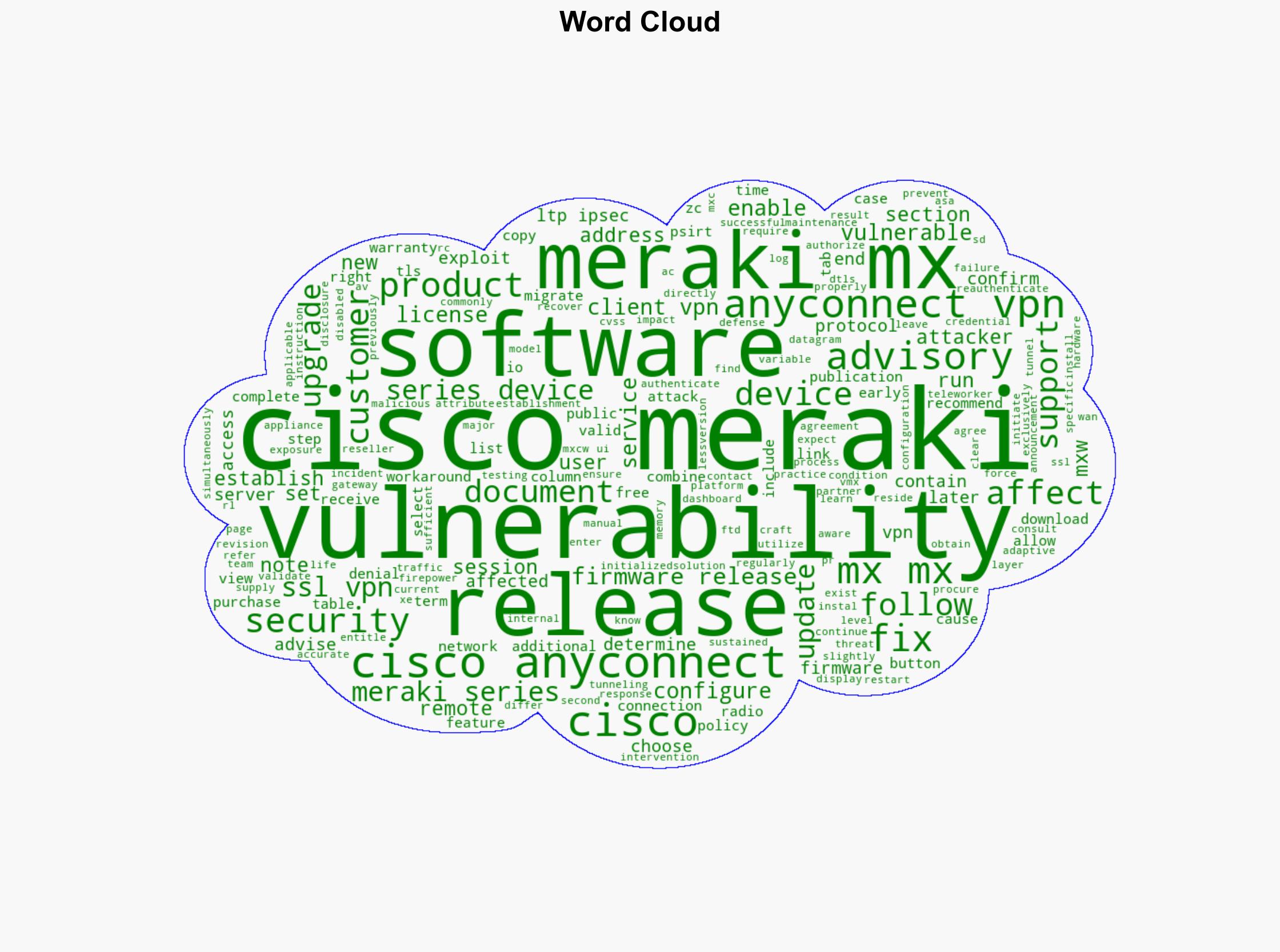
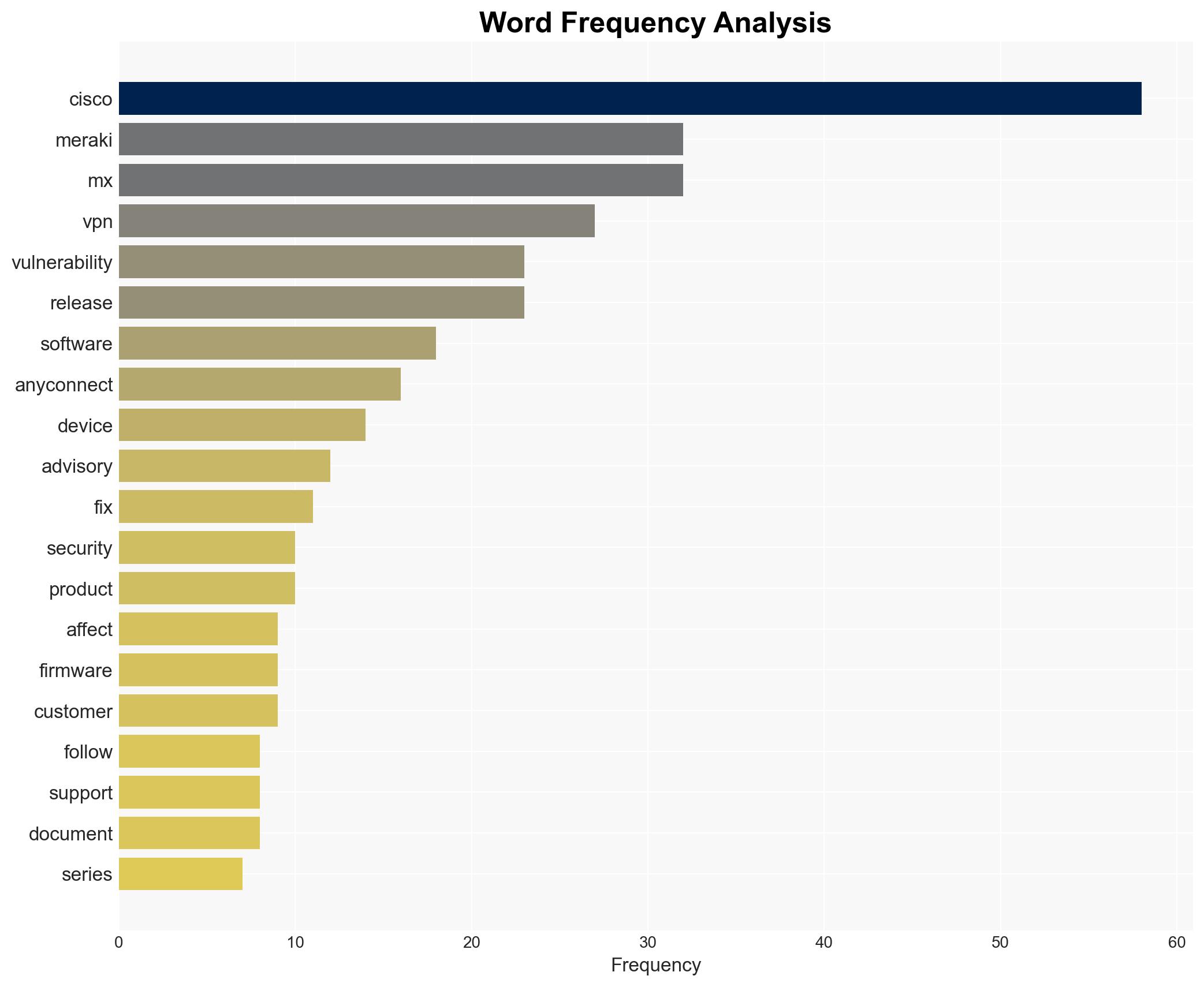
Cisco Meraki MX and Z Series AnyConnect VPN Denial of Service Vulnerability – Cisco.com
Published on: 2025-04-02
Intelligence Report: Cisco Meraki MX and Z Series AnyConnect VPN Denial of Service Vulnerability – Cisco.com
1. BLUF (Bottom Line Up Front)
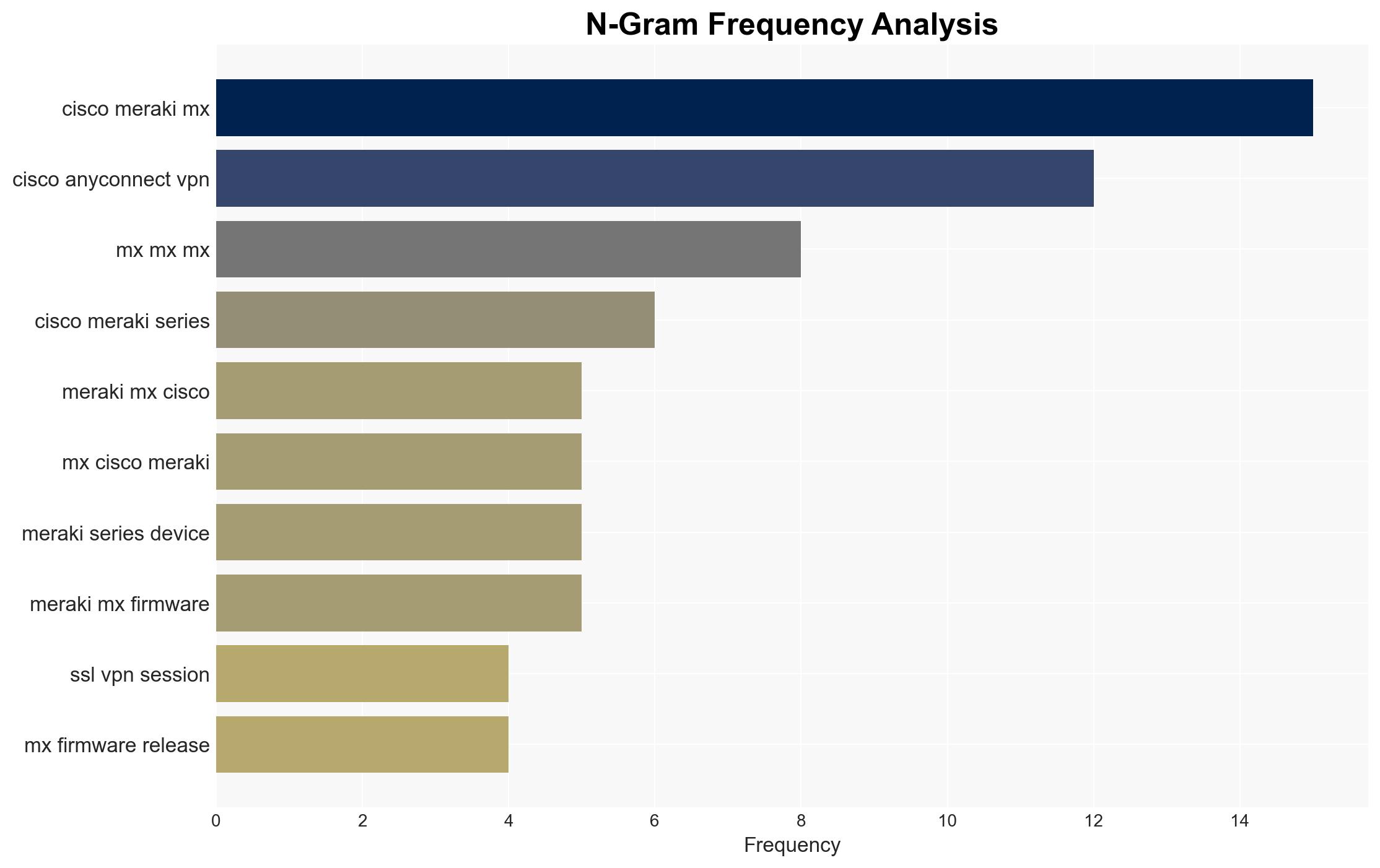
A critical vulnerability has been identified in Cisco Meraki MX and Z Series devices, specifically affecting the AnyConnect VPN service. This vulnerability allows authenticated remote attackers to cause a denial of service (DoS) condition by exploiting improperly initialized SSL VPN sessions. The vulnerability impacts devices running specific firmware versions, necessitating immediate attention to mitigate potential disruptions in secure communications.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
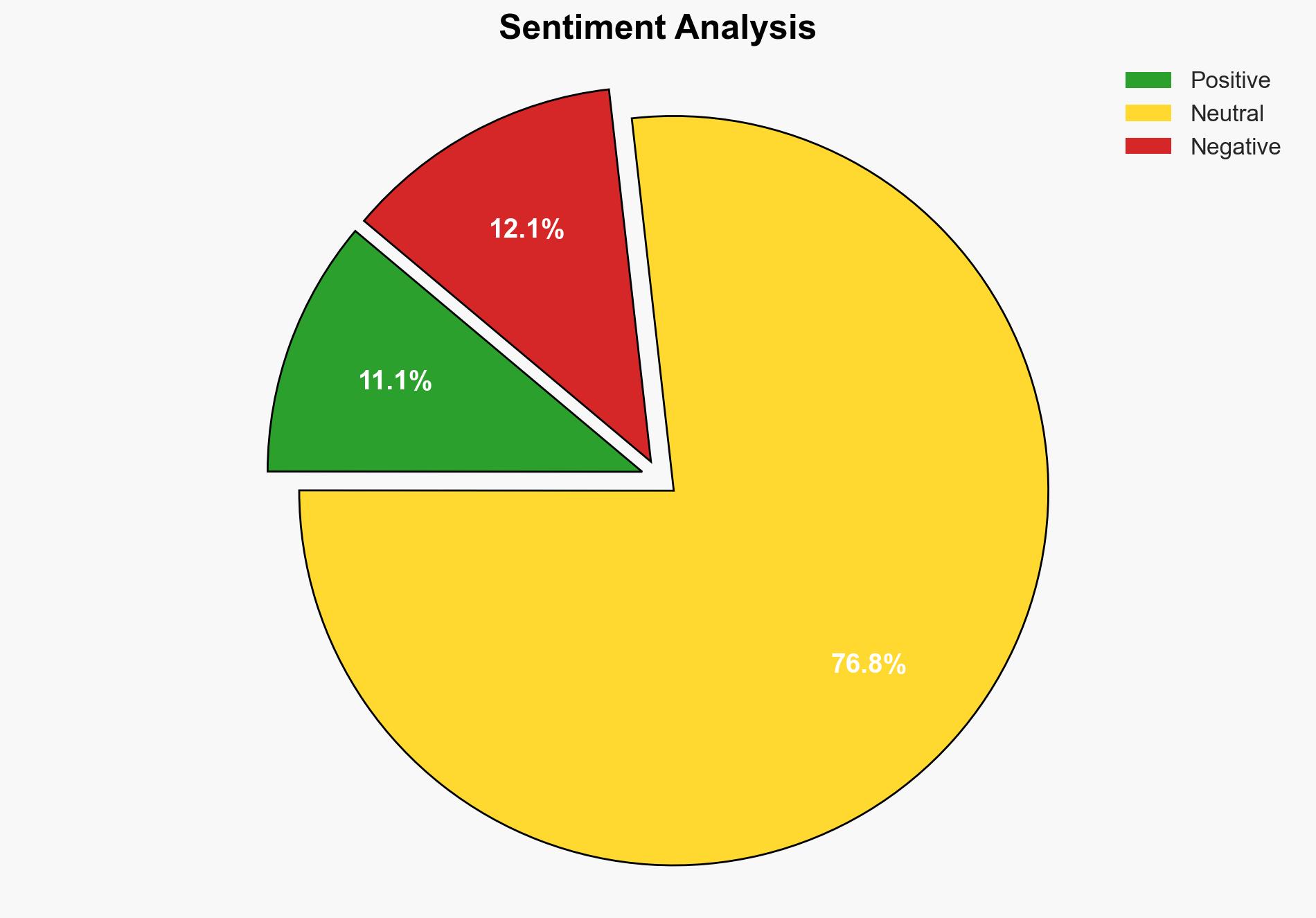
General Analysis
The vulnerability exists due to improperly initialized variables during SSL VPN session establishment. An attacker with valid VPN credentials can exploit this flaw by supplying crafted attributes, causing the Cisco AnyConnect VPN server to restart. This results in a temporary inability to establish new VPN connections, forcing remote users to reauthenticate. The attack can be sustained to prevent new connections until manual intervention is performed. Cisco has released a software update to address this issue, and a workaround is available for immediate mitigation.
3. Implications and Strategic Risks
The vulnerability poses significant risks to organizations relying on Cisco Meraki MX and Z Series devices for secure remote access. Potential impacts include:
- Disruption of secure communications, affecting business operations and continuity.
- Increased vulnerability to further cyberattacks during service downtime.
- Potential data breaches if attackers leverage the vulnerability for broader access.
On a larger scale, the vulnerability could impact national security and economic interests if exploited against critical infrastructure or government entities.
4. Recommendations and Outlook
Recommendations:
- Immediately apply the Cisco software update to affected devices to mitigate the vulnerability.
- Implement the available workaround as a temporary measure until the update is applied.
- Enhance monitoring of VPN traffic to detect and respond to potential exploitation attempts.
- Review and update incident response plans to address potential DoS scenarios.
Outlook:
Best-case scenario: Organizations promptly apply updates and workarounds, minimizing disruption and preventing exploitation.
Worst-case scenario: Delays in patching lead to widespread exploitation, resulting in significant operational and security impacts.
Most likely outcome: Affected organizations will gradually implement mitigations, with some experiencing temporary disruptions.
5. Key Individuals and Entities
The report mentions significant entities such as Cisco and Meraki, which are responsible for addressing the vulnerability. No individual names are referenced in the source material.