CISA Warns of Active Exploitation of Wing FTP Server Vulnerability; Immediate Patching Required
Published on: 2026-03-17
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: This Wing FTP Server flaw is being actively exploited in attacks CISA says mitigate now
1. BLUF (Bottom Line Up Front)
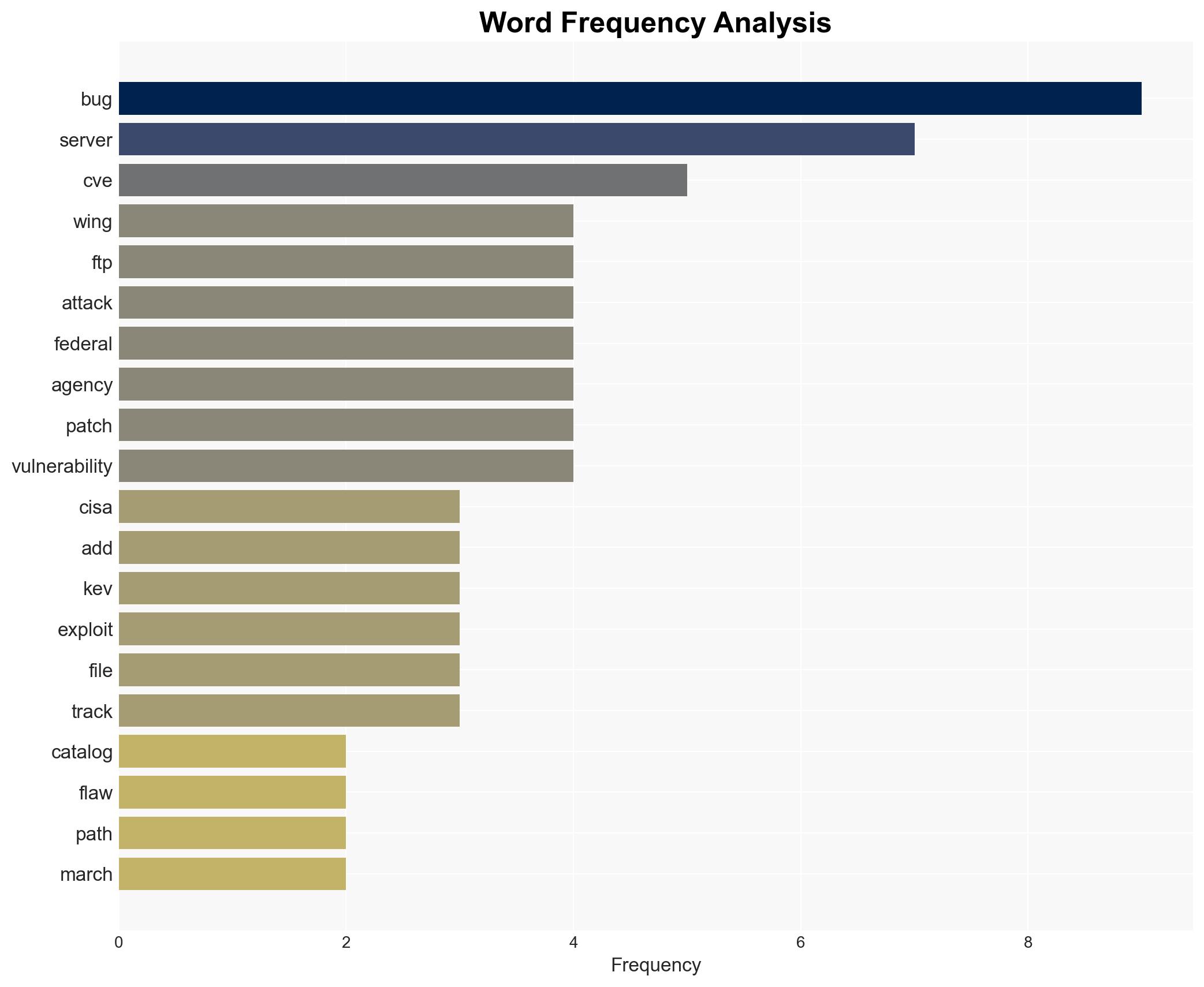
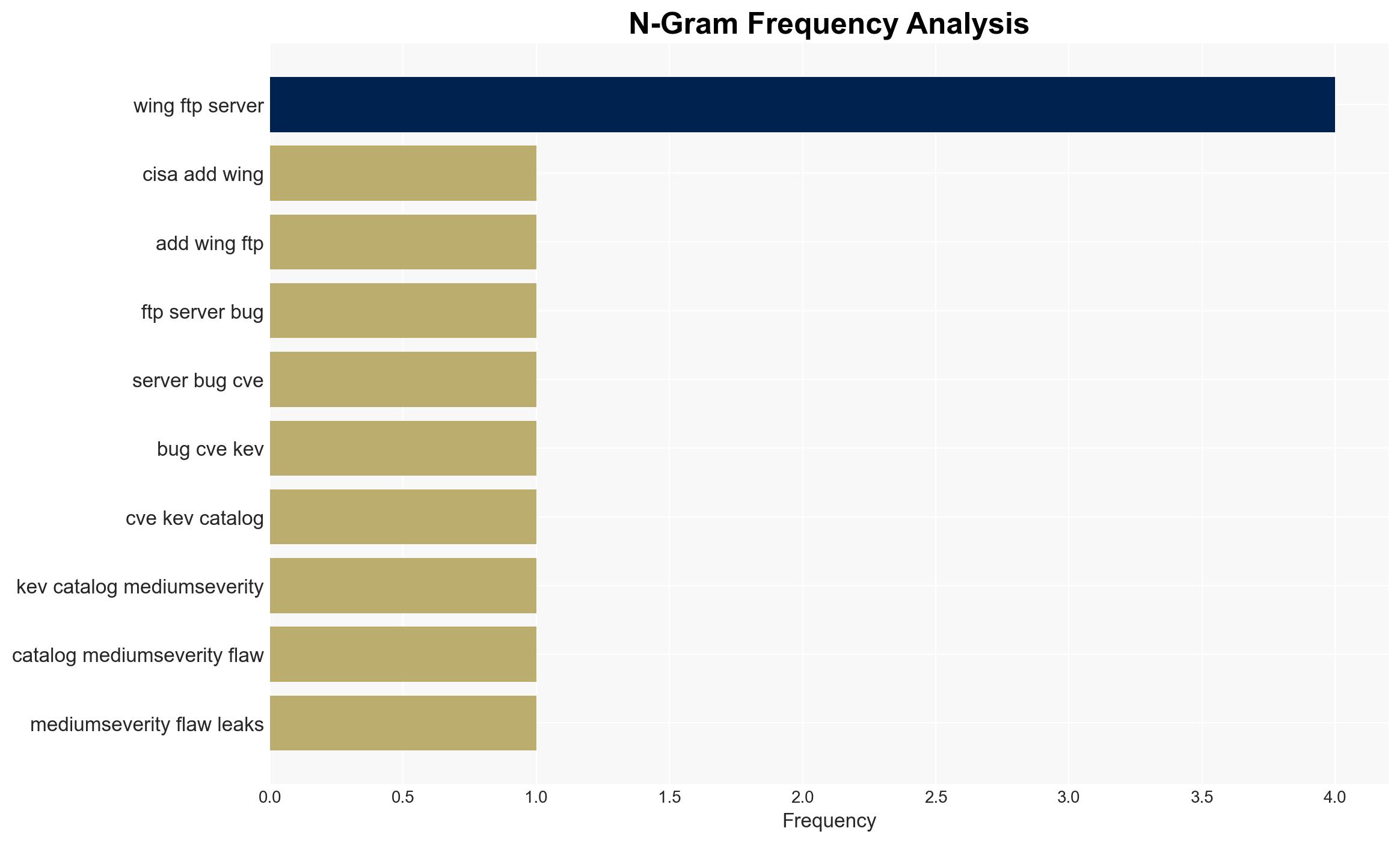
The Wing FTP Server vulnerability (CVE-2025-47813) is being actively exploited in cyber attacks, prompting CISA to mandate immediate patching by federal agencies. This flaw, while medium in severity, can be leveraged in combination with other vulnerabilities for more severe attacks. The situation poses a significant risk to federal cybersecurity infrastructure. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The vulnerability is primarily being exploited by opportunistic cybercriminals seeking to gain unauthorized access to sensitive data. This is supported by the medium severity rating and the known use of the vulnerability for reconnaissance. However, the lack of specific attribution to a threat actor leaves uncertainty.
- Hypothesis B: State-sponsored actors are exploiting the vulnerability as part of a broader campaign targeting critical infrastructure. This is supported by the involvement of high-profile entities like the US Air Force and Airbus, but contradicted by the medium severity rating, which suggests less sophisticated exploitation.
- Assessment: Hypothesis A is currently better supported due to the nature of the vulnerability and its use for reconnaissance. Indicators such as increased targeting of high-profile organizations could shift this judgment towards Hypothesis B.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerability is being actively exploited; federal agencies will comply with CISA’s directives; the patch will effectively mitigate the vulnerability.
- Information Gaps: Specific threat actor attribution; detailed impact assessment on affected organizations; confirmation of patch effectiveness.
- Bias & Deception Risks: Potential bias in reporting severity due to reliance on vendor information; risk of underestimating state-sponsored involvement.
4. Implications and Strategic Risks
The exploitation of this vulnerability could lead to increased cyber threats against federal and critical infrastructure, potentially impacting national security and public trust in digital systems.
- Political / Geopolitical: Potential for increased tensions if state-sponsored involvement is confirmed.
- Security / Counter-Terrorism: Heightened alert for federal cybersecurity teams; potential for increased cyber espionage activities.
- Cyber / Information Space: Risk of data breaches and information leaks; increased scrutiny on software supply chain security.
- Economic / Social: Potential financial impacts on affected organizations; erosion of trust in digital infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Ensure compliance with CISA’s patching directive; enhance monitoring for signs of exploitation; engage with vendors for patch verification.
- Medium-Term Posture (1–12 months): Develop resilience measures such as regular vulnerability assessments; strengthen partnerships with cybersecurity firms for threat intelligence sharing.
- Scenario Outlook: Best: Vulnerability is effectively mitigated with no major incidents. Worst: Exploitation leads to significant breaches and data loss. Most-Likely: Continued opportunistic attacks with moderate impact, prompting ongoing vigilance.
6. Key Individuals and Entities
- US Cybersecurity and Infrastructure Security Agency (CISA)
- Federal Civilian Executive Branch (FCEB) agencies
- Wing FTP Server users including US Air Force, Airbus, Reuters, Sony
- Julien Ahrens (security researcher)
7. Thematic Tags
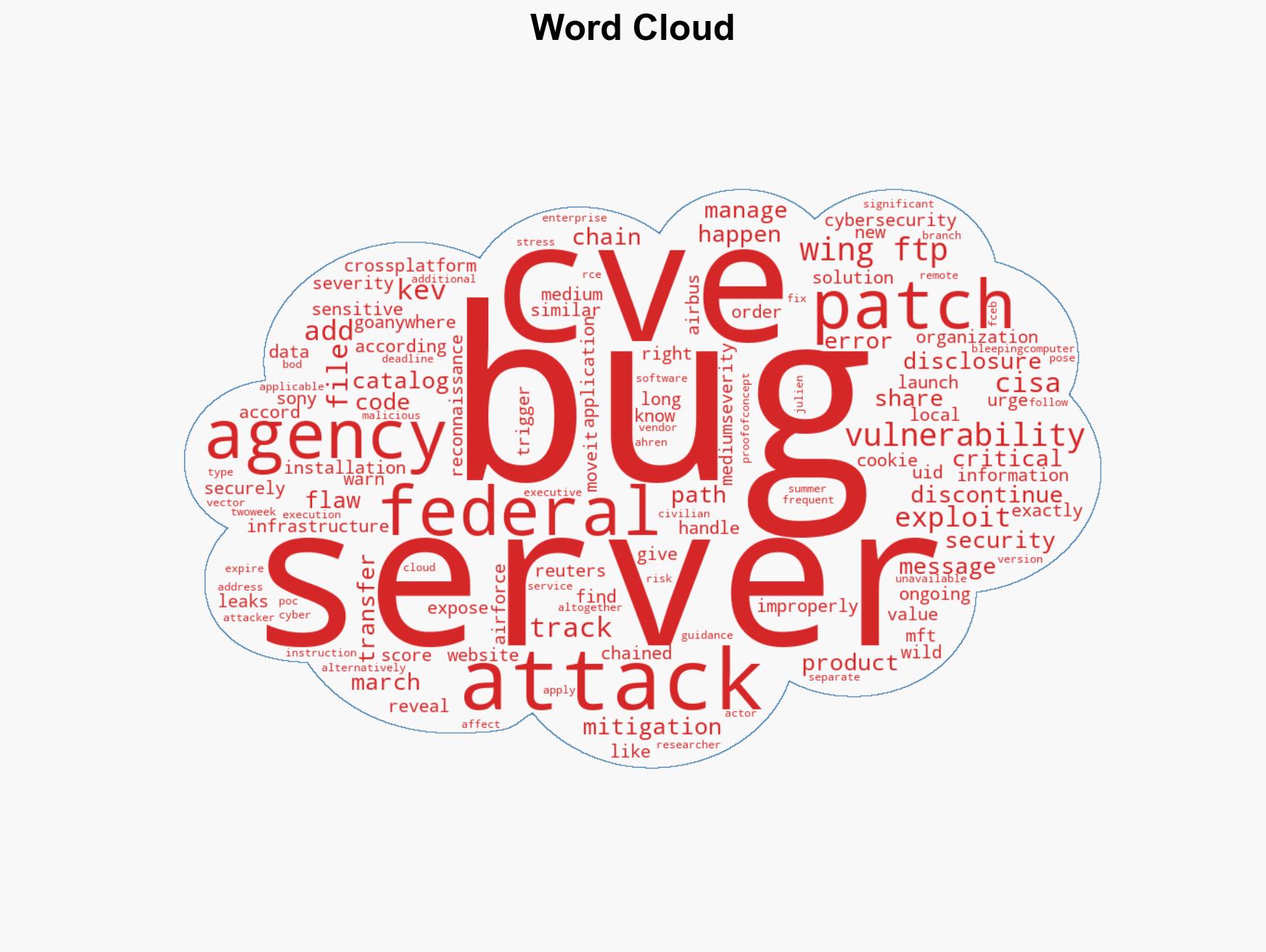
cybersecurity, vulnerability management, federal agencies, information disclosure, cyber threats, patch management, critical infrastructure
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us