CISA warns of Fast Flux DNS evasion used by cybercrime gangs – BleepingComputer
Published on: 2025-04-03
Intelligence Report: CISA warns of Fast Flux DNS evasion used by cybercrime gangs – BleepingComputer
1. BLUF (Bottom Line Up Front)
The Cybersecurity and Infrastructure Security Agency (CISA) has issued a warning regarding the use of Fast Flux DNS evasion techniques by cybercrime gangs. This method, employed by both low-tier cybercriminals and sophisticated nation-state actors, complicates efforts to trace and block malicious activities. CISA recommends enhanced detection and mitigation strategies to counter this threat.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
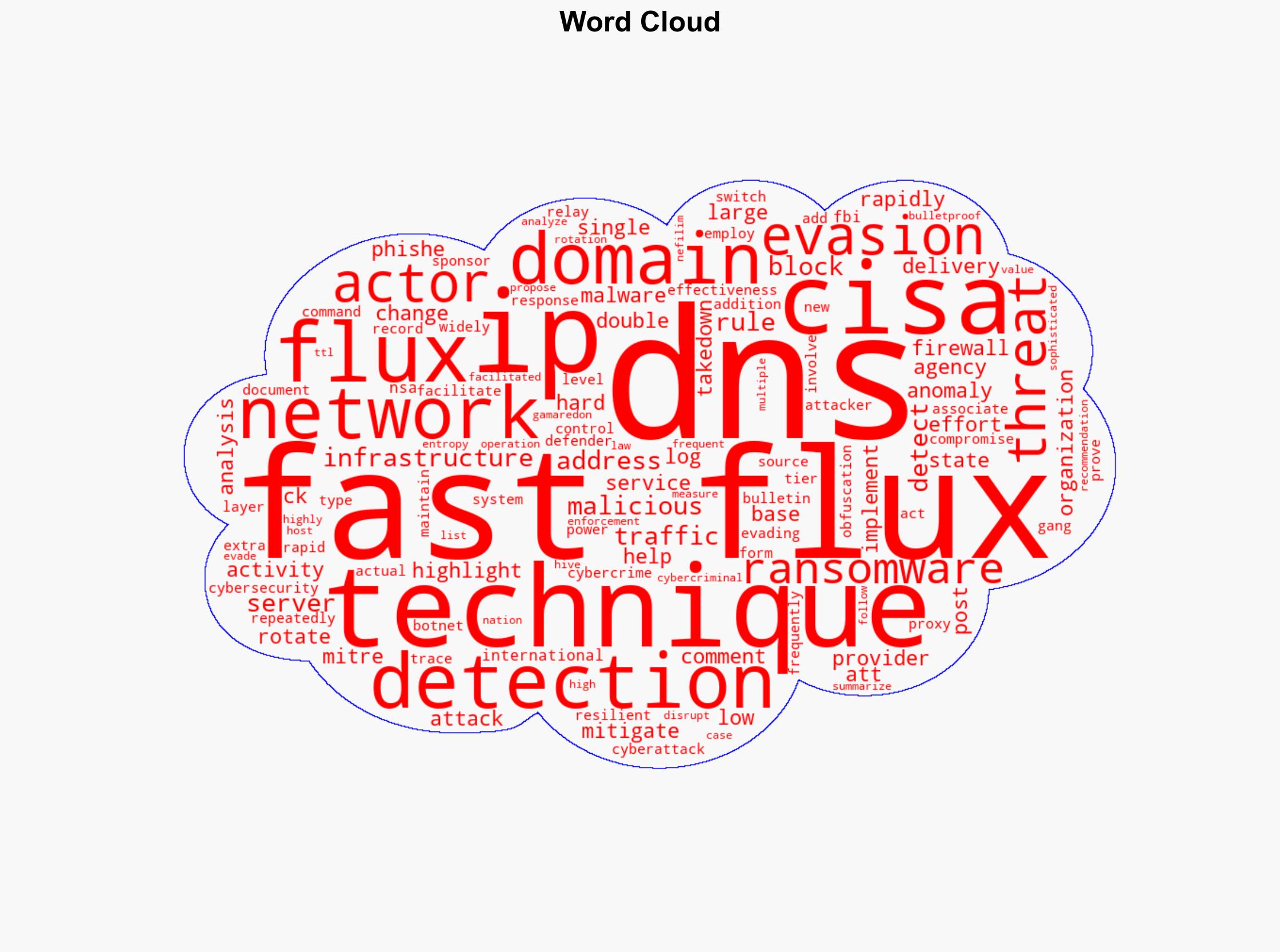
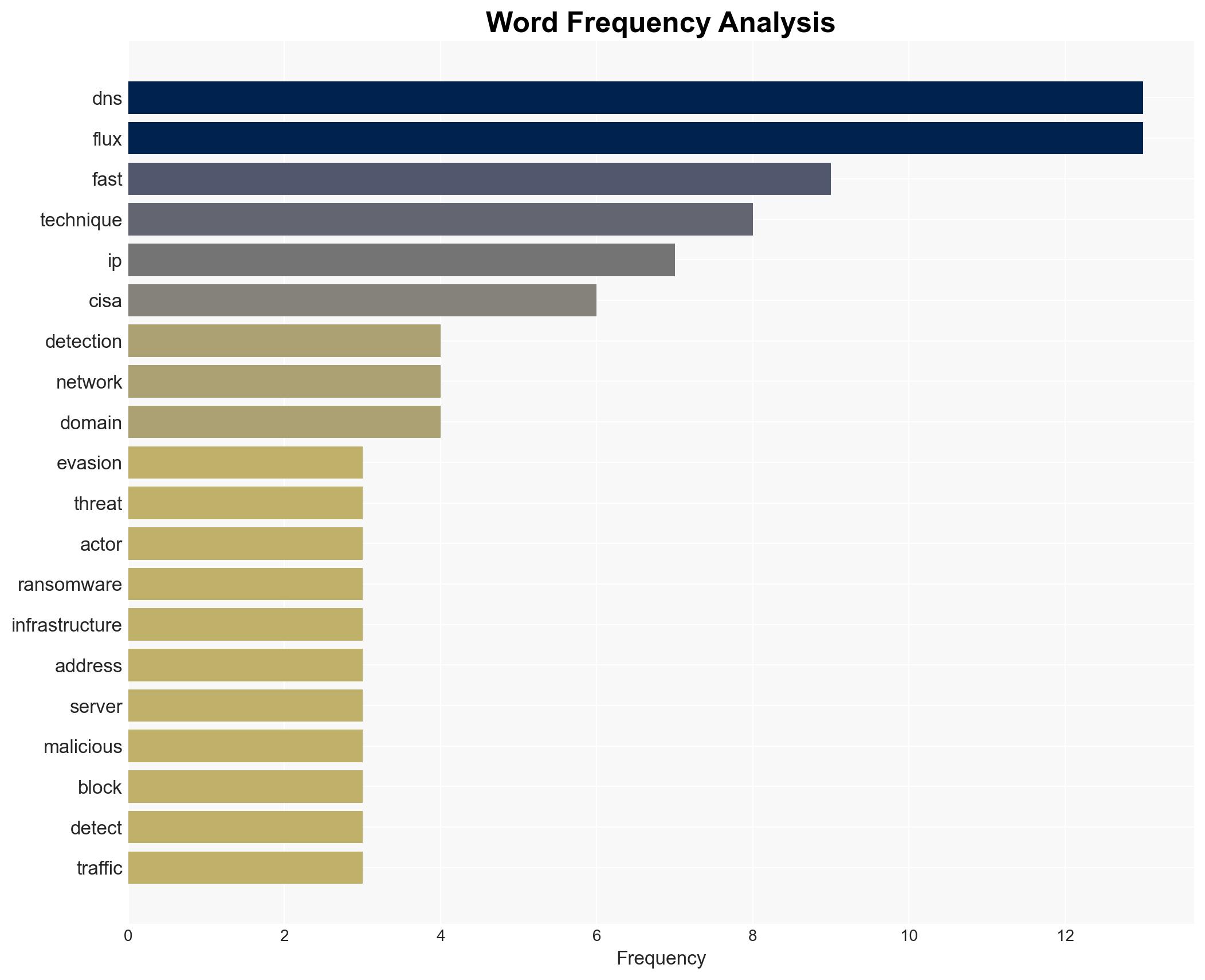
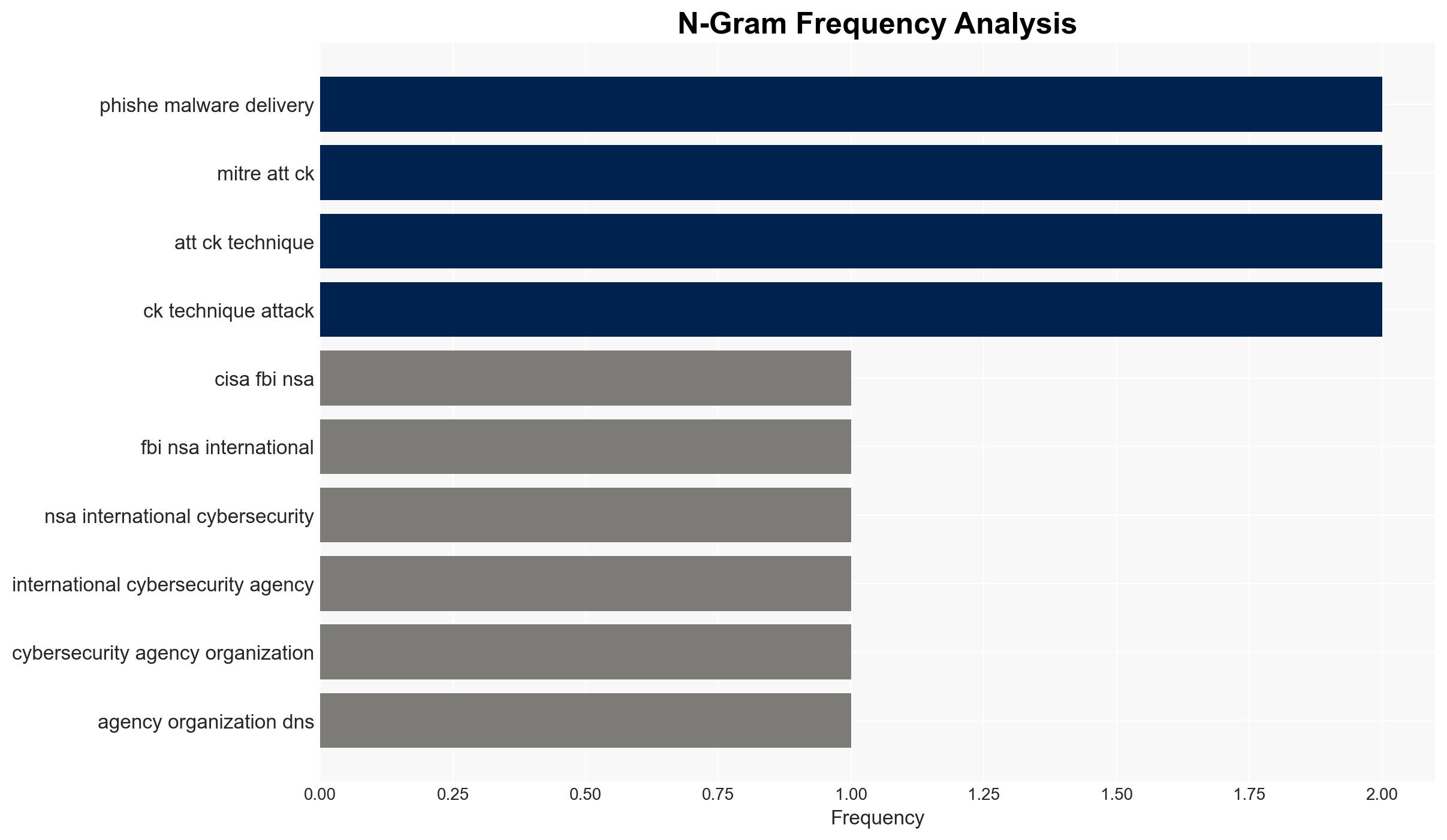
Fast Flux DNS is a technique used to evade detection by frequently changing DNS records and IP addresses associated with malicious domains. This method supports resilient command and control infrastructures for phishing and malware delivery. CISA highlights the use of both single and double flux techniques, which involve rapid IP rotation and DNS server changes, respectively. These tactics are employed by groups such as Gamaredon, Hive ransomware, and Nefilim ransomware, often in conjunction with bulletproof hosting services to resist law enforcement takedown efforts.
3. Implications and Strategic Risks
The widespread use of Fast Flux DNS poses significant risks to national security and economic interests. It enables cybercriminals to maintain robust infrastructures for launching attacks, complicating efforts to disrupt operations. The technique’s effectiveness in evading detection increases the likelihood of successful cyberattacks, potentially leading to data breaches, financial losses, and damage to critical infrastructure.
4. Recommendations and Outlook
Recommendations:
- Enhance DNS logging and monitoring to detect frequent IP address rotations and anomalies.
- Integrate external threat intelligence feeds and DNS reputation services to identify malicious activities.
- Implement network flow data analysis and anomaly detection algorithms to improve detection accuracy.
- Adopt centralized logging and real-time alerting systems for DNS anomalies.
- Encourage participation in information-sharing networks to enhance collective defense efforts.
Outlook:
In the best-case scenario, increased awareness and improved detection methods will mitigate the impact of Fast Flux DNS techniques. In the worst-case scenario, continued evasion by cybercriminals could lead to more frequent and severe cyberattacks. The most likely outcome involves a gradual improvement in detection and mitigation capabilities, reducing the effectiveness of these evasion techniques over time.
5. Key Individuals and Entities
The report mentions significant entities such as CISA, FBI, NSA, and international cybersecurity agencies. It also references cybercrime groups like Gamaredon, Hive ransomware, and Nefilim ransomware, as well as bulletproof hosting service providers.