China-linked espionage operation CL-STA-1087 has targeted Southeast Asian military entities since 2020
Published on: 2026-03-17
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: CL-STA-1087 targets military capabilities since 2020
1. BLUF (Bottom Line Up Front)
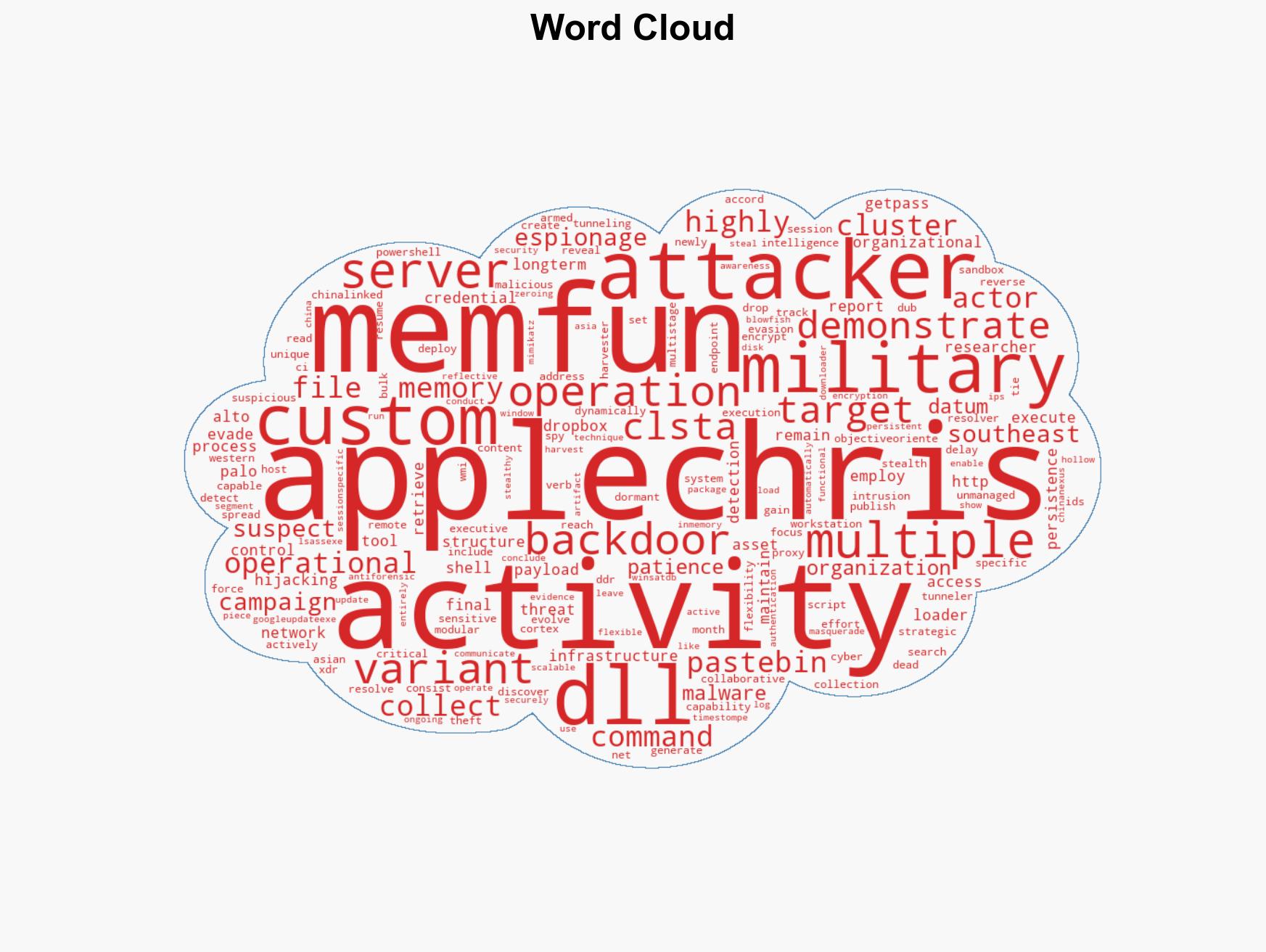
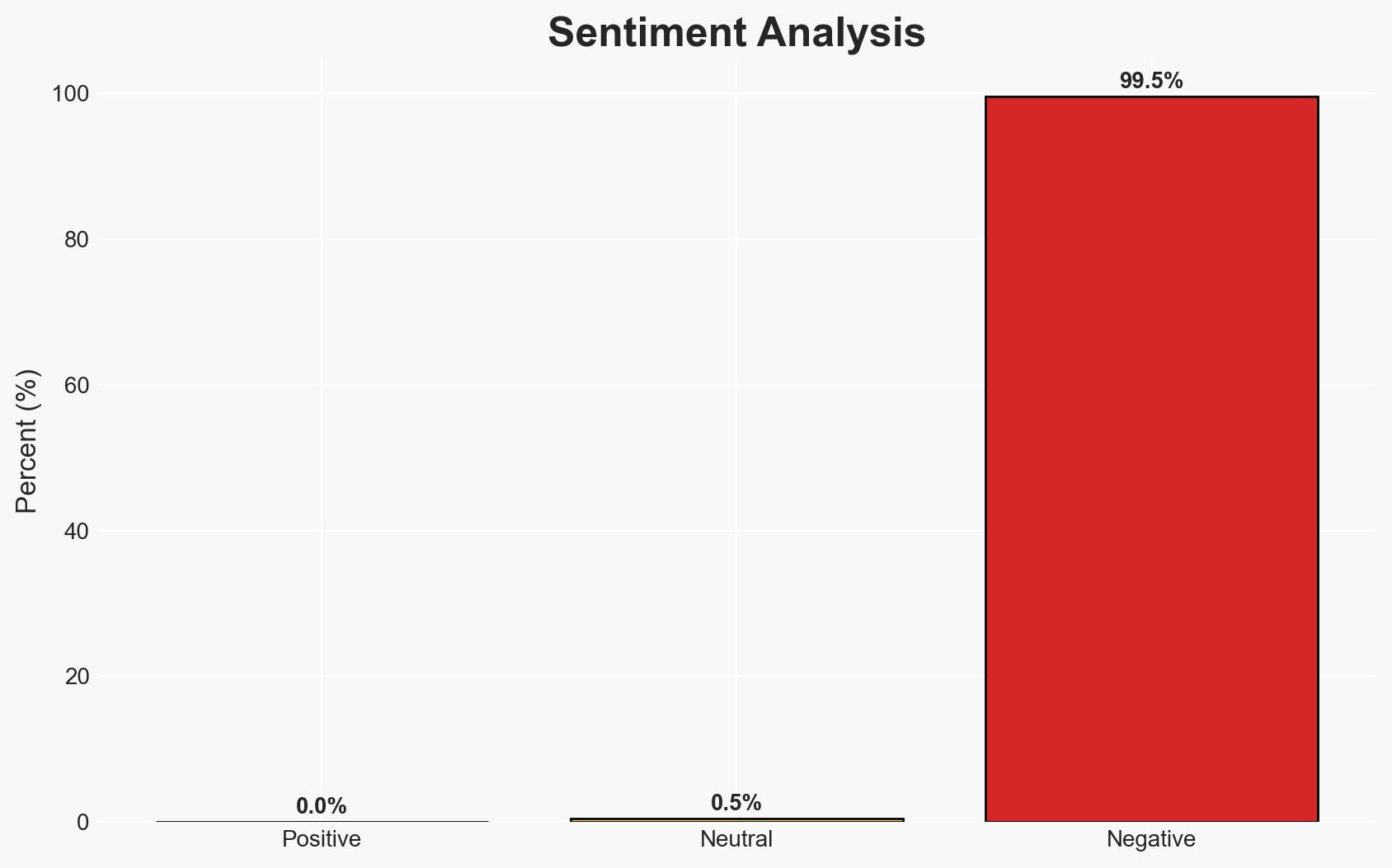
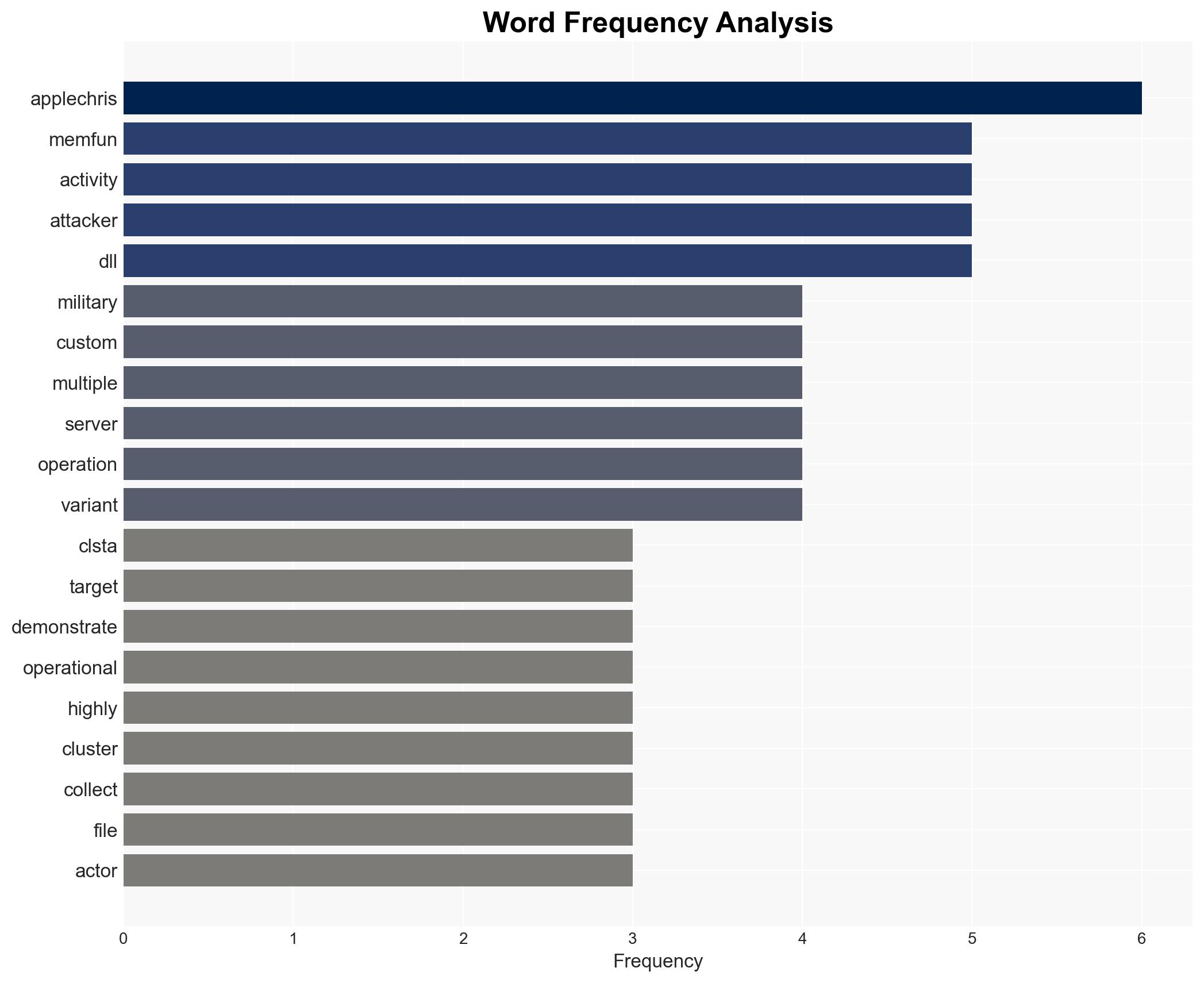
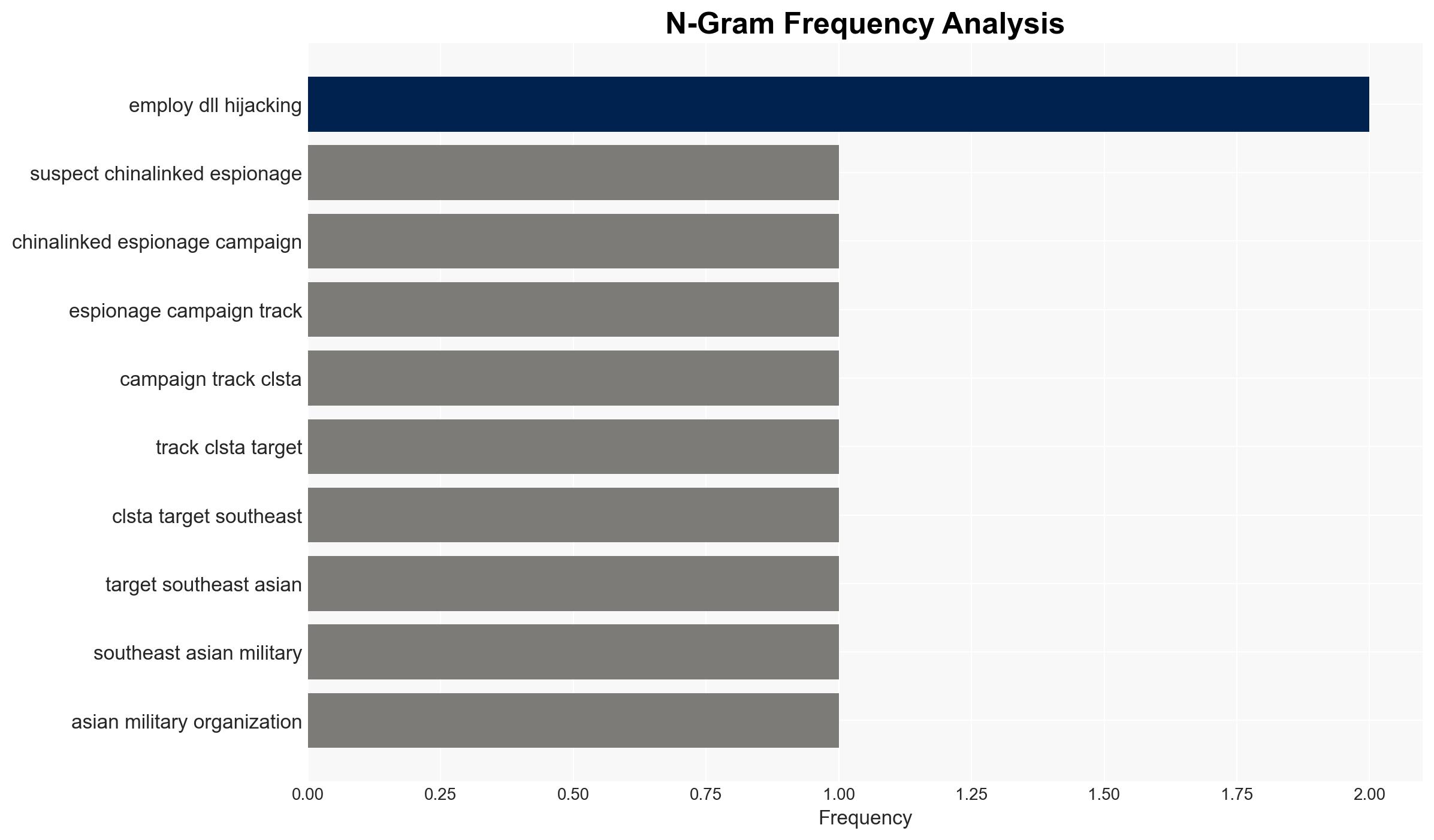
The CL-STA-1087 espionage campaign, likely linked to China, has been targeting Southeast Asian military organizations since 2020 using sophisticated malware such as AppleChris and MemFun. The campaign focuses on collecting intelligence on military capabilities and collaborations with Western forces. The overall confidence in this assessment is moderate due to the complexity of the operations and the potential for misattribution.
2. Competing Hypotheses
- Hypothesis A: CL-STA-1087 is a China-sponsored espionage operation aimed at gathering intelligence on Southeast Asian military capabilities and alliances. This is supported by the use of advanced malware and strategic targeting, but lacks direct attribution evidence.
- Hypothesis B: CL-STA-1087 could be a non-state actor or another nation-state masquerading as China to mislead attribution efforts. This is less supported due to the sophistication and resource intensity of the campaign, which aligns with state-sponsored capabilities.
- Assessment: Hypothesis A is currently better supported due to the alignment of tactics and objectives with known Chinese cyber-espionage patterns. However, further attribution evidence could shift this assessment.
3. Key Assumptions and Red Flags
- Assumptions: The campaign’s objectives are aligned with state-level strategic interests; the malware used is uniquely developed for this operation; the infrastructure is controlled by the attackers.
- Information Gaps: Direct evidence linking the campaign to Chinese state actors; comprehensive understanding of the full scope of targeted entities.
- Bias & Deception Risks: Attribution bias due to pre-existing narratives about Chinese cyber activities; potential for false-flag operations designed to mislead attribution.
4. Implications and Strategic Risks
The continuation of CL-STA-1087 could exacerbate regional tensions and influence military alliances in Southeast Asia. The campaign’s success may embolden similar operations, affecting global cyber stability.
- Political / Geopolitical: Escalation of cyber tensions between China and Southeast Asian nations, potentially drawing in Western allies.
- Security / Counter-Terrorism: Increased vulnerability of military networks, necessitating enhanced cybersecurity measures.
- Cyber / Information Space: Potential for increased cyber operations targeting military and critical infrastructure sectors.
- Economic / Social: Indirect effects on regional economic stability due to heightened geopolitical tensions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of military networks for indicators of compromise; collaborate with international partners for intelligence sharing.
- Medium-Term Posture (1–12 months): Develop resilience measures, including advanced threat detection capabilities and incident response protocols; strengthen alliances through joint cybersecurity exercises.
- Scenario Outlook: Best: Improved regional cybersecurity cooperation mitigates threats. Worst: Escalation leads to broader geopolitical conflict. Most-Likely: Continued low-level cyber engagements with periodic escalations.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cyber-espionage, military intelligence, Southeast Asia, China, malware, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us