CISA alerts on iOS vulnerabilities exploited in spyware and cryptocurrency theft using Coruna exploit kit
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: CISA warns of Apple flaws exploited in spyware crypto-theft attacks
1. BLUF (Bottom Line Up Front)
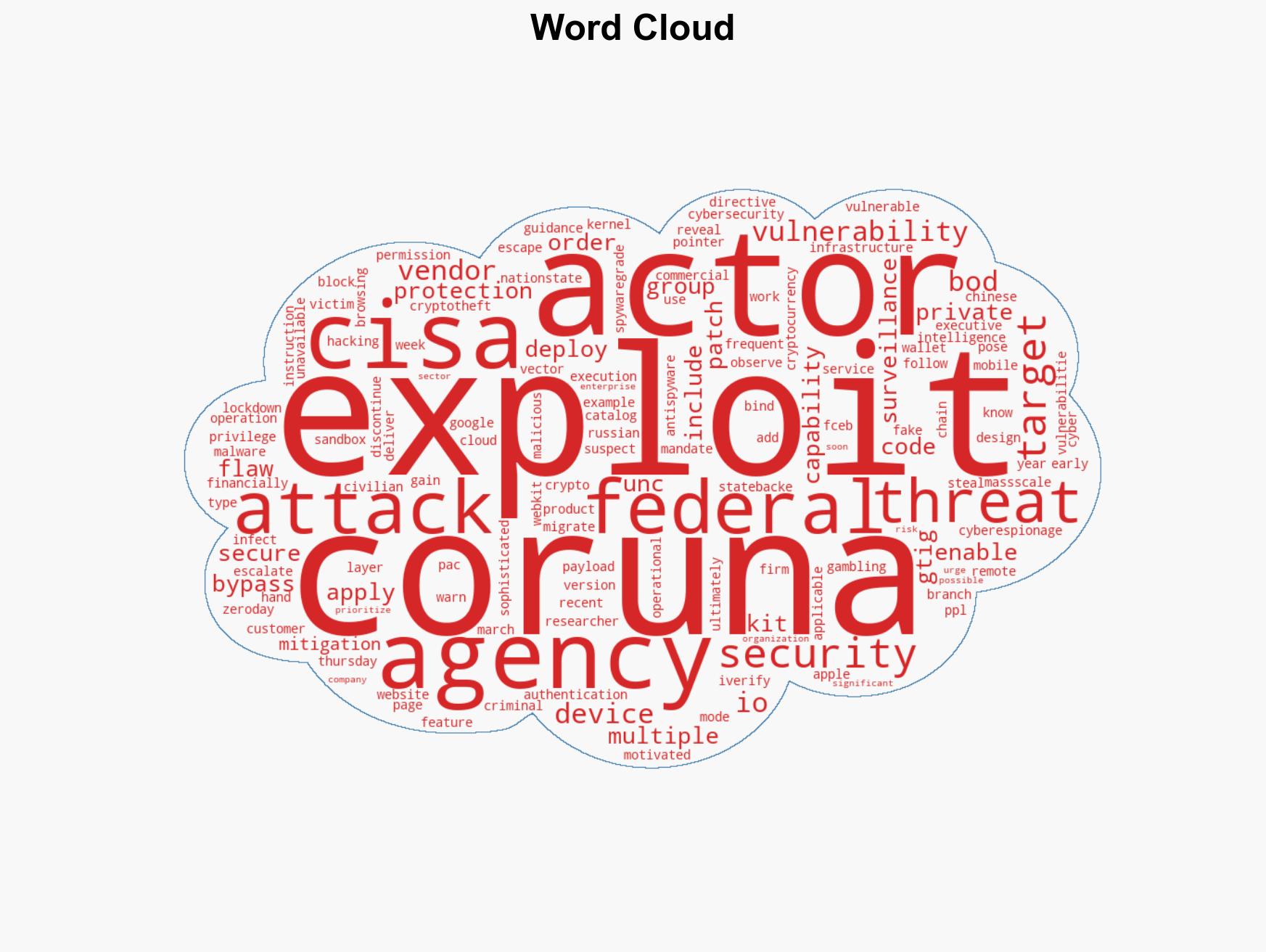
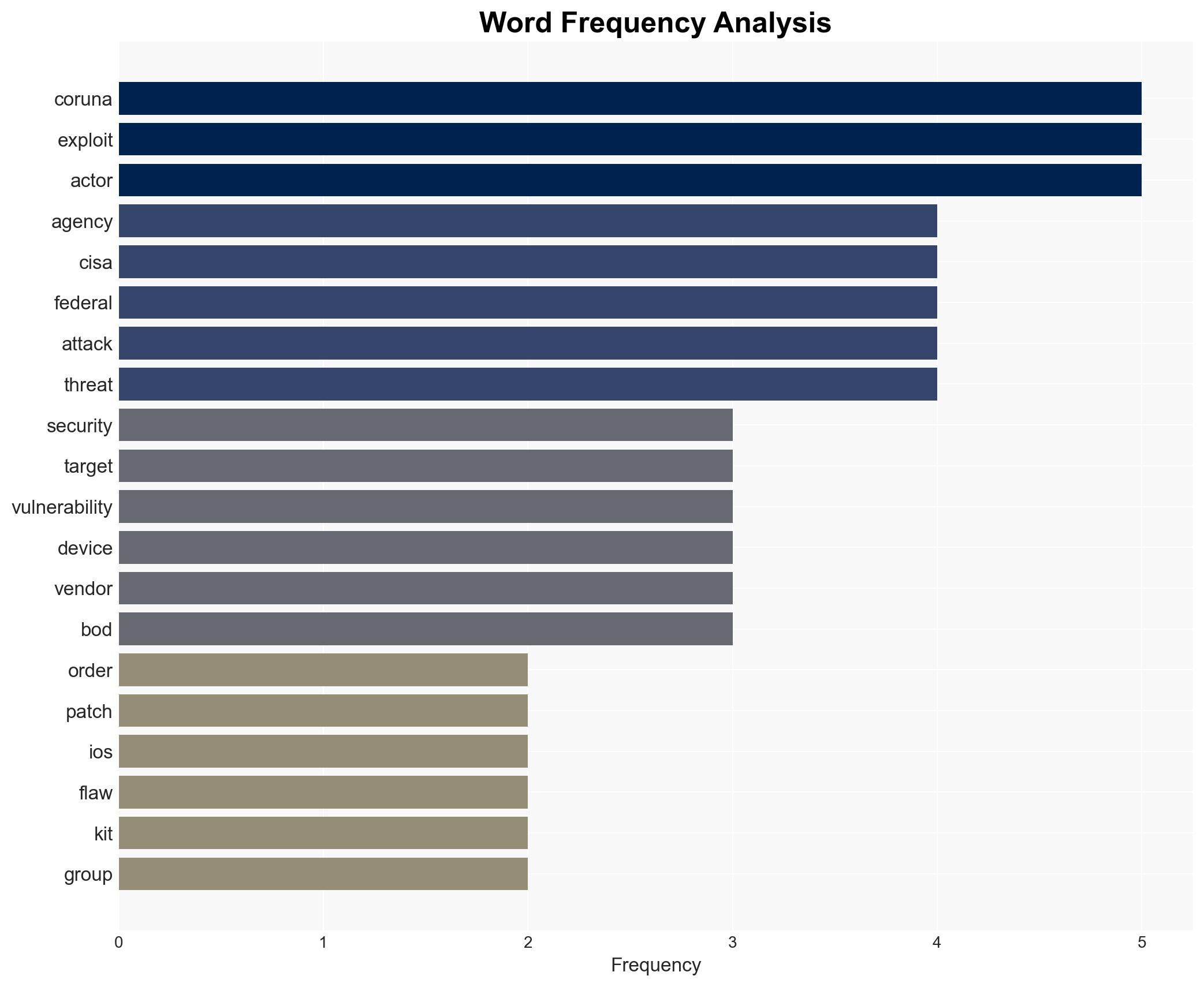
The Coruna exploit kit is actively being used to target iOS vulnerabilities, posing significant risks to both federal and private sector entities. The most likely hypothesis is that these attacks are driven by a mix of state-backed and financially motivated threat actors. The vulnerabilities are critical, but mitigations are available for recent iOS versions. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The Coruna exploit kit is primarily used by state-backed actors for cyberespionage. This is supported by the involvement of a suspected Russian state-backed group and the sophistication of the exploit kit. However, the presence of financially motivated actors suggests other motives.
- Hypothesis B: The Coruna exploit kit is predominantly used for financial gain by criminal organizations. The use of the exploit in fake gambling and crypto websites supports this, but the involvement of a surveillance vendor and state-backed actors contradicts a purely financial motive.
- Assessment: Hypothesis A is currently better supported due to the involvement of state-backed actors and the advanced capabilities of the exploit kit. Indicators such as increased targeting of government entities could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerabilities are not patched in all affected systems; state-backed actors have the capability to exploit these vulnerabilities; financial motives are a significant driver for some threat actors.
- Information Gaps: Specific details on the extent of exploitation and the full list of affected entities; the identity and motivations of all threat actors involved.
- Bias & Deception Risks: Potential bias in attributing attacks to state-backed actors without conclusive evidence; deception by threat actors to obscure true motives.
4. Implications and Strategic Risks
The exploitation of iOS vulnerabilities could lead to increased cyberespionage and financial theft, affecting national security and economic stability. The situation may evolve with further exploitation or discovery of additional vulnerabilities.
- Political / Geopolitical: Potential escalation of cyber tensions between the U.S. and state actors like Russia and China.
- Security / Counter-Terrorism: Increased risk of sensitive information being compromised, affecting national security operations.
- Cyber / Information Space: Potential for widespread cyber-attacks leveraging similar vulnerabilities, affecting public trust in digital security.
- Economic / Social: Financial losses from crypto-theft could undermine confidence in digital currencies and platforms.
5. Recommendations and Outlook
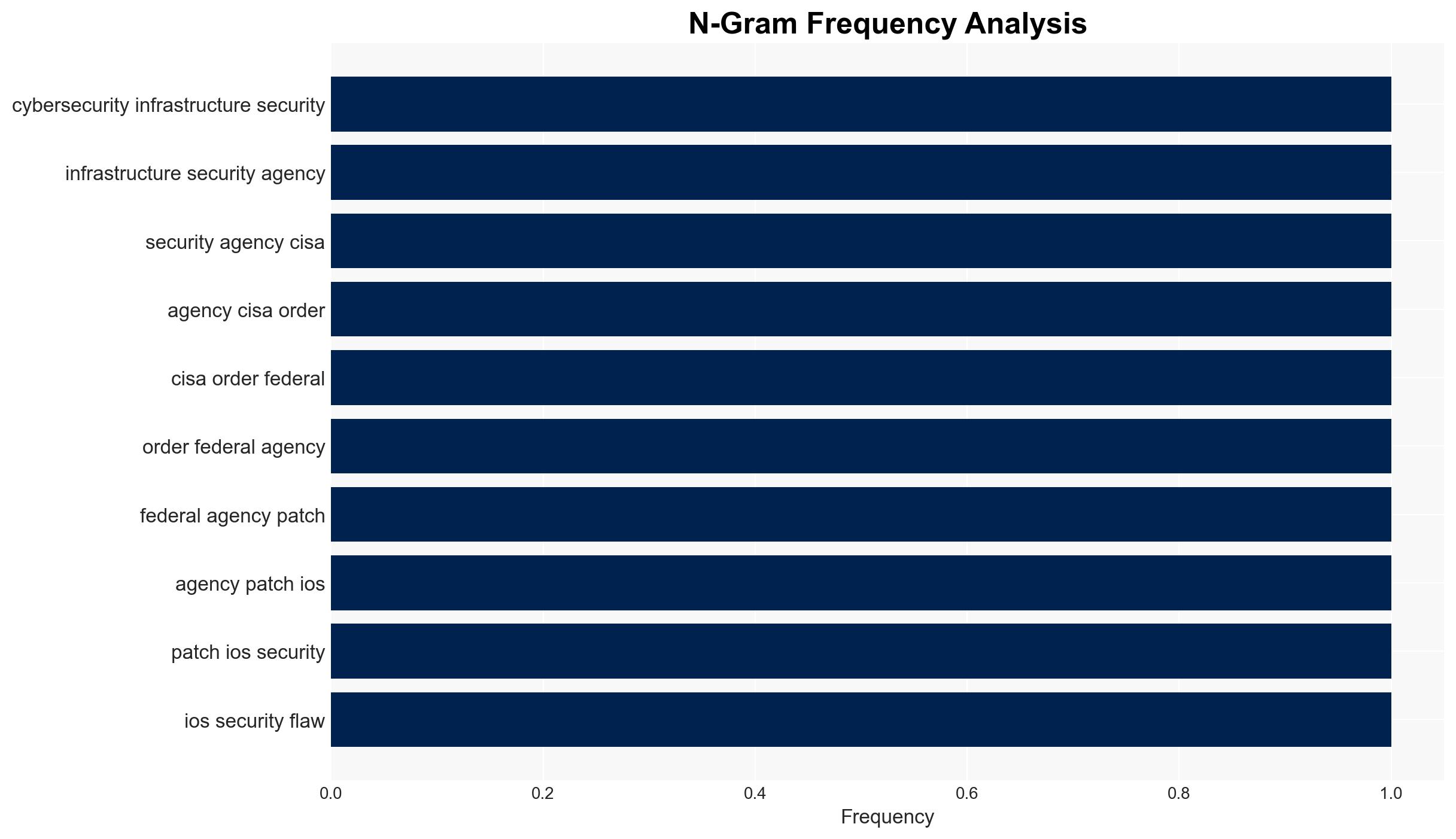
- Immediate Actions (0–30 days): Ensure all federal and private sector entities apply available patches; enhance monitoring for signs of exploitation.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; invest in cybersecurity resilience and response capabilities.
- Scenario Outlook: Best: Effective patching and mitigation reduce threat actor success. Worst: New vulnerabilities are discovered and exploited. Most-Likely: Continued exploitation with gradual mitigation as patches are applied.
6. Key Individuals and Entities
- Google Threat Intelligence Group (GTIG)
- U.S. Cybersecurity and Infrastructure Security Agency (CISA)
- UNC6353 (suspected Russian state-backed group)
- UNC6691 (financially motivated Chinese threat actor)
- iVerify (mobile security firm)
7. Thematic Tags
cybersecurity, cyber-espionage, state-backed actors, financial crime, iOS vulnerabilities, threat intelligence, digital security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us