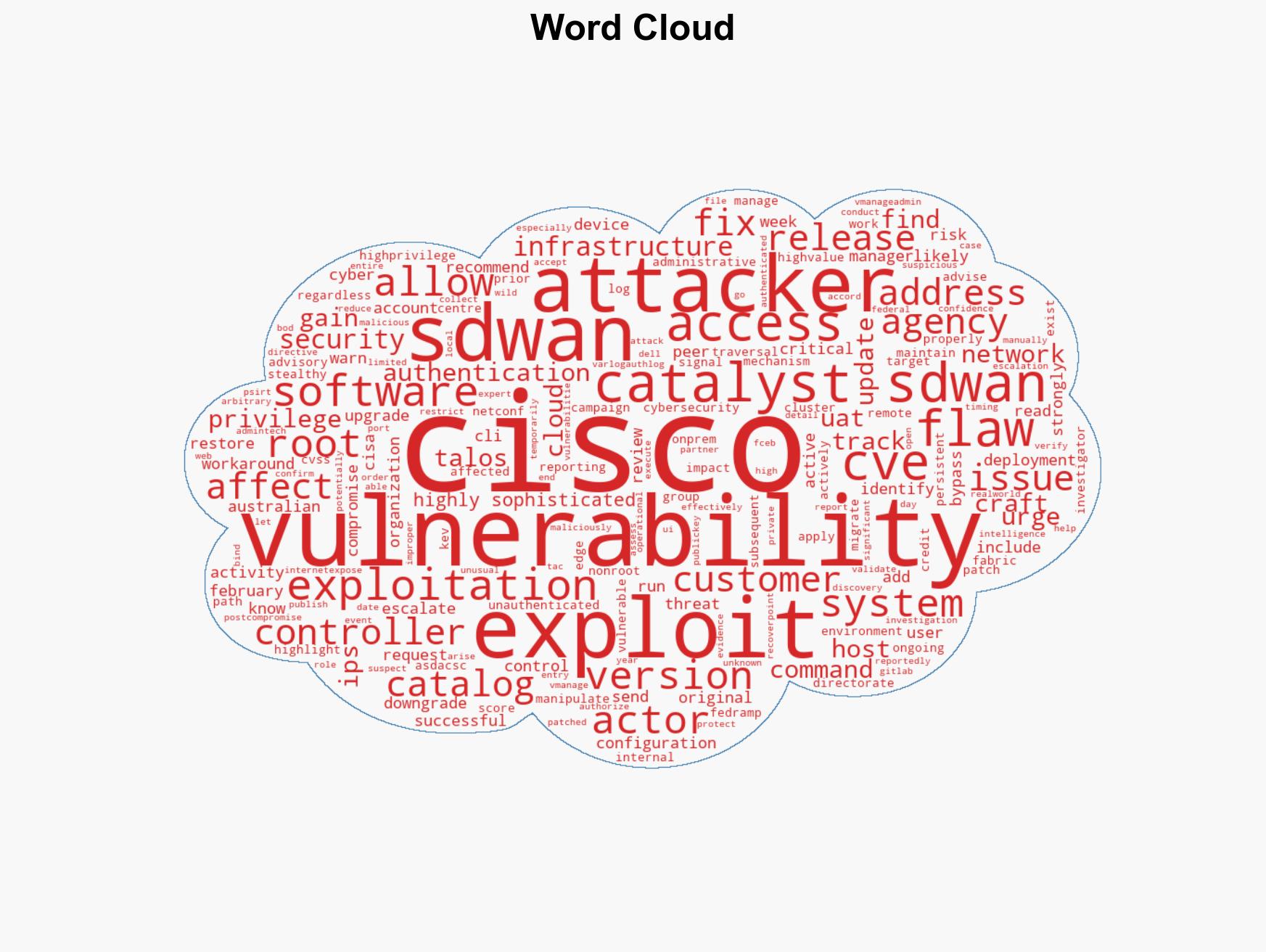
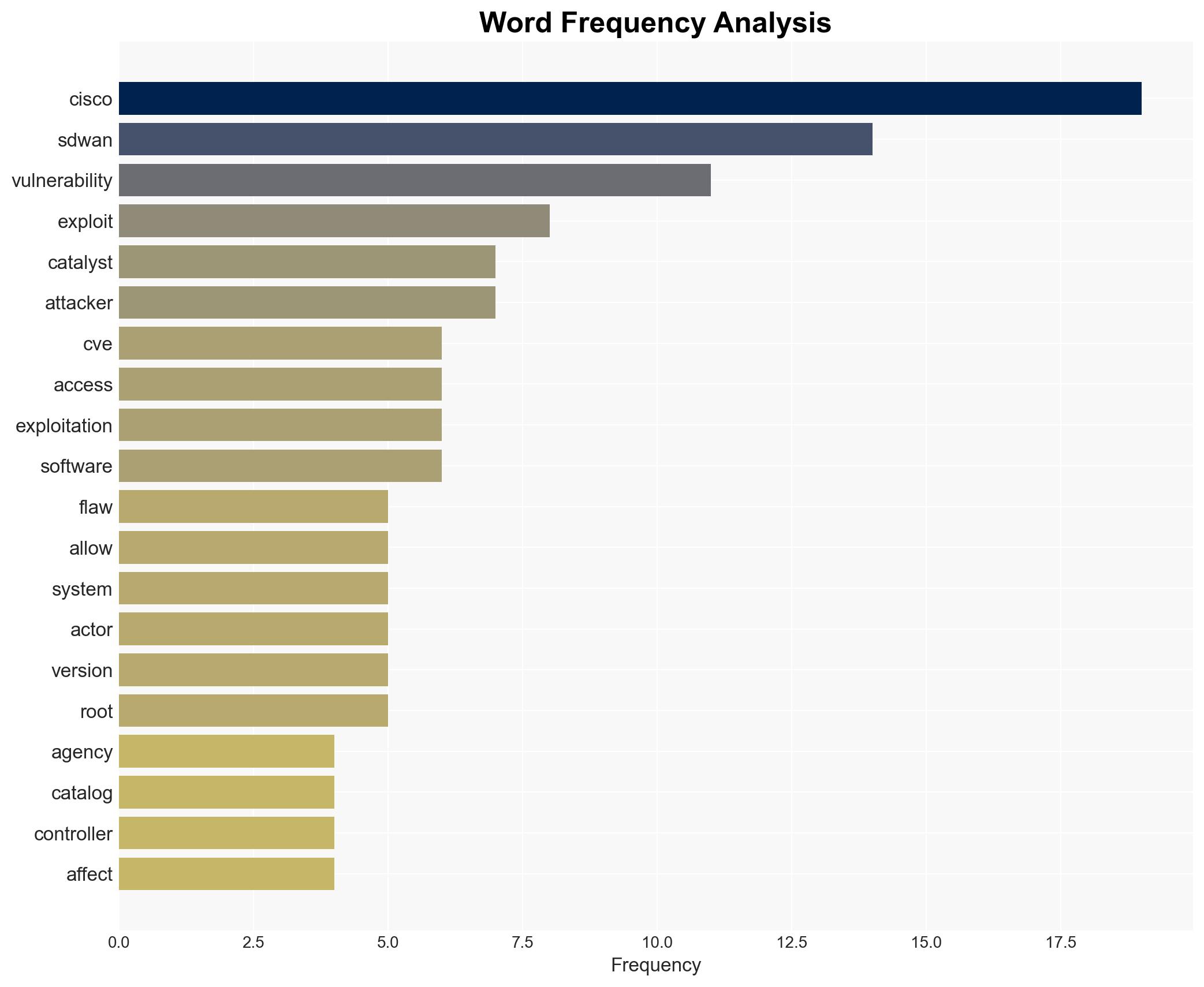
CISA includes critical Cisco SD-WAN vulnerabilities in its Known Exploited Vulnerabilities list
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: US CISA adds Cisco SD-WAN flaws to its Known Exploited Vulnerabilities catalog
1. BLUF (Bottom Line Up Front)
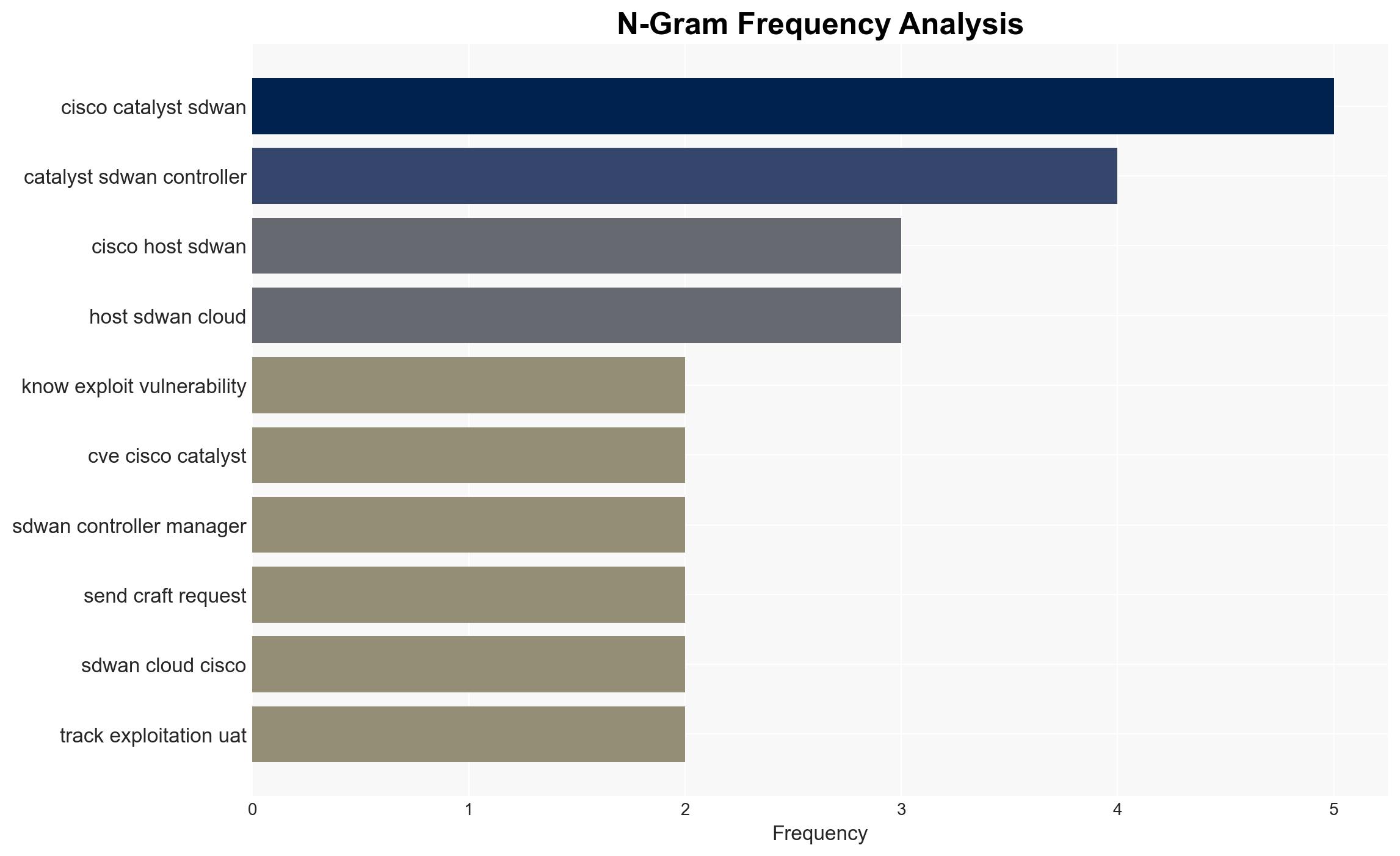
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has identified two critical vulnerabilities in Cisco SD-WAN systems, which are being actively exploited by a sophisticated threat actor. The vulnerabilities pose a significant risk to network security, particularly for high-value infrastructure organizations. The current assessment, with moderate confidence, is that the exploitation campaign is part of a broader strategy to gain persistent access to critical systems.
2. Competing Hypotheses
- Hypothesis A: The exploitation of Cisco SD-WAN vulnerabilities is primarily aimed at gaining persistent access to critical infrastructure for espionage purposes. This is supported by the sophisticated nature of the threat actor and the targeting of high-value network edge devices. However, the specific objectives of the actor remain unclear.
- Hypothesis B: The exploitation is part of a broader campaign to disrupt critical infrastructure operations, potentially as a precursor to more destructive cyber activities. While possible, there is less direct evidence supporting this hypothesis compared to espionage motives.
- Assessment: Hypothesis A is currently better supported due to the nature of the vulnerabilities exploited and the historical patterns of similar threat actors. Indicators that could shift this judgment include evidence of preparatory actions for disruptive attacks or changes in the targeting pattern.
3. Key Assumptions and Red Flags
- Assumptions: The threat actor is highly sophisticated and has the capability to exploit complex vulnerabilities. The vulnerabilities are being exploited primarily for espionage purposes. Cisco’s patching efforts will mitigate the immediate risk if widely adopted.
- Information Gaps: The identity and ultimate objectives of the threat actor remain unknown. The full scope of affected organizations and the potential for further exploitation are unclear.
- Bias & Deception Risks: There is a risk of confirmation bias in attributing the activity to espionage without considering alternative motives. Source bias may exist if the reporting entities have vested interests in highlighting certain aspects of the threat.
4. Implications and Strategic Risks
The exploitation of Cisco SD-WAN vulnerabilities could have significant implications for national security and critical infrastructure protection. The situation could evolve with broader geopolitical tensions and increased cyber threat activity.
- Political / Geopolitical: Potential escalation in cyber tensions between nation-states if attribution to a state-sponsored actor is confirmed.
- Security / Counter-Terrorism: Increased risk to critical infrastructure, necessitating heightened security measures and coordination among stakeholders.
- Cyber / Information Space: Potential for increased cyber espionage activities and information theft, impacting sensitive data integrity and confidentiality.
- Economic / Social: Disruption to critical services could have economic repercussions and affect public trust in digital infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently apply Cisco’s security updates, enhance monitoring of network traffic for signs of exploitation, and increase information sharing among affected entities.
- Medium-Term Posture (1–12 months): Develop resilience measures, strengthen public-private partnerships, and invest in advanced threat detection capabilities.
- Scenario Outlook:
- Best Case: Successful patching and mitigation efforts prevent further exploitation, and no significant breaches occur.
- Worst Case: Exploitation leads to significant disruptions in critical infrastructure, with cascading effects on national security.
- Most Likely: Continued low-level exploitation for espionage purposes, with periodic attempts at disruption.
6. Key Individuals and Entities
- U.S. Cybersecurity and Infrastructure Security Agency (CISA)
- Cisco Systems
- Australian Signals Directorate’s Australian Cyber Security Centre (ASD-ACSC)
- Cisco Talos
- Not clearly identifiable from open sources in this snippet
7. Thematic Tags
cybersecurity, critical infrastructure, cyber-espionage, vulnerability management, network security, threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us