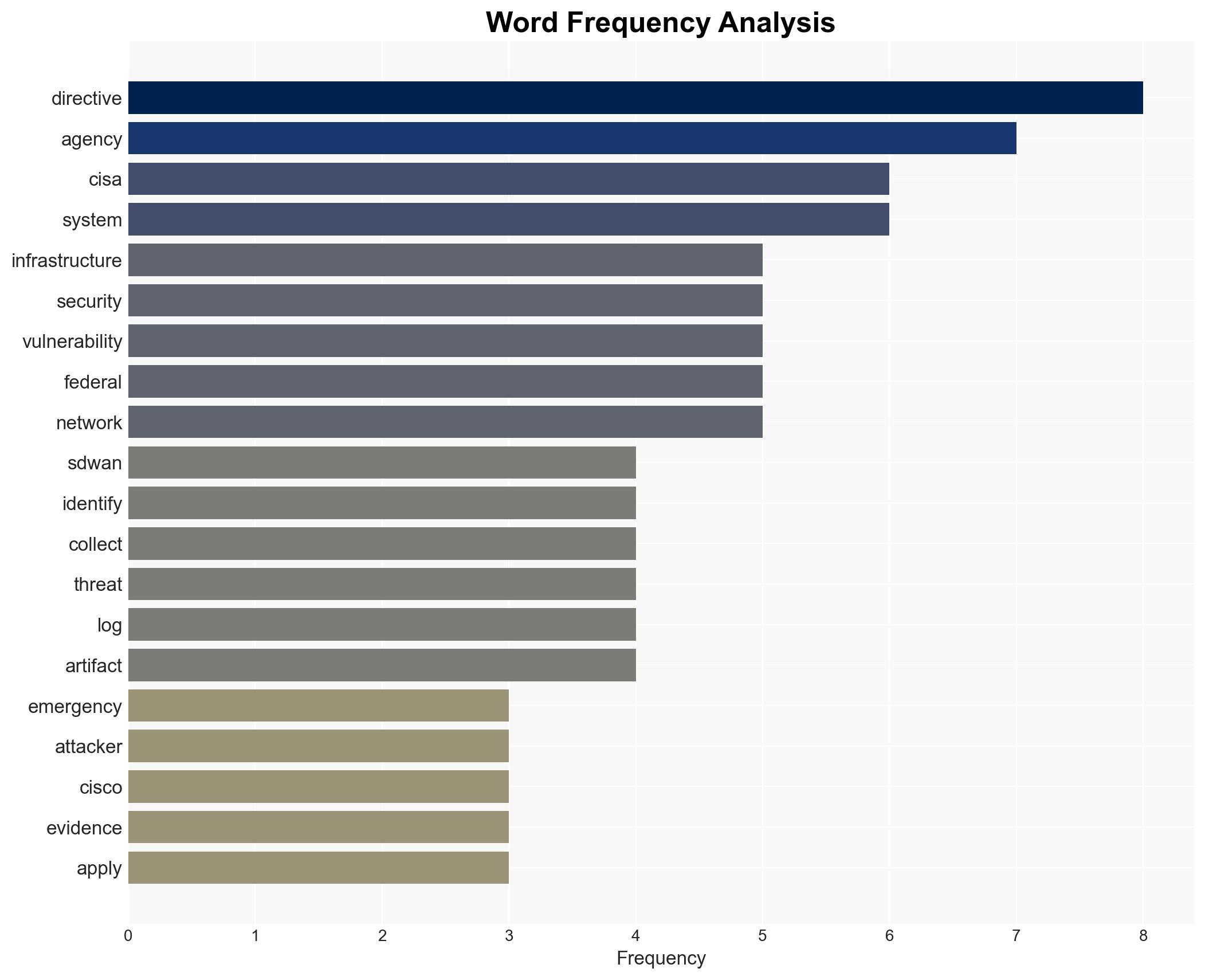
CISA Issues Urgent Directive as Cisco SD-WAN Vulnerabilities Are Actively Exploited by Attackers
Published on: 2026-03-12
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: CISA Issues Emergency Directive Over Exploited Cisco SD-WAN Flaws
1. BLUF (Bottom Line Up Front)
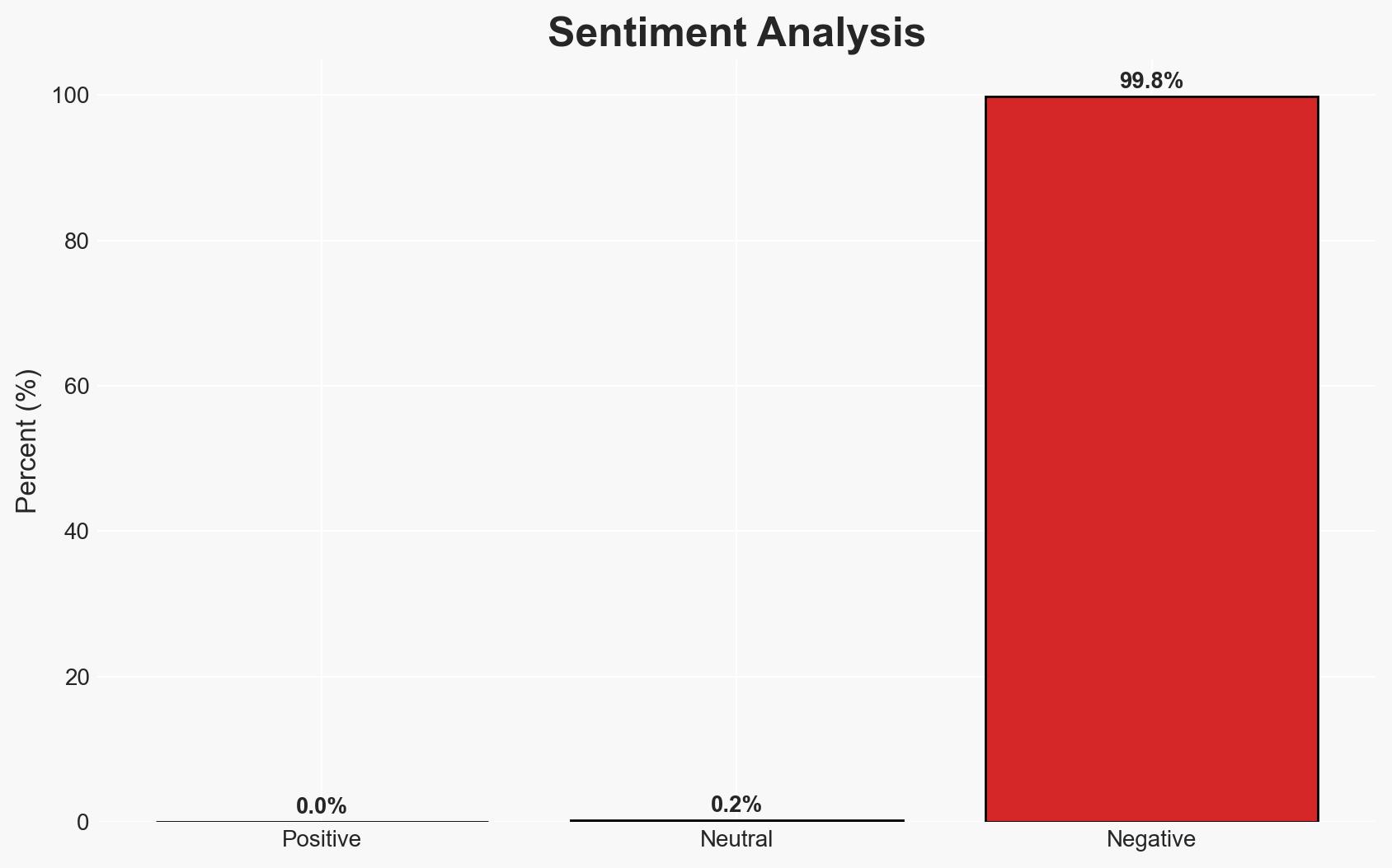
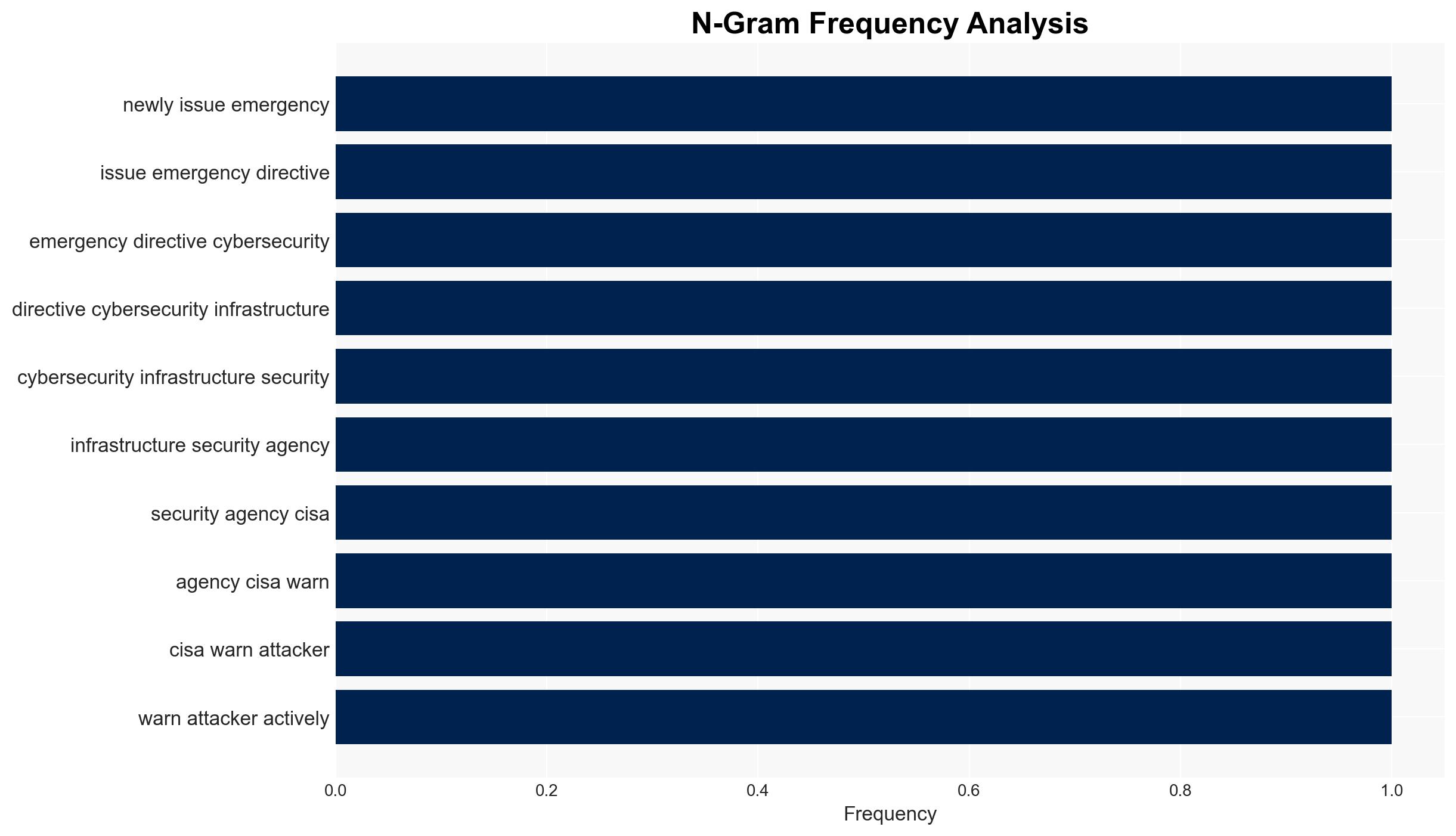
The CISA has issued an emergency directive in response to active exploitation of critical vulnerabilities in Cisco SD-WAN infrastructure across US federal networks. The directive mandates urgent identification, forensic analysis, and patching of affected systems. This situation poses a significant risk to federal network security, with moderate confidence that exploitation is ongoing. Federal agencies are the primary entities affected.
2. Competing Hypotheses
- Hypothesis A: The vulnerabilities are being exploited by state-sponsored actors aiming to compromise US federal networks for intelligence gathering. This is supported by the critical nature of the vulnerability and the strategic value of federal networks. However, there is no direct attribution to a specific actor.
- Hypothesis B: The exploitation is being conducted by cybercriminal groups seeking financial gain through ransomware or data theft. This is plausible given the broad control such access could provide, but less supported due to the lack of financial demands or indicators typical of criminal operations.
- Assessment: Hypothesis A is currently better supported due to the strategic implications and the nature of the targets. Indicators such as attribution to a known state actor or specific intelligence objectives could further substantiate this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerability is being actively exploited; federal networks are the primary target; CISA’s directive is based on credible threat intelligence; patching will mitigate the threat.
- Information Gaps: Specific attribution of the threat actors; extent of compromise across non-federal networks; effectiveness of patches in preventing future exploitation.
- Bias & Deception Risks: Potential confirmation bias in attributing the threat to state actors without direct evidence; reliance on vendor-provided patch efficacy data without independent verification.
4. Implications and Strategic Risks
The exploitation of these vulnerabilities could lead to significant disruptions in federal operations and erode trust in government cybersecurity capabilities. Over time, this could affect international relations and domestic confidence in digital infrastructure.
- Political / Geopolitical: Potential escalation in cyber tensions with suspected state actors; increased scrutiny on US cybersecurity policies.
- Security / Counter-Terrorism: Heightened alert levels and resource allocation to cyber defense, potentially diverting attention from other security threats.
- Cyber / Information Space: Increased cyber defense measures; potential for retaliatory cyber operations; heightened public awareness of cyber vulnerabilities.
- Economic / Social: Potential economic impact from disrupted government services; increased demand for cybersecurity solutions and expertise.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Ensure compliance with CISA directives; enhance monitoring of federal networks; conduct threat hunting and forensic analysis.
- Medium-Term Posture (1–12 months): Strengthen inter-agency collaboration on cybersecurity; invest in advanced threat detection and response capabilities; review and update cybersecurity policies.
- Scenario Outlook:
- Best: Successful mitigation and no further exploitation, leading to improved cybersecurity posture.
- Worst: Continued exploitation leading to significant data breaches and operational disruptions.
- Most-Likely: Partial mitigation with ongoing attempts at exploitation, requiring sustained vigilance and response.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
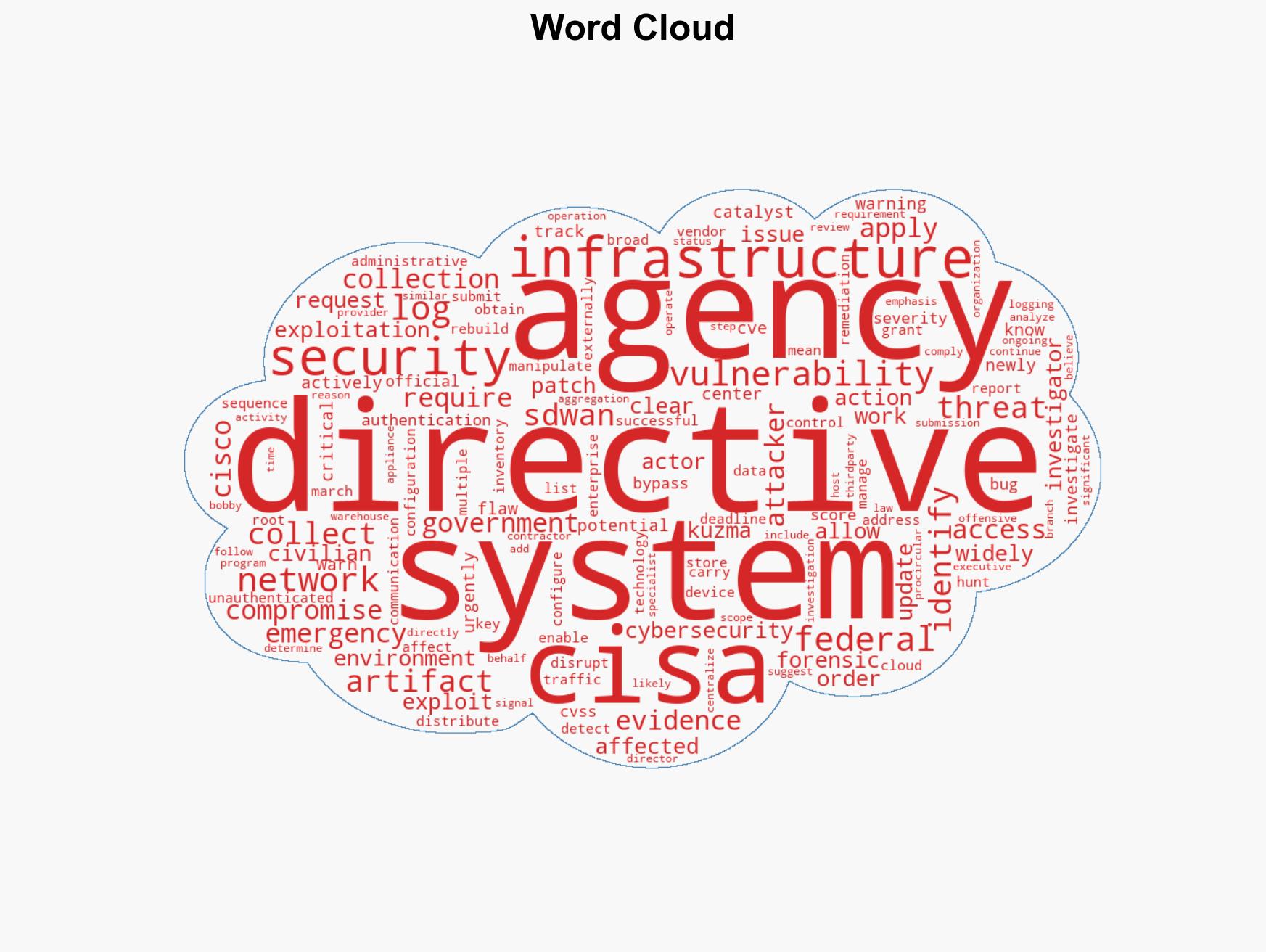
cybersecurity, federal networks, vulnerability exploitation, CISA directive, state-sponsored threats, cyber defense, Cisco SD-WAN
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us