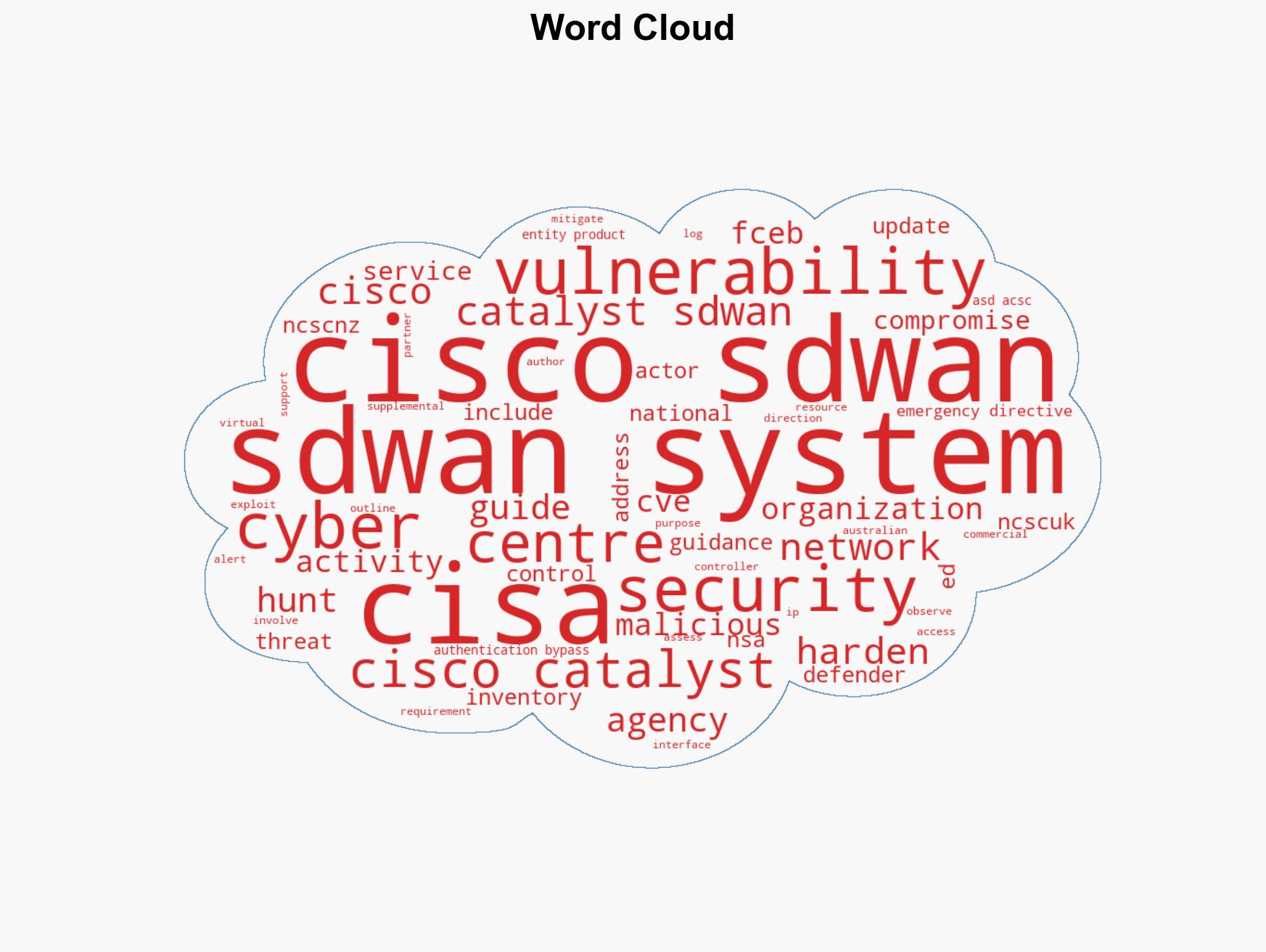
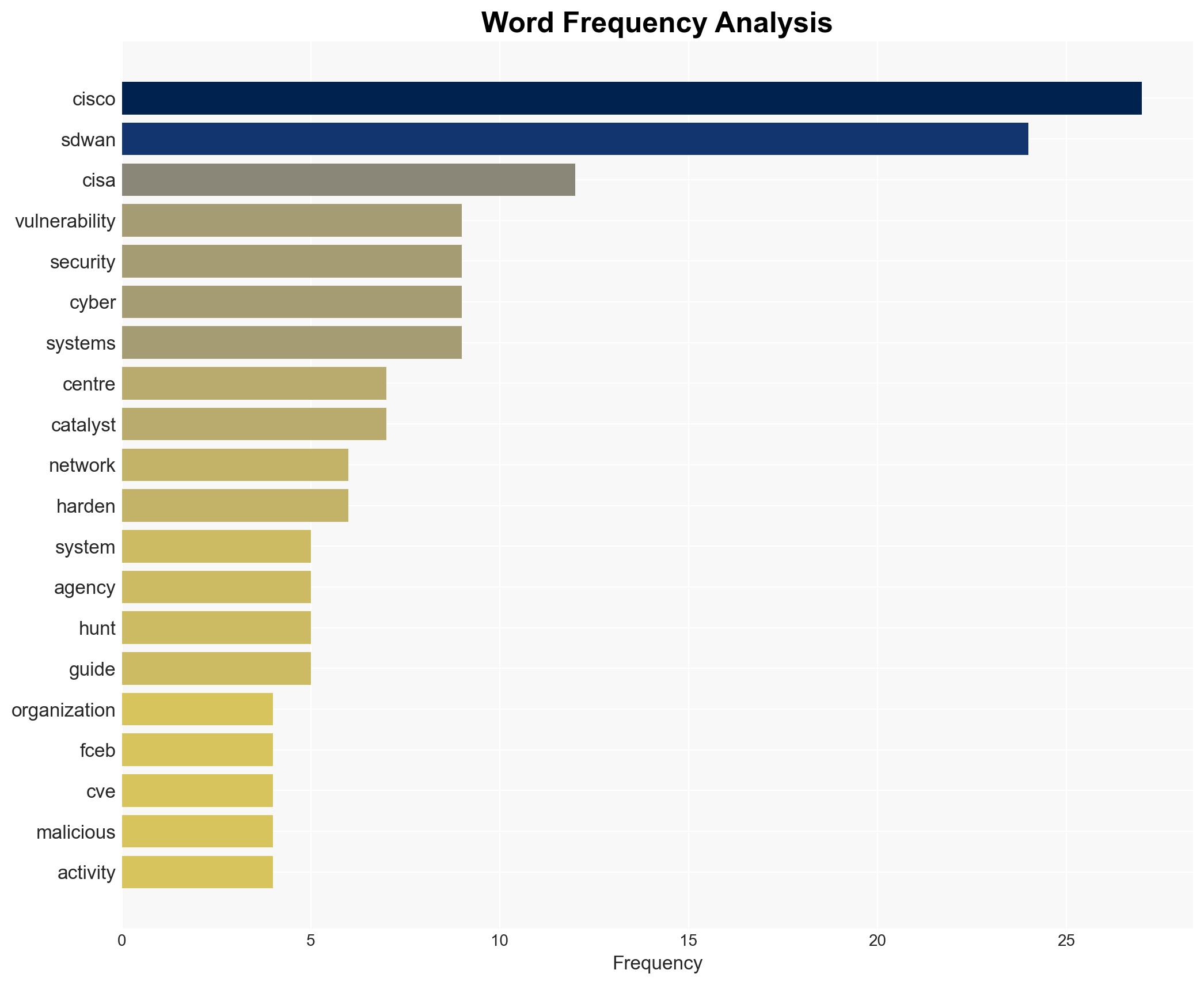
CISA Issues Alert on Ongoing Global Threats to Cisco SD-WAN Systems Amid New Vulnerabilities
Published on: 2026-02-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: CISA and Partners Release Guidance for Ongoing Global Exploitation of Cisco SD-WAN Systems
1. BLUF (Bottom Line Up Front)
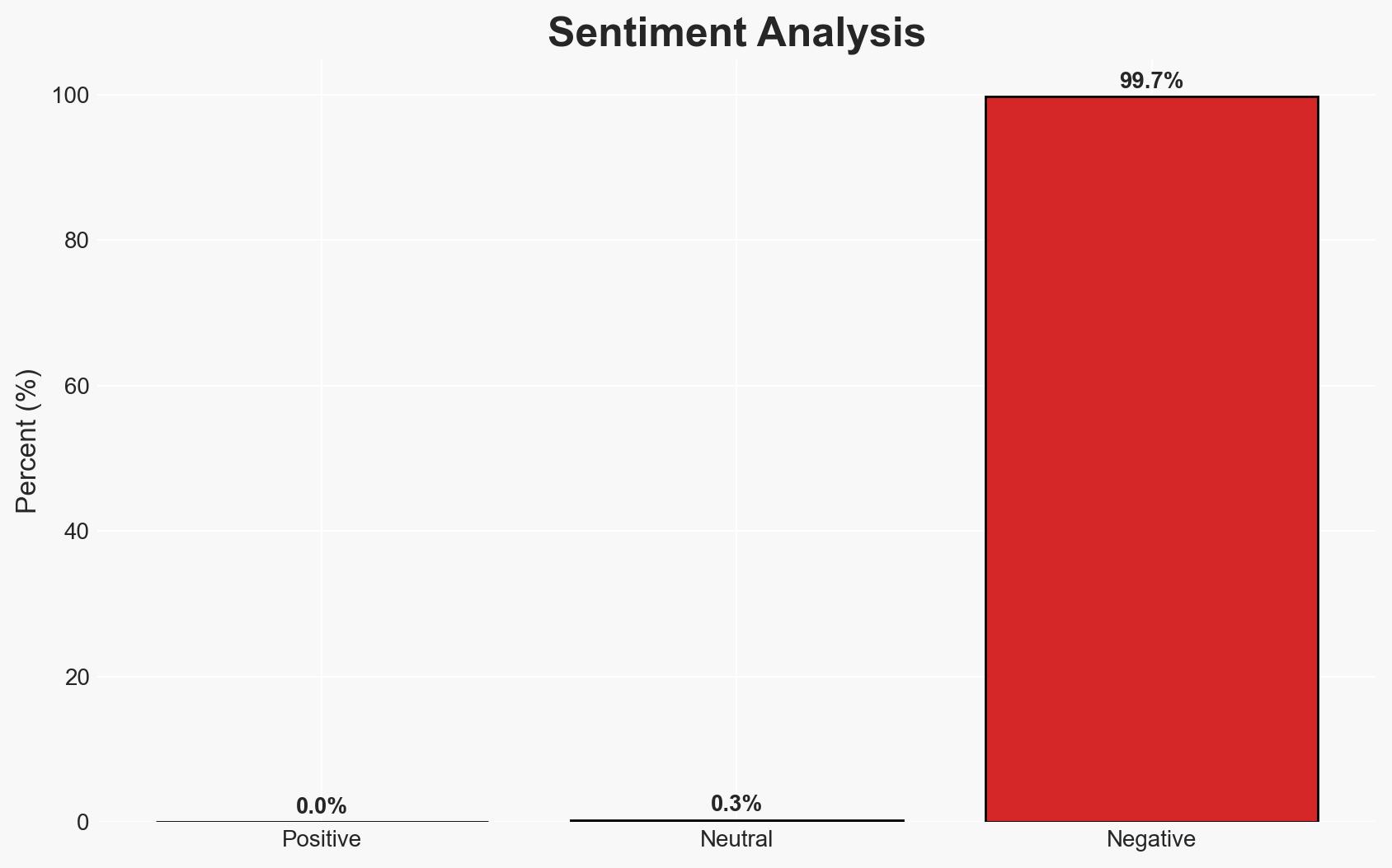
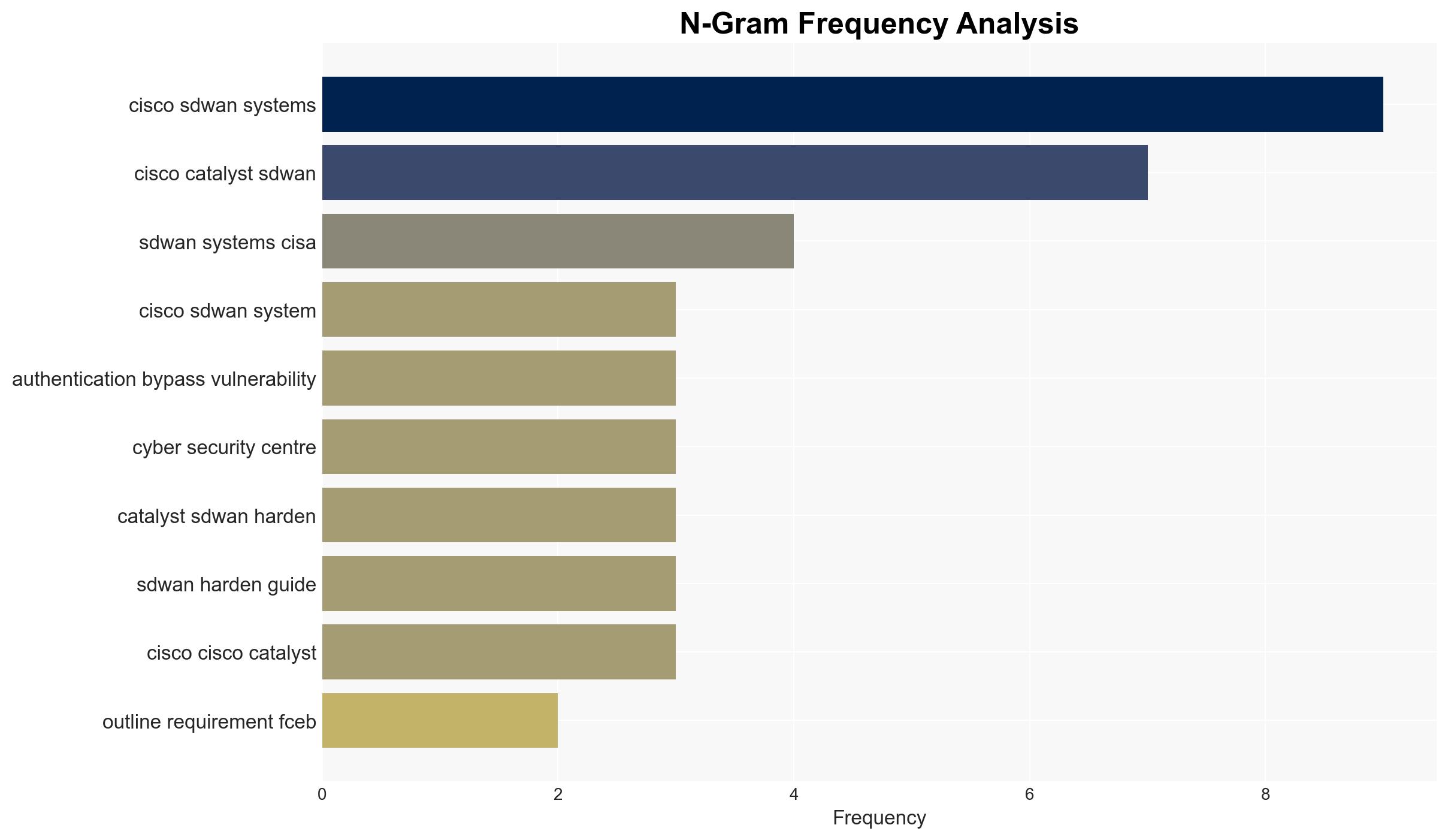
The ongoing exploitation of Cisco SD-WAN systems by malicious actors presents a significant cybersecurity threat to organizations globally, including Federal Civilian Executive Branch (FCEB) agencies. The most likely hypothesis is that these actors are leveraging specific vulnerabilities to gain unauthorized access and establish persistence. This assessment is made with moderate confidence due to the coordinated response by CISA and international partners, indicating a credible threat.
2. Competing Hypotheses
- Hypothesis A: Malicious actors are exploiting known vulnerabilities in Cisco SD-WAN systems to gain unauthorized access and establish persistence. This is supported by the addition of CVE-2026-20127 and CVE-2022-20775 to CISA’s Known Exploited Vulnerabilities Catalog and the issuance of Emergency Directive 26-03. However, the exact identity and motives of the actors remain unclear.
- Hypothesis B: The reported vulnerabilities are being exaggerated, and the threat is less severe than portrayed. This could be contradicted by the coordinated international response and the issuance of specific directives and guidance, which suggest a substantial threat level.
- Assessment: Hypothesis A is currently better supported due to the coordinated actions by CISA and international partners, indicating a credible and ongoing threat. Key indicators that could shift this judgment include new intelligence on actor identities or motives and evidence of exploitation impacts.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerabilities are actively being exploited; the actors have the capability to maintain persistence; CISA’s guidance will mitigate the threat if implemented effectively; international cooperation is based on accurate threat assessments.
- Information Gaps: Specific actor identities and motivations; the full scope of compromised systems; the effectiveness of mitigation measures.
- Bias & Deception Risks: Potential over-reliance on vendor and agency reports; confirmation bias in threat assessment; possible misinformation from adversarial sources.
4. Implications and Strategic Risks
The exploitation of Cisco SD-WAN systems could lead to increased cyber threats and vulnerabilities across affected organizations, impacting operational integrity and data security.
- Political / Geopolitical: Potential for increased tensions if state actors are involved or perceived to be involved in cyber exploitation.
- Security / Counter-Terrorism: Heightened risk of cyber-attacks on critical infrastructure; potential for exploitation by terrorist groups.
- Cyber / Information Space: Increased focus on cybersecurity measures; potential for further vulnerabilities to be discovered and exploited.
- Economic / Social: Potential economic impact due to compromised systems; loss of trust in cybersecurity measures could affect social cohesion.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Inventory and patch all Cisco SD-WAN systems; conduct threat hunts for evidence of compromise; implement CISA’s hardening guidance.
- Medium-Term Posture (1–12 months): Develop resilience measures, enhance cybersecurity partnerships, and invest in capability development for threat detection and response.
- Scenario Outlook:
- Best: Successful mitigation of vulnerabilities with no further exploitation.
- Worst: Widespread compromise leading to significant operational disruptions.
- Most-Likely: Continued attempts at exploitation with varying degrees of success, mitigated by ongoing cybersecurity efforts.
6. Key Individuals and Entities
- Cybersecurity and Infrastructure Security Agency (CISA)
- National Security Agency (NSA)
- Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC)
- Canadian Centre for Cyber Security (Cyber Centre)
- New Zealand National Cyber Security Centre (NCSC-NZ)
- United Kingdom National Cyber Security Centre (NCSC-UK)
- Federal Civilian Executive Branch (FCEB) agencies
- Cisco Systems
7. Thematic Tags
cybersecurity, vulnerability management, international cooperation, cyber threats, network security, information assurance, critical infrastructure protection
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us