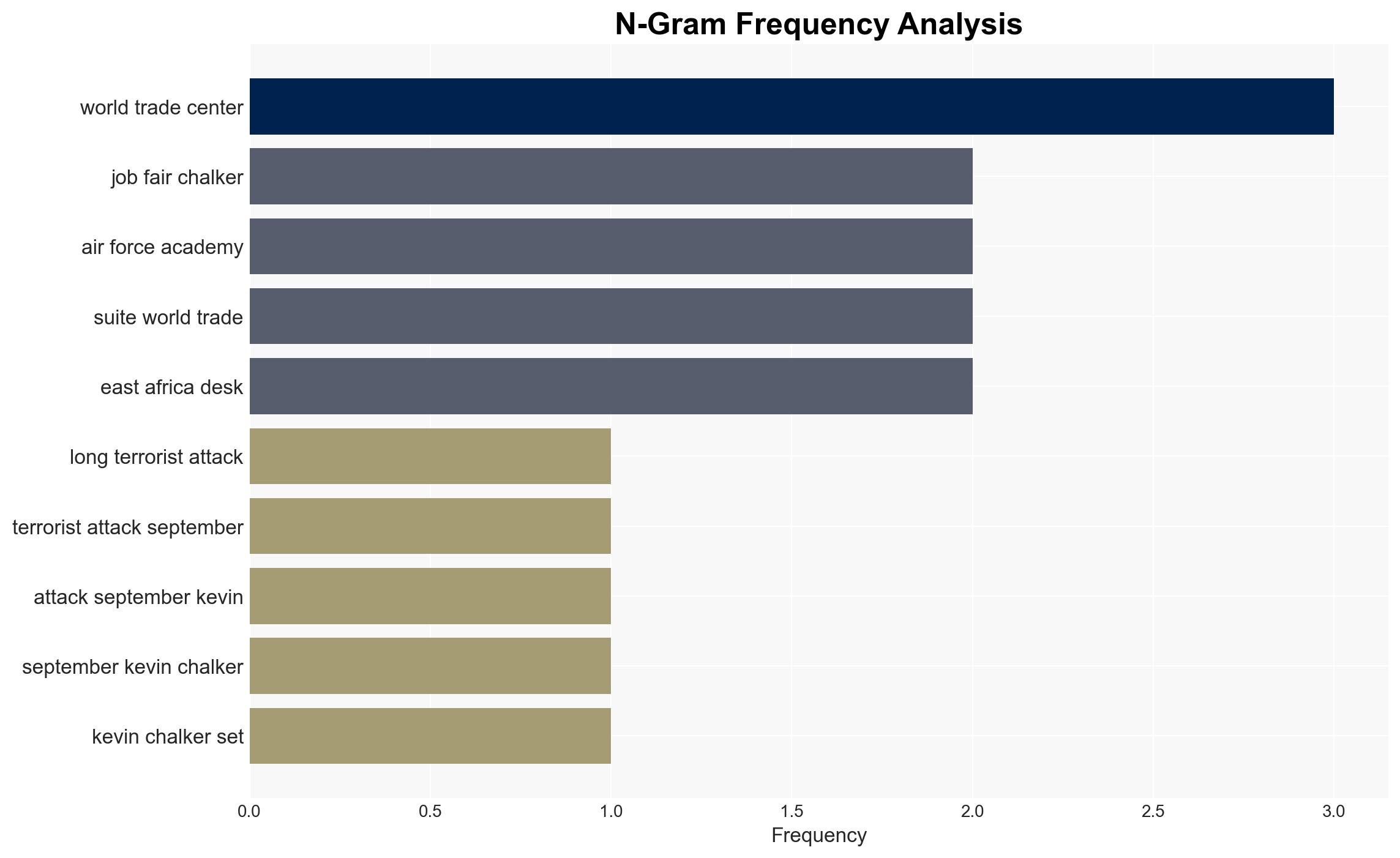
Kevin Chalker’s transition from a CIA operative to a security consultant for Qatar raises questions about potential cyber operations against U.S. interests. The most likely hypothesis is that Chalker leveraged his CIA background to conduct cyber activities on behalf of Qatar, possibly targeting U.S. entities. This situation affects U.S. national security and diplomatic relations with Qatar. Overall confidence in this assessment is moderate due to limited direct evidence from the snippet.
2. Competing Hypotheses
- Hypothesis A: Chalker used his CIA experience to conduct cyber operations against U.S. interests on behalf of Qatar. This is supported by the lawsuit filed by Elliott Broidy, which claims Chalker orchestrated cyberattacks. However, there is uncertainty regarding the extent of his involvement and the direct link to Qatar’s government.
- Hypothesis B: Chalker’s activities were legitimate security consulting services unrelated to cyber operations against U.S. interests. This could be supported by the lack of direct evidence linking him to the alleged cyberattacks, suggesting the lawsuit may be politically motivated or based on misinterpretation.
- Assessment: Hypothesis A is currently better supported due to the lawsuit’s specific allegations and Chalker’s background in cyber operations. Key indicators that could shift this judgment include new evidence of direct orders from Qatar or further legal developments.
3. Key Assumptions and Red Flags
- Assumptions: Chalker maintained operational capabilities from his CIA tenure; Qatar has interests in conducting cyber operations against U.S. entities; the lawsuit’s claims are based on credible evidence.
- Information Gaps: Details on Chalker’s specific activities for Qatar, evidence of direct Qatari government involvement, and the outcome of the lawsuit.
- Bias & Deception Risks: Potential bias in the lawsuit due to political motivations; risk of deception in public statements by involved parties.
4. Implications and Strategic Risks
The development could strain U.S.-Qatar relations and influence cyber policy discussions. It may also impact the operational landscape for former intelligence operatives in private sectors.
- Political / Geopolitical: Potential diplomatic tensions between the U.S. and Qatar, affecting bilateral cooperation.
- Security / Counter-Terrorism: Increased scrutiny on former intelligence personnel in private security roles.
- Cyber / Information Space: Heightened awareness and potential policy shifts regarding cyber operations conducted by private entities.
- Economic / Social: Possible impacts on the security consulting industry and its regulatory environment.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor legal proceedings for new evidence; engage with Qatari counterparts to clarify intentions and mitigate tensions.
- Medium-Term Posture (1–12 months): Develop frameworks for oversight of private security firms employing former intelligence personnel; strengthen cyber defense collaborations with allies.
- Scenario Outlook:
- Best: Resolution of legal issues with no diplomatic fallout.
- Worst: Escalation leading to significant diplomatic rift and regulatory crackdowns on private security firms.
- Most-Likely: Continued legal proceedings with moderate diplomatic engagement to manage tensions.
6. Key Individuals and Entities
- Kevin Chalker – Former CIA operative, security consultant
- Elliott Broidy – Investor and political donor
- Qatar – Alleged client of Chalker’s consulting firm
- Not clearly identifiable from open sources in this snippet – Other potential individuals/entities involved
7. Thematic Tags
cybersecurity, cyber-espionage, national security, U.S.-Qatar relations, intelligence operations, private security sector, legal proceedings, diplomatic tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us