CISA alerts to critical RCE vulnerability in n8n being actively exploited, urging immediate patching.
Published on: 2026-03-12
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: CISA warns max-severity n8n bug is being exploited in the wild
1. BLUF (Bottom Line Up Front)
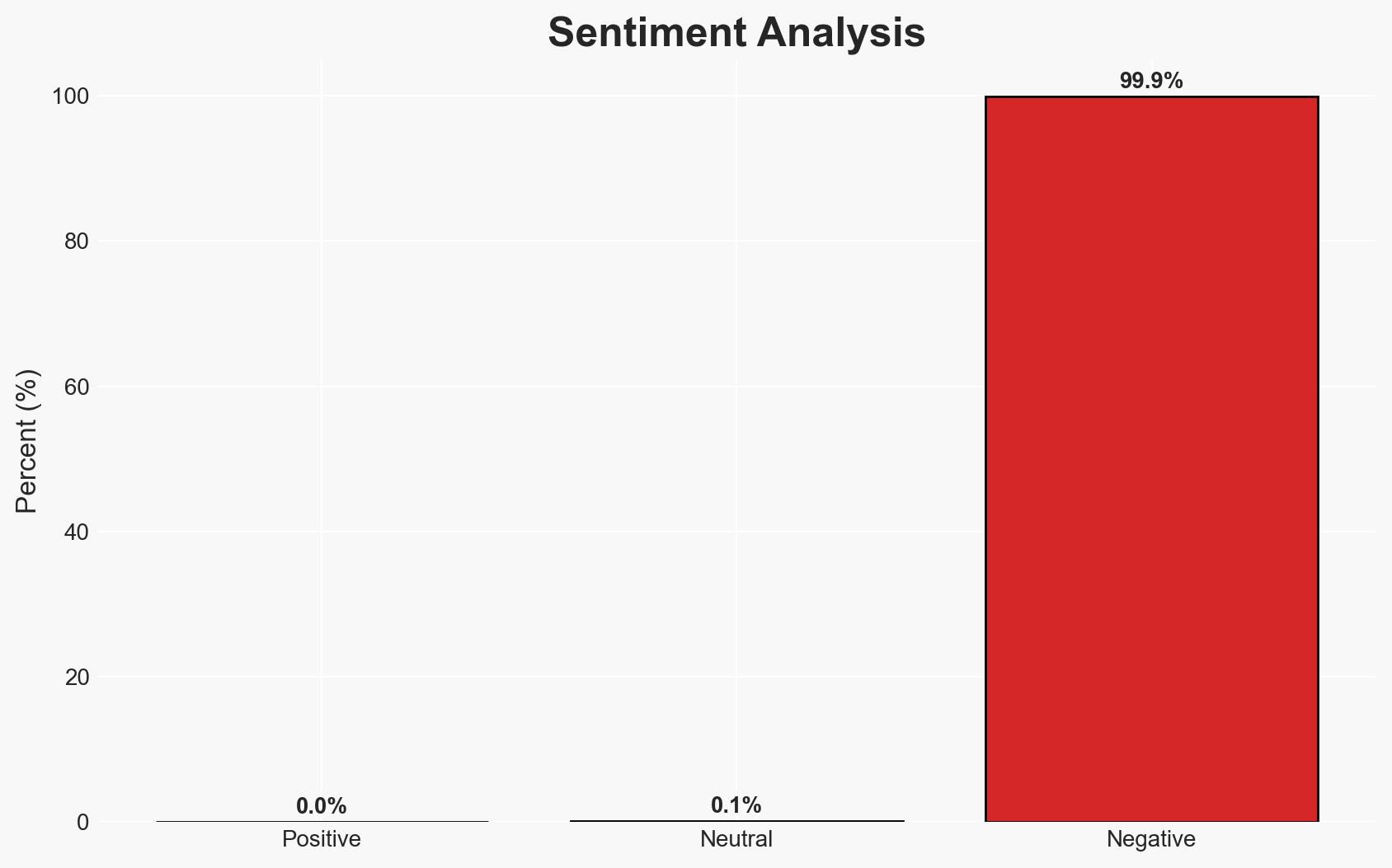
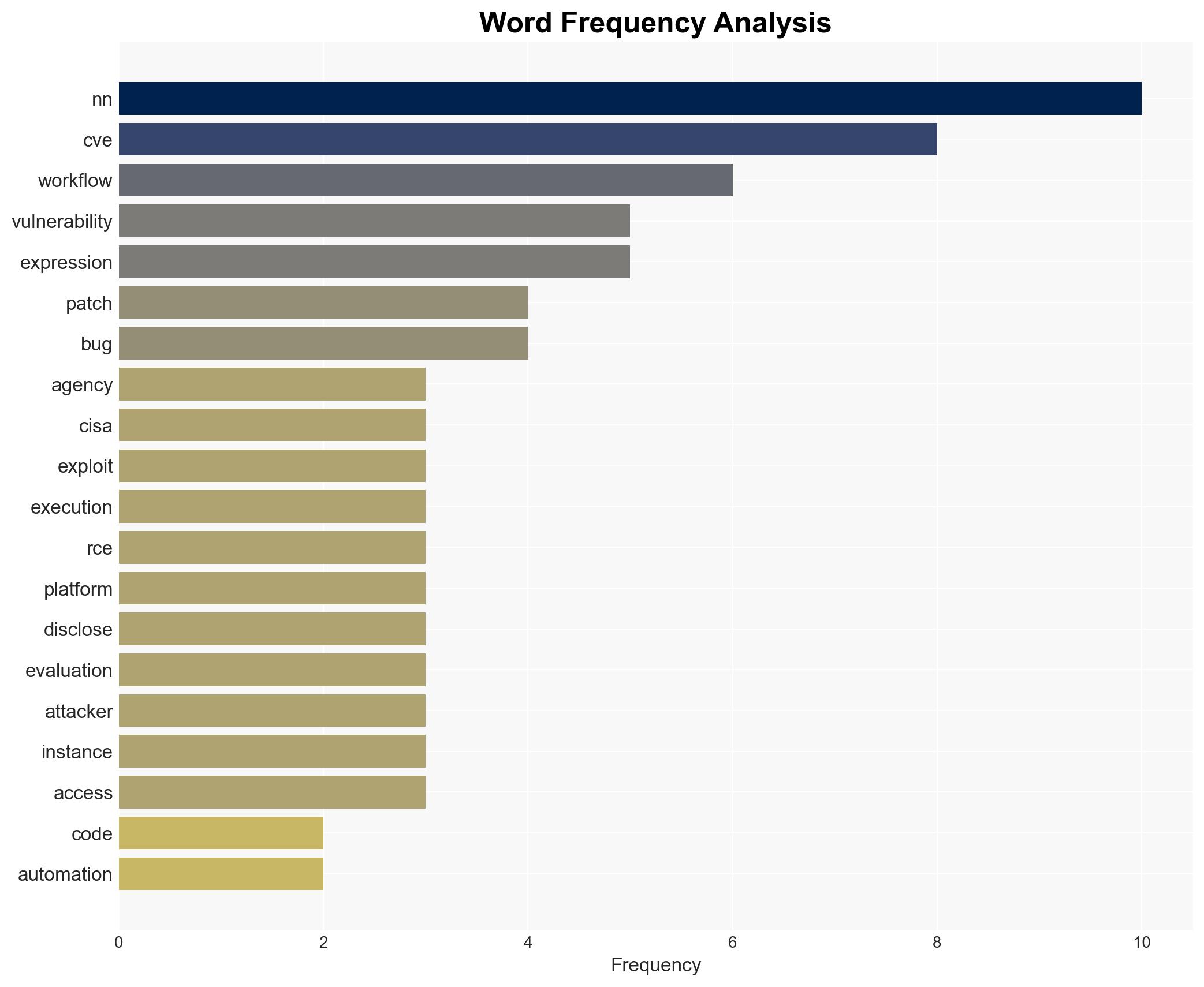
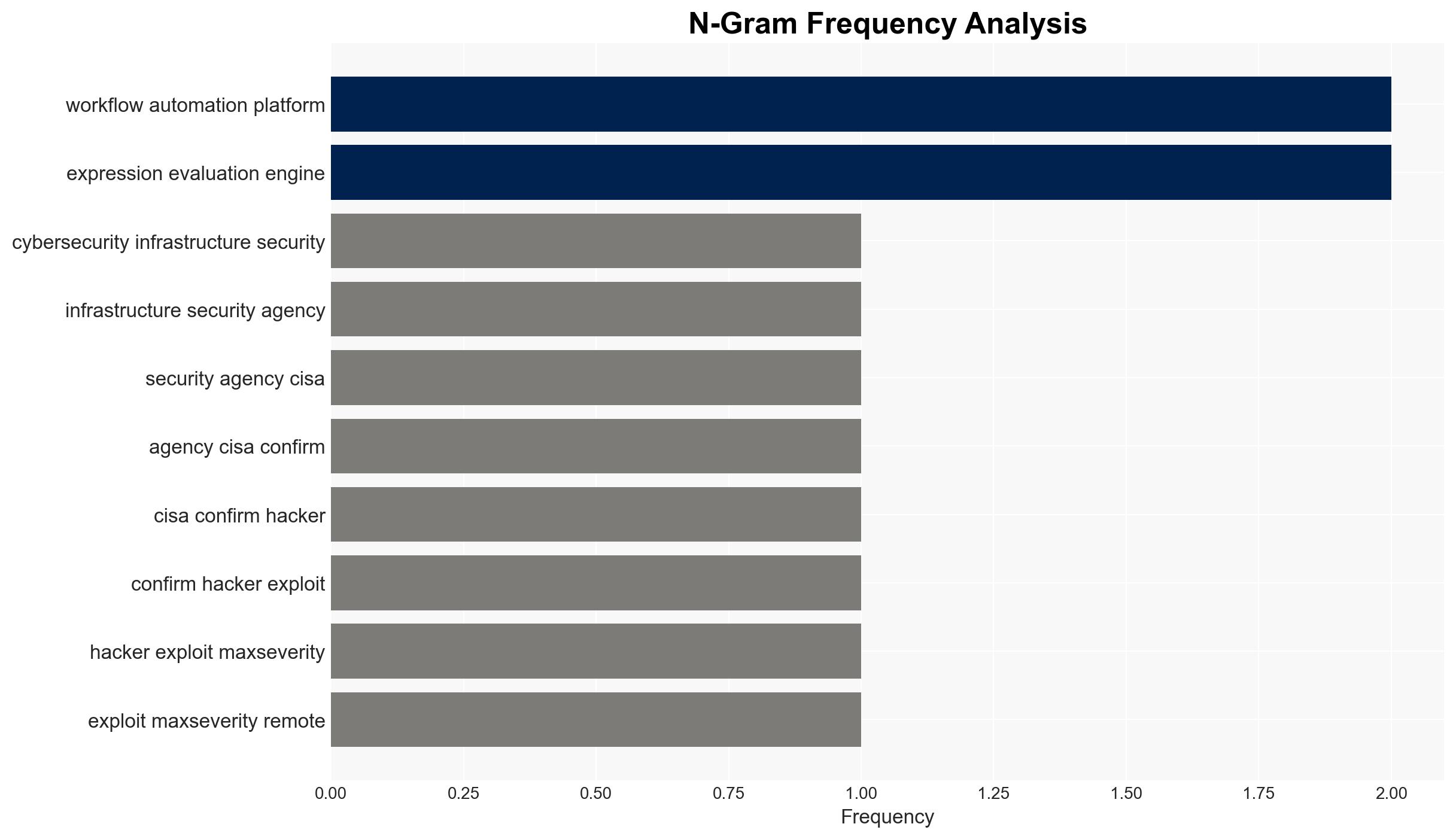
The US Cybersecurity and Infrastructure Security Agency (CISA) has identified active exploitation of a critical vulnerability in the n8n workflow automation platform, potentially affecting over 103,000 users. The vulnerability allows remote code execution, posing significant risks of data theft and supply chain compromise. The most likely hypothesis is that threat actors are targeting unpatched systems to gain unauthorized access. Overall confidence in this assessment is moderate due to the lack of detailed attribution information.
2. Competing Hypotheses
- Hypothesis A: Threat actors are exploiting the n8n vulnerability primarily for financial gain through data theft and ransomware. Supporting evidence includes the high vulnerability score and the potential for unauthorized access to sensitive data. Key uncertainties include the specific identities and motivations of the attackers.
- Hypothesis B: The exploitation is part of a broader campaign aimed at establishing persistent access for future strategic operations, possibly by state-sponsored actors. This is supported by the potential for full system compromise and supply chain infiltration. Contradicting evidence includes the lack of specific attribution to state actors.
- Assessment: Hypothesis A is currently better supported due to the immediate financial incentives and the prevalence of similar cybercrime activities targeting unpatched vulnerabilities. Indicators such as increased targeting of critical infrastructure or specific geopolitical entities could shift this judgment towards Hypothesis B.
3. Key Assumptions and Red Flags
- Assumptions: Organizations have not uniformly applied the patch; attackers are motivated by financial gain; the vulnerability is being exploited by multiple actors.
- Information Gaps: Specific attribution of the threat actors; detailed impact analysis on affected organizations; comprehensive patch adoption statistics.
- Bias & Deception Risks: Potential bias in vendor reporting on vulnerability impact; risk of underestimating state-sponsored involvement due to lack of direct evidence.
4. Implications and Strategic Risks
The exploitation of the n8n vulnerability could lead to significant disruptions if not mitigated promptly. The situation may evolve with broader implications for cybersecurity practices and international relations.
- Political / Geopolitical: Potential for increased tensions if state-sponsored actors are implicated, leading to diplomatic confrontations.
- Security / Counter-Terrorism: Heightened risk of cyber-attacks on critical infrastructure, necessitating enhanced security measures.
- Cyber / Information Space: Increased focus on patch management and vulnerability disclosure practices; potential for misinformation campaigns exploiting the vulnerability.
- Economic / Social: Potential economic impact on businesses reliant on n8n; increased demand for cybersecurity solutions and services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urge all users to apply the patch immediately; enhance monitoring for signs of exploitation; share threat intelligence with relevant stakeholders.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing; invest in cybersecurity training and awareness programs; review and update incident response plans.
- Scenario Outlook:
- Best: Rapid patch adoption mitigates risk, and no significant breaches occur.
- Worst: Widespread exploitation leads to major data breaches and supply chain disruptions.
- Most-Likely: Continued exploitation of unpatched systems with moderate impact, prompting gradual improvements in cybersecurity practices.
6. Key Individuals and Entities
- US Cybersecurity and Infrastructure Security Agency (CISA)
- n8n (workflow automation platform)
- Resecurity (vendor providing vulnerability data)
- Cyera (researchers identifying additional vulnerabilities)
7. Thematic Tags
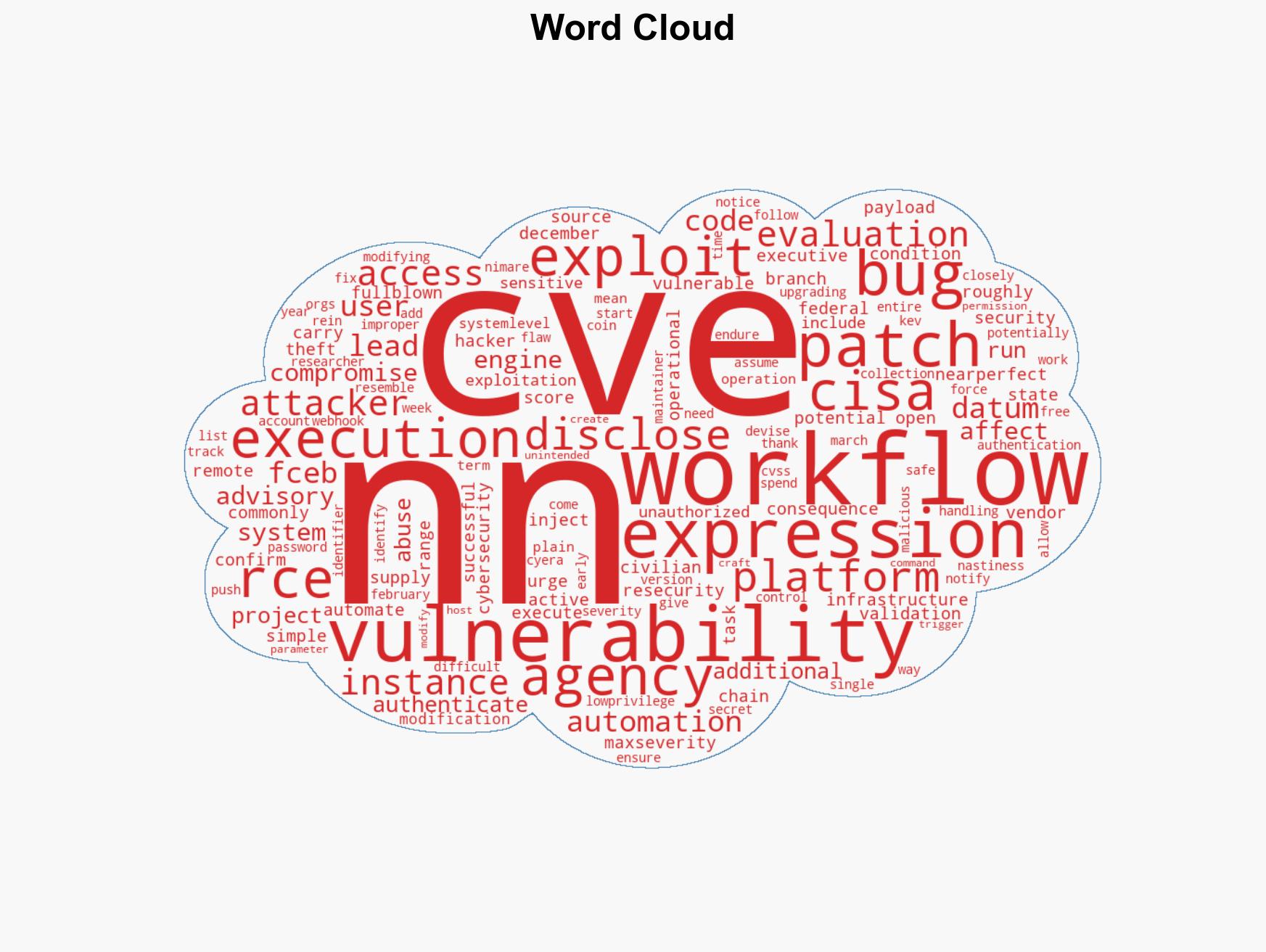
cybersecurity, vulnerability management, remote code execution, supply chain risk, patch management, cybercrime, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us