CISA Identifies Exploited Ivanti EPM Vulnerability; Urges Federal Agencies to Implement Patch Promptly
Published on: 2026-03-10
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: CISA Recently patched Ivanti EPM flaw now actively exploited
1. BLUF (Bottom Line Up Front)
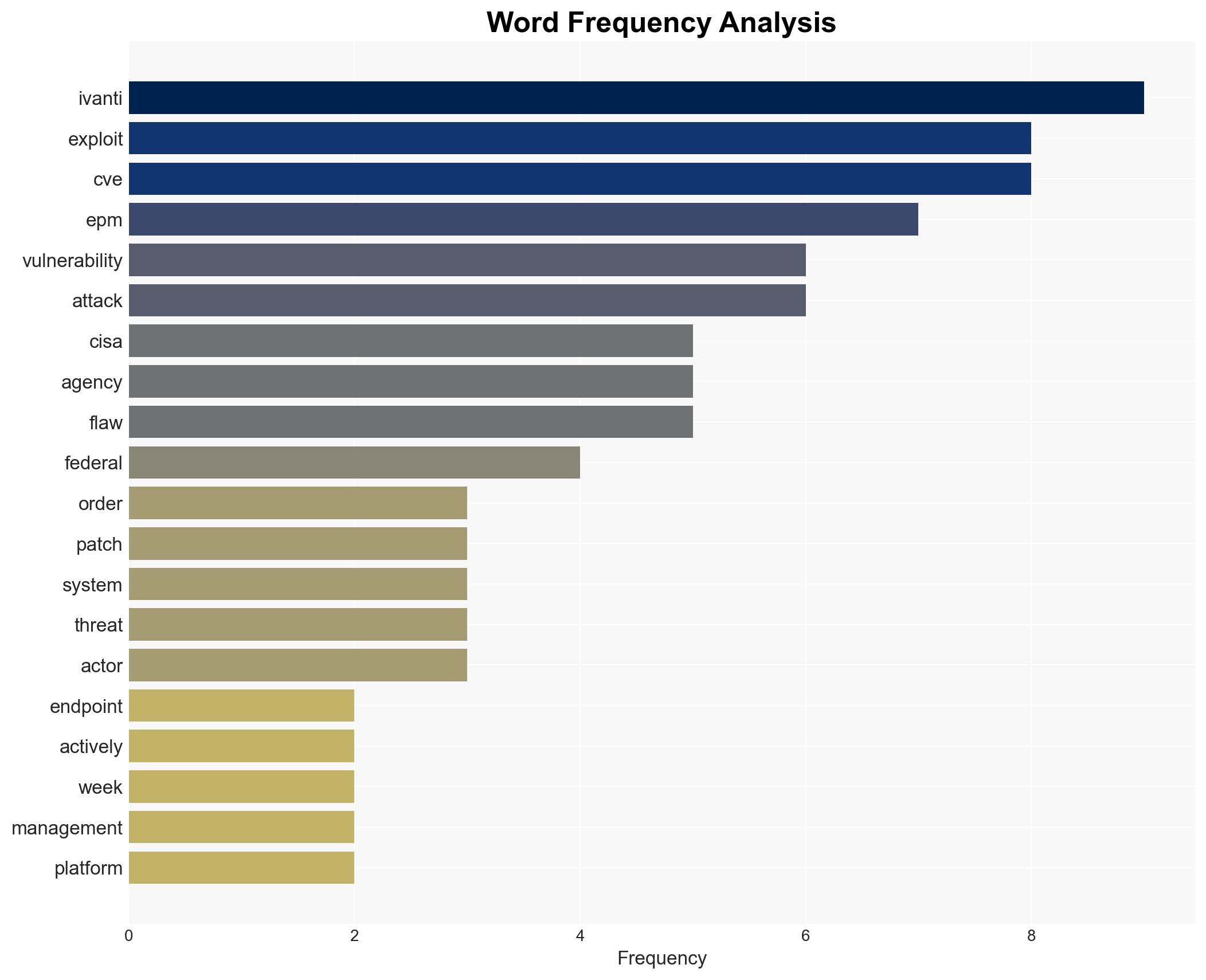
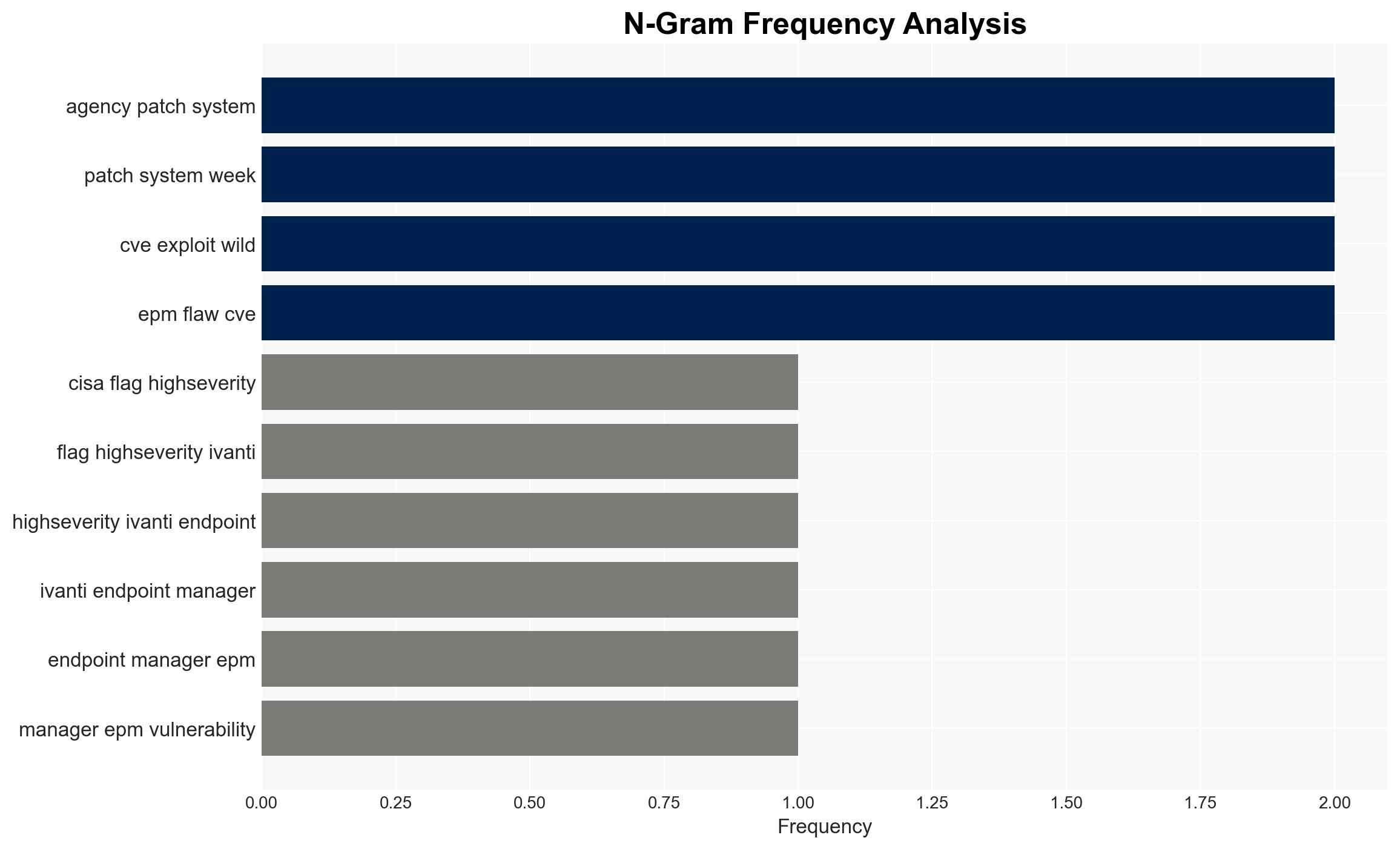
The Ivanti Endpoint Manager (EPM) vulnerability, CVE-2026-1603, has been flagged by CISA as actively exploited, posing significant risks to U.S. federal agencies. Despite Ivanti’s claims of no known exploitation, the vulnerability’s characteristics suggest a high potential for malicious activity. The most likely hypothesis is that threat actors are beginning to exploit this vulnerability, with moderate confidence due to limited evidence of active exploitation.
2. Competing Hypotheses
- Hypothesis A: The vulnerability is being actively exploited by threat actors, as indicated by CISA’s inclusion in the Known Exploited Vulnerabilities (KEV) Catalog. This is supported by the vulnerability’s ease of exploitation and historical targeting of Ivanti EPM flaws. However, Ivanti reports no evidence of exploitation, creating uncertainty.
- Hypothesis B: The vulnerability is not yet being actively exploited, and CISA’s actions are precautionary. Ivanti’s statement of no known exploitation supports this, but the lack of detailed attack data and the vulnerability’s presence in the KEV Catalog contradict this hypothesis.
- Assessment: Hypothesis A is currently better supported due to CISA’s proactive measures and the vulnerability’s inclusion in the KEV Catalog. Indicators that could shift this judgment include verified reports of exploitation or further technical analysis confirming active attacks.
3. Key Assumptions and Red Flags
- Assumptions: CISA’s KEV Catalog inclusion implies credible threat intelligence; Ivanti’s patch effectively mitigates the vulnerability; federal agencies will comply with patch directives.
- Information Gaps: Specific details on the nature and scope of any active exploitation; the number of unpatched systems; threat actor identities and motivations.
- Bias & Deception Risks: Potential over-reliance on vendor statements; risk of underestimating threat actor capabilities or intentions; possible misinformation from threat actors to obscure true exploitation status.
4. Implications and Strategic Risks
The exploitation of CVE-2026-1603 could lead to significant security breaches within U.S. federal systems, impacting national security and public trust. The situation may evolve rapidly if threat actors leverage this vulnerability for broader campaigns.
- Political / Geopolitical: Escalation in cyber tensions, particularly if state-sponsored actors are involved.
- Security / Counter-Terrorism: Increased vulnerability of federal systems could be exploited by terrorist groups for intelligence or disruption.
- Cyber / Information Space: Potential for widespread data breaches and credential theft, increasing the risk of further cyber operations.
- Economic / Social: Potential economic impact from data breaches, including financial loss and reputational damage to affected entities.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Ensure all federal agencies comply with patch directives; enhance monitoring for signs of exploitation; engage with Ivanti for threat intelligence sharing.
- Medium-Term Posture (1–12 months): Develop resilience measures, including regular vulnerability assessments; strengthen partnerships with cybersecurity vendors and international allies.
- Scenario Outlook:
- Best Case: Successful patching prevents exploitation, with no significant breaches reported.
- Worst Case: Widespread exploitation leads to major breaches and data loss, necessitating extensive recovery efforts.
- Most Likely: Limited exploitation occurs, prompting increased cybersecurity measures and awareness.
6. Key Individuals and Entities
- Ivanti
- CISA (Cybersecurity and Infrastructure Security Agency)
- Shadowserver Foundation
- Federal Civilian Executive Branch (FCEB) agencies
7. Thematic Tags
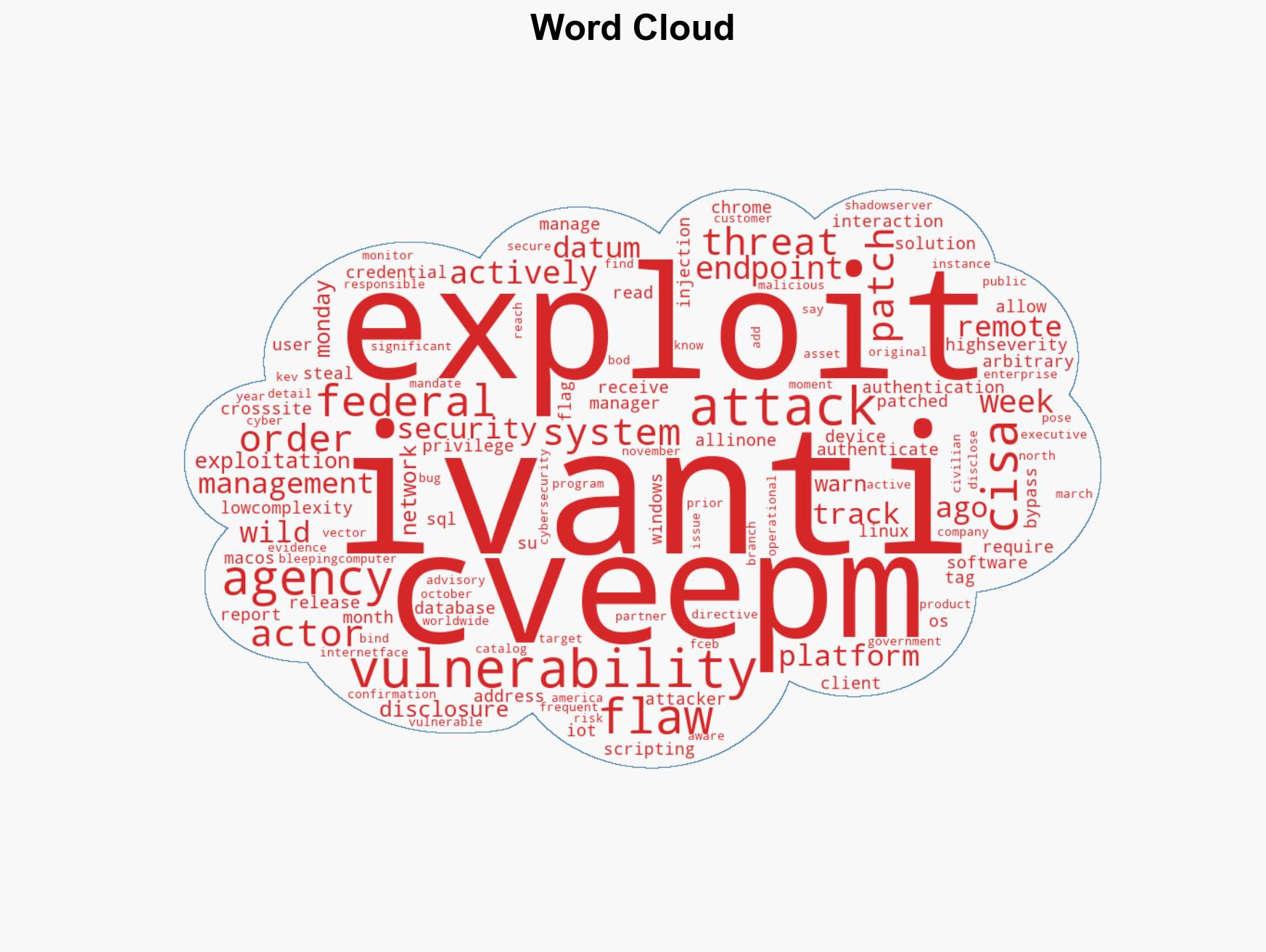
cybersecurity, vulnerability management, federal agencies, endpoint security, threat intelligence, patch management, cyber risk
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us