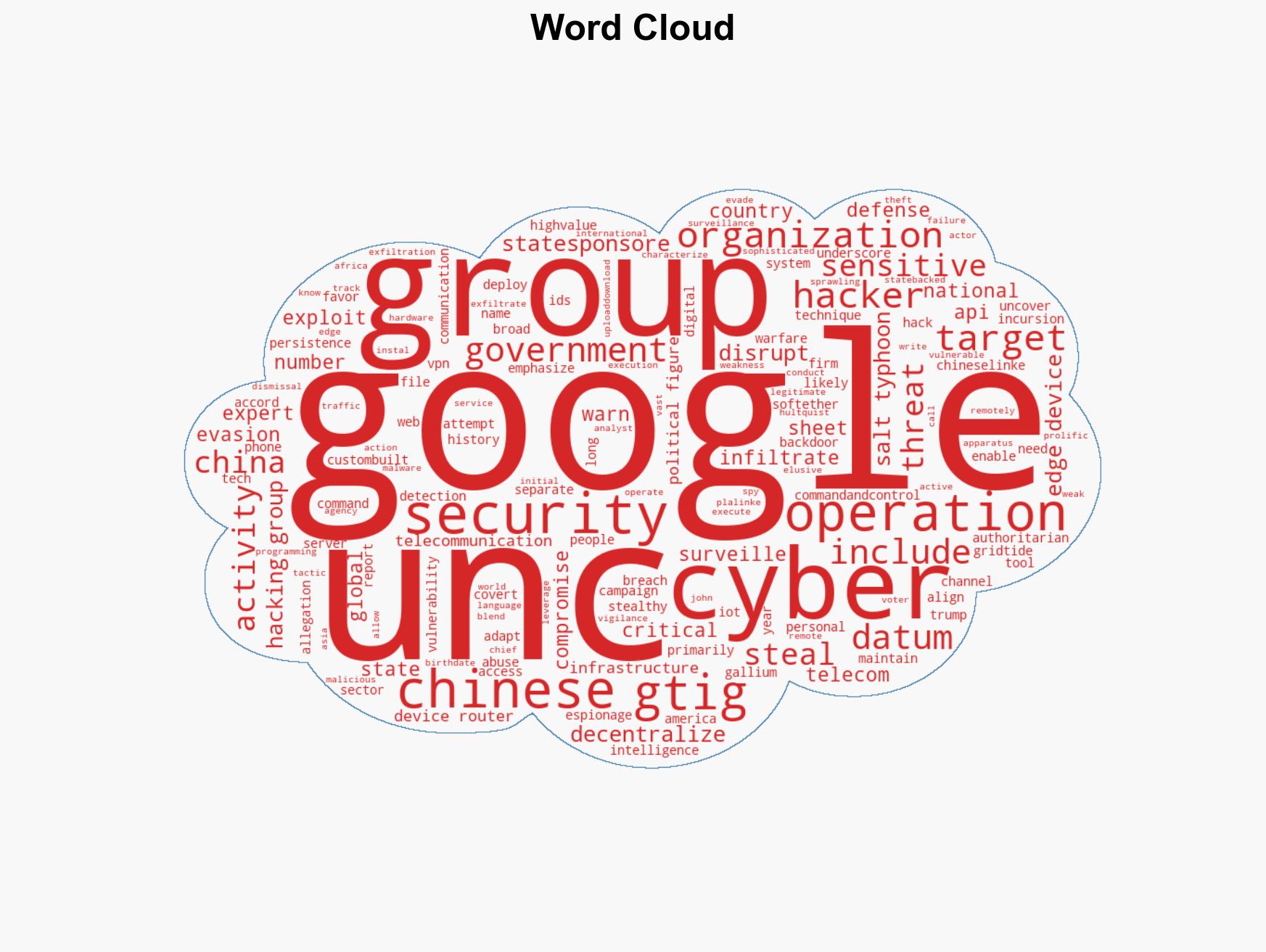
Chinese Hacking Group UNC2814 Compromises 53 Organizations Across 42 Countries, Stealing Sensitive Data
Published on: 2026-02-28
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Google exposes MASSIVE Chinese cyber espionage campaign targeting 42 countries
1. BLUF (Bottom Line Up Front)
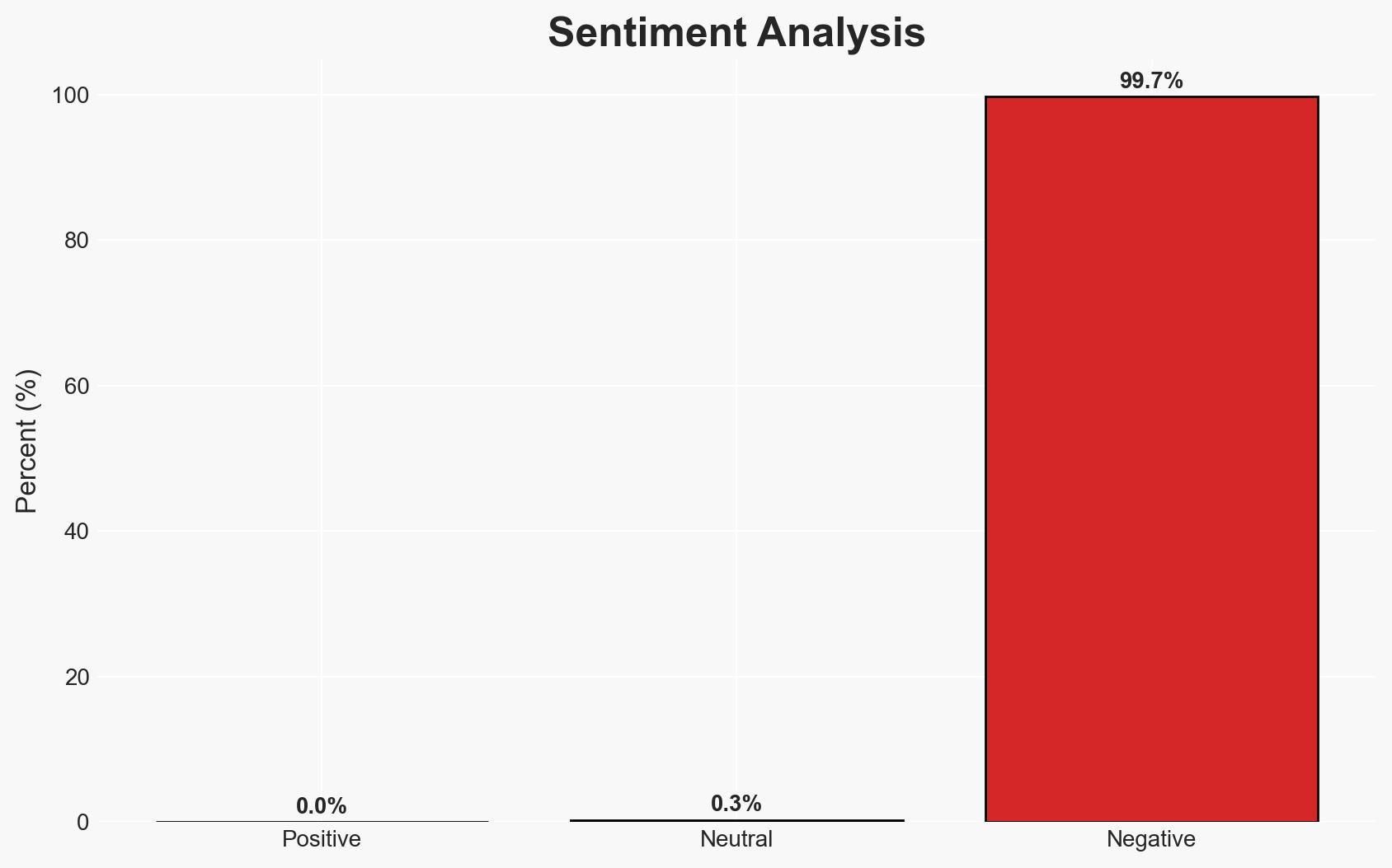
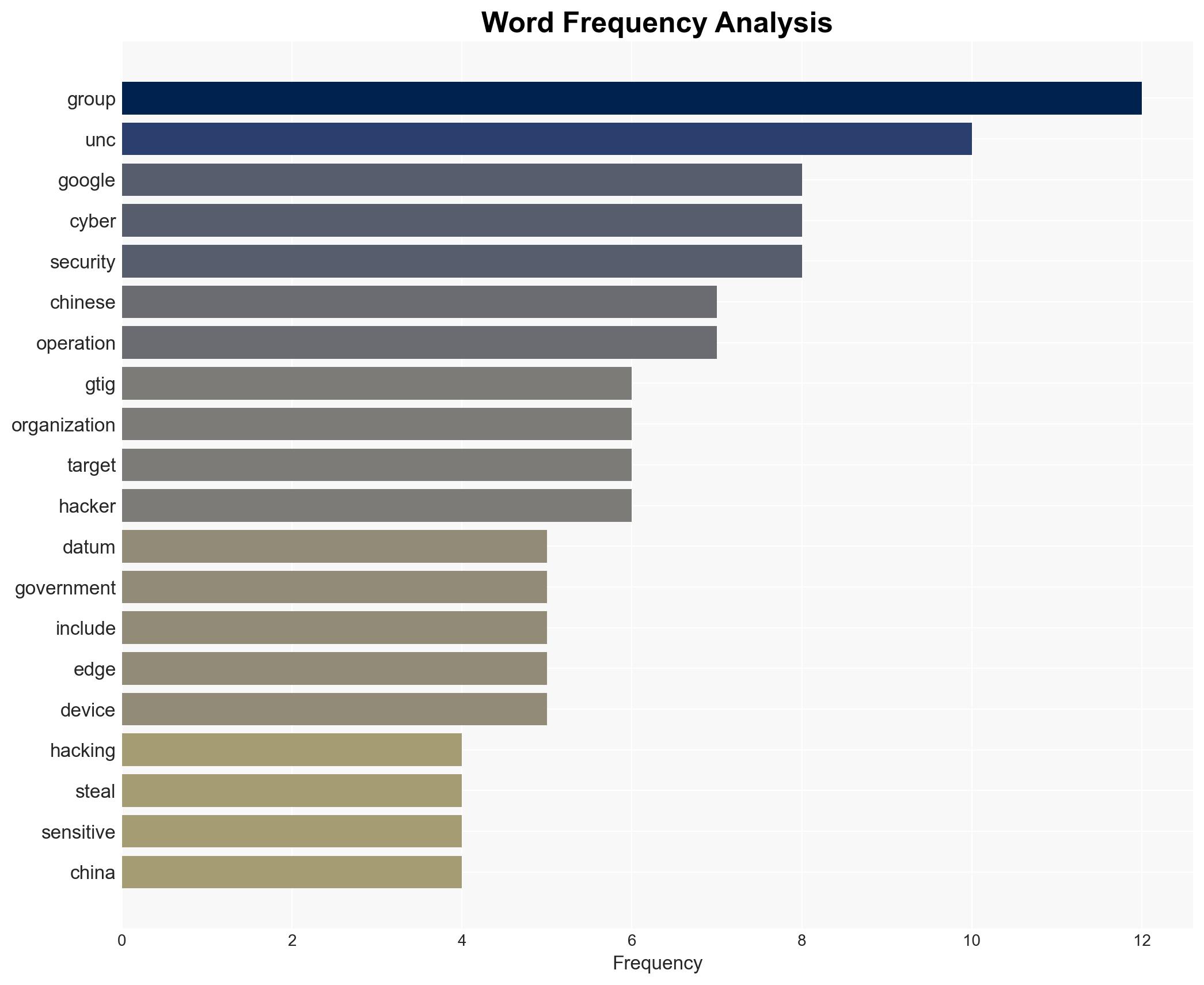
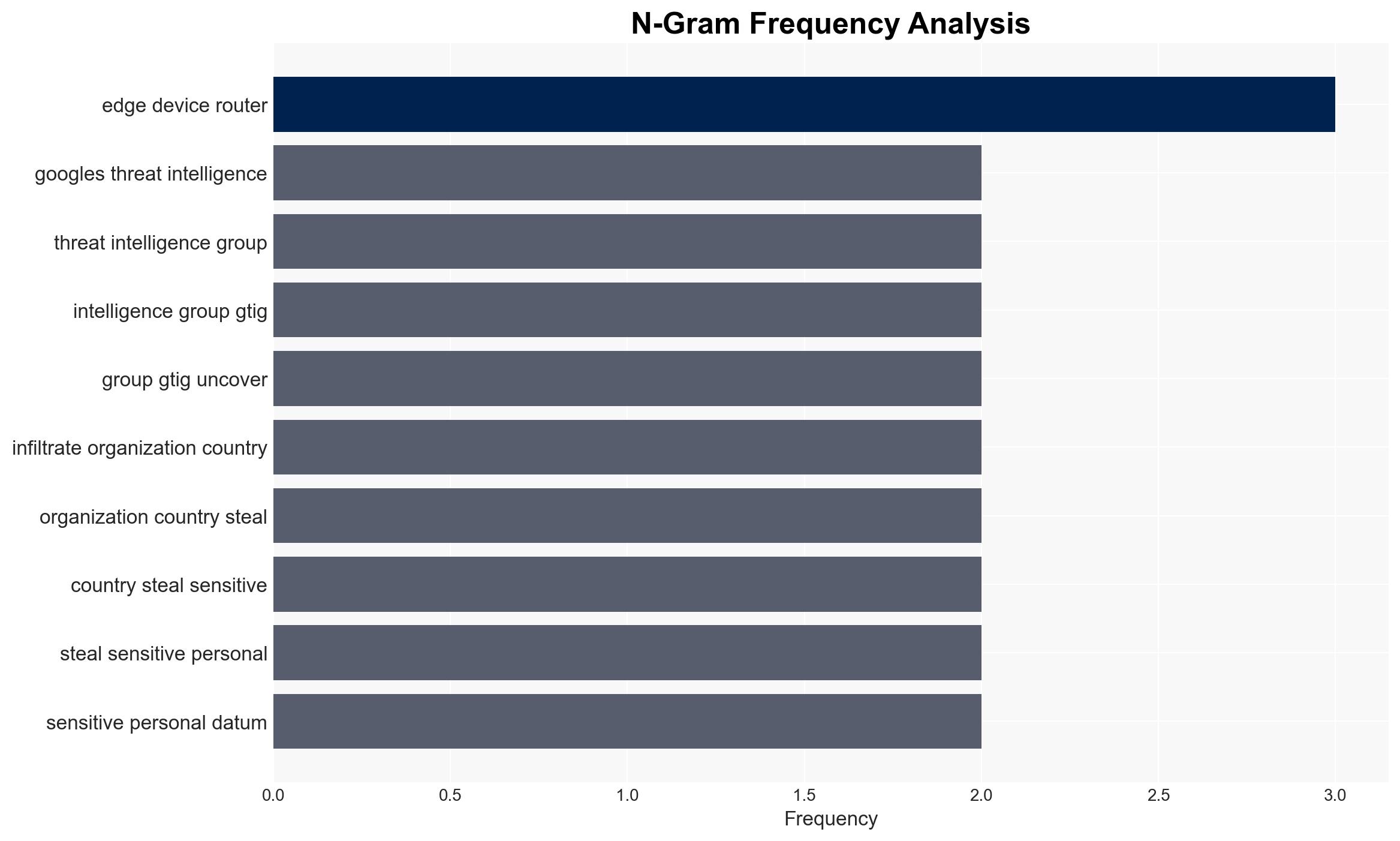
Google’s Threat Intelligence Group has identified a significant cyber espionage campaign by Chinese-linked group UNC2814, targeting telecom and government sectors across 42 countries. The campaign, active since 2017, exploited edge device vulnerabilities to exfiltrate sensitive data. The most likely hypothesis is that this operation is state-sponsored, aligning with broader Chinese cyber warfare strategies. Overall confidence in this assessment is moderate, given the alignment with known patterns of Chinese cyber activities.
2. Competing Hypotheses
- Hypothesis A: UNC2814 is a state-sponsored Chinese cyber espionage group targeting global telecom and government sectors to gather intelligence. This is supported by the use of sophisticated techniques and tools commonly associated with state-backed actors. However, China’s denial of involvement introduces uncertainty.
- Hypothesis B: UNC2814 is an independent cybercriminal group exploiting vulnerabilities for financial gain, not directly linked to state sponsorship. This hypothesis is less supported due to the strategic nature of targets and the alignment with known Chinese cyber warfare tactics.
- Assessment: Hypothesis A is currently better supported due to the strategic targeting and sophisticated methods used, which are indicative of state-sponsored operations. Indicators such as further evidence of state involvement or changes in targeting patterns could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: UNC2814’s activities are aligned with Chinese state interests; the use of advanced techniques indicates state sponsorship; the targets were selected for strategic intelligence value.
- Information Gaps: Direct evidence of Chinese government involvement; comprehensive data on all compromised organizations; full scope of data exfiltrated.
- Bias & Deception Risks: Potential confirmation bias in attributing activities to China; source bias from Google’s perspective; possible Chinese misinformation or denial strategies.
4. Implications and Strategic Risks
This development could lead to increased geopolitical tensions and a reevaluation of cyber defense strategies globally. The persistence of such campaigns highlights vulnerabilities in critical infrastructure.
- Political / Geopolitical: Potential escalation in cyber diplomacy tensions between China and affected countries.
- Security / Counter-Terrorism: Heightened threat environment for telecom and government sectors; increased focus on securing edge devices.
- Cyber / Information Space: Likely adaptation and evolution of cyber tactics by state-sponsored groups; increased emphasis on cyber defense and intelligence sharing.
- Economic / Social: Potential economic impacts due to data breaches; erosion of trust in digital infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of edge devices; conduct thorough security audits; increase intelligence sharing among affected countries.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical infrastructure; strengthen international cyber defense partnerships; invest in cybersecurity capabilities.
- Scenario Outlook: Best: Strengthened global cyber defenses reduce future incidents. Worst: Escalation of cyber conflicts and increased state-sponsored activities. Most-Likely: Continued adaptation by cyber actors with sporadic high-profile breaches.
6. Key Individuals and Entities
- Google’s Threat Intelligence Group (GTIG)
- UNC2814 (Gallium)
- John Hultquist, GTIG Chief Analyst
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cyber-espionage, state-sponsored hacking, telecommunications security, Chinese cyber operations, data exfiltration, international cybersecurity, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us