Cisco IMC vulnerability CVE-2026-20093 enables remote attackers to bypass authentication and change admin pas…
Published on: 2026-04-03
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Cisco IMC auth bypass vulnerability allows attackers to alter user passwords CVE-2026-20093
1. BLUF (Bottom Line Up Front)
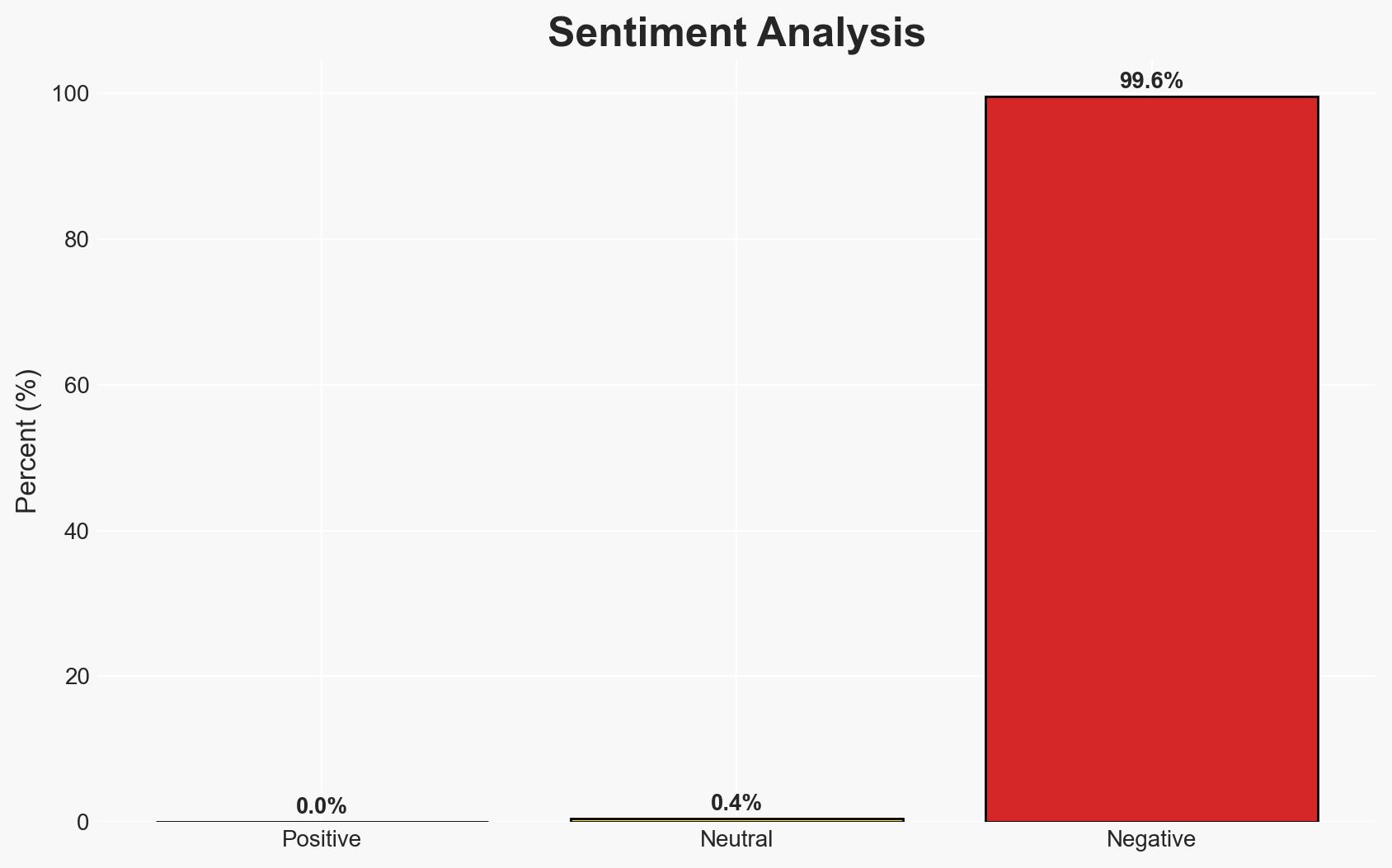
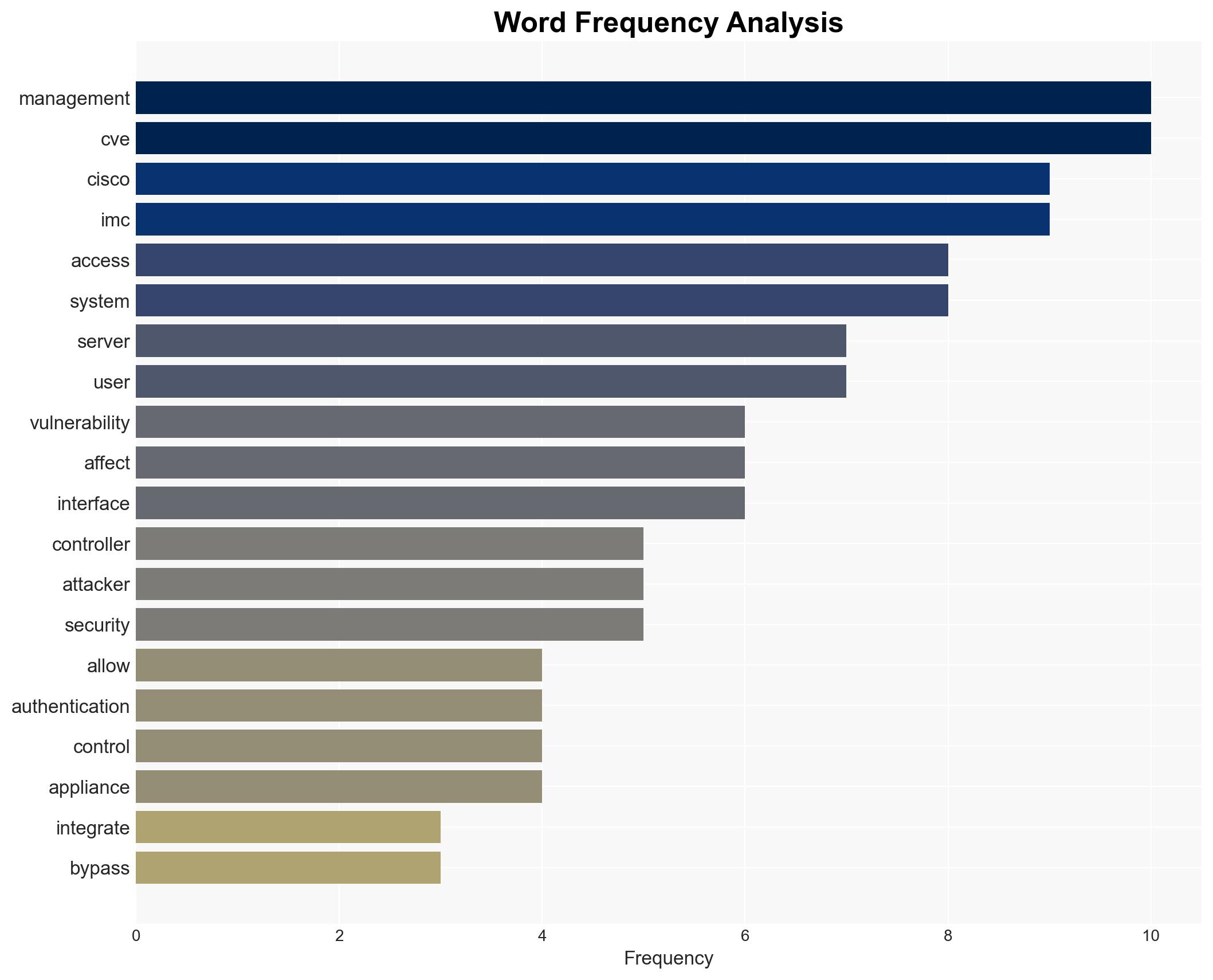
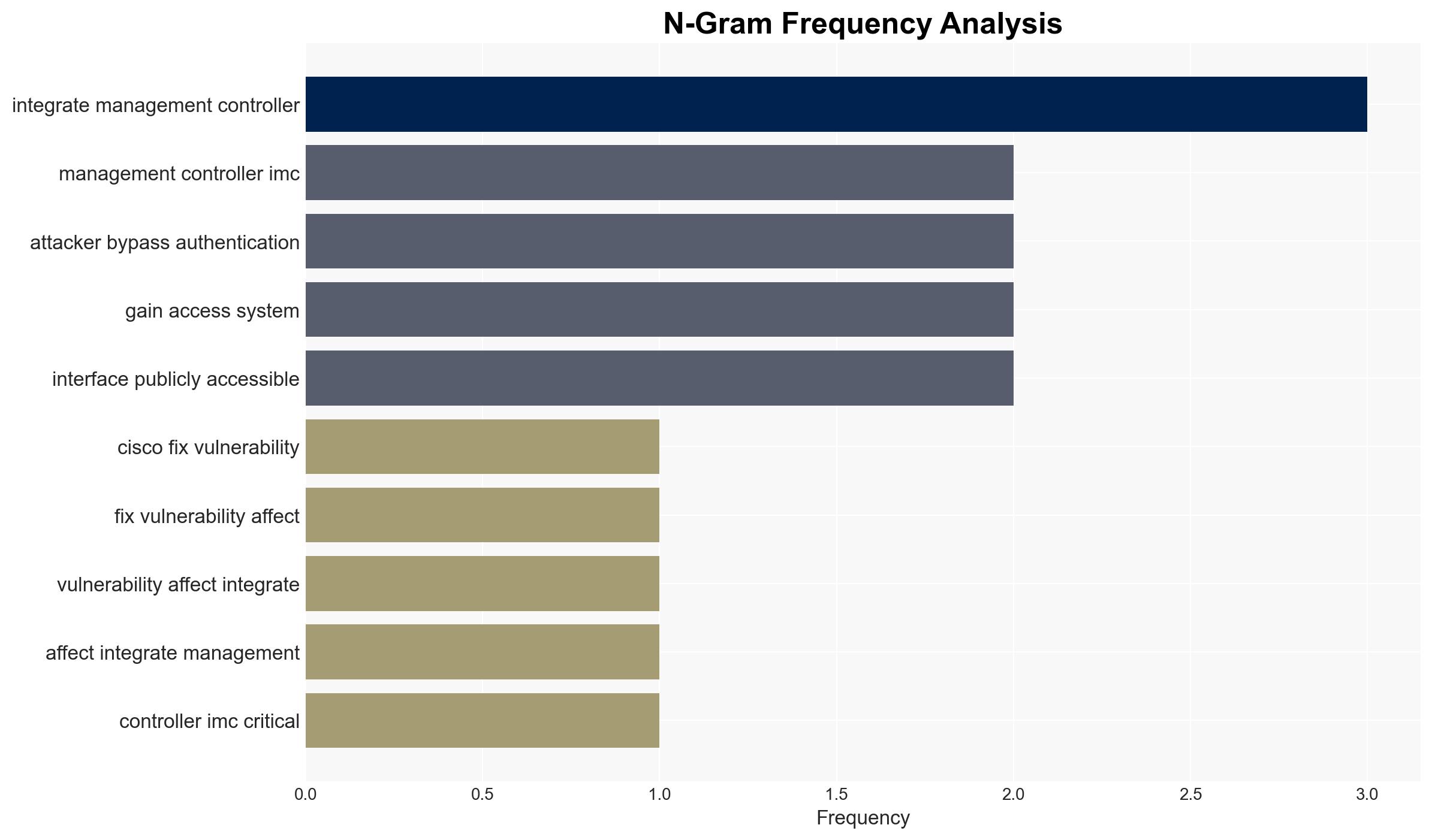
The Cisco IMC vulnerability CVE-2026-20093 poses a significant security risk, allowing unauthenticated remote attackers to gain admin access to affected systems. This vulnerability impacts a wide range of Cisco server platforms, potentially compromising critical infrastructure. The overall confidence level in this assessment is moderate, given the lack of active exploitation reports but the high potential impact.
2. Competing Hypotheses
- Hypothesis A: The vulnerability will be actively exploited in the near term due to its critical nature and the widespread use of affected systems. Supporting evidence includes the potential for high-impact breaches and the lack of current exploitation, which may change as awareness increases. Key uncertainties include the speed of patch adoption and attacker capabilities.
- Hypothesis B: The vulnerability will not see widespread exploitation due to rapid patch deployment and mitigations by affected organizations. This is supported by Cisco’s prompt advisory and the absence of current exploitation. However, this hypothesis is contradicted by the historical lag in patch application across large networks.
- Assessment: Hypothesis A is currently better supported due to the critical nature of the vulnerability and the potential for high-value targets. Indicators that could shift this judgment include reports of active exploitation or widespread patch adoption.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will prioritize patching critical vulnerabilities; attackers are aware of the vulnerability; Cisco’s advisory reaches all affected entities.
- Information Gaps: Specific details on the number of unpatched systems and the timeline for patch deployment.
- Bias & Deception Risks: Potential underreporting of exploitation due to reputational concerns; overreliance on vendor advisories without independent verification.
4. Implications and Strategic Risks
This vulnerability could lead to significant security breaches if exploited, affecting not only the targeted organizations but also broader network security dynamics.
- Political / Geopolitical: Potential for state-sponsored actors to exploit the vulnerability for espionage or sabotage.
- Security / Counter-Terrorism: Increased risk of cyber-attacks on critical infrastructure, potentially affecting national security.
- Cyber / Information Space: Heightened threat landscape with potential for increased cybercrime and information warfare.
- Economic / Social: Possible economic impacts due to service disruptions and increased cybersecurity costs.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urge all organizations to apply Cisco’s security updates immediately and restrict public access to management interfaces.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing on vulnerabilities and enhance monitoring capabilities for early detection of exploitation.
- Scenario Outlook:
- Best Case: Rapid patch deployment prevents any significant exploitation.
- Worst Case: Delayed patching leads to widespread breaches, impacting critical infrastructure.
- Most Likely: Mixed patching success with isolated incidents of exploitation.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
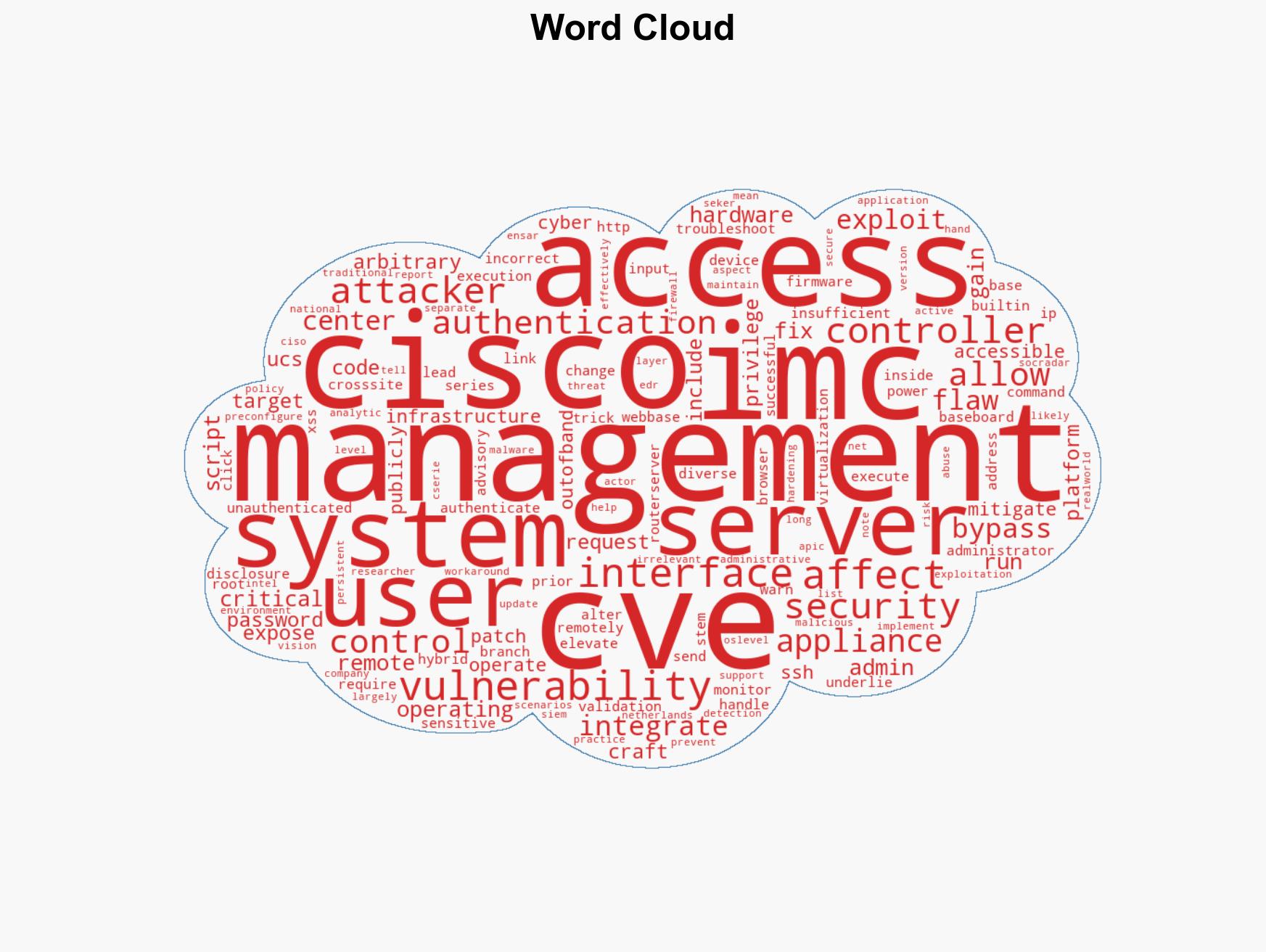
cybersecurity, vulnerability management, critical infrastructure, Cisco IMC, cyber threat, patch management, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us