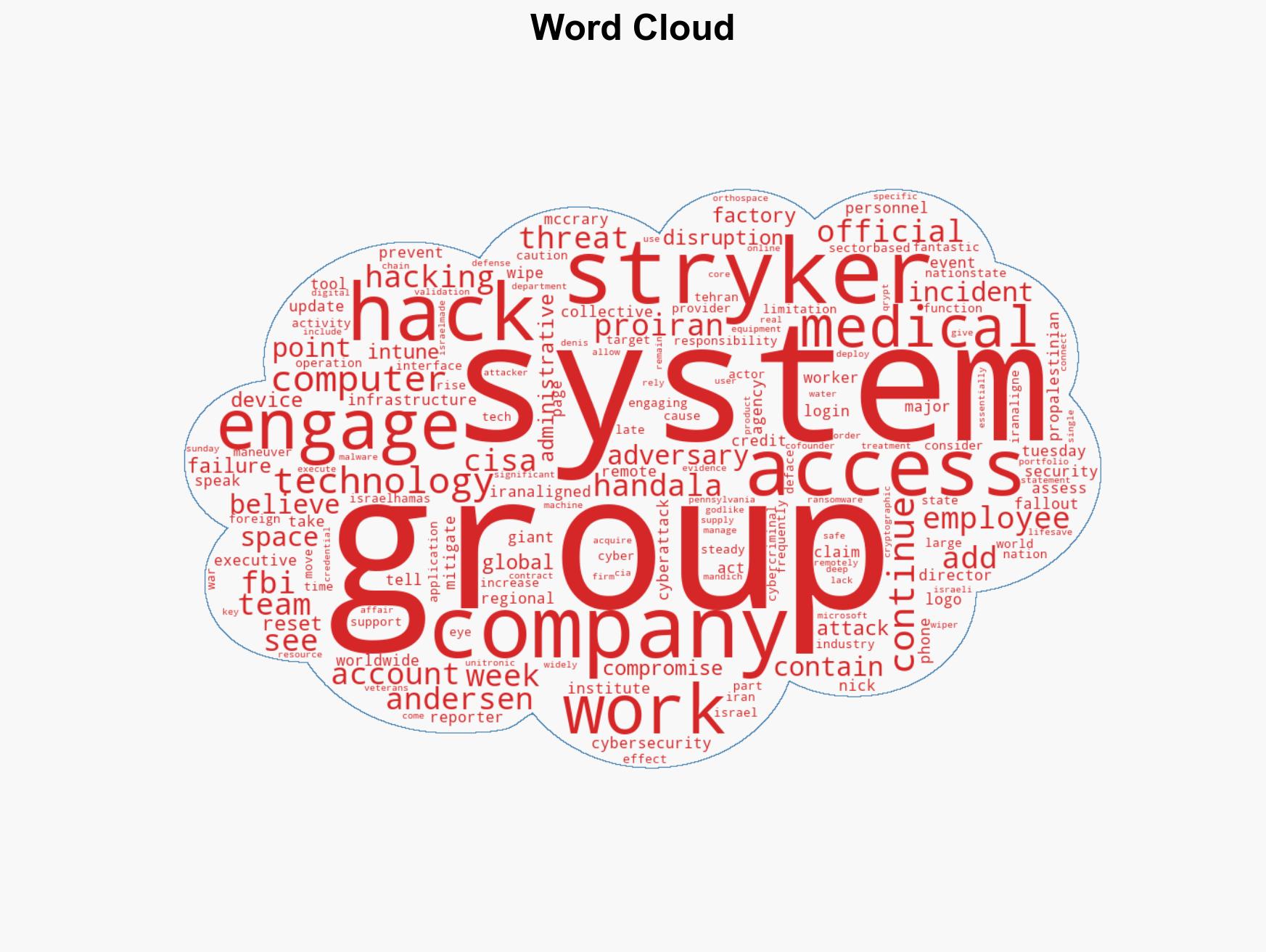
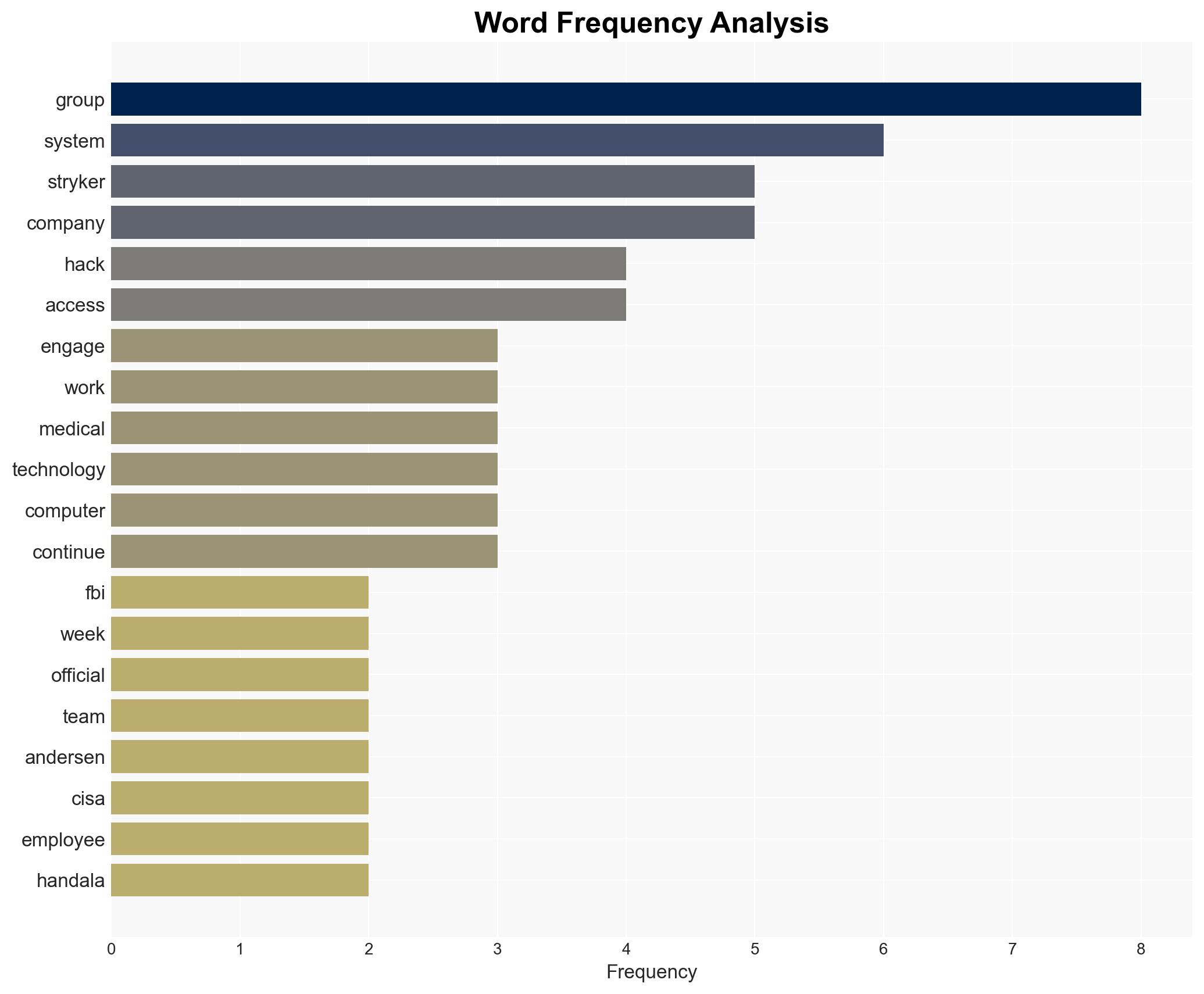
CISA and FBI Collaborate with Stryker Following Major Cyberattack Linked to Iran-Aligned Group
Published on: 2026-03-17
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: CISA FBI have engaged with Stryker staff after cyberattack official says
1. BLUF (Bottom Line Up Front)
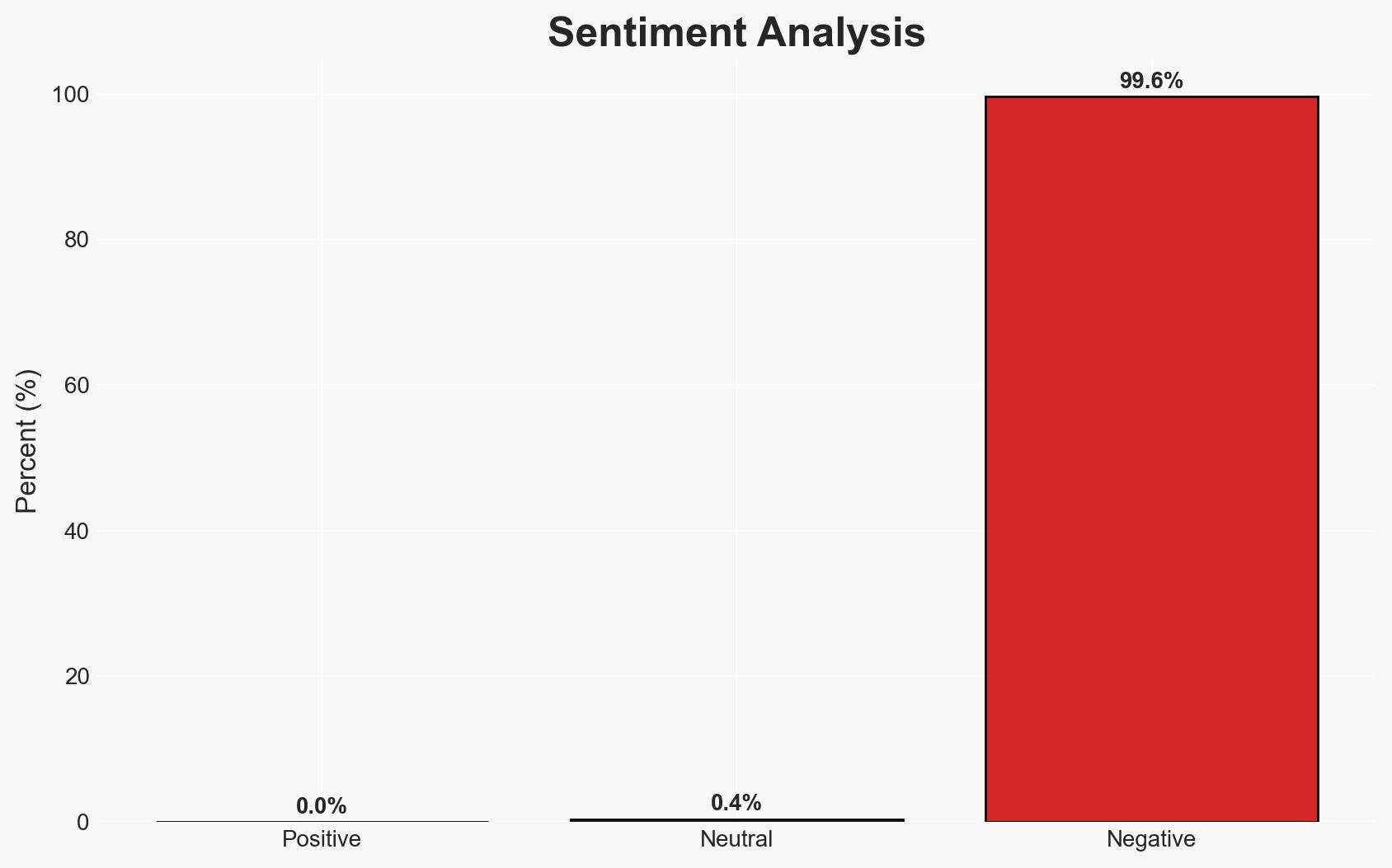
The cyberattack on Stryker, attributed to an Iran-aligned group, highlights vulnerabilities in critical infrastructure management systems. The incident underscores the persistent threat from state-affiliated cyber actors targeting U.S. entities. Current evidence supports the hypothesis that the attack was politically motivated, leveraging existing geopolitical tensions. Overall confidence in this assessment is moderate due to limited details on the attackers’ capabilities and intentions.
2. Competing Hypotheses
- Hypothesis A: The attack was politically motivated, aimed at disrupting a U.S. company with ties to Israeli technology and U.S. defense contracts. Supporting evidence includes the timing during heightened geopolitical tensions and the use of a pro-Iran hacking group’s signature. Key uncertainties involve the extent of state sponsorship and the specific objectives of the attack.
- Hypothesis B: The attack was primarily financially motivated, with the political narrative serving as a cover for cybercriminal activities. This hypothesis is less supported due to the lack of ransom demands and the focus on disruption rather than financial gain.
- Assessment: Hypothesis A is currently better supported due to the geopolitical context and the attackers’ known affiliations. Indicators such as further attacks on similar targets or statements from Iranian officials could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The group is genuinely aligned with Iranian interests; the attack was intended to disrupt rather than extract data; Stryker’s security measures were standard for the industry.
- Information Gaps: Detailed technical analysis of the attack vector; confirmation of Iranian state involvement; full scope of the attack’s impact on Stryker’s operations.
- Bias & Deception Risks: Potential bias in attributing the attack solely based on claimed responsibility; risk of overestimating the group’s capabilities or intentions without further evidence.
4. Implications and Strategic Risks
This incident could exacerbate geopolitical tensions and encourage further cyber operations against U.S. and allied infrastructure. The attack highlights the need for enhanced cybersecurity measures across critical sectors.
- Political / Geopolitical: Potential for increased U.S.-Iran tensions, influencing diplomatic and military postures.
- Security / Counter-Terrorism: Heightened alert for similar attacks on critical infrastructure, necessitating increased vigilance and coordination among security agencies.
- Cyber / Information Space: Demonstrates vulnerabilities in remote management systems, prompting a reevaluation of cybersecurity protocols and incident response strategies.
- Economic / Social: Disruption to Stryker’s operations could have downstream effects on healthcare delivery and supply chains, impacting economic stability in affected regions.
5. Recommendations and Outlook
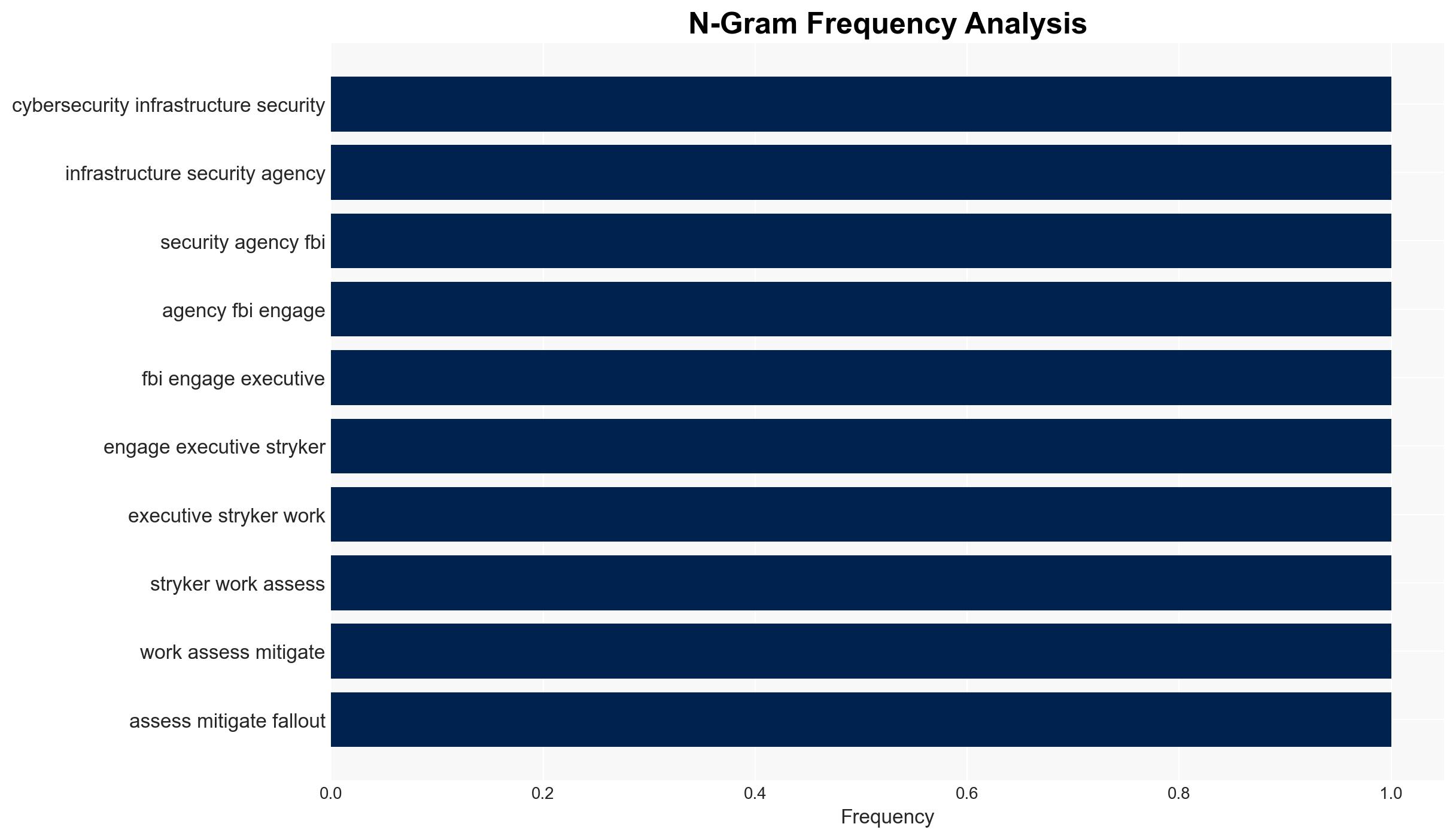
- Immediate Actions (0–30 days): Enhance monitoring of Stryker’s network for further intrusions; share threat intelligence with industry partners; conduct a comprehensive security audit.
- Medium-Term Posture (1–12 months): Develop resilience measures, including improved access controls and incident response capabilities; foster public-private partnerships for threat information sharing.
- Scenario Outlook:
- Best: Strengthened cybersecurity measures prevent further incidents, leading to improved industry standards.
- Worst: Escalation of cyberattacks leads to significant disruptions in critical infrastructure and diplomatic conflicts.
- Most-Likely: Continued low-level cyber activity with periodic disruptions, prompting gradual policy and security enhancements.
6. Key Individuals and Entities
- Nick Andersen, CISA’s acting director
- Stryker Corporation
- Handala hacking group
- Denis Mandich, former CIA official and co-founder of Qrypt
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, geopolitical tensions, critical infrastructure, Iran-aligned cyber threats, remote management vulnerabilities, public-private partnerships
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us