Cisco identifies critical SD-WAN vulnerability exploited since 2023, prompting urgent patching measures.
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Cisco warns of critical SD-WAN security flaw which has been open since 2023
1. BLUF (Bottom Line Up Front)
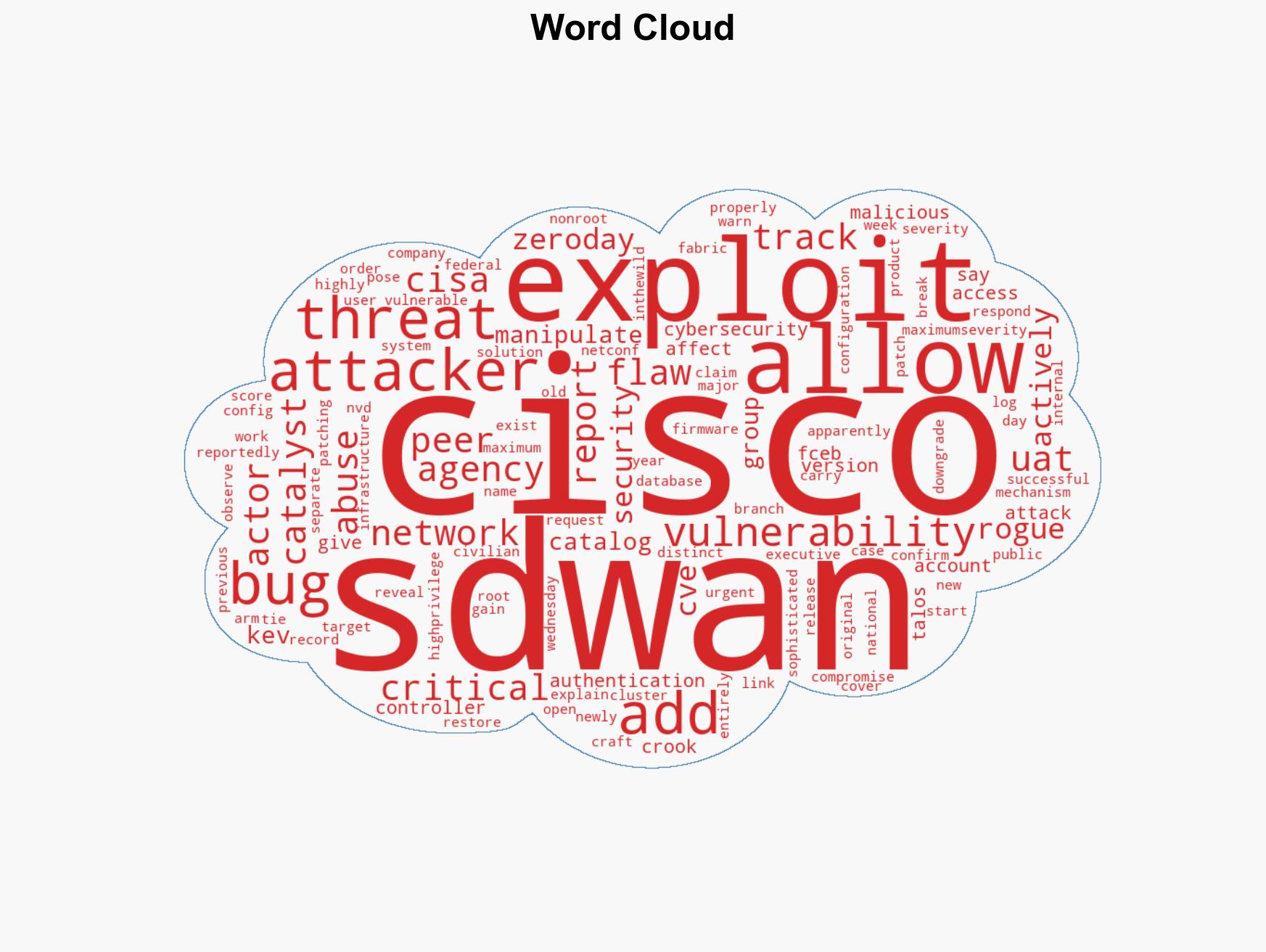
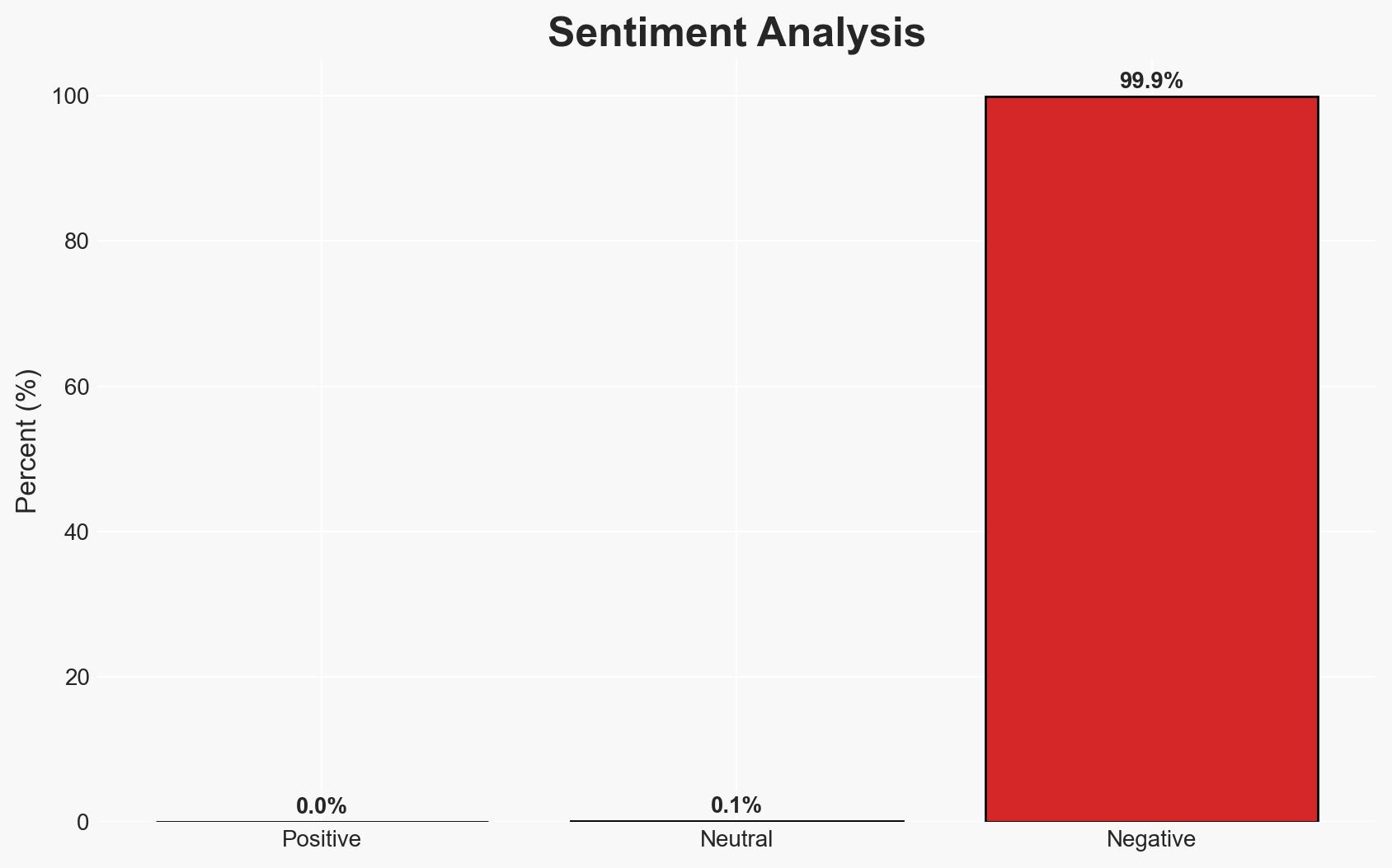
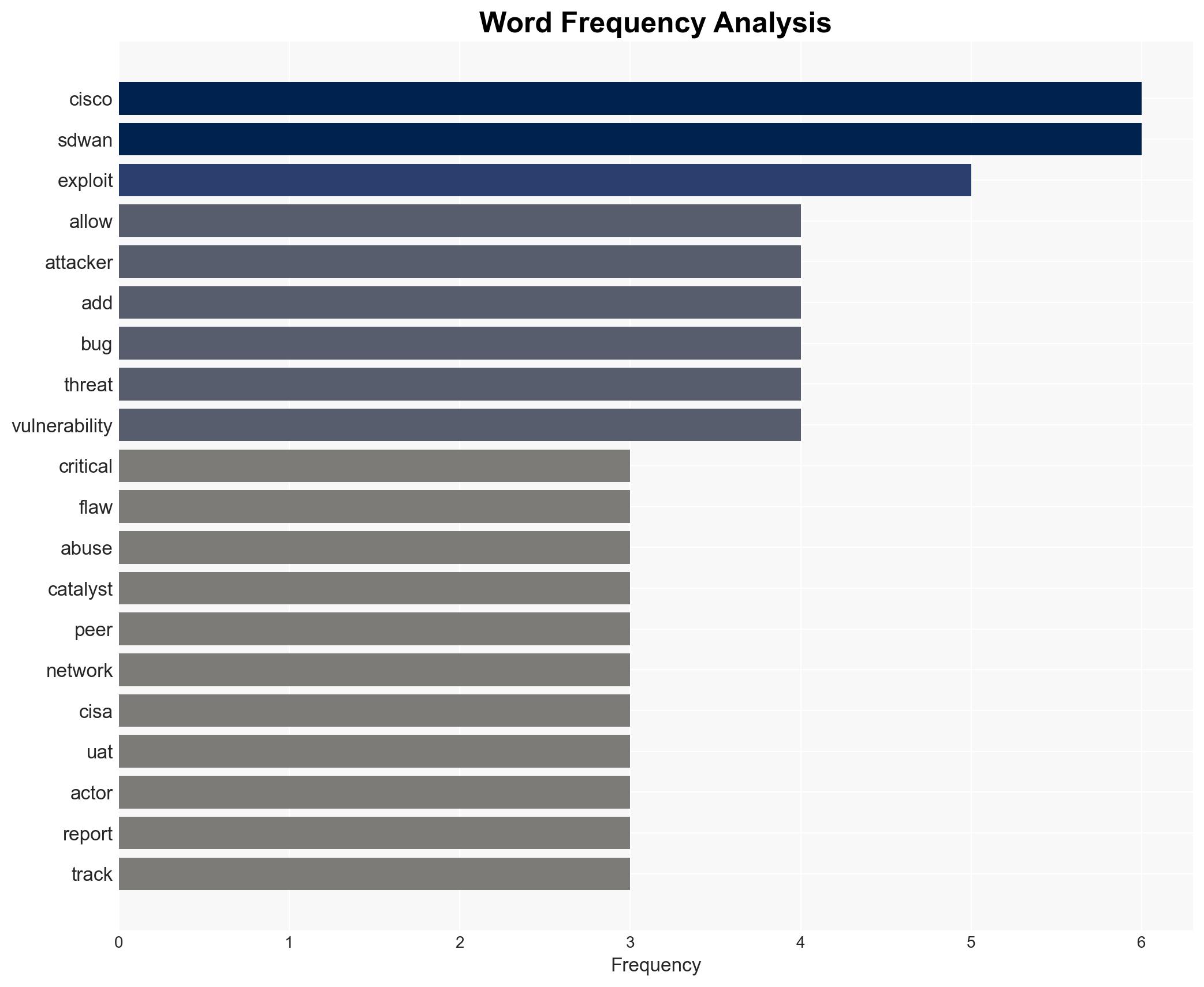
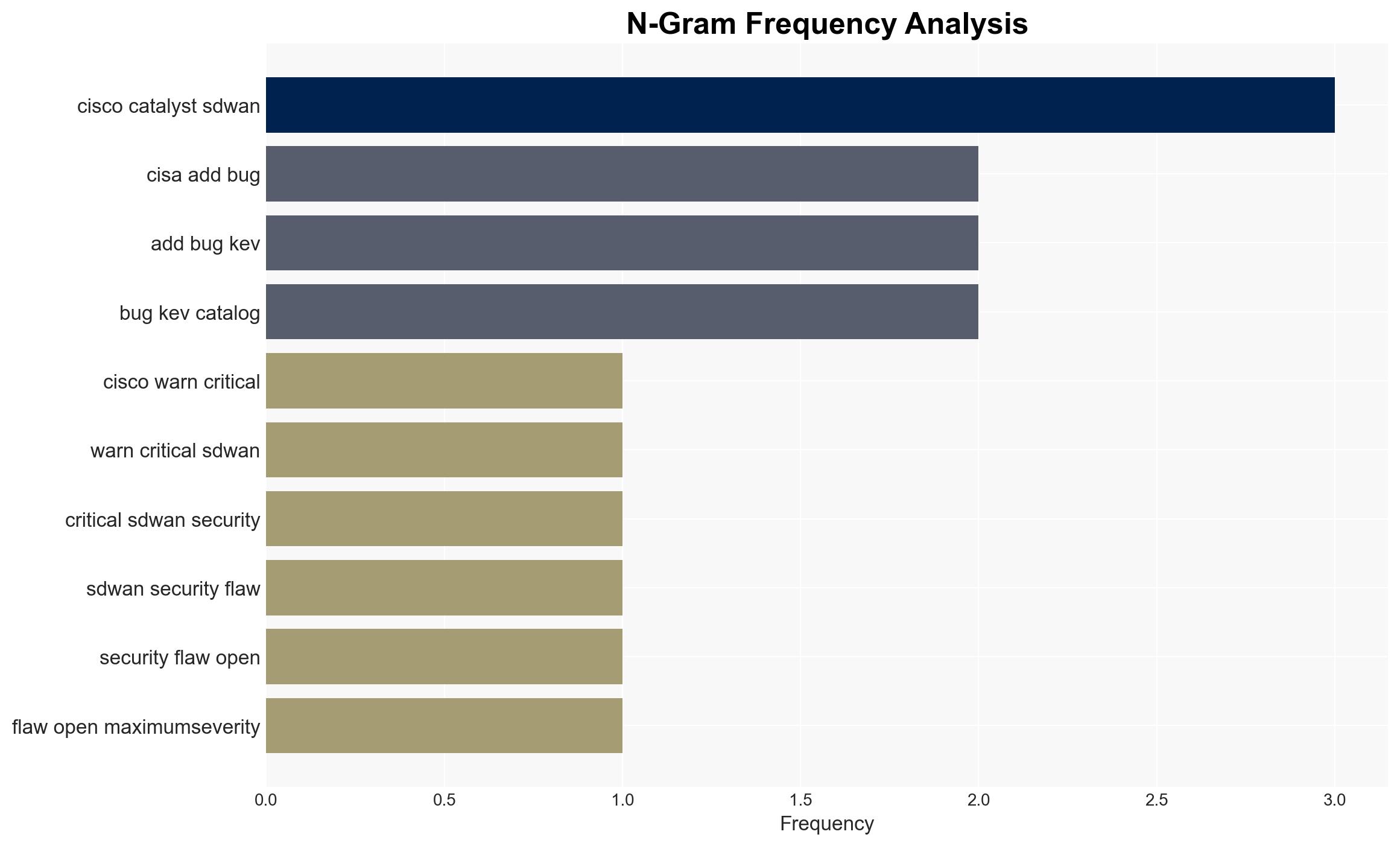
The Cisco Catalyst SD-WAN vulnerability CVE-2026-20127 has been actively exploited by threat actors, notably UAT-8616, since 2023. This flaw allows unauthorized access and manipulation of network configurations, posing a significant risk to affected systems. The urgency of the situation is underscored by CISA’s rapid response requirements. Overall confidence in this assessment is moderate, given the limited public information on UAT-8616.
2. Competing Hypotheses
- Hypothesis A: UAT-8616 is a state-sponsored group leveraging the vulnerability for strategic espionage. Supporting evidence includes the sophisticated nature of the attacks and the ability to cover tracks. However, there is no direct attribution to a specific nation-state.
- Hypothesis B: UAT-8616 is a financially motivated cybercriminal group exploiting the vulnerability for profit. This is supported by the typical modus operandi of exploiting and monetizing vulnerabilities. The lack of clear financial gain evidence contradicts this.
- Assessment: Hypothesis A is currently better supported due to the complexity and persistence of the attacks, which align with state-sponsored capabilities. Indicators such as direct attribution or financial transactions could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerability is primarily exploited by UAT-8616; Cisco’s reporting is accurate and comprehensive; CISA’s urgency reflects the true severity of the threat.
- Information Gaps: Detailed information on UAT-8616’s objectives and affiliations; comprehensive impact assessment on affected networks.
- Bias & Deception Risks: Potential bias in attributing the attacks to a newly named group without historical context; risk of underestimating the financial motivations of the actors involved.
4. Implications and Strategic Risks
This vulnerability’s exploitation could lead to significant disruptions in network operations and potential data breaches, affecting both public and private sectors. The situation could escalate if more threat actors exploit the flaw.
- Political / Geopolitical: Potential for increased tensions if state-sponsored involvement is confirmed, leading to diplomatic repercussions.
- Security / Counter-Terrorism: Heightened threat environment for organizations using Cisco SD-WAN, necessitating increased security measures.
- Cyber / Information Space: Increased focus on securing SD-WAN infrastructures and potential for widespread cyber defense initiatives.
- Economic / Social: Possible financial losses for affected companies and reputational damage to Cisco, impacting market trust.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently apply patches as directed by CISA; enhance monitoring of network traffic for signs of exploitation; conduct security audits on SD-WAN configurations.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing on threat actor activities; invest in cybersecurity training and infrastructure resilience.
- Scenario Outlook: Best: Vulnerability patched and no further exploitation. Worst: Widespread exploitation leading to major breaches. Most-Likely: Continued targeted exploitation with gradual mitigation as patches are applied.
6. Key Individuals and Entities
- Cisco (affected entity)
- UAT-8616 (threat actor)
- CISA (regulatory body)
- Talos (Cisco’s cybersecurity arm)
7. Thematic Tags
cybersecurity, vulnerability management, state-sponsored threats, network security, cyber defense, threat intelligence, SD-WAN
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us