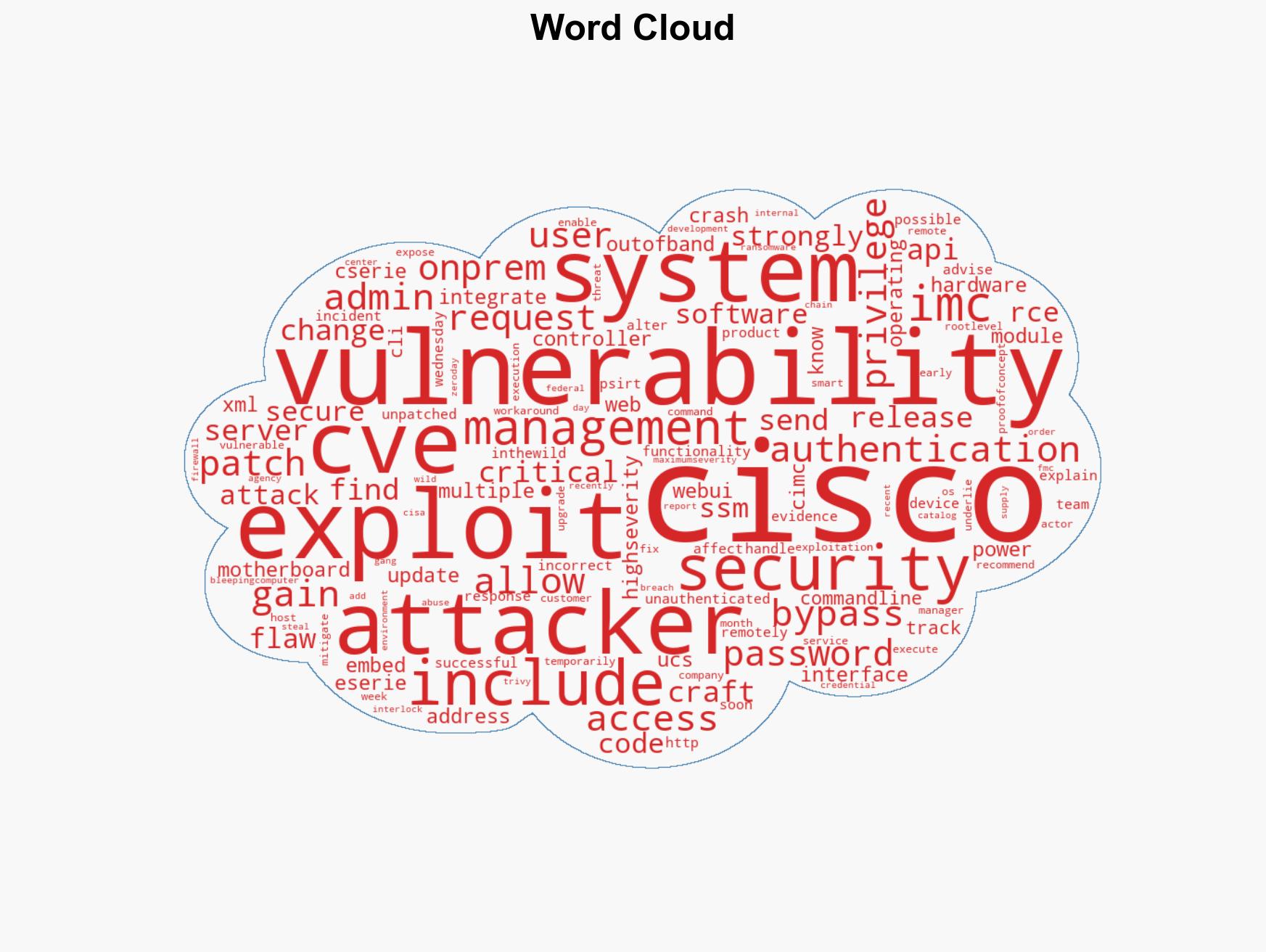
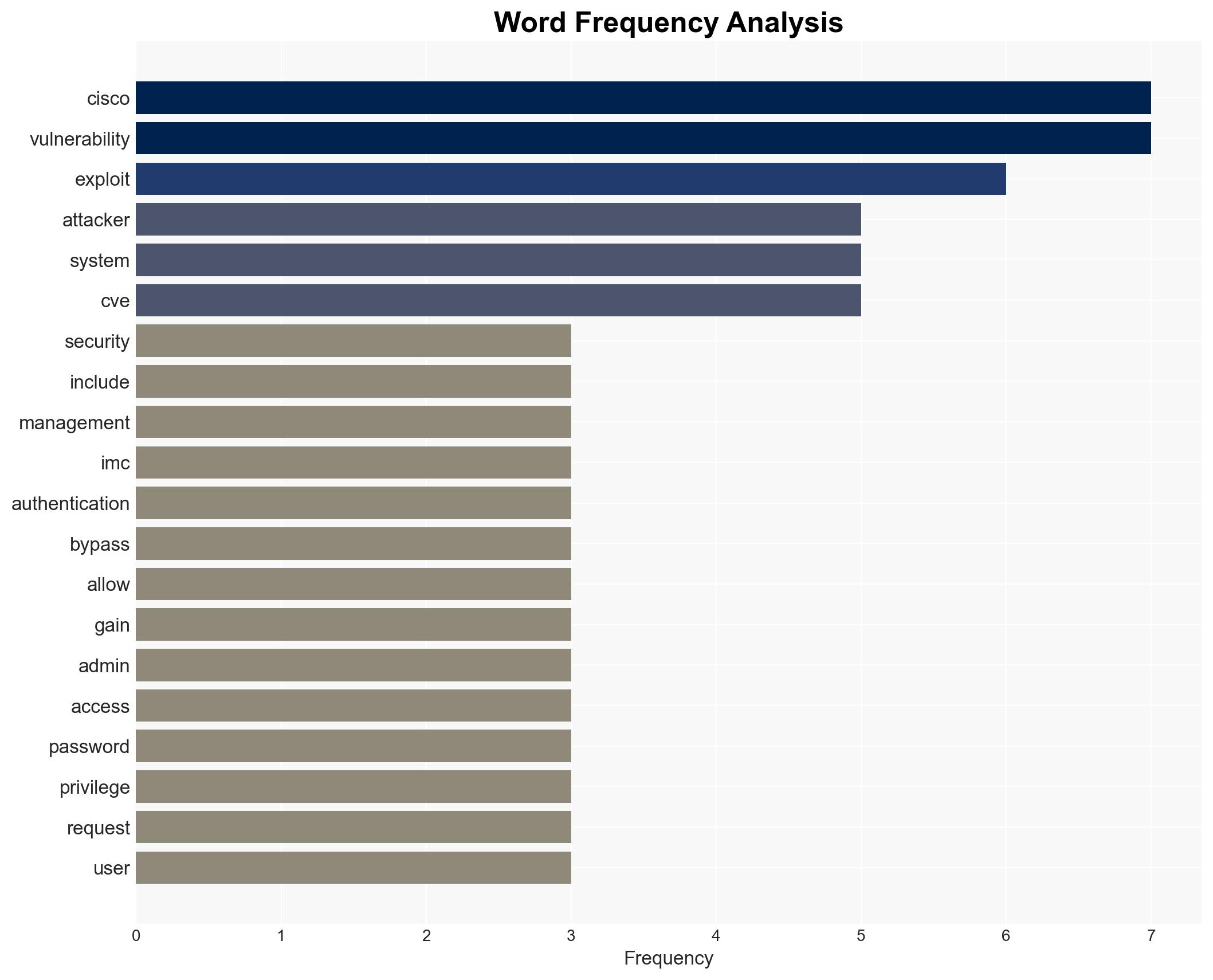
Cisco IMC vulnerability enables unauthenticated attackers to gain Admin access through authentication bypass
Published on: 2026-04-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Critical Cisco IMC auth bypass gives attackers Admin access
1. BLUF (Bottom Line Up Front)
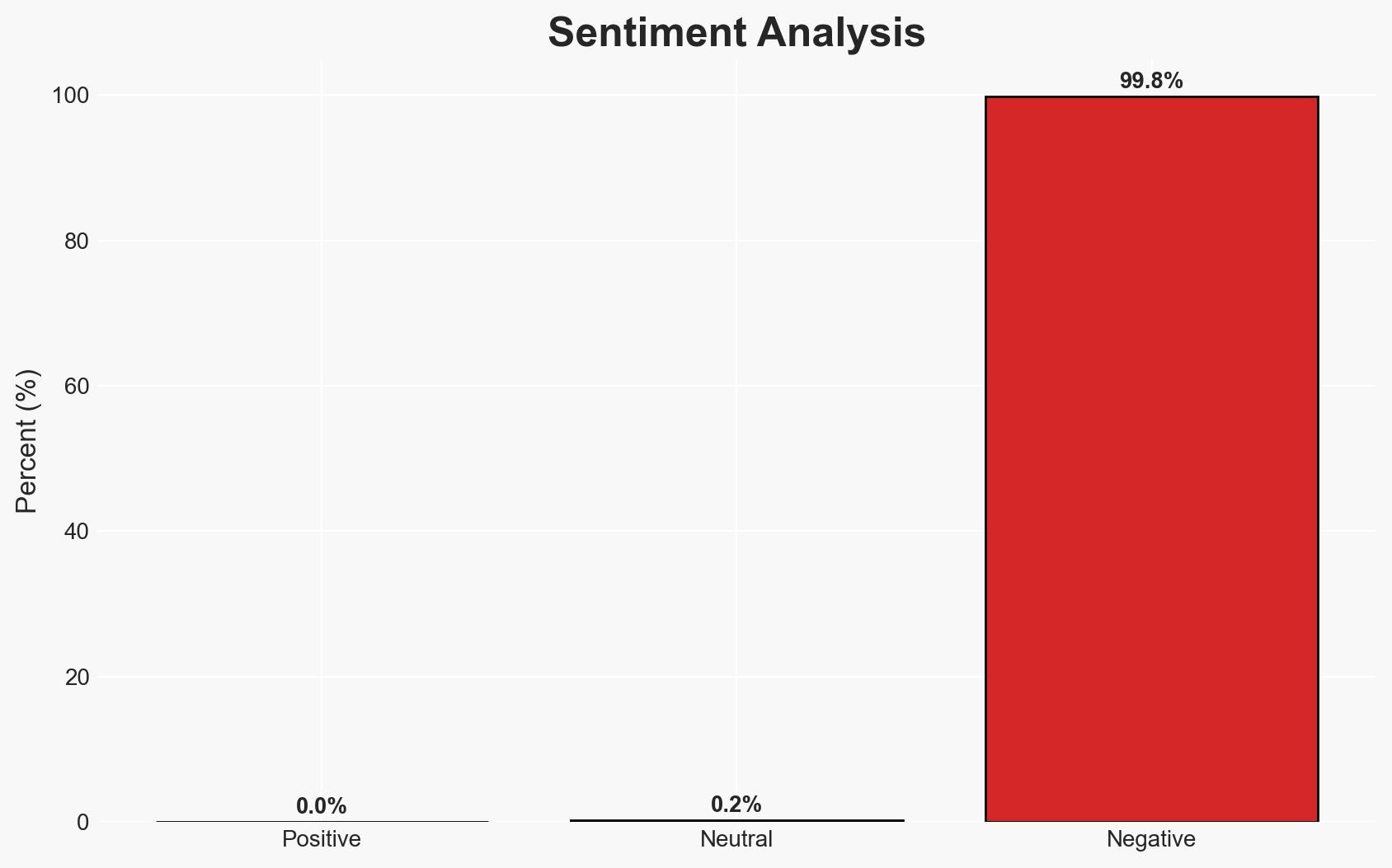
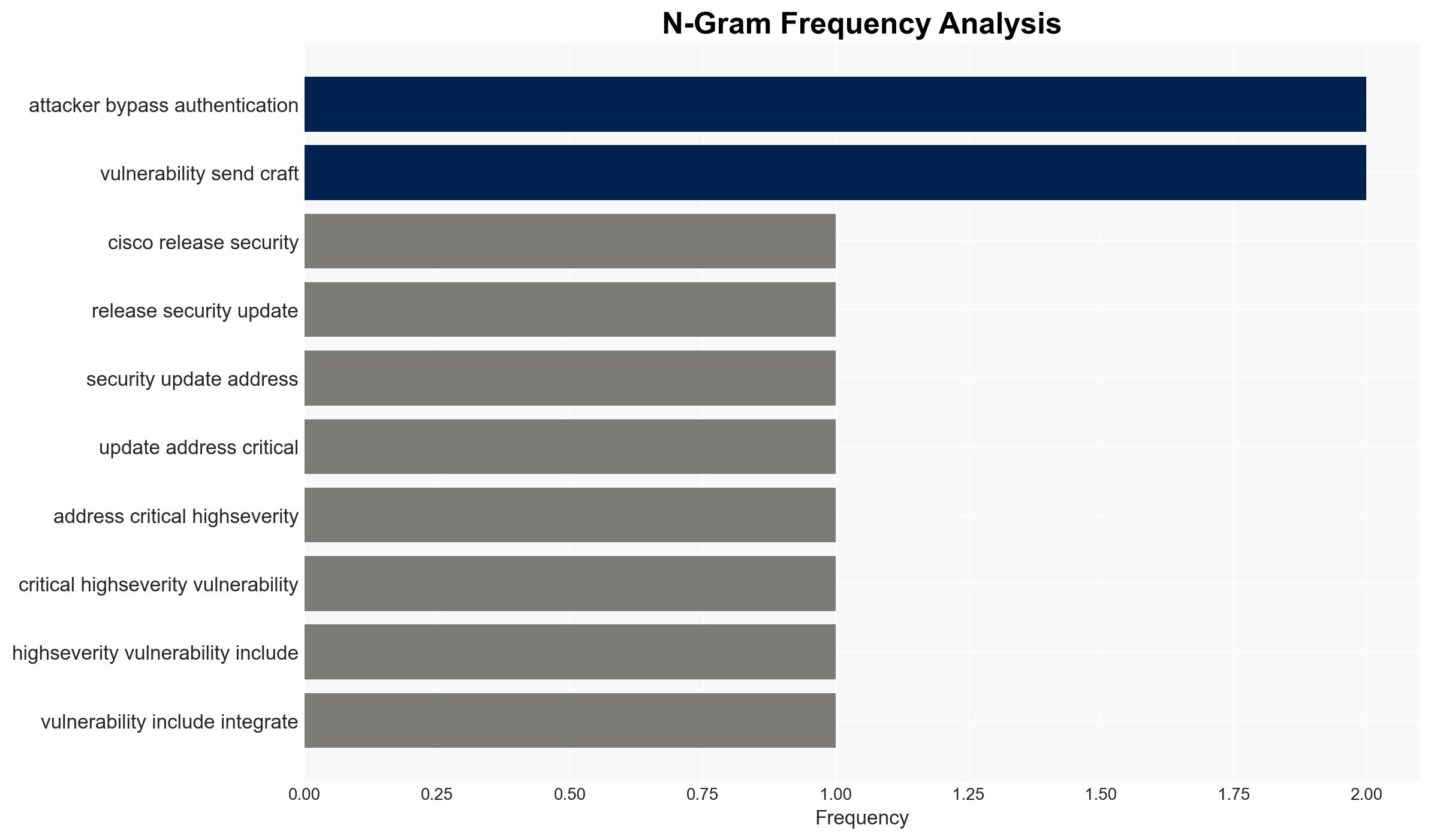
The discovery of a critical authentication bypass vulnerability in Cisco’s Integrated Management Controller (IMC) poses a significant risk to organizations using Cisco UCS C-Series and E-Series servers. This vulnerability allows unauthenticated attackers to gain admin access, potentially compromising sensitive systems. While no active exploitation has been reported, the lack of workarounds necessitates immediate patching. Overall confidence in this assessment is moderate due to the absence of in-the-wild exploitation evidence.
2. Competing Hypotheses
- Hypothesis A: The vulnerability will be exploited in the near future, leading to significant security breaches. This is supported by the critical nature of the vulnerability and the lack of workarounds, but contradicted by the current lack of exploitation evidence.
- Hypothesis B: Organizations will rapidly deploy patches, preventing widespread exploitation. This is supported by Cisco’s strong recommendation to patch and the proactive nature of many organizations, but contradicted by potential delays in patch deployment due to operational constraints.
- Assessment: Hypothesis B is currently better supported due to Cisco’s immediate communication and patch release, which may prompt rapid organizational responses. However, any reports of exploitation or delays in patching could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will prioritize patching; attackers have not yet developed a reliable exploit; Cisco’s patch is effective.
- Information Gaps: Current status of patch deployment across affected organizations; potential existence of undisclosed exploitations.
- Bias & Deception Risks: Over-reliance on Cisco’s reporting; potential underestimation of attackers’ capabilities to develop exploits quickly.
4. Implications and Strategic Risks
This vulnerability could lead to significant security breaches if exploited, affecting critical infrastructure and sensitive data. The situation may evolve based on the speed of patch deployment and the emergence of exploit tools.
- Political / Geopolitical: Potential for state-sponsored actors to exploit the vulnerability for espionage.
- Security / Counter-Terrorism: Increased risk of cyber-attacks on critical infrastructure.
- Cyber / Information Space: Heightened alert in the cybersecurity community; potential for increased cyber defense measures.
- Economic / Social: Financial implications for affected organizations due to potential breaches and mitigation costs.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently apply Cisco’s patches; enhance monitoring for unusual activity; communicate risks to stakeholders.
- Medium-Term Posture (1–12 months): Develop contingency plans for potential breaches; invest in cybersecurity training and infrastructure.
- Scenario Outlook: Best: Rapid patching prevents exploitation. Worst: Delayed patching leads to widespread breaches. Most-Likely: Mixed patching response with isolated incidents.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, vulnerability management, Cisco, critical infrastructure, patch management, cyber defense, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us