Chinese-linked breach of FBI system potentially exposes monitored targets’ phone numbers
Published on: 2026-04-03
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Suspected Chinese breach of FBI system exposed surveillance targets phone numbers
1. BLUF (Bottom Line Up Front)
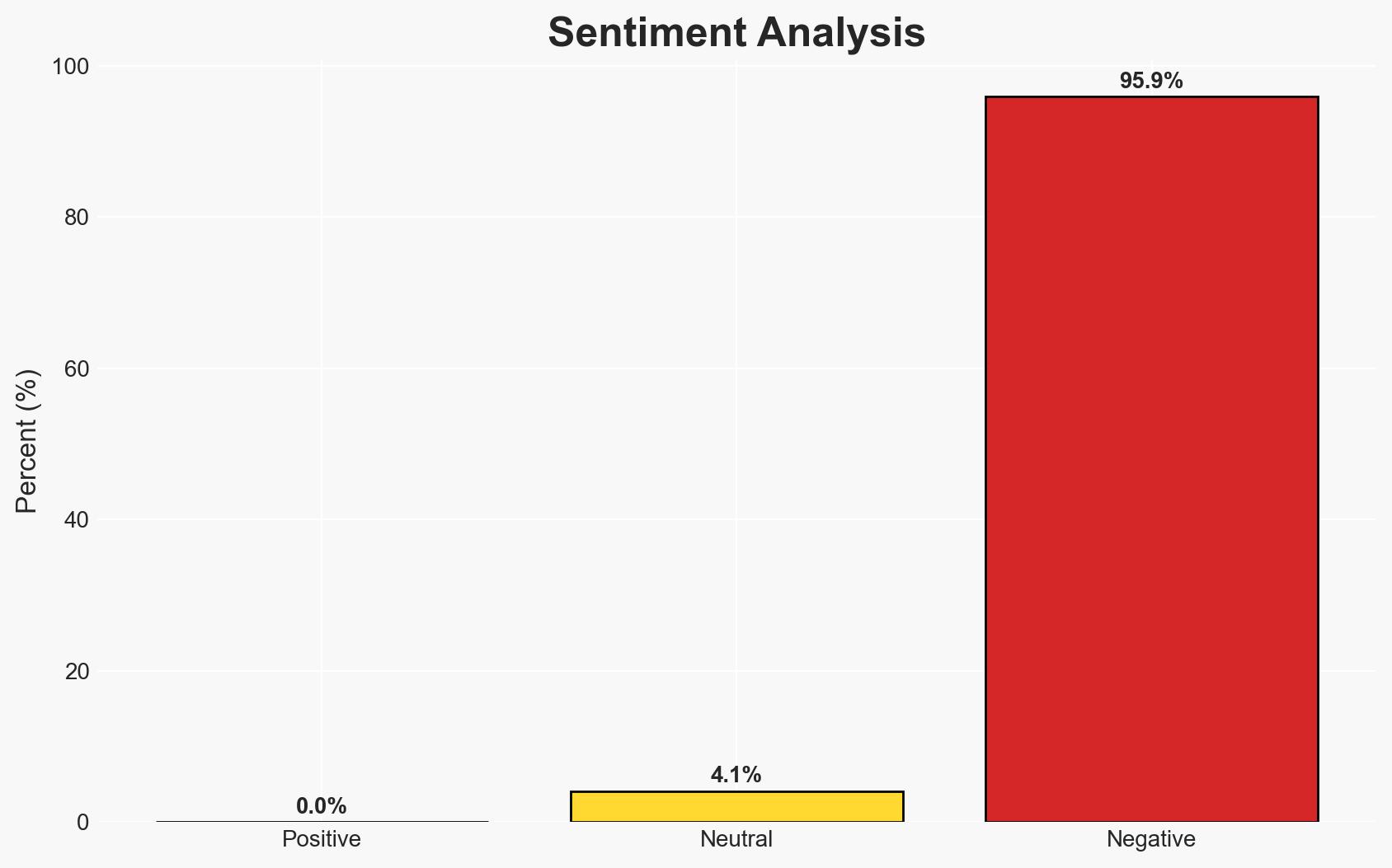
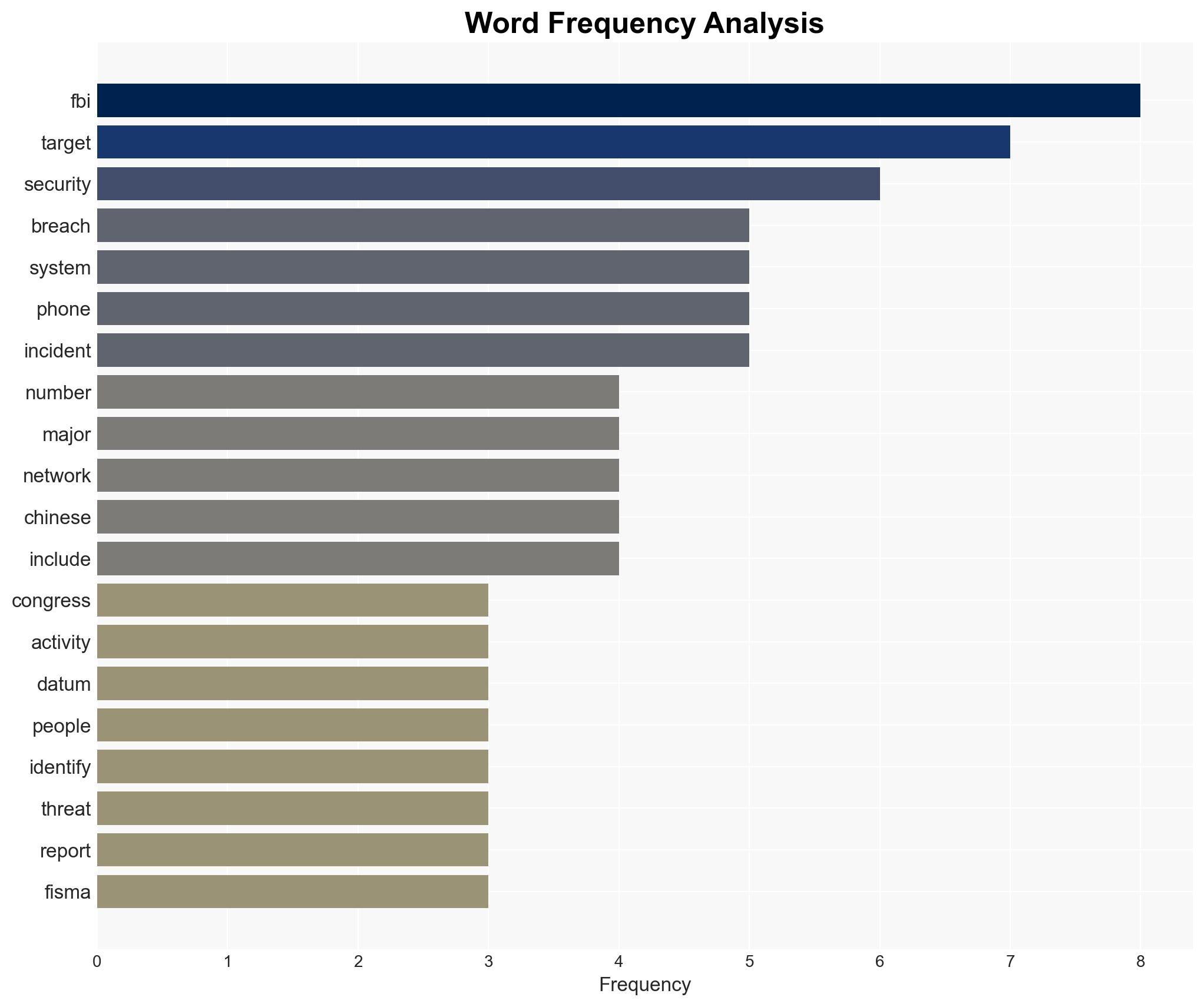
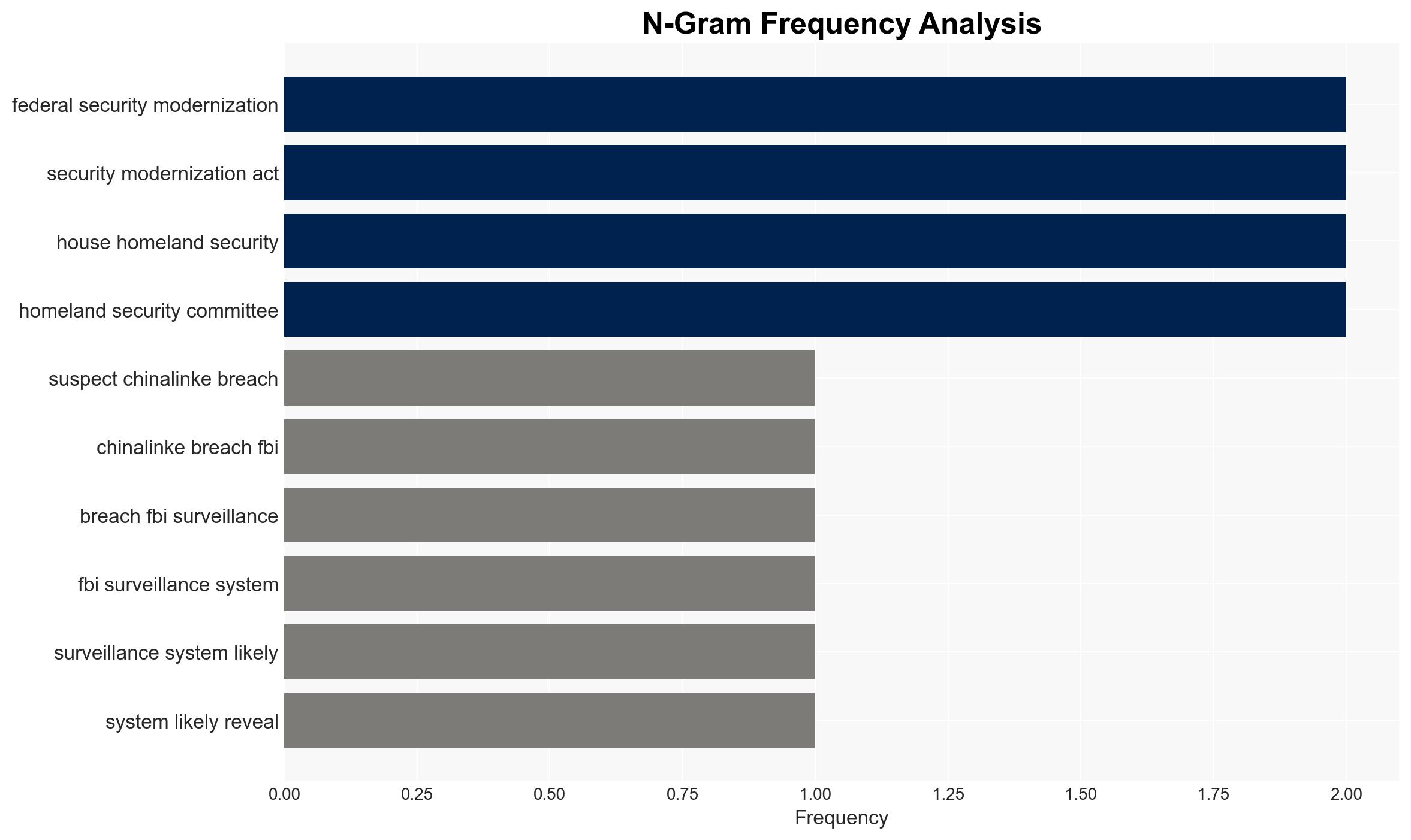
The FBI’s unclassified surveillance system was reportedly breached, potentially exposing phone numbers of surveillance targets. This incident is suspected to be linked to Chinese threat actors, posing significant counterintelligence risks. The breach’s attribution to China is not definitively confirmed, and remediation efforts are ongoing. Overall confidence in this judgment is moderate due to the lack of independently verified attribution.
2. Competing Hypotheses
- Hypothesis A: The breach was conducted by Chinese state-sponsored actors to gain insights into U.S. surveillance operations. Supporting evidence includes reports of a suspected Chinese nexus and the strategic interest China has in understanding U.S. counterintelligence efforts. Contradicting evidence includes the lack of independent confirmation of Chinese involvement.
- Hypothesis B: The breach was conducted by non-state actors or another nation-state with interests in U.S. surveillance operations. Supporting evidence includes the general interest multiple adversaries have in U.S. intelligence activities. The lack of specific indicators pointing exclusively to China supports this hypothesis.
- Assessment: Hypothesis A is currently better supported due to the reported suspected Chinese link and the strategic value such information would hold for China. However, further confirmation is needed to solidify this assessment. Indicators that could shift this judgment include verified technical forensics linking the breach to Chinese infrastructure or actors.
3. Key Assumptions and Red Flags
- Assumptions: The breach was executed with the intent to gather intelligence on U.S. surveillance targets; the exposed data could be used to map relationships and networks; the breach was facilitated through a third-party vulnerability.
- Information Gaps: Lack of detailed forensic evidence linking the breach to specific actors; absence of information on the full extent of data accessed or compromised.
- Bias & Deception Risks: Potential source bias due to reliance on unnamed individuals familiar with the matter; risk of deception if the breach is a false flag operation designed to mislead attribution efforts.
4. Implications and Strategic Risks
The breach could have significant implications for U.S. national security and counterintelligence operations, potentially compromising ongoing investigations and surveillance efforts.
- Political / Geopolitical: Escalation in U.S.-China tensions, potential diplomatic repercussions, and increased scrutiny of Chinese cyber activities.
- Security / Counter-Terrorism: Compromised surveillance operations may hinder counterintelligence efforts and expose U.S. vulnerabilities.
- Cyber / Information Space: Increased focus on securing unclassified systems and third-party vulnerabilities; potential for retaliatory cyber operations.
- Economic / Social: Potential impact on public trust in government cybersecurity measures and increased demand for robust cybersecurity protocols.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive forensic investigation to confirm attribution; enhance monitoring of affected systems; notify potentially impacted individuals and entities.
- Medium-Term Posture (1–12 months): Strengthen partnerships with private sector cybersecurity firms; develop and implement improved security protocols for unclassified systems; increase intelligence-sharing with allies.
- Scenario Outlook:
- Best: Attribution is confirmed, and vulnerabilities are patched, leading to improved security posture.
- Worst: Breach leads to significant intelligence losses and escalates geopolitical tensions.
- Most-Likely: Ongoing remediation efforts mitigate immediate risks, but attribution remains inconclusive, maintaining moderate tension levels.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
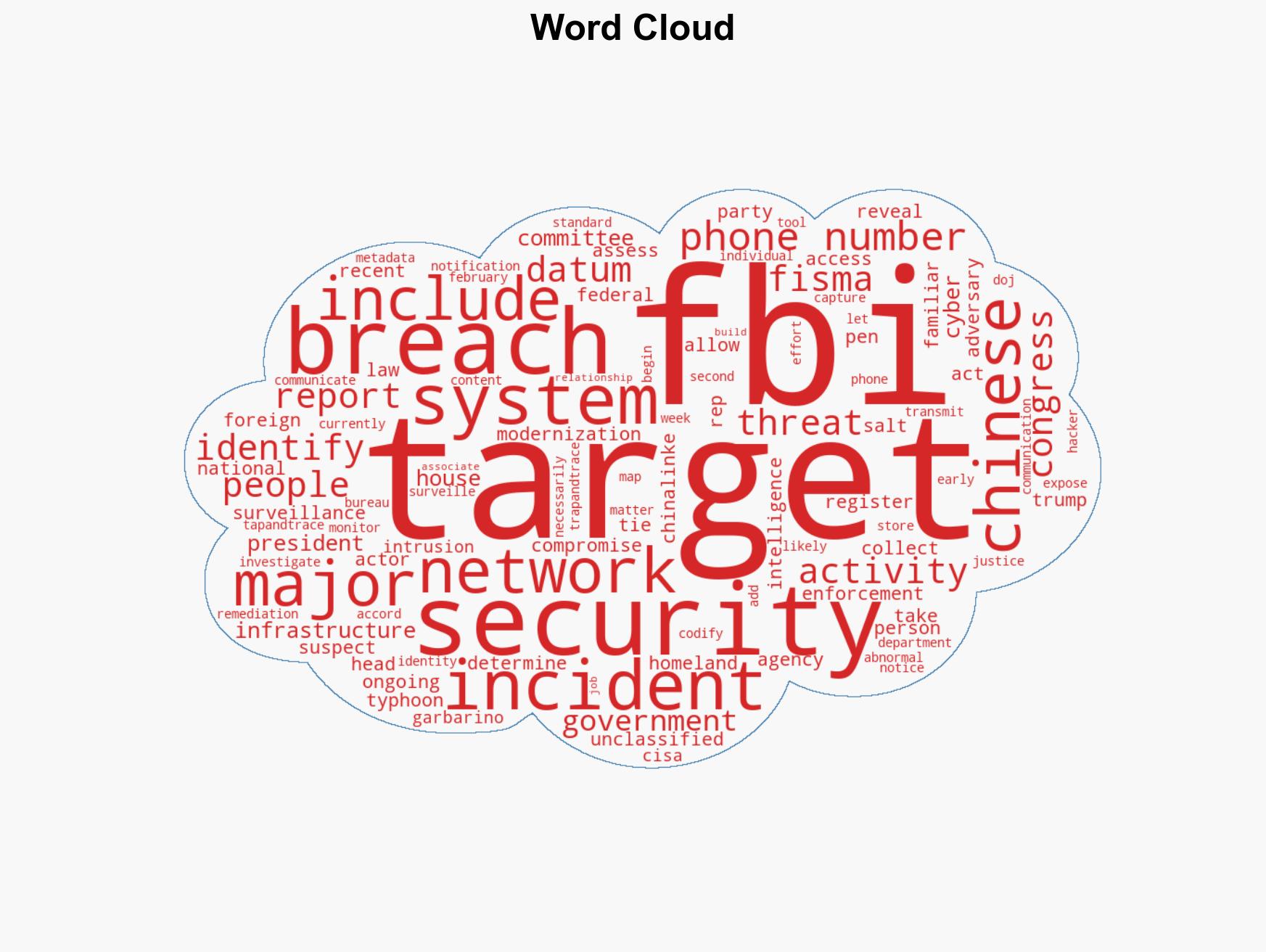
cybersecurity, counterintelligence, U.S.-China relations, surveillance, cyber-espionage, national security, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us